Carder
Professional
- Messages
- 2,635
- Reaction score
- 2,067
- Points
- 113
Pentesting = Basically Cracking
I'm cracking for a while, now I want to share with you how to check Accounts properly Included Screenshot, Tools and Useful Links to start Checking Today !
You gonna learn the basic of checking and how you can profit from it. Hope you enjoy my work
Table of contents:
What is Cracking?
Openbullet
Combo, Proxy, Config, RDP
Start Cracking
Make Profit
Conclusion
What is Cracking?
Basically said you download an account list use a software (checker) that tries to
log into the account with your ip or proxy and if its correct it shows as a hit.
Openbullet
Openbullet is one of the most popular program used for Cracking accounts nowday, very stable and up to date.
Its included many feature with GUI interface, easy to use.
Download Links:
- OB Standard (supported only .loli config): https://github.com/openbullet/openbullet/releases
- OB Anomaly version (ability to use .anom Config): https://github.com/PurityWasHere/Anomaly-Mod-Hosting
PS: run Anomaly Updater.exe to download the latest OB Anomaly
- OB v1.2.0 (ability to use encryped config .lolix):
Combo, Proxy, Config, RDP
Combo
Combo/ComboList: A list of Username assword or Email
assword or Email assword, mostly saved on a text file.
assword, mostly saved on a text file.
Where I can get combo?
- Using SQL injection methods.
- Paying for private combo or Editing service.
You can find a bunch of tool to edit your combo :https://cracked.to/Forum-Pentesting-Tools (run it on VM or Sandboxies)
Proxy
For cracking, its a list of IP ort / IP
ort / IP ort:User
ort:User ass, mostly saved on a text file.
ass, mostly saved on a text file.
There are three different main types of proxies: HTTP / SOCKS4 / SOCKS5
Proxies are important because without them you will be limited on how many attempts you can make while cracking accountss.
Where I can get proxy?
- FREE: https://proxyscrape.com/free-proxy-list (Socks4 are recommended)
- Paid: Fineproxy.org, proxiware.com, smartproxy.com
How to choose the best proxy? It depends on your budget and the targeted site.
Config
Simply explained, what you use to crack a specific site, for example if I want netflix accounts I use a netflix config.
Explain some words used for config:
- Proxyless: without proxy
- Capture: capture information about the account like type of the sub / date of expiration / amount of points
- Captchaless: a config that bypass captcha using a private API.
RDP
(Remote Desktop Protocol) RDP is a network communications protocol developed by Microsoft, which allows users to remotely connect to another computer.
It very important to use RDP when cracking for the speed.
You can still use your PC for cracking, but its better to buy one for cheap like only 5$
Start Cracking
If you use your PC, turn on the VPN.
First, save all your config on "Config" folder.
Run openbullet, and click on rescan to load your configs
Conclusion
Cracking still a profitable business that need time and work, dont expect high result at the first time but after gain reputation and customer u gonna make good cash easly in.
? Sites for Begginers to Learn Cyber Hacking and Security with links ?
#mostrequested
EnigmaGroup
 www.enigmagroup.org
www.enigmagroup.org
Exploit Exercises

 exploit-exercises.com
exploit-exercises.com
Google Gruyere
Gh0st Lab
Hack This Site

 www.hackthissite.org
www.hackthissite.org
HackThis
HackQuest
Hack.me
 hack.me
hack.me
Hacking-Lab
 www.hacking-lab.com
www.hacking-lab.com
Hacker Challenge
Hacker Test
hACME Game
Hax.Tor
OverTheWire
 www.overthewire.org
www.overthewire.org
pwn0
RootContest
Root Me
 www.root-me.org
www.root-me.org
Security Treasure Hunt
Smash The Stack
TheBlackSheep and Erik
ThisIsLegal
 thisislegal.com
thisislegal.com
Try2Hack
WabLab
XSS: Can You XSS This?
XSS: ProgPHP
DigitalCorpora
Digital Forensics Tool Testing Images
DFRWS 2014 Forensics Rodeo
Linux LEO Supplemental Files
 linuxleo.com
linuxleo.com
volatility memory samples
ISFCE Sample Practical Exercise
ForGe Forensic test image generator

 github.com
github.com
Network Forensics
Wireshark Sample Captures
Wireshark Network Analysis Book Supplements
pcapr
PacketLife Capture Collection
 packetlife.net
packetlife.net
DigitalCorpora Packet Dumps
Evil Fingers PCAP Challenges
 www.evilfingers.com
www.evilfingers.com
PCAPS Repository

 github.com
github.com
Chris Sanders Packet Captures
 chrissanders.org
chrissanders.org
Tcpreplay Sample Captures
Enron Email Dataset
MAWI Working Group Traffic Archive
LBNL-FTP-PKT
Malware Analysis
Open Malware / Offensive Computing
Contagio
VX Heaven
VirusShare.com / VXShare
 virusshare.com
virusshare.com
VXVault
MalShare
Virusign
 www.virusign.com
www.virusign.com
theZoo / Malware DB
malc0de
FakeAVs blog
malware_traffic

