Hacker
Professional
- Messages
- 1,041
- Reaction score
- 852
- Points
- 113
Today we will talk about finding subdomains-an integral part of preparing for hacking, and thanks to some tools, countering these actions has become much easier. Subdomains may contain a vulnerable script, admin panel, etc., which can help us in hacking the site.
In the latest incident, the entire code of the Vine site could be downloaded from an unprotected subdomain.
If you are a website owner or are studying information security issues, you can use the following tools to find subdomains of any domain.
1. Censys
First of all, they usually use Censys to search for subdomains. In addition to the subdomain, you can find many other interesting things, such as:
You'll get a good overview of your domain information.
2. Pentest-Tools
Using Pentest-Tools, you can use several methods when searching for a subdomain, for example: passing a DNS zone, searching DNS based on a list of words, or using a search engine.
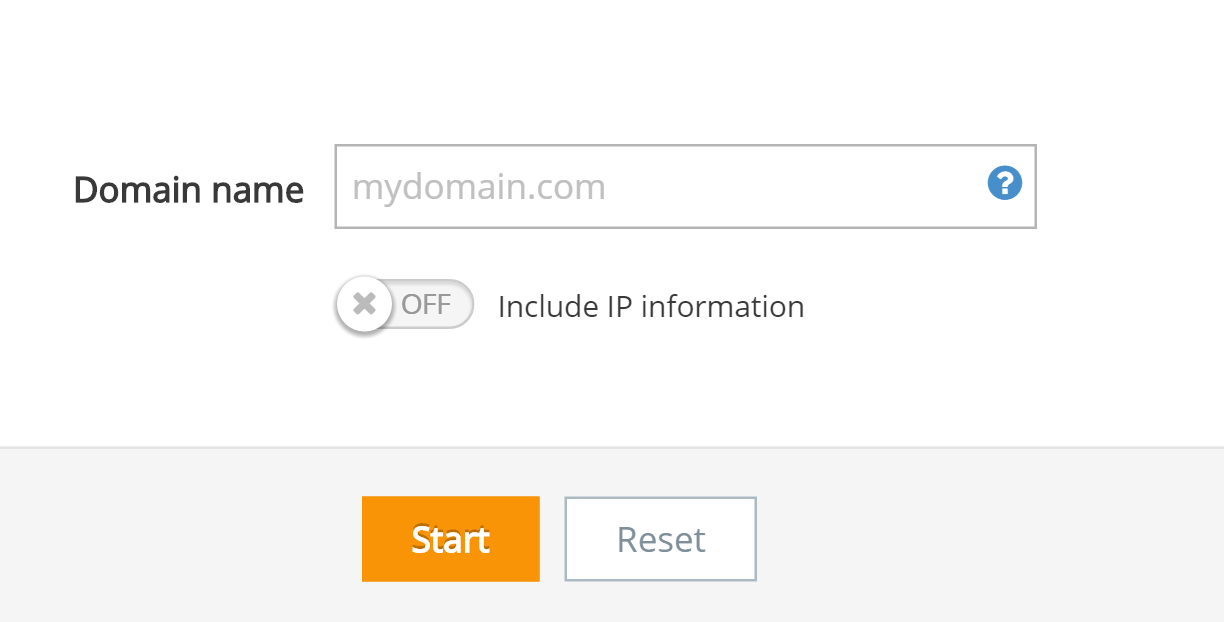
The search results can be saved in PDF format.
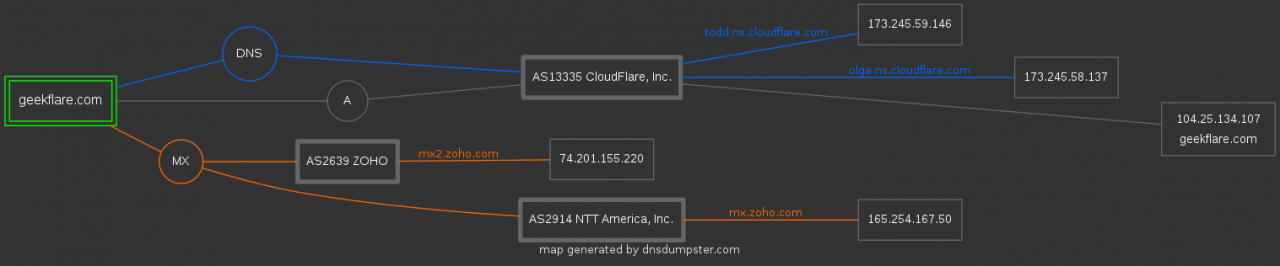
3. DNS Dumpster
DNS Dumpster is a tool for finding domain and host information. Project authors - HackerTarget.com.
