Carding
Professional
- Messages
- 2,870
- Reaction score
- 2,522
- Points
- 113
Using information that was accidentally leaked to the public, well-known blogger and researcher Brian Krebs was able to determine that part of the site code created by the cryptographer's operators was written by a 36-year-old programmer living in Chisinau.
The cyber group behind 8Base uses a double extortion scheme, demanding a ransom for decrypting data and threatening non-payers with disclosure of the fact of hacking. Its website, designed for such publications, is accessible via Tor.
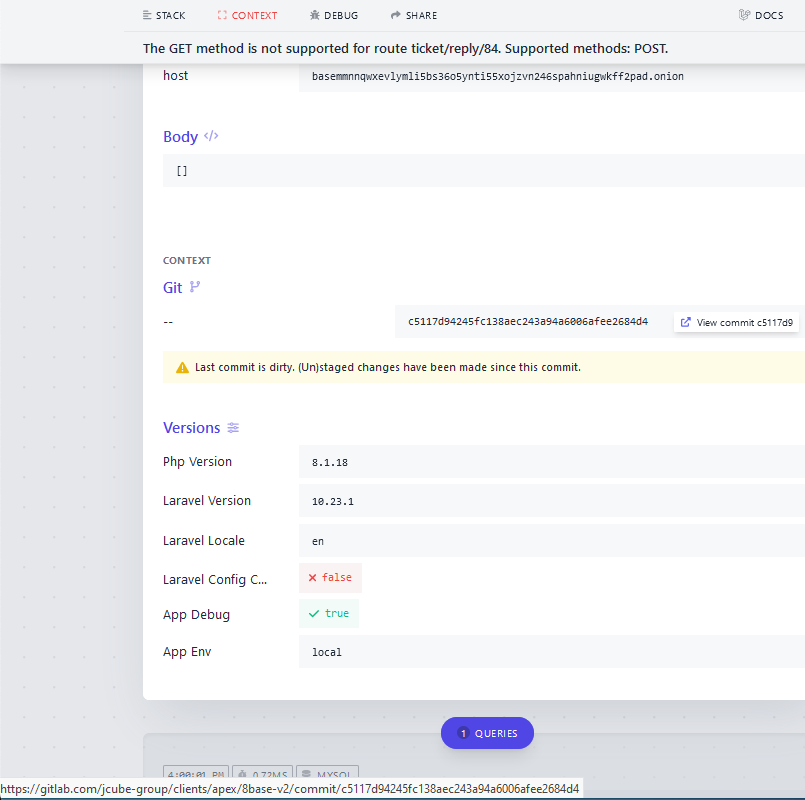
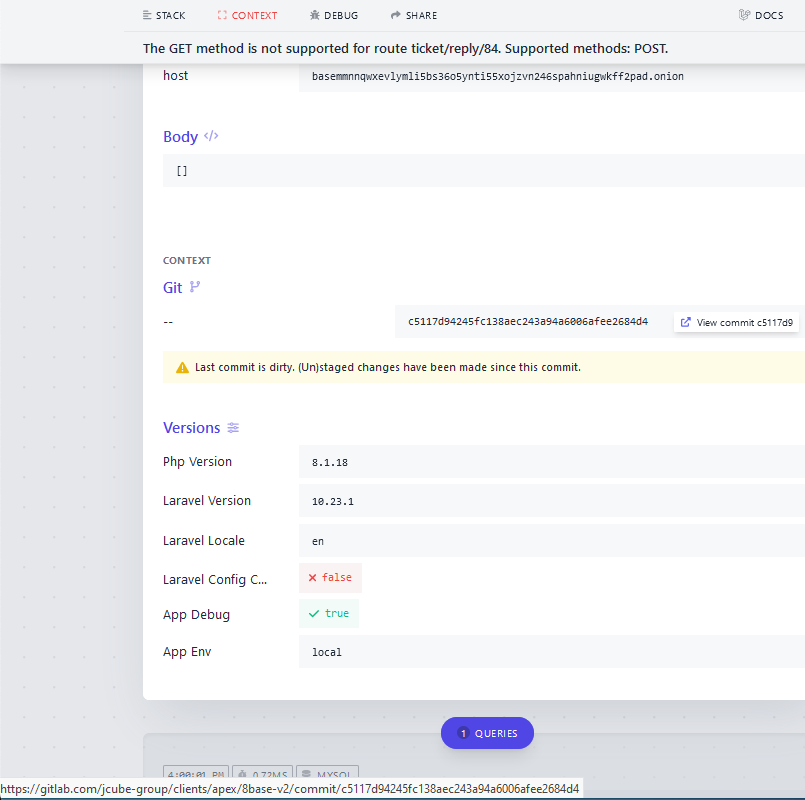
The built-in chat for conducting negotiations uses the Laravel PHP framework and, according to Krebs, works properly when sending data to the server (via POST). Until recently, GET requests returned a lengthy error message revealing the IP address of a host (95.216.51[.]74 in Finland) hidden using Tor services.
Scrolling through the page, you could find a link to the Gitlab server dedicated to the needs of the JCube Group. As it turned out, the linked repository also contains other PHP codes used by the 8Base site.
Further excavations revealed that the JCube Group Gitlab account was created by developer Andrey Kolev, who lives in the capital of Moldova. At least that's what his LinkedIn profile says. There is also a specialization: full-cycle web application development (on the client and server side); place of work-JCube Group, address and phone number match the contacts published on the company's website.
All Kolev's " X's "(tweets in the old way) are written in Russian. Krebs asked for a comment, but the source said he didn't know why the 8Base darknet site was uploading code from the Clients folder to its storage.
However, the telltale error message on the 8Base website was quickly removed. Instead, it now displays error 405 — "HTTP method is not allowed". The author of the discovery, thanks to which Krebs began another investigation, is almost sure that deanonymization occurred because the creator of the onion site unintentionally left the development mode (forgot to disable debugging and testing tools).
The cyber group behind 8Base uses a double extortion scheme, demanding a ransom for decrypting data and threatening non-payers with disclosure of the fact of hacking. Its website, designed for such publications, is accessible via Tor.
The built-in chat for conducting negotiations uses the Laravel PHP framework and, according to Krebs, works properly when sending data to the server (via POST). Until recently, GET requests returned a lengthy error message revealing the IP address of a host (95.216.51[.]74 in Finland) hidden using Tor services.
Scrolling through the page, you could find a link to the Gitlab server dedicated to the needs of the JCube Group. As it turned out, the linked repository also contains other PHP codes used by the 8Base site.
Further excavations revealed that the JCube Group Gitlab account was created by developer Andrey Kolev, who lives in the capital of Moldova. At least that's what his LinkedIn profile says. There is also a specialization: full-cycle web application development (on the client and server side); place of work-JCube Group, address and phone number match the contacts published on the company's website.
All Kolev's " X's "(tweets in the old way) are written in Russian. Krebs asked for a comment, but the source said he didn't know why the 8Base darknet site was uploading code from the Clients folder to its storage.
| "There is no such project in my repository," the developer said. — They [8Base] are not my clients. Currently, we only work on our own projects." |
However, the telltale error message on the 8Base website was quickly removed. Instead, it now displays error 405 — "HTTP method is not allowed". The author of the discovery, thanks to which Krebs began another investigation, is almost sure that deanonymization occurred because the creator of the onion site unintentionally left the development mode (forgot to disable debugging and testing tools).