Father
Professional
- Messages
- 2,602
- Reaction score
- 850
- Points
- 113
Hi!
A simple thermal imager is enough
You entered your password, then simply put your smartphone away. Scientists from the University of Stuttgart, together with colleagues from the Ludwig-Maximilian University of Munich, proved that this is not safe.
Armed with a compact thermal imager, the scientists were able to read the entered password from the smartphone screen. After 15 seconds of entering, the four-digit PIN code was recognized in 90% of cases. And the graphic key was almost always guessed, even after 30 seconds.
If you hide the thermal imager in your sleeve or disguise it as a toy, no one will think that the person passing by the smartphone was reading the code.
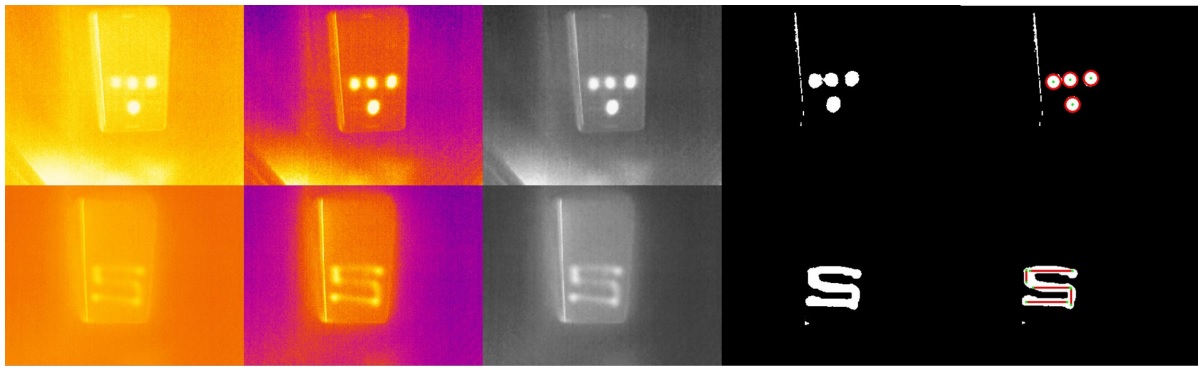
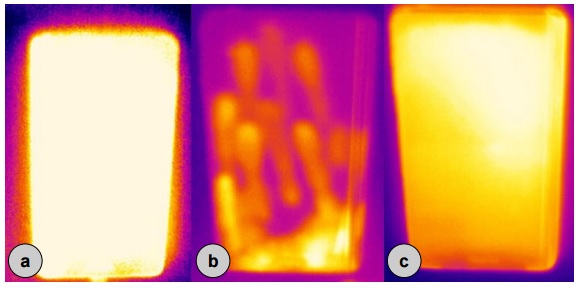
To protect themselves, scientists suggested random swipes on the screen (b). Among the hardware methods – increasing the brightness of the display for a few seconds (a) or a sharp increase in the load on the processor (c). In the thermal imager, this looks like this:
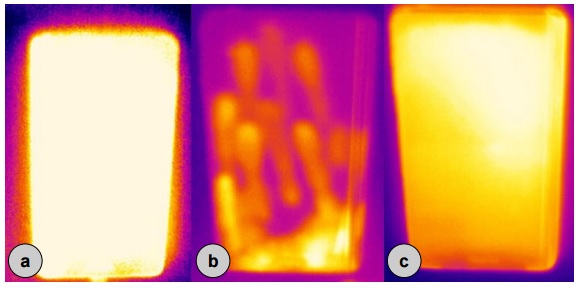
You can calculate the password from oil trails
The high-resolution camera is able to take a high-quality picture, which will be able to recognize oil marks from fingers on the smartphone screen. Back in 2010, experts from the University of Pennsylvania described this method.
Today, even an amateur camera or a good smartphone can do this. It won't be hard to pretend that you're shooting your food for Instagram instead of your colleague's smartphone at lunch.