You can find information not only about the subdomain, but also about the DNS server, MX and TXT records, as well as get a graphical representation of information about your domain.
4. Sublist3r

Sublist3r is a Python tool for detecting subdomains using search engines. Today Sublist3r supports Google, Yahoo, Bing, Baidu, Ask, Netcraft, Virustotal, ThreatCrowd, DNSdumpster and PassiveDNS.
Sublist3r only supports Python version 2.7 and depends on several libraries.
You can use this tool on Windows, CentOS, RedHat, Ubuntu, Debian, and any other UNIX-based OS. The following is an example for CentOS.
Log in to your Linux server;
Download the latest version of Sublist3r
Unzip the downloaded file:
A new folder “Sublist3r-master "will be created.”
As I mentioned earlier, there are the following dependencies that you can use the yum command to install:
You are now ready to detect subdomains with the following command:
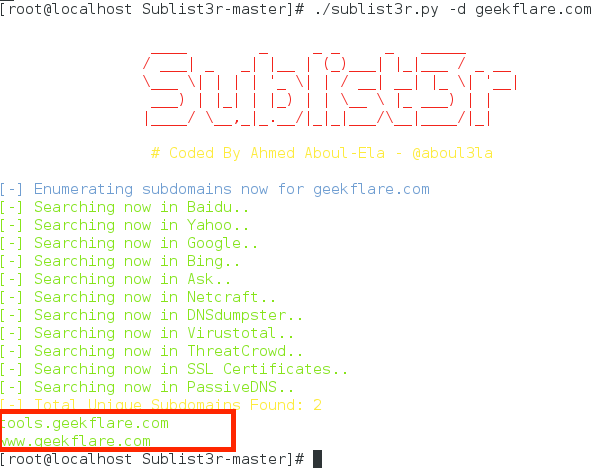
As you can see, the tool detected my subdomains.
5. Netcraft
Netcraft has an extensive database of domains and should not be ignored when searching for open information about subdomains.
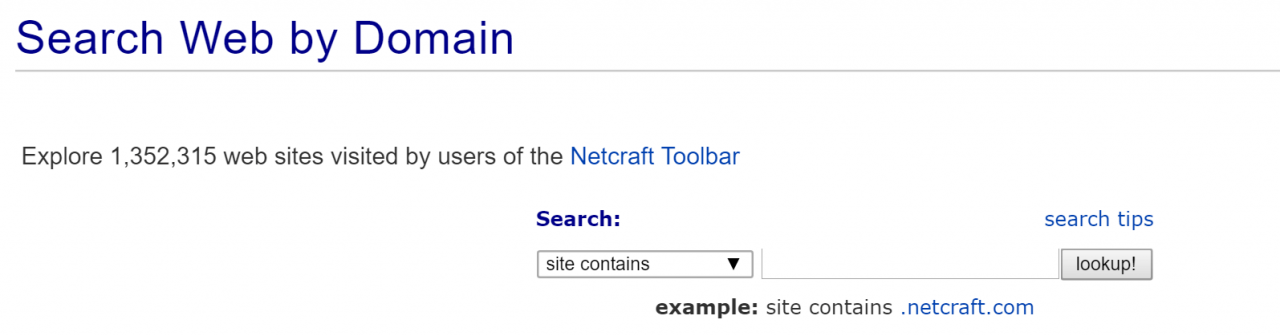
The search result will contain all information about the domain and subdomains, including the date of the first view, the address range, and information about the operating system. If you need to get more information about the site, just open the site report and you will be provided with a lot of information about technologies, rating, etc.
