Hacker
Professional
- Messages
- 1,041
- Reaction score
- 852
- Points
- 113
Foreword. So that there was a performance just do.
Personally, I have been hanging out in the shadow sphere for several years, as they say nowadays. To be more precise, I mostly relate myself to carders. I have seen enchanting ups and downs, big money, various insider insights, loud scams among “friends”, hypes out of thin air, even creativity or perversion in one form or another in relation to someone or something from the dark theme.
But now, perhaps, not about me. Let's talk about the real world and essential things, what is relevant? where is the hype? where are the grandmas all the same spinning? on the other side of the monitor.
So, let's start with the fact that, at the moment, there are many ramifications in online carding, from banal driving from someone else's credit card of an American for $ 7-12 to auto refills from bank botnets with a financial turnover of $ 300,000-400,000 / month. I will try to touch on the hottest topics that everyone is discussing around at the moment, but it is not always clear to the end how it works for beginners, in one area or another, and even if they have vast experience behind them.
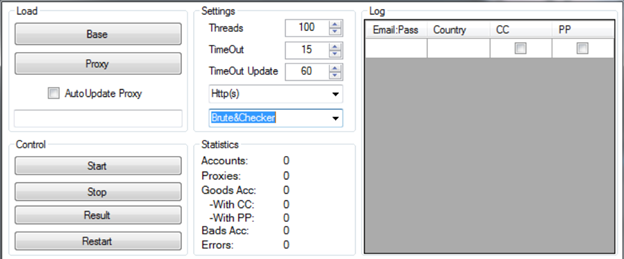
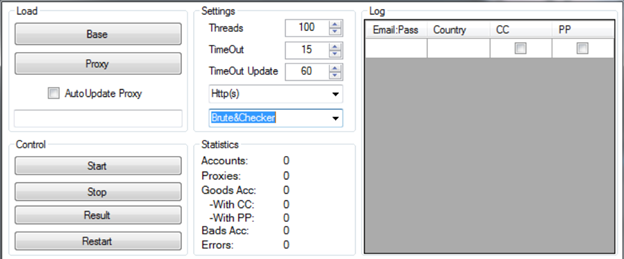
The first, which I would like to tell you about, this is driving from the "brute" accounts of various stores, quite a monotonous occupation, but having a significant reason for profit, given the degree of carded your office. What are brute accounts, this is the personal account of the site user, for example, ebay.com or amazon.com. Before starting to google what it is and what it is eaten with, it is worth considering one weighty moment, namely: the more famous the domain, those site - the more likely it is that with your little experience it is unlikely that anything can be