This method best recognizes traces of entering a graphic key, and a little more difficult – a PIN code or an alphanumeric password. If it's not a word, phrase, or date of birth, there will be too many variations in the order of letters and numbers.
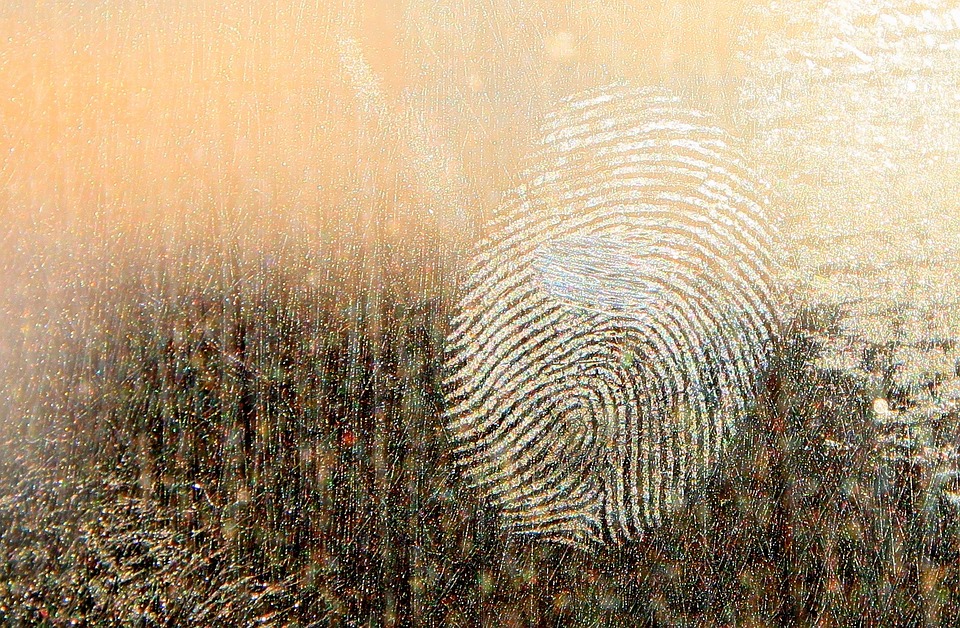
In general, the Android graphic key is the most insecure one
The more complex the graphic key, the easier it is to recognize it, researchers say. It is enough to sit on the side of the victim at a distance of up to 5 meters and simply shoot the unblocking process on video.
The video is then uploaded to a special app. It analyzes finger movements and offers up to five key options. In 95% of cases, one of these keys is correct.
Your password can "leak" the Wi-Fi network
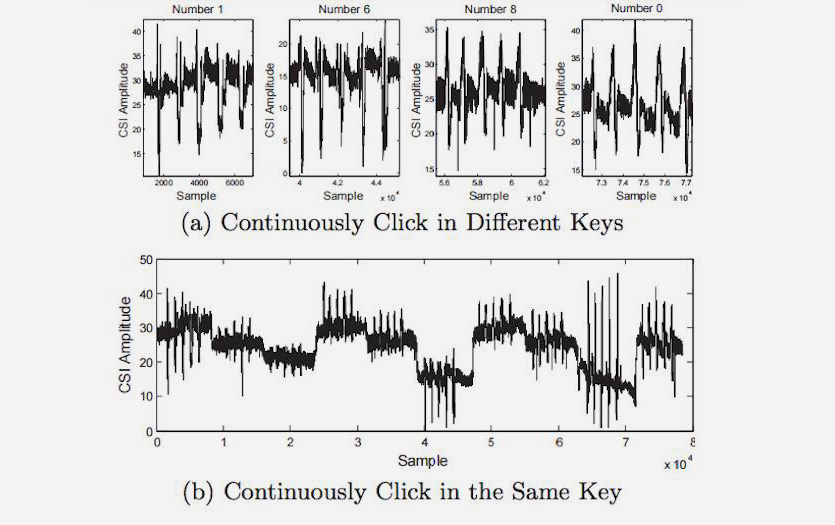
Former technical director of SpringSource, Adrian Collier, toldhow to intercept a PIN code using Wi-Fi signal analysis. He named the technology WindTalker.