Georgia Tech malrec page
Kernelmode Forum
Malware Hub Forum

 malwaretips.com
malwaretips.com
MalwareBlacklist.com
Joxean Koret’s List
Sucuri Research Labs
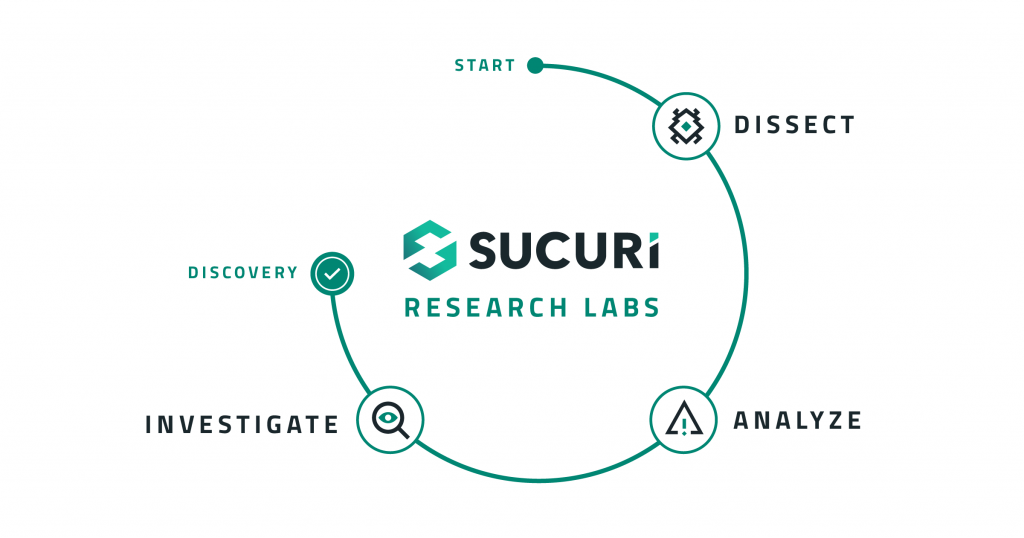
 labs.sucuri.net
labs.sucuri.net
CLEAN MX realtime database
 support.clean-mx.de
support.clean-mx.de
Contagio Mobile Malware
 contagiominidump.blogspot.com
contagiominidump.blogspot.com
Android Sandbox
maltrieve
HoneyDrive