done at all, unfortunately, the harsh reality. If you try yourself - then only on any low-fraud sites - of which there are a lot, you just need to show your imagination. And how to get brute accounts is already a completely different story, but in short I will say that - it is taken: encoder + server + good bases of the soap format: password,
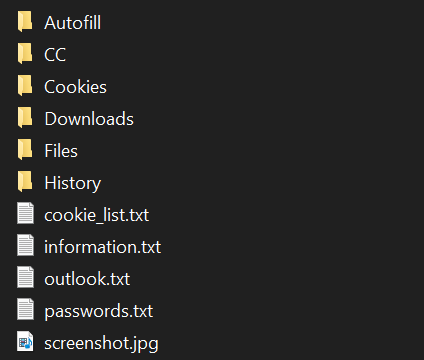
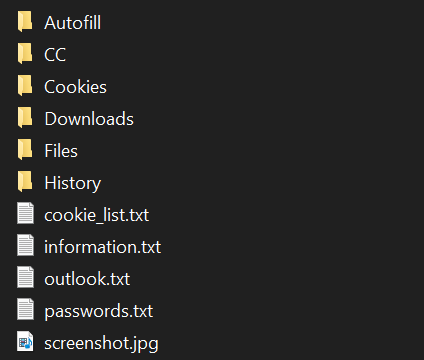
Second what they most often work with, now at the moment - these are logs from stealers. How it works: there are various malware programs that are distributed by traffic arbitrage, or through install exchanges, a more advanced class of young hackers. As a result, we have to buy the data of someone else's computer in the form of a neat archived file that carries a number of information, including cookies from the browser and logins passwords from the owner of the pc. It is more pleasant to work with such material for a number of reasons, one of which is that you can deceive fraud (security / protection system) by posing as the real owner of the log - your beloved. But there is also a significant disadvantage of this material, it is its availability and price. Our valiant hucksters do not always sell good material, passing it off as unique, at a price of $ 10 for one log. And I almost forgot for one more minus,
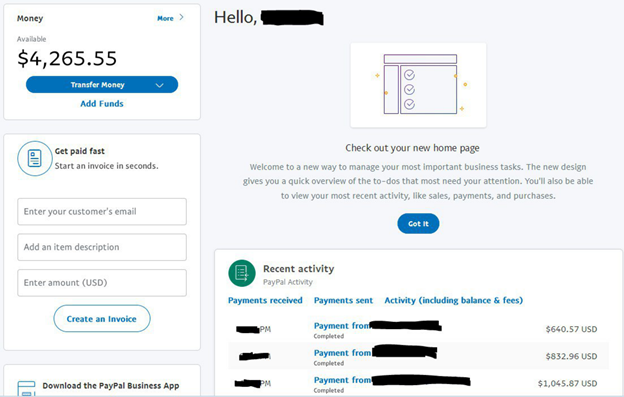
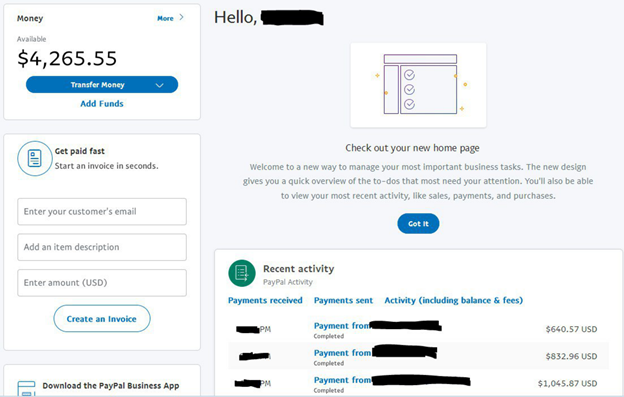
Third, it's not everyone's favorite PayPal trash. If you are a beginner and do not know what it is. Being in a frenzy while working with the so-called "stick" by the people, I noticed a regularity, those people who are not the first day in the subject, and the longer they work with this payment aggregator, have more and more money from it. And newcomers, who have come back to the stick, quit before starting. On my own behalf, the seeker will always find - this is an iron rule that must be adhered to 24/7.