Collier found that finger movements on the screen affect the Wi-Fi signal. If an attacker creates an access point, they will be able to track this micro-interference.
In the experiment, Collier managed to hack the account of Alipay, the payment system of Alibaba. The app gave him three password options, and one of them came up.
The accuracy of the method is 68%. The more data, the more accurate the analysis. The more input attempts the app allows, the more likely it is to enter the correct password.
Movements of a fitness tracker or smartwatch also "pass" the password

If a hacker installs a special scanner near your workplace, ATM, or terminal, they can get a password or PIN code by tracking the movement of your hands on a fitness tracker or smart watch.
The experiment was conducted by employees of the Stevens Institute of Technology and Binghamton University (USA). They developed a scanner that tracks electromagnetic radiation from sensors in smart watches and trackers. Data from the scanner was transmitted via Bluetooth.
The scan results were processed in an application that detects up to 5 thousand key movements. Two dozen users, two models of smart watches and a fitness bracelet with a standard nine-axis accelerometer were used to create the algorithm.
On the first attempt, the password was recognized in 80% of cases, and on the second attempt (if the user enters the same combination twice) – in 90%. The more sensors in a wearable device (gyroscopes, magnetometers, accelerometers), the higher the accuracy. The position of the hand does not affect it.
Even screenshots will reveal your password
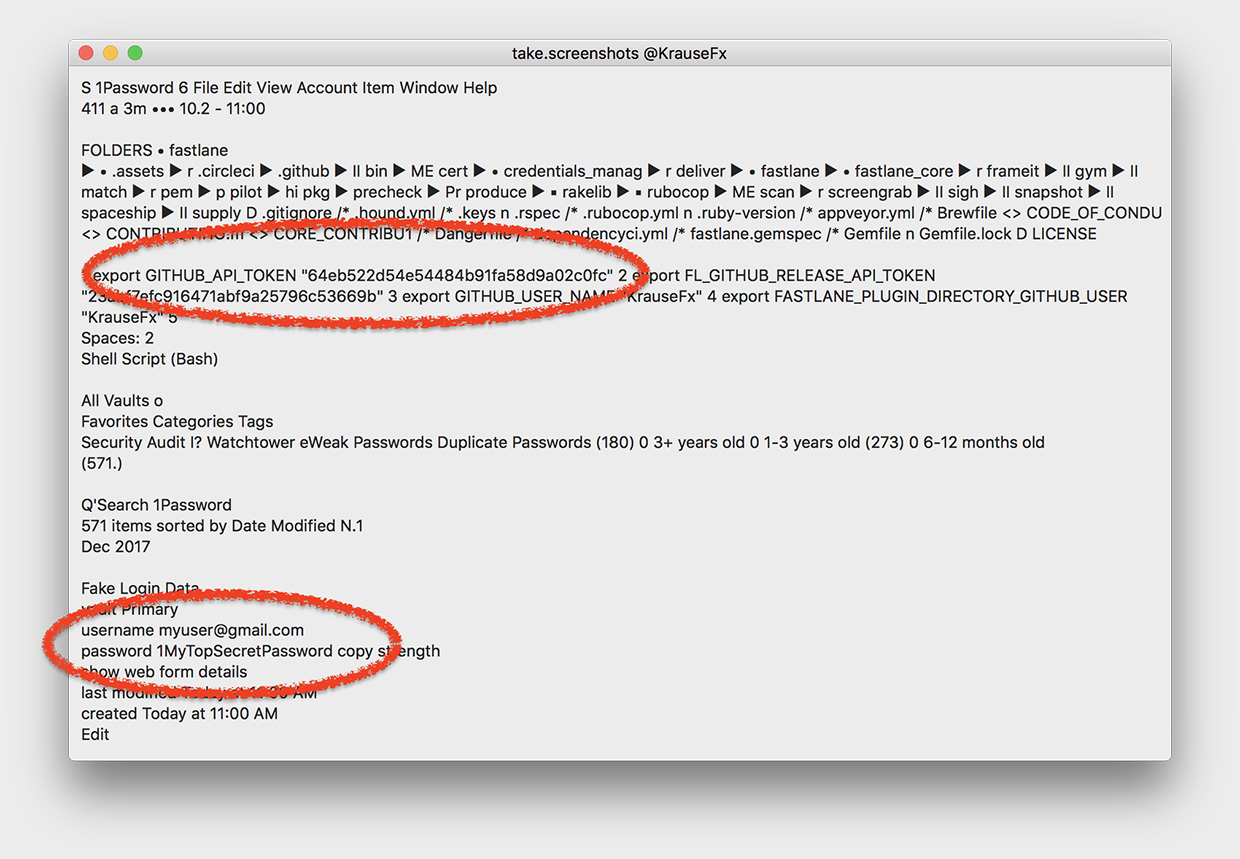
Your computer can technically take a screenshot at any time, including when you enter your password. The opportunity was discovered back in November 2017 by the founder of Fastlane Tools, Felix Krause.
The CGWindowListCreateImage function takes a screenshot. It doesn't require user permission.
A virus that takes screenshots can run in the background. It will still have access to literally every pixel.
Moving on to the real hack. MITM attacks
MITM (Man-in-the-middle) – man-in-the-middle attacks. Most often, sniffers like Intercepter-NG are used to intercept passwords and cookies using attacks of this type .
Intercepted data allows you to log in to other people's accounts, view uploaded files, and so on. In addition, the app allows you to forcibly delete the user's cookies, forcing them to re-log in.
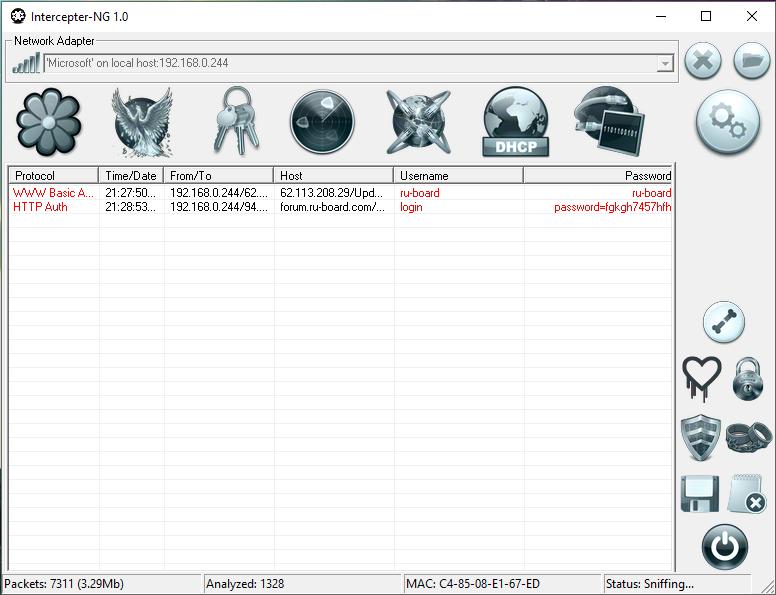
Previously, the tool allowed you to intercept even passwords from iCloud. But Apple developers have already fixed this.
Other ways to intercept traffic (including passwords) also exist. Even if they are passwords from HTTPS resources. The main thing is that the victim's device is located on the same Wi-Fi network as the hacker's device.
iphones.ru
This article is presented for informational purposes only and does not carry a call to action. All information is aimed at protecting readers from illegal actions.