6. CloudPiercer
CloudPiercer can sometimes be useful when searching for information about whether a subdomain of your domain exists. By the way, CloudPiercer is an awesome and easy way to find out if your site's actual IP address is protected. Public IP address information makes your site vulnerable to DDoS attacks.
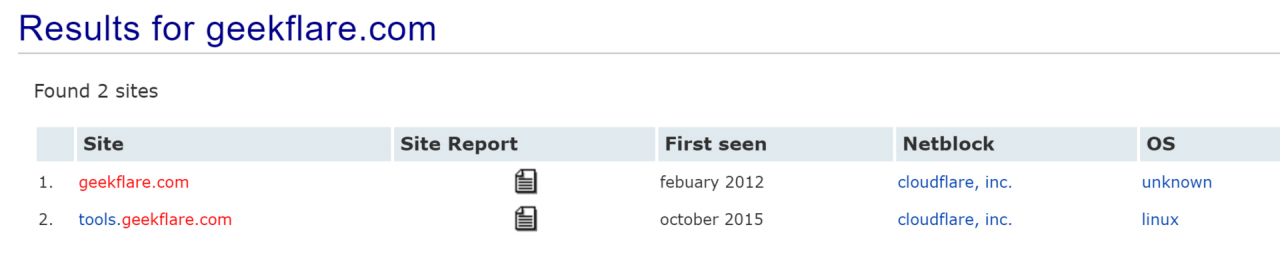
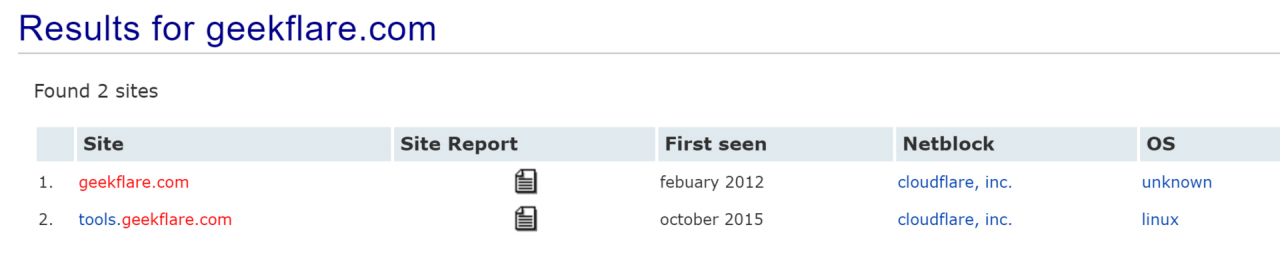
7. Detectify
Detectify searches for subdomains using a predefined list of several hundred words, but only if you are the owner of the domain. However, if you are a registered Detectify user, you can enable the subdomain detection feature in the overview section of settings.
8. SubBrute

SubBrute is one of the most popular and accurate subdomain enumeration tools. The project is developed by the community and uses an open name resolver as a proxy, so that SubBrute does not send traffic to the target DNS server.
It's not an online tool, so you'll have to install it on your computer. SubBrute can be used on Windows or UNIX systems. The program is very easy to install. Below is an example for CentOS / Linux.
Log in to your Linux server
Download the latest version of SubBrute
Unzip the downloaded zip file
A new folder “subbrute-master " will be created. Go to the folder and execute subbrute.py with the required domain.
The operation will take a few seconds and the found subdomains will be displayed.
9. Knock

Knock is another Python tool for detecting subdomains. It is tested for Python 2.7.6. Knock finds subdomains of the target domain from a list of words.
Knock can be installed on a Linux-based OS.
Unzip the downloaded zip file with the unzip command
As a result, a new folder “knock-knock3 "will be created.”