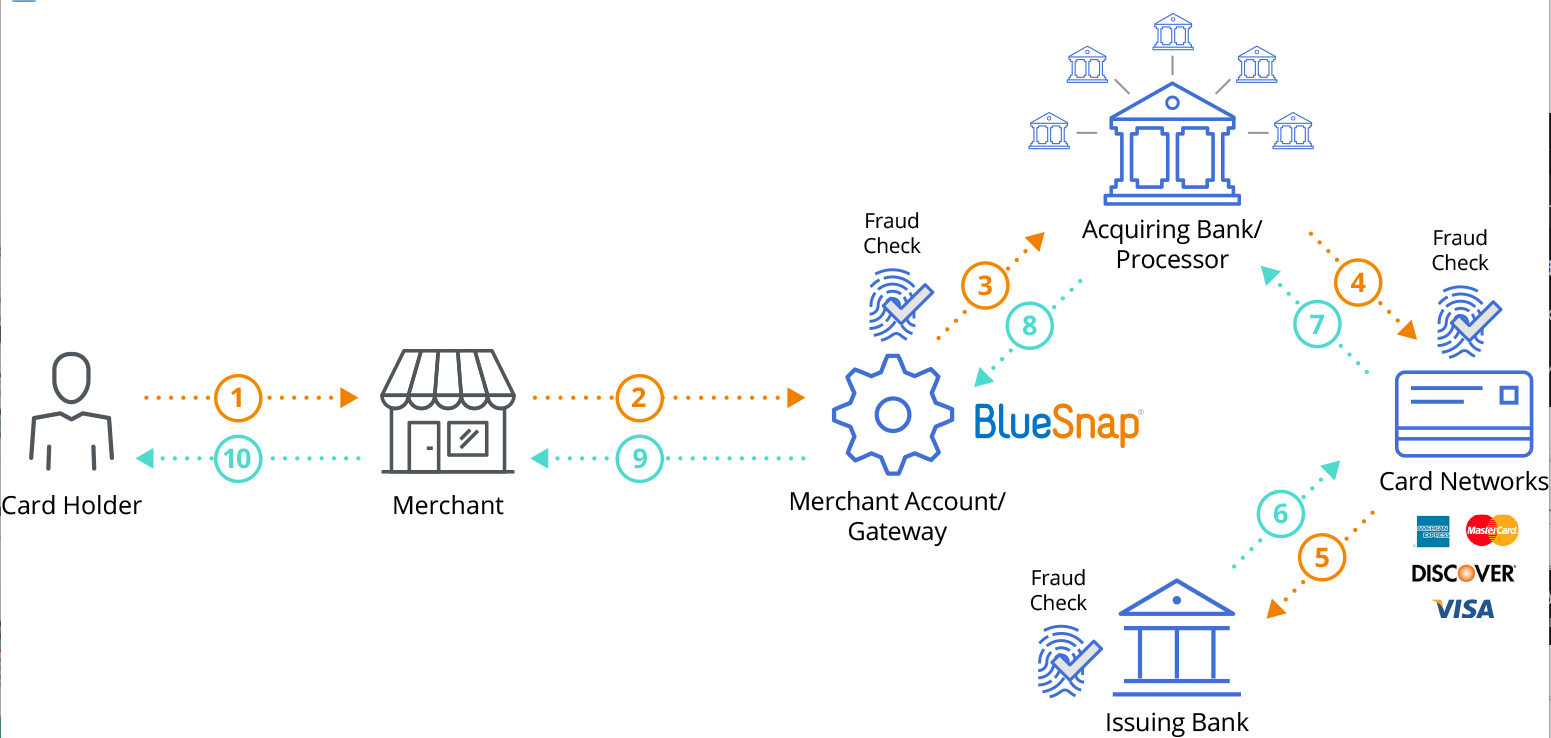
Then I would like to tell you about such a direction as ACH.
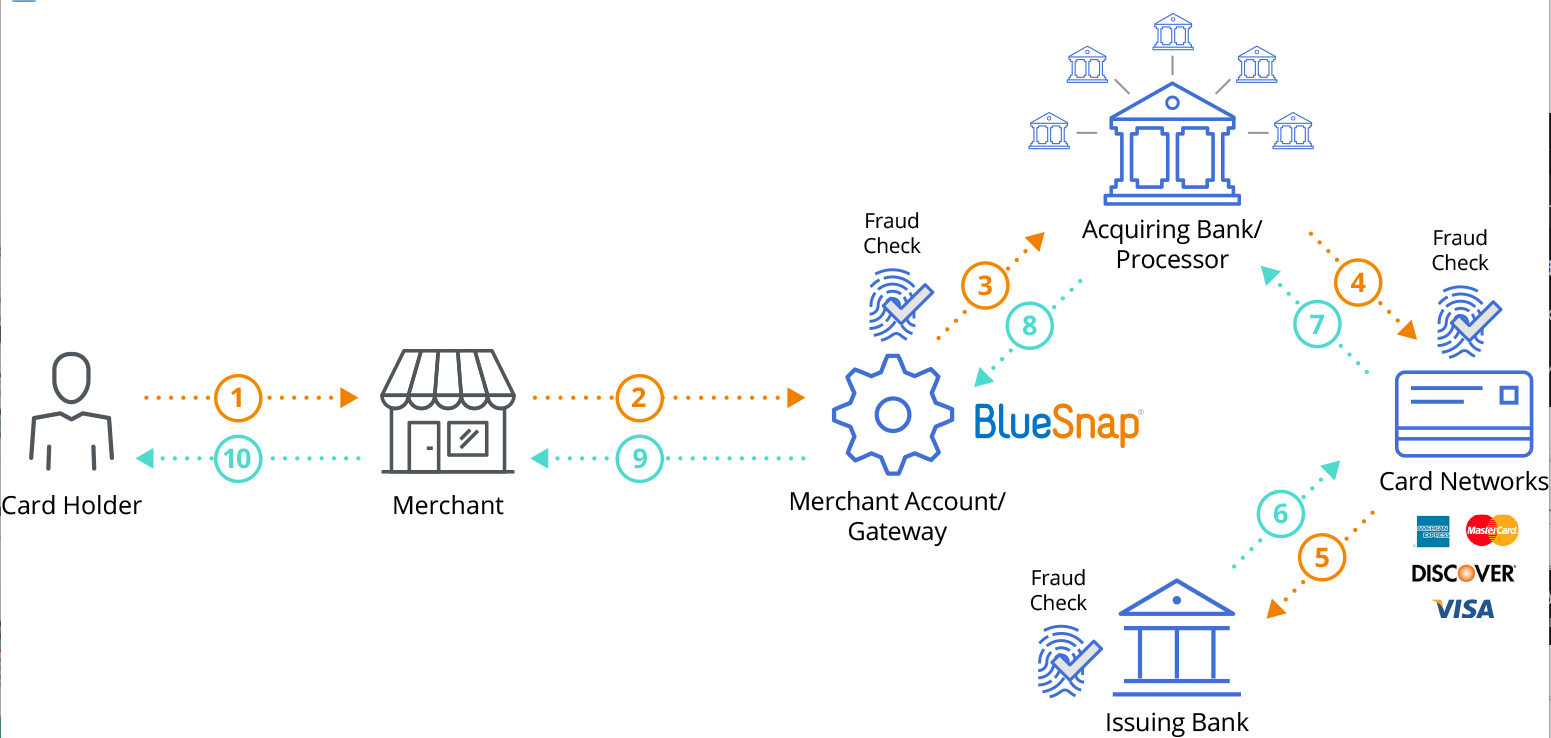
ACH is the most popular way to transfer money in the United States. If an American receives a Direct Deposit salary, then this is done through the ACN. If an American sets monthly payments to his insurance company, then they also go through the ASN. If he wants to transfer some of the money from his current account to a brokerage account or to a trading company, then the funds will also go through the ACN. Anyway, all Bill Pay, which the average American makes at least a dozen every month, go through the ACN. ASN is wherever there is cash flow.
At the moment, the most frequent thing carders come to most often is the search for their own personal pad office or the search for a method was dumped by usa banks. Conditionally: he brought money to the site, went through a ton of verification, scrolled the funds on the site, withdrew to his bank. This is just a very short description. In fact, there are so many nuances that sometimes it takes months to find such gaskets. Yes, and the material at the moment is still quite difficult to get, and if possible, then the horse price tag of a grief-huckster leaves much to be desired. It is even more difficult to get such material yourself, the brute + server method is used, but there is such a nuance - this is that these are BANKS and be healthy there for protection. Somewhere less, somewhere more, but in general, mining bank accounts is not an easy task. But the profits here are completely different and very serious.