A simple thermal imager is enough
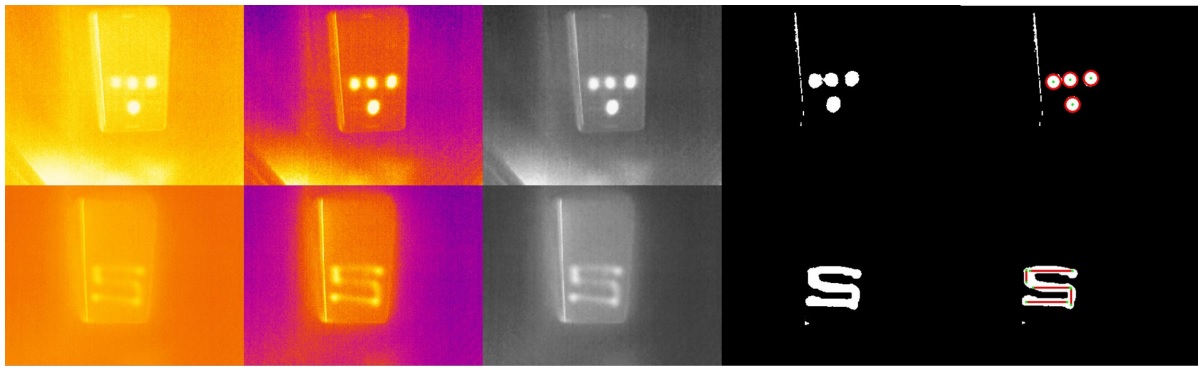
You entered your password, then simply put your smartphone away. Scientists from the University of Stuttgart, together with colleagues from the Ludwig-Maximilian University of Munich, proved that this is not safe.
Armed with a compact thermal imager, the scientists were able to read the entered password from the smartphone screen. After 15 seconds of entering, the four-digit PIN code was recognized in 90% of cases. And the graphic key was almost always guessed, even after 30 seconds.
If you hide the thermal imager in your sleeve or disguise it as a toy, no one will think that the person passing by the smartphone was reading the code.
To protect themselves, scientists suggested random swipes on the screen (b). Among the hardware methods – increasing the brightness of the display for a few seconds (a) or a sharp increase in the load on the processor (c). In the thermal imager, this looks like this:
You can calculate the password from oil trails
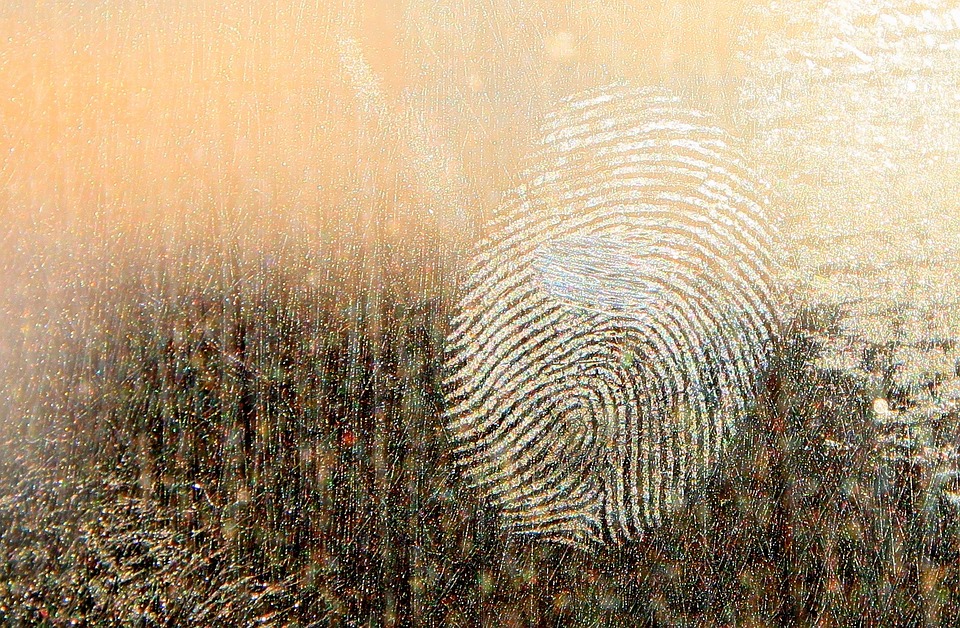
The high-resolution camera is able to take a high-quality picture, which will be able to recognize oil marks from fingers on the smartphone screen. Back in 2010, experts from the University of Pennsylvania described this method.