Go to the folder and install using the following command
After installation, you can search for subdomains as follows:
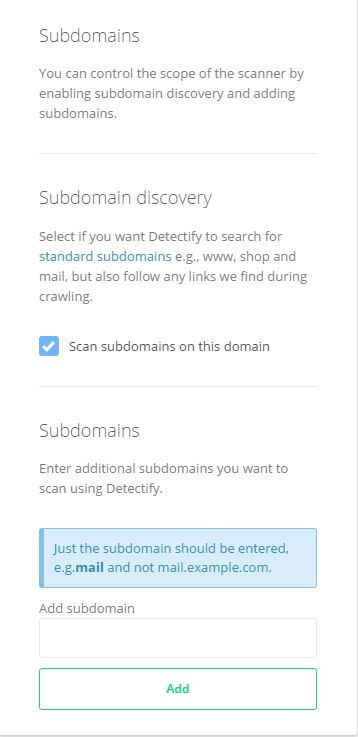
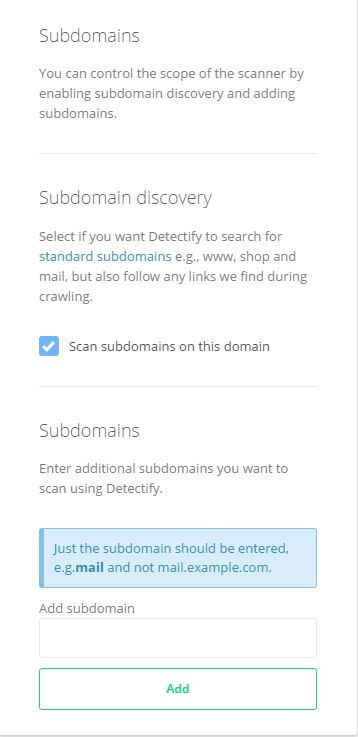
10. DNSRecon for Kali Linux
Kali Linux is an excellent platform for evaluating information security and you can use DNSRecon on it without installing any additional tools.
DNSRecon checks all NS records for zone changes, shared DNS records, template processing, PTR records, and so on.
To use DNSRecon, simply run the following command
I hope that using the tools listed above, you will be able to detect subdomains of the target domain as part of your information security assessment work.
Images: cryptoworld.su
In the latest incident, the entire code of the Vine site could be downloaded from an unprotected subdomain.
If you are a website owner or are studying information security issues, you can use the following tools to find subdomains of any domain.
1. Censys
First of all, they usually use Censys to search for subdomains. In addition to the subdomain, you can find many other interesting things, such as:
- IP data (can be useful for finding a real IP address);
- certificate details;
- open ports;
- SSL / TLS handshake protocol and encryption algorithms (useful when searching for weak ciphers/protocols).
You'll get a good overview of your domain information.
2. Pentest-Tools
Using Pentest-Tools, you can use several methods when searching for a subdomain, for example: passing a DNS zone, searching DNS based on a list of words, or using a search engine.
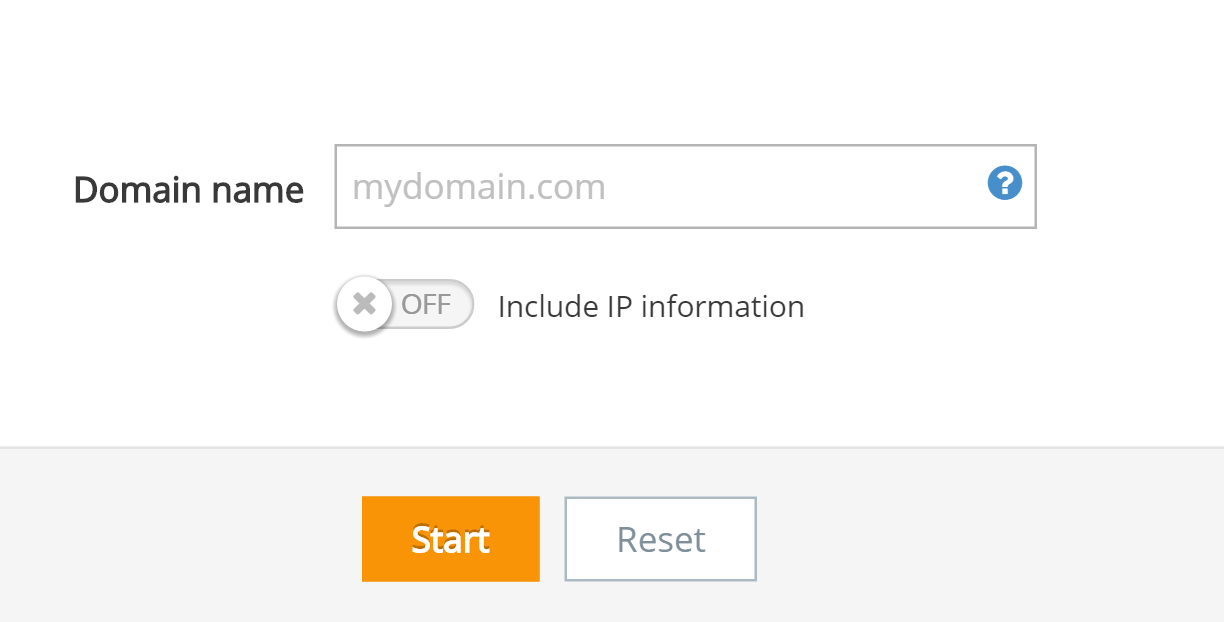
The search results can be saved in PDF format.