Well, in conclusion, I want to tell you about such a direction as Botnets. This is definitely one of the most difficult areas in the shadow business. In order to get into this whole story with a bot, you need to study a ton of material, just stupidly in order to understand how it works and what depends on what. There are so many terms in this topic that when you and your friend talk about the topic of botnets, you can not hide your conversation from strangers, no one will understand you anyway, it's like conducting a dialogue in Chinese.
The most juicy topic of this trend is the final material that you get on the way out. Passing a mountain of information about what it is, you only need to know one thing: hVNC - in short, this is a certain module through which you can remotely and secretly connect to the PC of a random user, having previously infected him with a Trojan spyware. What is the juice, you ask? It's simple, you = the real owner of the browser / ip address / dns / pc hardware. Accordingly, any security system perceives you as the real owner of, for example, a bank account, or an Amazon account, or a trader's account on one of the largest investment fund platforms. Few? - and if I say that sms are also hijacked, but this is a completely separate topic. Those you have already imagined a picture of the possibilities of such material. A separate conversation is the topic of settings, those methods of getting yourself the very bots, but we'll talk about this later.

Personally, I have been hanging out in the shadow sphere for several years, as they say nowadays. To be more precise, I mostly relate myself to carders. I have seen enchanting ups and downs, big money, various insider insights, loud scams among “friends”, hypes out of thin air, even creativity or perversion in one form or another in relation to someone or something from the dark theme.
But now, perhaps, not about me. Let's talk about the real world and essential things, what is relevant? where is the hype? where are the grandmas all the same spinning? on the other side of the monitor.
