Lord777
Professional
- Messages
- 2,576
- Reaction score
- 1,565
- Points
- 113
Zero-day in a popular email client resulted in data loss for thousands of users.
A zero-day vulnerability was discovered in the Zimbra email software, which was exploited by four different groups of hackers to steal email data, user credentials, and authentication tokens.
Google TAG experts report in their report that most of the attacks were fixed after the initial fix was published on GitHub.
The vulnerability, tracked as CVE-2023-37580 with a CVSS score of 6.1, is a cross-site scripting (XSS) vulnerability in versions prior to 8.8.15 Patch 41. The company fixed the issue as part of updates released on July 25, 2023.
Exploiting this flaw allows malicious scripts to be executed in the victim's web browser via an XSS request after simply clicking on the URL link. You don't even need to download and install something.
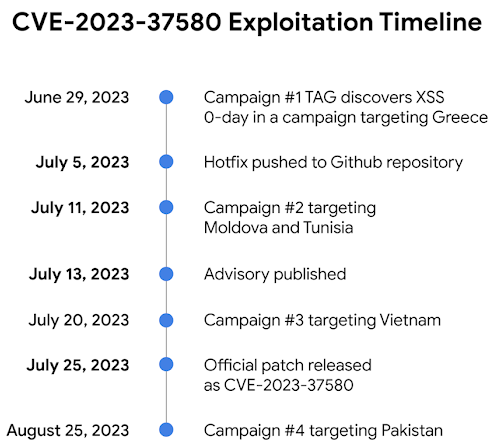
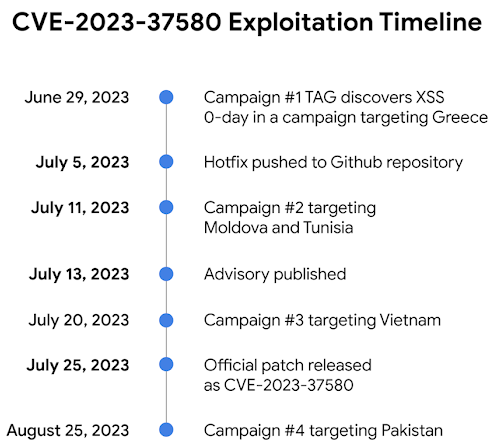
Google TAG researcher Clement Lesigne reported several waves of such attacks starting on June 29, 2023, at least two weeks before the official Zimbra notice was published. Three of the four malicious campaigns were detected before the patch was released, and the fourth one was detected a month after the patch was published.
The first campaign targeted a state-run organization in Greece, which sent emails with exploit URLs that were clicked on to deliver email-stealing malware previously seen in the February 2022 "EmailThief" cyber espionage operation.
The second malicious operation, which exploited CVE-2023-37580, was organized by hackers Winter Vivern, who attacked state organizations in Moldova and Tunisia shortly after the hot fix for the vulnerability was published on GitHub on July 5.
TAG identified a third unidentified group exploiting a vulnerability to phish an organization's credentials in Vietnam before the patch was released on July 25. In this case, the exploit URL pointed to a script that displayed a phishing page and collected users ' webmail credentials, then sending these stolen credentials to a URL that was compromised by the attackers.
Finally, the fourth attack was carried out on August 25 against a government organization in Pakistan, which resulted in the exfiltration of the Zimbra authentication token to the remote domain "ntcpk [.] org".
Google notes that attackers regularly exploit XSS vulnerabilities in mail servers, which requires a thorough audit of such applications.
"The discovery of at least four campaigns exploiting CVE-2023-37580, three of them after the vulnerability became publicly known, underscores the importance of timely patching of mail servers," TAG said in a statement.
"These campaigns also demonstrate how attackers constantly monitor open repositories to exploit vulnerabilities when a fix is already in the repository, but has not yet been released to users," Google concluded.
A zero-day vulnerability was discovered in the Zimbra email software, which was exploited by four different groups of hackers to steal email data, user credentials, and authentication tokens.
Google TAG experts report in their report that most of the attacks were fixed after the initial fix was published on GitHub.
The vulnerability, tracked as CVE-2023-37580 with a CVSS score of 6.1, is a cross-site scripting (XSS) vulnerability in versions prior to 8.8.15 Patch 41. The company fixed the issue as part of updates released on July 25, 2023.
Exploiting this flaw allows malicious scripts to be executed in the victim's web browser via an XSS request after simply clicking on the URL link. You don't even need to download and install something.
Google TAG researcher Clement Lesigne reported several waves of such attacks starting on June 29, 2023, at least two weeks before the official Zimbra notice was published. Three of the four malicious campaigns were detected before the patch was released, and the fourth one was detected a month after the patch was published.
The first campaign targeted a state-run organization in Greece, which sent emails with exploit URLs that were clicked on to deliver email-stealing malware previously seen in the February 2022 "EmailThief" cyber espionage operation.
The second malicious operation, which exploited CVE-2023-37580, was organized by hackers Winter Vivern, who attacked state organizations in Moldova and Tunisia shortly after the hot fix for the vulnerability was published on GitHub on July 5.
TAG identified a third unidentified group exploiting a vulnerability to phish an organization's credentials in Vietnam before the patch was released on July 25. In this case, the exploit URL pointed to a script that displayed a phishing page and collected users ' webmail credentials, then sending these stolen credentials to a URL that was compromised by the attackers.
Finally, the fourth attack was carried out on August 25 against a government organization in Pakistan, which resulted in the exfiltration of the Zimbra authentication token to the remote domain "ntcpk [.] org".
Google notes that attackers regularly exploit XSS vulnerabilities in mail servers, which requires a thorough audit of such applications.
"The discovery of at least four campaigns exploiting CVE-2023-37580, three of them after the vulnerability became publicly known, underscores the importance of timely patching of mail servers," TAG said in a statement.
"These campaigns also demonstrate how attackers constantly monitor open repositories to exploit vulnerabilities when a fix is already in the repository, but has not yet been released to users," Google concluded.