 bruteforce.gr
bruteforce.gr
Online and CTFs
Honeynet Challenges
I Smell Packets

Network Forensics Puzzle contest
 forensicscontest.com
forensicscontest.com
DEF CON CTF Archive
 www.defcon.org
www.defcon.org
DFRWS
I'm cracking for a while, now I want to share with you how to check Accounts properly Included Screenshot, Tools and Useful Links to start Checking Today !
You gonna learn the basic of checking and how you can profit from it. Hope you enjoy my work
Table of contents:
What is Cracking?
Openbullet
Combo, Proxy, Config, RDP
Start Cracking
Make Profit
Conclusion
What is Cracking?
Basically said you download an account list use a software (checker) that tries to
log into the account with your ip or proxy and if its correct it shows as a hit.
Openbullet
Openbullet is one of the most popular program used for Cracking accounts nowday, very stable and up to date.
Its included many feature with GUI interface, easy to use.
Download Links:
- OB Standard (supported only .loli config): https://github.com/openbullet/openbullet/releases
- OB Anomaly version (ability to use .anom Config): https://github.com/PurityWasHere/Anomaly-Mod-Hosting
PS: run Anomaly Updater.exe to download the latest OB Anomaly
- OB v1.2.0 (ability to use encryped config .lolix):
Combo, Proxy, Config, RDP
Combo
Combo/ComboList: A list of Username
Where I can get combo?
- Using SQL injection methods.
- Paying for private combo or Editing service.
You can find a bunch of tool to edit your combo :https://cracked.to/Forum-Pentesting-Tools (run it on VM or Sandboxies)
Proxy
For cracking, its a list of IP
There are three different main types of proxies: HTTP / SOCKS4 / SOCKS5
Proxies are important because without them you will be limited on how many attempts you can make while cracking accountss.
Where I can get proxy?
- FREE: https://proxyscrape.com/free-proxy-list (Socks4 are recommended)
- Paid: Fineproxy.org, proxiware.com, smartproxy.com
How to choose the best proxy? It depends on your budget and the targeted site.
Config
Simply explained, what you use to crack a specific site, for example if I want netflix accounts I use a netflix config.
Explain some words used for config:
- Proxyless: without proxy
- Capture: capture information about the account like type of the sub / date of expiration / amount of points
- Captchaless: a config that bypass captcha using a private API.
RDP
(Remote Desktop Protocol) RDP is a network communications protocol developed by Microsoft, which allows users to remotely connect to another computer.
It very important to use RDP when cracking for the speed.
You can still use your PC for cracking, but its better to buy one for cheap like only 5$
Start Cracking
If you use your PC, turn on the VPN.
First, save all your config on "Config" folder.
Run openbullet, and click on rescan to load your configs
Conclusion
Cracking still a profitable business that need time and work, dont expect high result at the first time but after gain reputation and customer u gonna make good cash easly in.
? Sites for Begginers to Learn Cyber Hacking and Security with links ?
#mostrequested
EnigmaGroup
The Enigma Group - The Enigma Group
The Enigma Group's main goal is to increase user awareness in web and server security by teaching them how to write secure code, how to audit code, and how to exploit code. Remember, by knowing your enemy, you can defeat your enemy! The Enigma Group, Web Security Training
Exploit Exercises

Homepage One - exploit-exercises.com
The self-instruction book is good because it quickly immerses you in the topic. You will start coding almost the day you open the book.
 exploit-exercises.com
exploit-exercises.com
Google Gruyere
Gh0st Lab
Hack This Site

HackThisSite
HackThisSite.org is a free, safe and legal training ground for hackers to test and expand their ethical hacking skills with challenges, CTFs, and more.
HackThis
HackQuest
Hack.me
Hack.me · The house of rising sandbox
Hack.me is a free community based project powered by eLearnSecurity. The community can build, host and share vulnerable web application code for educational and research purposes.The platform is available without any restriction to any party interested in Web Application Security: students...
Hacking-Lab
Hacking-Lab
Hacker Challenge
Watch Free Old and Young Porn Videos and Sex Clips Online
Free Old and Young porn here! Check out the best Old and Young porn tube with thousands of high quality sex videos.
www.dareyourmind.net
Hacker Test
hACME Game
5分快三怎么推算大小单双-大发福彩快三-快三江苏今天开奖结果-天天快三网安全么
中国彩票大发福彩快三计划提供5分快三怎么推算大小单双,福彩3D彩票,双色球福利彩票,一分钟一期的快三app,一分钟快3全天计划,一分快三计划在线网页,快3全天实时人工计划,一分快三金牌导师。
www.hacmegame.org
Hax.Tor
HAX.TOR :: Hacking Challenges - Free Shell Account - Security
Hacking Challenges - challenges, riddles, exploiting, funny pictures, music
hax.tor.hu
OverTheWire
OverTheWire: Wargames
pwn0
RootContest
Root Me
Welcome [Root Me : Hacking and Information Security learning platform]
Root Me is a platform for everyone to test and improve knowledge in computer security and hacking.
 www.root-me.org
www.root-me.org
Security Treasure Hunt
Smash The Stack
TheBlackSheep and Erik
ThisIsLegal
ThisisLegal.com - Are You?
ThisisLegal - a hacker wargames site with forums, tutorials and more
Try2Hack
WabLab
XSS: Can You XSS This?
XSS: ProgPHP
DigitalCorpora
Digital Forensics Tool Testing Images
DFRWS 2014 Forensics Rodeo
Linux LEO Supplemental Files
Linux LEO
volatility memory samples
ISFCE Sample Practical Exercise
ForGe Forensic test image generator
GitHub - hannuvisti/forge: ForGe Forensic test image generator
ForGe Forensic test image generator. Contribute to hannuvisti/forge development by creating an account on GitHub.
Network Forensics
Wireshark Sample Captures
Wireshark Network Analysis Book Supplements
pcapr
PacketLife Capture Collection
Packet Captures - PacketLife.net
DigitalCorpora Packet Dumps
Evil Fingers PCAP Challenges
EvilFingers - PCAP Challenge
PCAPS Repository
GitHub - markofu/pcaps: Public Repository of all Publicly Available Packet Captures that I've used or come across
Public Repository of all Publicly Available Packet Captures that I've used or come across - markofu/pcaps
Chris Sanders Packet Captures
Packets | Chris Sanders
Tcpreplay Sample Captures
Sample Captures
List of sample network capture files for use with Tcpreplay suite
tcpreplay.appneta.com
Enron Email Dataset
MAWI Working Group Traffic Archive
LBNL-FTP-PKT
Malware Analysis
Open Malware / Offensive Computing
Contagio
VX Heaven
VirusShare.com / VXShare
VirusShare.com
VXVault
MalShare
Virusign
Virusign - Home
theZoo / Malware DB
theZoo - A Live Malware Repository
A repository of LIVE malwares for your own joy and pleasure
ytisf.github.io
malc0de
FakeAVs blog
malware_traffic