So, let's start with the fact that, at the moment, there are many ramifications in online carding, from banal driving from someone else's credit card of an American for $ 7-12 to auto refills from bank botnets with a financial turnover of $ 300,000-400,000 / month. I will try to touch on the hottest topics that everyone is discussing around at the moment, but it is not always clear to the end how it works for beginners, in one area or another, and even if they have vast experience behind them.
The first, which I would like to tell you about, this is driving from the "brute" accounts of various stores, quite a monotonous occupation, but having a significant reason for profit, given the degree of carded your office. What are brute accounts, this is the personal account of the site user, for example, ebay.com or amazon.com. Before starting to google what it is and what it is eaten with, it is worth considering one weighty moment, namely: the more famous the domain, those site - the more likely it is that with your little experience it is unlikely that anything can be done at all, unfortunately, the harsh reality. If you try yourself - then only on any low-fraud sites - of which there are a lot, you just need to show your imagination. And how to get brute accounts is already a completely different story, but in short I will say that - it is taken: encoder + server + good bases of the soap format: password,
Second what they most often work with, now at the moment - these are logs from stealers. How it works: there are various malware programs that are distributed by traffic arbitrage, or through install exchanges, a more advanced class of young hackers. As a result, we have to buy the data of someone else's computer in the form of a neat archived file that carries a number of information, including cookies from the browser and logins passwords from the owner of the pc. It is more pleasant to work with such material for a number of reasons, one of which is that you can deceive fraud (security / protection system) by posing as the real owner of the log - your beloved. But there is also a significant disadvantage of this material, it is its availability and price. Our valiant hucksters do not always sell good material, passing it off as unique, at a price of $ 10 for one log. And I almost forgot for one more minus,
Third, it's not everyone's favorite PayPal trash. If you are a beginner and do not know what it is. Being in a frenzy while working with the so-called "stick" by the people, I noticed a regularity, those people who are not the first day in the subject, and the longer they work with this payment aggregator, have more and more money from it. And newcomers, who have come back to the stick, quit before starting. On my own behalf, the seeker will always find - this is an iron rule that must be adhered to 24/7.
Then I would like to tell you about such a direction as ACH.
ACH is the most popular way to transfer money in the United States. If an American receives a Direct Deposit salary, then this is done through the ACN. If an American sets monthly payments to his insurance company, then they also go through the ASN. If he wants to transfer some of the money from his current account to a brokerage account or to a trading company, then the funds will also go through the ACN. Anyway, all Bill Pay, which the average American makes at least a dozen every month, go through the ACN. ASN is wherever there is cash flow.
At the moment, the most frequent thing carders come to most often is the search for their own personal pad office or the search for a method was dumped by usa banks. Conditionally: he brought money to the site, went through a ton of verification, scrolled the funds on the site, withdrew to his bank. This is just a very short description. In fact, there are so many nuances that sometimes it takes months to find such gaskets. Yes, and the material at the moment is still quite difficult to get, and if possible, then the horse price tag of a grief-huckster leaves much to be desired. It is even more difficult to get such material yourself, the brute + server method is used, but there is such a nuance - this is that these are BANKS and be healthy there for protection. Somewhere less, somewhere more, but in general, mining bank accounts is not an easy task. But the profits here are completely different and very serious.
Well, in conclusion, I want to tell you about such a direction as Botnets. This is definitely one of the most difficult areas in the shadow business. In order to get into this whole story with a bot, you need to study a ton of material, just stupidly in order to understand how it works and what depends on what. There are so many terms in this topic that when you and your friend talk about the topic of botnets, you can not hide your conversation from strangers, no one will understand you anyway, it's like conducting a dialogue in Chinese.
The most juicy topic of this trend is the final material that you get on the way out. Passing a mountain of information about what it is, you only need to know one thing: hVNC - in short, this is a certain module through which you can remotely and secretly connect to the PC of a random user, having previously infected him with a Trojan spyware. What is the juice, you ask? It's simple, you = the real owner of the browser / ip address / dns / pc hardware. Accordingly, any security system perceives you as the real owner of, for example, a bank account, or an Amazon account, or a trader's account on one of the largest investment fund platforms. Few? - and if I say that sms are also hijacked, but this is a completely separate topic. Those you have already imagined a picture of the possibilities of such material. A separate conversation is the topic of settings, those methods of getting yourself the very bots, but we'll talk about this later.

