chushpan
Professional
- Messages
- 1,355
- Reaction score
- 1,697
- Points
- 113
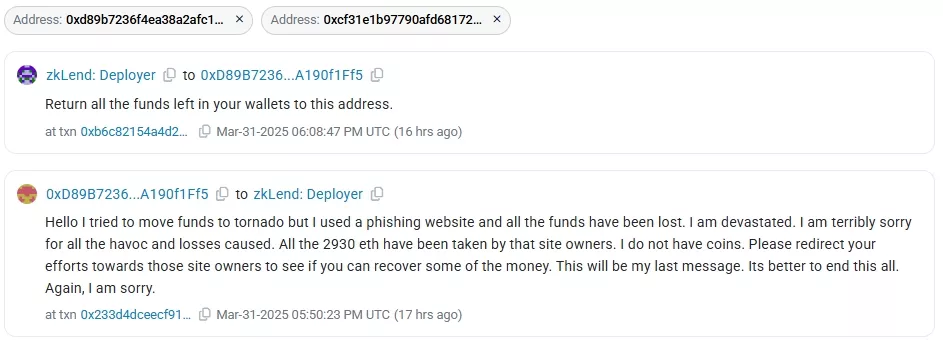
In response to another offer from the zkLend team to return the stolen funds, the hacker who hacked the protocol reported that he sent 2930 ETH (~$5.4 million) to the fake Tornado Cash website.
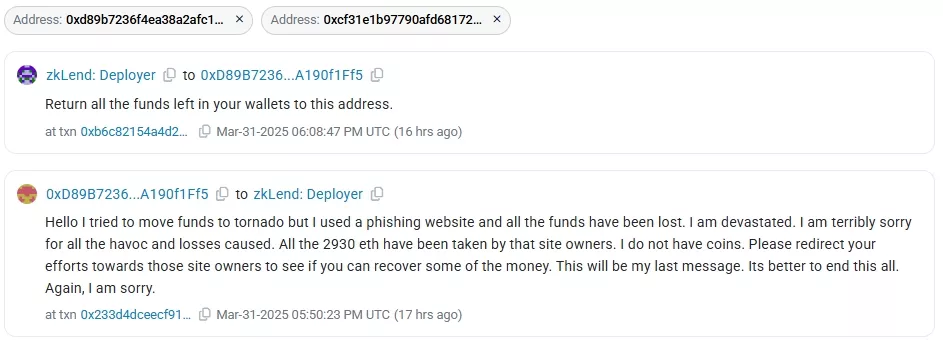
Data: Etherscan.
As a result of the incident on February 12, the Starknet -based L2 project lost ~3666 ETH ($9.6 million at the time). The attacker was immediately offered to return the assets for a reward of 10% of the amount and a waiver of prosecution.
The attacker advised to "redirect efforts" to return assets from him to the operators of the phishing site.
The transactions in which the hacker allegedly lost coins were confirmed by a cybersecurity researcher under the nickname Vladimir S and a number of other specialists, including the administrator of the TornadoCashBot X-account.
However, the latter suggested that the zkLend hacker and the owner of the fake Tornado Cash could be the same person. At the very least, both used the same ENS address safe-relayer.eth.
According to the expert, the site with the domain tornadorth[.]cash has been featured in the mixing platform's Telegram chat since 2024 and has attracted attention. The address safe-relayer.eth was registered in the phishing platform's code as a relay, although the original mixing service in this case uses a dynamic registry.
The developers of the L2 protocol confirmed the active movement of assets stolen by the attacker in the last 24 hours.
According to them, the phishing site has been operating for at least five years, but they currently have no convincing evidence of the site's interaction with the hacker. The zkLend team has included the addresses associated with it in the measures to track the funds.
Data: Etherscan.
As a result of the incident on February 12, the Starknet -based L2 project lost ~3666 ETH ($9.6 million at the time). The attacker was immediately offered to return the assets for a reward of 10% of the amount and a waiver of prosecution.
"Hi, I tried to transfer funds to Tornado but I used a phishing website and lost everything. I am devastated. I am so sorry for the destruction and loss caused. All 2930 ETH were taken by the owners of this site. I have no coins," the hacker wrote in response to the zkLend team on March 31.
The attacker advised to "redirect efforts" to return assets from him to the operators of the phishing site.
The transactions in which the hacker allegedly lost coins were confirmed by a cybersecurity researcher under the nickname Vladimir S and a number of other specialists, including the administrator of the TornadoCashBot X-account.
However, the latter suggested that the zkLend hacker and the owner of the fake Tornado Cash could be the same person. At the very least, both used the same ENS address safe-relayer.eth.
According to the expert, the site with the domain tornadorth[.]cash has been featured in the mixing platform's Telegram chat since 2024 and has attracted attention. The address safe-relayer.eth was registered in the phishing platform's code as a relay, although the original mixing service in this case uses a dynamic registry.
“Since the source code of the fraudulent site deleted safe-relayer.eth, and he still withdraws funds from Tornado Cash through it, he may be the hacker who hacked zkLend,” the expert concluded.
The developers of the L2 protocol confirmed the active movement of assets stolen by the attacker in the last 24 hours.
According to them, the phishing site has been operating for at least five years, but they currently have no convincing evidence of the site's interaction with the hacker. The zkLend team has included the addresses associated with it in the measures to track the funds.