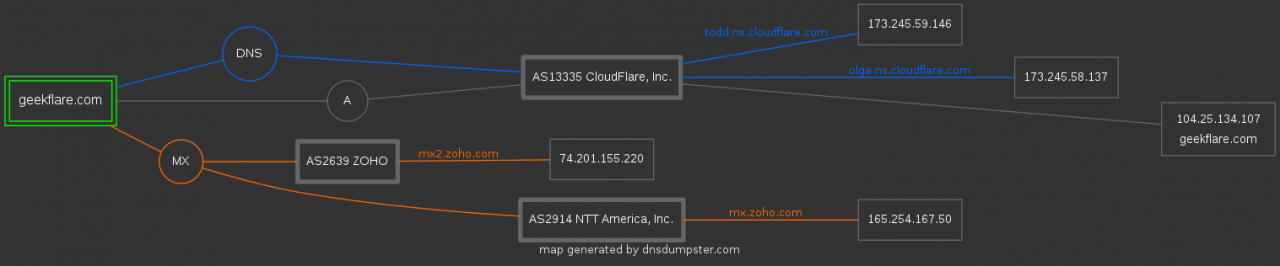
3. DNS Dumpster
DNS Dumpster is a tool for finding domain and host information. Project authors - HackerTarget.com.
You can find information not only about the subdomain, but also about the DNS server, MX and TXT records, as well as get a graphical representation of information about your domain.
4. Sublist3r

Sublist3r is a Python tool for detecting subdomains using search engines. Today Sublist3r supports Google, Yahoo, Bing, Baidu, Ask, Netcraft, Virustotal, ThreatCrowd, DNSdumpster and PassiveDNS.
Sublist3r only supports Python version 2.7 and depends on several libraries.
You can use this tool on Windows, CentOS, RedHat, Ubuntu, Debian, and any other UNIX-based OS. The following is an example for CentOS.
Log in to your Linux server;
Download the latest version of Sublist3r
Code:
wget https://github.com/aboul3la/Sublist3r/archive/master.zipUnzip the downloaded file:
Code:
unzip master.zipA new folder “Sublist3r-master "will be created.”
As I mentioned earlier, there are the following dependencies that you can use the yum command to install:
Code:
yum install python-requests python-argparseYou are now ready to detect subdomains with the following command:
Code:
./sublist3r.py -d yourdomain.com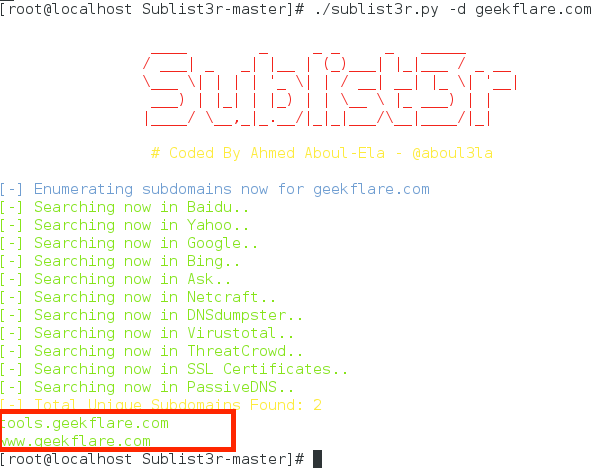
As you can see, the tool detected my subdomains.
