You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Need Vouch Please
- Thread starter PlraX
- Start date
Does any know how to pay the LR fee. I've tried contacting admin with no response recieved
It's good way to collect your money
- Messages
- 4
- Reaction score
- 0
- Points
- 1
Please note, if you want to make a deal with this user, that it is blocked.
Hi vouch me i am interesting some to this forum.

I got recently a package of files found in a infected POS (POS hacked due to a weak rdp password)

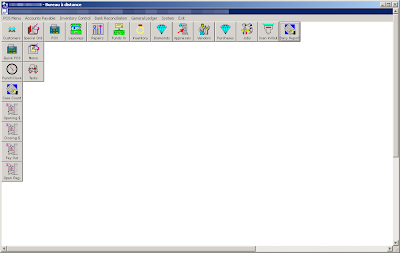
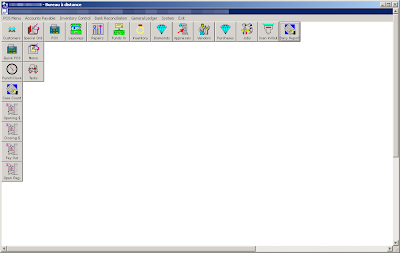
Interface of a compromised POS used by a jeweller:
out.exe is a Ardamax Keylogger (ardamax.com) and vui qua.exe is a SFX archive who display this picture when executed:

And drop Pefect Keylogger (blazingtools.com) behind.
"vui qua" might be a Vietnamese phrase which translated is "so funny".
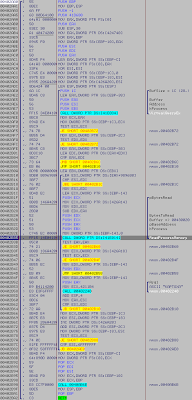
These two keyloggers are probably useless for the carder, the interesting file here is "mmon.exe" a ram scraper.
It scan each and every process looking for CC dumps thats been written to memory Track 1, 2.
If a Point Of Sale device is connected to the computer it will grab it's card data right away.
How? POS always use end to end encryption, the only place where it's not encrypted are inside the memory.
But.. the memory have limited storage so it overwrites the data all the time.
It's also a problem for mmon, because this crap have no loop feature and does not write inside a file.
POS Carders usually use better malware than this, but i got this so...
(mmon.exe, "Kartoxa" is probably the distorted version of the word "potato")
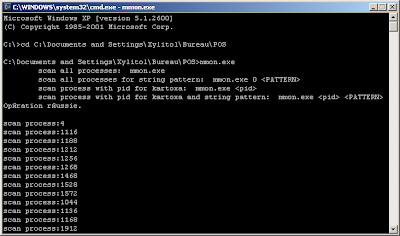
mmon scanning process.
test of mmon with a valid track two in memory
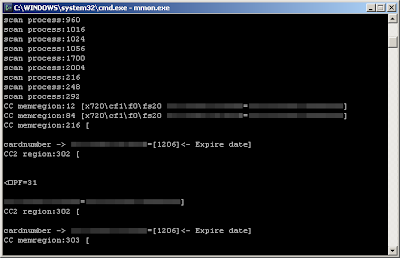
When a dump is found, the program do nothing with it, it just display the stuff on console.
The bad guys just connect to the POS via RDP, get dumps via mmon and write them out on magnetic stripe with a card writer.

(MSR606 USB Magnetic Stripe Reader Writer/Encoder)
Then use an embosser to make imprinted numbers on the card.
(A DXR 70C embosser)
And it's ready to use... in USA (Type 101)
The ones we have in Europe are 201 cards (pin and chip)
101 only need to swipes the card in a store and the cashier checks the 4 last digits on the card if they are corect.
Carders also use printers like Fargo to make fake identities.
Anyway, a POS malware have a high price, it's not a business that everyone can do.
Just some interesting to carders info
to plus my vouch community

I got recently a package of files found in a infected POS (POS hacked due to a weak rdp password)
Interface of a compromised POS used by a jeweller:
out.exe is a Ardamax Keylogger (ardamax.com) and vui qua.exe is a SFX archive who display this picture when executed:

And drop Pefect Keylogger (blazingtools.com) behind.
"vui qua" might be a Vietnamese phrase which translated is "so funny".
These two keyloggers are probably useless for the carder, the interesting file here is "mmon.exe" a ram scraper.
It scan each and every process looking for CC dumps thats been written to memory Track 1, 2.
If a Point Of Sale device is connected to the computer it will grab it's card data right away.
How? POS always use end to end encryption, the only place where it's not encrypted are inside the memory.
But.. the memory have limited storage so it overwrites the data all the time.
It's also a problem for mmon, because this crap have no loop feature and does not write inside a file.
POS Carders usually use better malware than this, but i got this so...
(mmon.exe, "Kartoxa" is probably the distorted version of the word "potato")
mmon scanning process.
test of mmon with a valid track two in memory
When a dump is found, the program do nothing with it, it just display the stuff on console.
The bad guys just connect to the POS via RDP, get dumps via mmon and write them out on magnetic stripe with a card writer.

(MSR606 USB Magnetic Stripe Reader Writer/Encoder)
Then use an embosser to make imprinted numbers on the card.
(A DXR 70C embosser)
And it's ready to use... in USA (Type 101)
The ones we have in Europe are 201 cards (pin and chip)
101 only need to swipes the card in a store and the cashier checks the 4 last digits on the card if they are corect.
Carders also use printers like Fargo to make fake identities.
Anyway, a POS malware have a high price, it's not a business that everyone can do.
Just some interesting to carders info
to plus my vouch community
Mailer-Daemon
Professional
- Messages
- 649
- Reaction score
- 118
- Points
- 43
OMG Im afraid you are way too advanced for this board... otherwise nice copypaste from FBI manual, yeah?
Mailer-Daemon
Professional
- Messages
- 649
- Reaction score
- 118
- Points
- 43
Why?
skorpionas
Member
- Messages
- 1
- Reaction score
- 0
- Points
- 1
vouch for me,help
benz-brabus
Professional
- Messages
- 672
- Reaction score
- 143
- Points
- 43
Do you have a template, but there is no 50 LR?
Ninja
Moderator
- Messages
- 2,306
- Reaction score
- 442
- Points
- 83
Update from our "friend":

u know alot of millionaries who act like that? lol
[07:55] 641743721: sup dickhead
[07:55] 641743721: im fuckin millionaire today
[07:56] Ninja: dickhead is ur fathers son. tell me something funny about ur millions. we need some laughts )
[07:56] cashdoe: im fuckin milionai
[07:56] cashdoe: r
[07:57] Ninja: thats all u wanted to say?
[07:57] cashdoe: ye bitch
u know alot of millionaries who act like that? lol
robertas_25
Member
- Messages
- 0
- Reaction score
- 19
- Points
- 18