Today, even an amateur camera or a good smartphone can do this. It won't be hard to pretend that you're shooting your food for Instagram instead of your colleague's smartphone at lunch.
This method best recognizes traces of entering a graphic key, and a little more difficult – a PIN code or an alphanumeric password. If it's not a word, phrase, or date of birth, there will be too many variations in the order of letters and numbers.
In general, the Android graphic key is the most insecure one
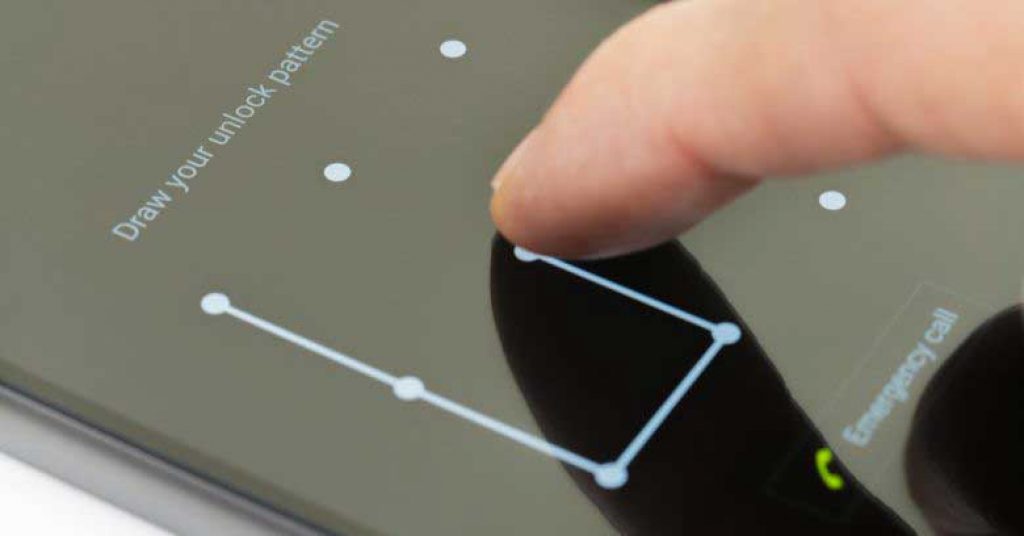
The more complex the graphic key, the easier it is to recognize it, researchers say. It is enough to sit on the side of the victim at a distance of up to 5 meters and simply shoot the unblocking process on video.
The video is then uploaded to a special app. It analyzes finger movements and offers up to five key options. In 95% of cases, one of these keys is correct.
Your password can "leak" the Wi-Fi network
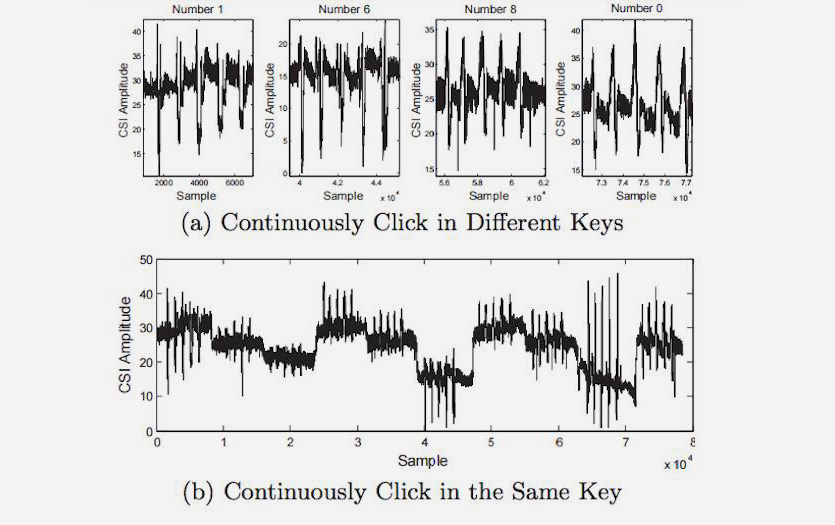
Former technical director of SpringSource, Adrian Collier, toldhow to intercept a PIN code using Wi-Fi signal analysis. He named the technology WindTalker.
