Lord777
Professional
- Messages
- 2,576
- Reaction score
- 1,565
- Points
- 113
N-able's Advanced Monitoring Agent has become a new weapon in the hands of hackers.
The well-known Iranian hacker group MuddyWater has launched a new campaign of cyber attacks using targeted phishing techniques against two Israeli organizations. The purpose of this malicious campaign is to deploy the legitimate remote management tool Advanced Monitoring Agent from N-able.
According to information provided by experts from Deep Instinct , the attacks demonstrate updated tactics and techniques (TTPs), especially in comparison with the previous MuddyWater activity.
In the past, hackers have used similar methods to distribute other remote access tools, such as ScreenConnect and RemoteUtilities. However, the innovation of the latest attacks is the use of software produced by N-able for remote monitoring, which emphasizes the effectiveness of the group's almost unchanged modus operandi.
The data obtained by the Deep Instinct researchers was also confirmed by Group-IB in their mini-report.
The MuddyWater group, which has been operating since 2017, is an element allegedly subordinate to the Iranian Ministry of Intelligence and Security. The MuddyWater hackers are also linked to other groups like OilRig and Scarred Manticore that specialize in cyber espionage.
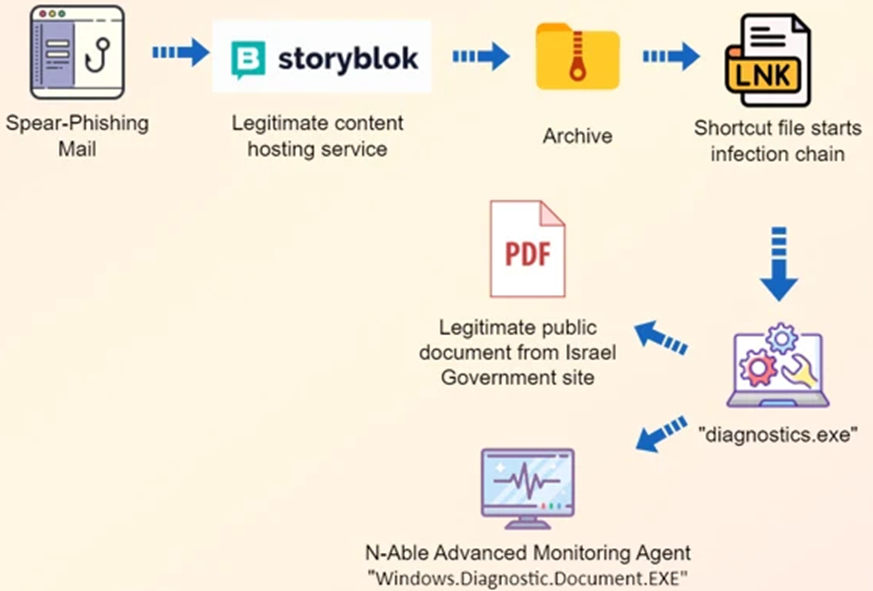
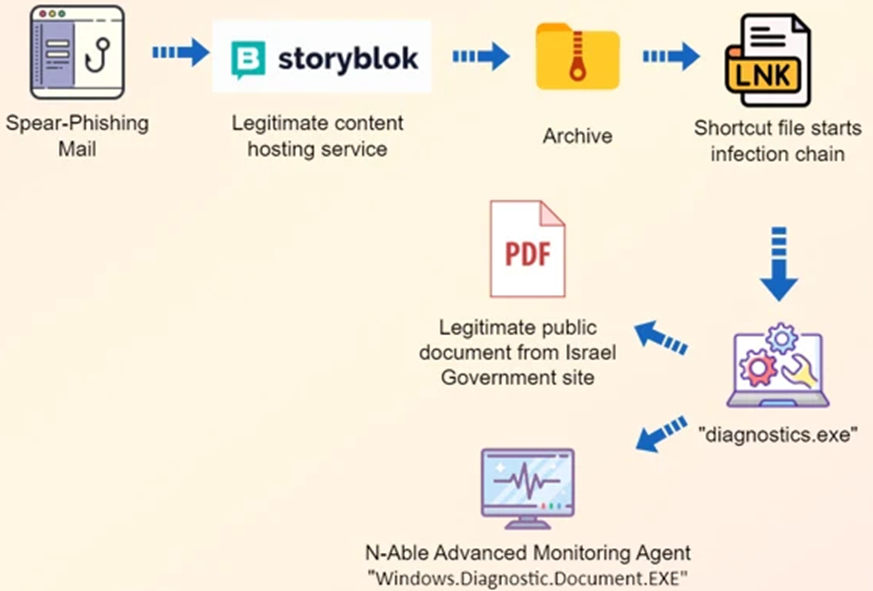
In previous campaigns, attacks were carried out through phishing emails with direct links or archive attachments with HTML, PDF, and RTF content, which led to downloading remote management tools. In the current campaign, we also noticed the use of the Storyblok hosting service to launch a multi-stage infection.
As Deep Instinct's Simon Kenin pointed out, attackers now have hidden files and LNK shortcuts packed in archives that trigger the infection process, as well as executable files that display a decoy document in the foreground of the operating system interface, while malicious actions are performed in the background using Advanced Monitoring Agent.
Attack pattern
In addition to improving tactics, Deep Instinct revealed that the MuddyWater group uses the new MuddyC2Go C2 infrastructure, which is the successor to MuddyC3 and PhonyC2. This functionality update is evidence of the increased cyber capabilities of Iranian national hackers.
The well-known Iranian hacker group MuddyWater has launched a new campaign of cyber attacks using targeted phishing techniques against two Israeli organizations. The purpose of this malicious campaign is to deploy the legitimate remote management tool Advanced Monitoring Agent from N-able.
According to information provided by experts from Deep Instinct , the attacks demonstrate updated tactics and techniques (TTPs), especially in comparison with the previous MuddyWater activity.
In the past, hackers have used similar methods to distribute other remote access tools, such as ScreenConnect and RemoteUtilities. However, the innovation of the latest attacks is the use of software produced by N-able for remote monitoring, which emphasizes the effectiveness of the group's almost unchanged modus operandi.
The data obtained by the Deep Instinct researchers was also confirmed by Group-IB in their mini-report.
The MuddyWater group, which has been operating since 2017, is an element allegedly subordinate to the Iranian Ministry of Intelligence and Security. The MuddyWater hackers are also linked to other groups like OilRig and Scarred Manticore that specialize in cyber espionage.
In previous campaigns, attacks were carried out through phishing emails with direct links or archive attachments with HTML, PDF, and RTF content, which led to downloading remote management tools. In the current campaign, we also noticed the use of the Storyblok hosting service to launch a multi-stage infection.
As Deep Instinct's Simon Kenin pointed out, attackers now have hidden files and LNK shortcuts packed in archives that trigger the infection process, as well as executable files that display a decoy document in the foreground of the operating system interface, while malicious actions are performed in the background using Advanced Monitoring Agent.
Attack pattern
In addition to improving tactics, Deep Instinct revealed that the MuddyWater group uses the new MuddyC2Go C2 infrastructure, which is the successor to MuddyC3 and PhonyC2. This functionality update is evidence of the increased cyber capabilities of Iranian national hackers.