malware-traffic-analysis.net
malware-traffic-analysis.net
Georgia Tech malrec page
Kernelmode Forum
Malware Hub Forum

Malware Hub
 malwaretips.com
malwaretips.com
MalwareBlacklist.com
Joxean Koret’s List
Sucuri Research Labs
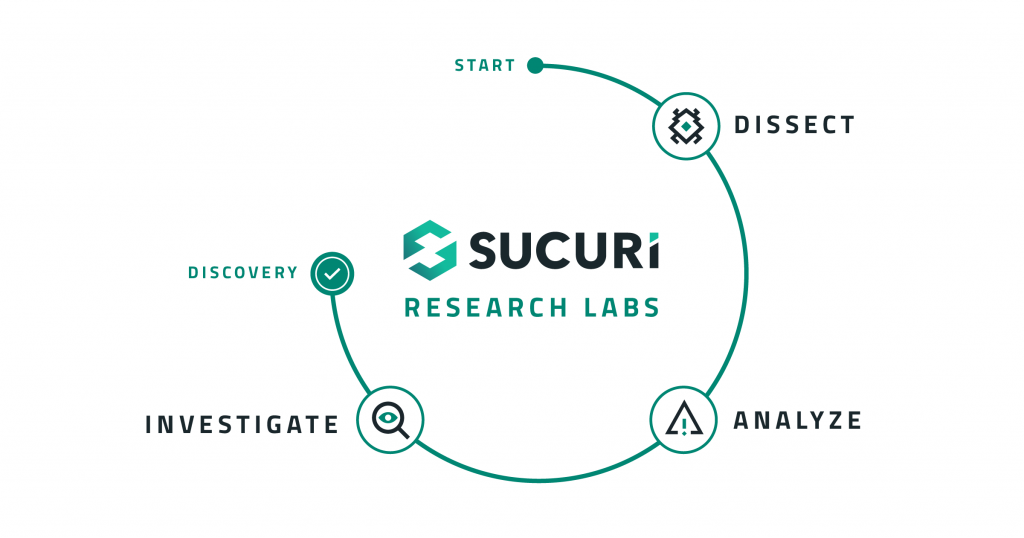
About Sucuri Labs - Sucuri Labs
What is Sucuri Labs? Here at Sucuri Labs is where we share our technical research. We are a group of website security professionals who are passionate about discovering emerging web-based malware and software vulnerabilities. Not only do we create tools and detection rules for our customers, we...
CLEAN MX realtime database
Malware - Clean MX - realtime
clean-mx , a spam and virus management system for mail servers
Contagio Mobile Malware
contagio mobile
Android Sandbox
maltrieve
HoneyDrive

HoneyDrive
HoneyDrive is the premier honeypot Linux distro. It is a virtual appliance (OVA) with Xubuntu Desktop 12.04.4 LTS edition installed. It contains over 10 pre-installed and pre-configured honeypot so…
Online and CTFs
Honeynet Challenges
I Smell Packets
Network Forensics Puzzle contest
Puzzles! – Network Forensics Puzzle Contest
 forensicscontest.com
forensicscontest.com
DEF CON CTF Archive
DEF CON® Hacking Conference - Capture the Flag Archive
A page devoted to collecting accounts, walk throughs and other resources of Capture the Flag at DEF CON over the years, not only for history's sake but so the uninformed can better grasp the epic journey that teams must face on the road to CTF victory!
DFRWS