5. Netcraft
Netcraft has an extensive database of domains and should not be ignored when searching for open information about subdomains.
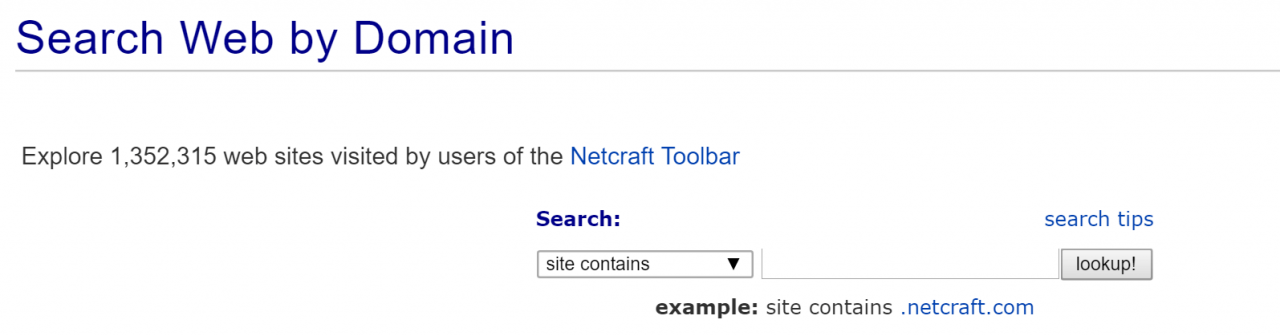
The search result will contain all information about the domain and subdomains, including the date of the first view, the address range, and information about the operating system. If you need to get more information about the site, just open the site report and you will be provided with a lot of information about technologies, rating, etc.
6. CloudPiercer
CloudPiercer can sometimes be useful when searching for information about whether a subdomain of your domain exists. By the way, CloudPiercer is an awesome and easy way to find out if your site's actual IP address is protected. Public IP address information makes your site vulnerable to DDoS attacks.
7. Detectify
Detectify searches for subdomains using a predefined list of several hundred words, but only if you are the owner of the domain. However, if you are a registered Detectify user, you can enable the subdomain detection feature in the overview section of settings.
8. SubBrute

SubBrute is one of the most popular and accurate subdomain enumeration tools. The project is developed by the community and uses an open name resolver as a proxy, so that SubBrute does not send traffic to the target DNS server.
It's not an online tool, so you'll have to install it on your computer. SubBrute can be used on Windows or UNIX systems. The program is very easy to install. Below is an example for CentOS / Linux.
Log in to your Linux server
Download the latest version of SubBrute
Code:
wget https://github.com/TheRook/subbrute/archive/master.zipUnzip the downloaded zip file
Code:
unzip master.zipA new folder “subbrute-master " will be created. Go to the folder and execute subbrute.py with the required domain.
Code:
./subbrute.py yourdomain.comThe operation will take a few seconds and the found subdomains will be displayed.
9. Knock

Knock is another Python tool for detecting subdomains. It is tested for Python 2.7.6. Knock finds subdomains of the target domain from a list of words.
Knock can be installed on a Linux-based OS.
Code:
wget https://github.com/guelfoweb/knock/archive/knock3.zipUnzip the downloaded zip file with the unzip command
Code:
unzip knock3.zipAs a result, a new folder “knock-knock3 "will be created.”
Go to the folder and install using the following command
Code:
python setup.py installAfter installation, you can search for subdomains as follows:
Code:
./knockpy.py yourdomain.com10. DNSRecon for Kali Linux
Kali Linux is an excellent platform for evaluating information security and you can use DNSRecon on it without installing any additional tools.
DNSRecon checks all NS records for zone changes, shared DNS records, template processing, PTR records, and so on.
To use DNSRecon, simply run the following command
Code:
dnsrecon –d yourdomain.com
I hope that using the tools listed above, you will be able to detect subdomains of the target domain as part of your information security assessment work.
Images: cryptoworld.su