Collier found that finger movements on the screen affect the Wi-Fi signal. If an attacker creates an access point, they will be able to track this micro-interference.
In the experiment, Collier managed to hack the account of Alipay, the payment system of Alibaba. The app gave him three password options, and one of them came up.
The accuracy of the method is 68%. The more data, the more accurate the analysis. The more input attempts the app allows, the more likely it is to enter the correct password.
Movements of a fitness tracker or smartwatch also "pass" the password

If a hacker installs a special scanner near your workplace, ATM, or terminal, they can get a password or PIN code by tracking the movement of your hands on a fitness tracker or smart watch.
The experiment was conducted by employees of the Stevens Institute of Technology and Binghamton University (USA). They developed a scanner that tracks electromagnetic radiation from sensors in smart watches and trackers. Data from the scanner was transmitted via Bluetooth.
The scan results were processed in an application that detects up to 5 thousand key movements. Two dozen users, two models of smart watches and a fitness bracelet with a standard nine-axis accelerometer were used to create the algorithm.
On the first attempt, the password was recognized in 80% of cases, and on the second attempt (if the user enters the same combination twice) – in 90%. The more sensors in a wearable device (gyroscopes, magnetometers, accelerometers), the higher the accuracy. The position of the hand does not affect it.
Even screenshots will reveal your password
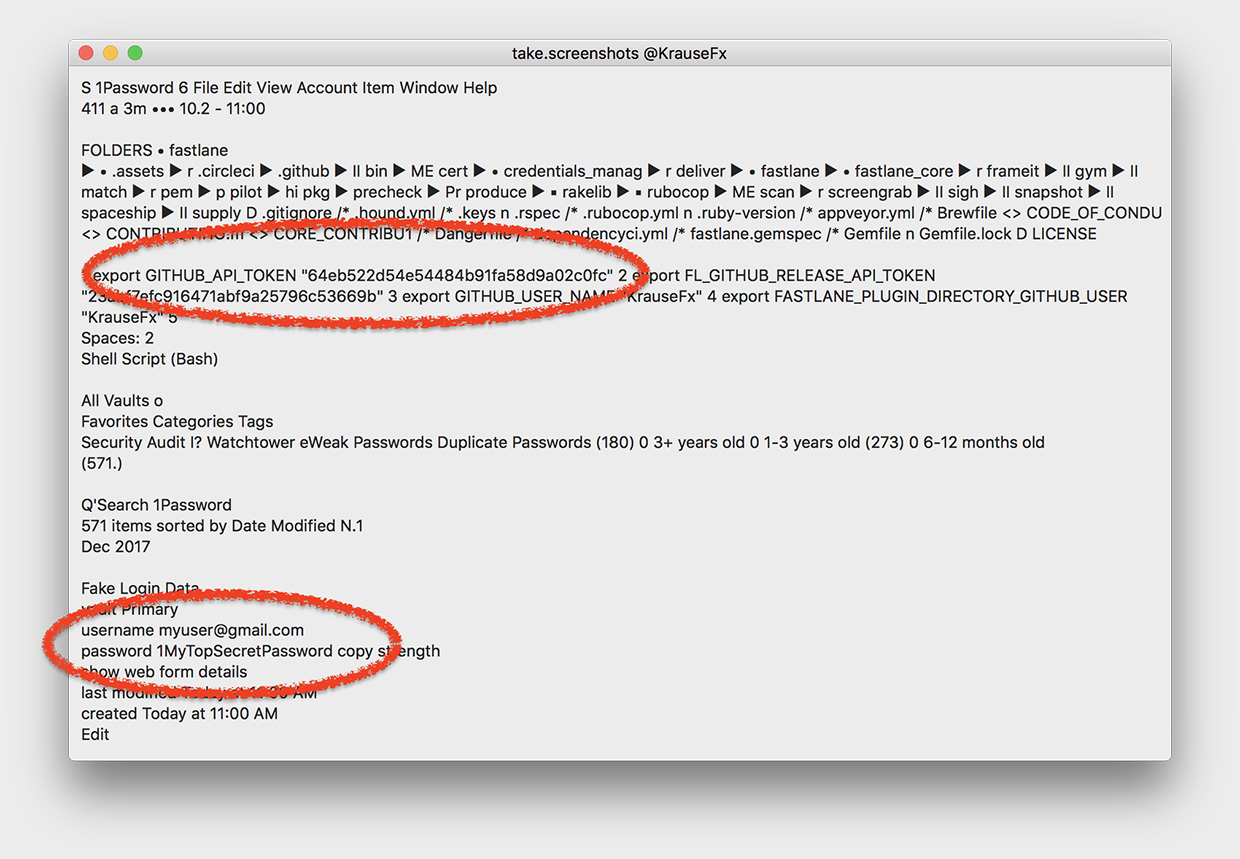
Your computer can technically take a screenshot at any time, including when you enter your password. The opportunity was discovered back in November 2017 by the founder of Fastlane Tools, Felix Krause.
The CGWindowListCreateImage function takes a screenshot. It doesn't require user permission.
A virus that takes screenshots can run in the background. It will still have access to literally every pixel.
Moving on to the real hack. MITM attacks
MITM (Man-in-the-middle) – man-in-the-middle attacks. Most often, sniffers like Intercepter-NG are used to intercept passwords and cookies using attacks of this type .
Intercepted data allows you to log in to other people's accounts, view uploaded files, and so on. In addition, the app allows you to forcibly delete the user's cookies, forcing them to re-log in.
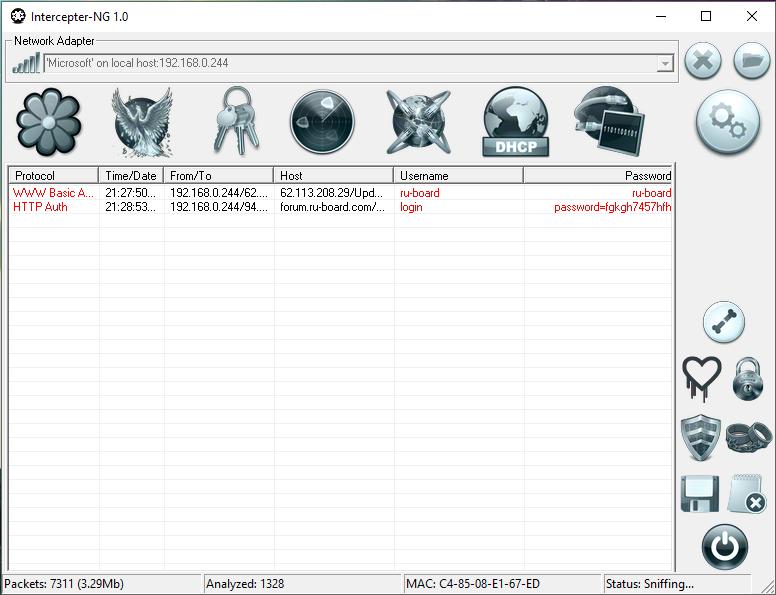
Previously, the tool allowed you to intercept even passwords from iCloud. But Apple developers have already fixed this.
Other ways to intercept traffic (including passwords) also exist. Even if they are passwords from HTTPS resources. The main thing is that the victim's device is located on the same Wi-Fi network as the hacker's device.
iphones.ru
