Carding 4 Carders
Professional
- Messages
- 2,724
- Reaction score
- 1,598
- Points
- 113
MSIX packages and sophisticated techniques allow hackers to conduct stealthy but devastating attacks.
Security researchers at Elastic Security Labs documented a new wave of attacks in which attackers use fake MSIX application package files to distribute a malicious downloader called GHOSTPULSE. Files are disguised as popular software products, such as Google Chrome, Microsoft Edge, Brave, Grammarly services, and Cisco Webex.
MSIX is a Windows application package format that allows developers to package and distribute their applications to Windows users. It is noted that creating MSIX packages requires access to purchased or stolen code signing certificates, which indicates the high resources of the criminal group behind these attacks.
It is assumed that victims are attracted to downloading malicious packages through infected websites, manipulating Internet search results, or through malicious advertising. Running a malicious MSIX file in this campaign causes the user to see a window with a suggestion to install the program, but clicking the "Install" button initiates a hidden download of GHOSTPULSE from a remote server via a PowerShell script written by attackers.
The infection process takes place in several stages. Initially, a TAR archive is loaded containing an executable file that disguises itself as the Oracle VM VirtualBox service, but is actually a legitimate program included in Notepad++. The archive also contains an encrypted file "handoff. wav" and a modified version "libcurl.dll", used to move to the next stage of infection by exploiting the Sideloading DLL method.
The spoofed DLL file is processed by analyzing "handoff.wav", which, in turn, contains encrypted malicious code. This code is decrypted and executed using "mshtml. dl". This method is known as "Module Stomping". Eventually, this whole sequence of actions leads to the activation of GHOSTPULSE.
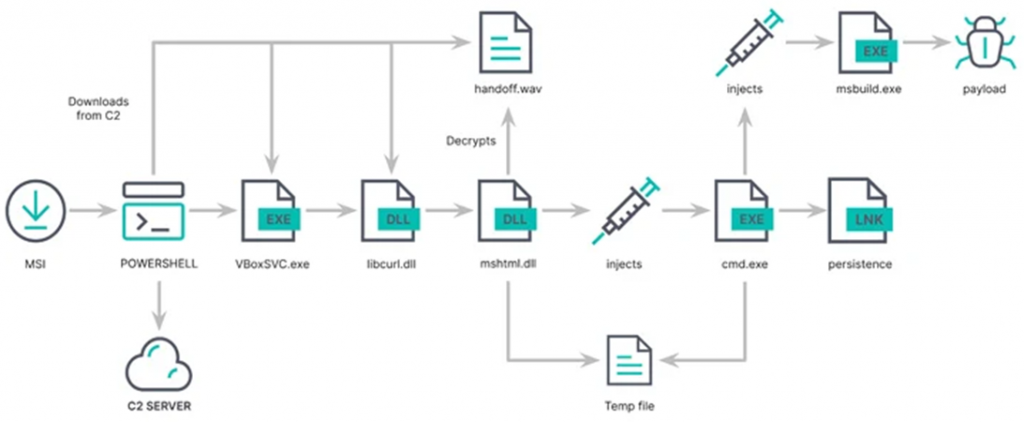
Infection scheme
GHOSTPULSE acts as a loader and uses a technique called "Process Doppelganging" to start executing the final malicious software, including SectopRAT, Rhadamanthys, Vidar, Lumma, and NetSupport RAT.
Security researchers at Elastic Security Labs documented a new wave of attacks in which attackers use fake MSIX application package files to distribute a malicious downloader called GHOSTPULSE. Files are disguised as popular software products, such as Google Chrome, Microsoft Edge, Brave, Grammarly services, and Cisco Webex.
MSIX is a Windows application package format that allows developers to package and distribute their applications to Windows users. It is noted that creating MSIX packages requires access to purchased or stolen code signing certificates, which indicates the high resources of the criminal group behind these attacks.
It is assumed that victims are attracted to downloading malicious packages through infected websites, manipulating Internet search results, or through malicious advertising. Running a malicious MSIX file in this campaign causes the user to see a window with a suggestion to install the program, but clicking the "Install" button initiates a hidden download of GHOSTPULSE from a remote server via a PowerShell script written by attackers.
The infection process takes place in several stages. Initially, a TAR archive is loaded containing an executable file that disguises itself as the Oracle VM VirtualBox service, but is actually a legitimate program included in Notepad++. The archive also contains an encrypted file "handoff. wav" and a modified version "libcurl.dll", used to move to the next stage of infection by exploiting the Sideloading DLL method.
The spoofed DLL file is processed by analyzing "handoff.wav", which, in turn, contains encrypted malicious code. This code is decrypted and executed using "mshtml. dl". This method is known as "Module Stomping". Eventually, this whole sequence of actions leads to the activation of GHOSTPULSE.
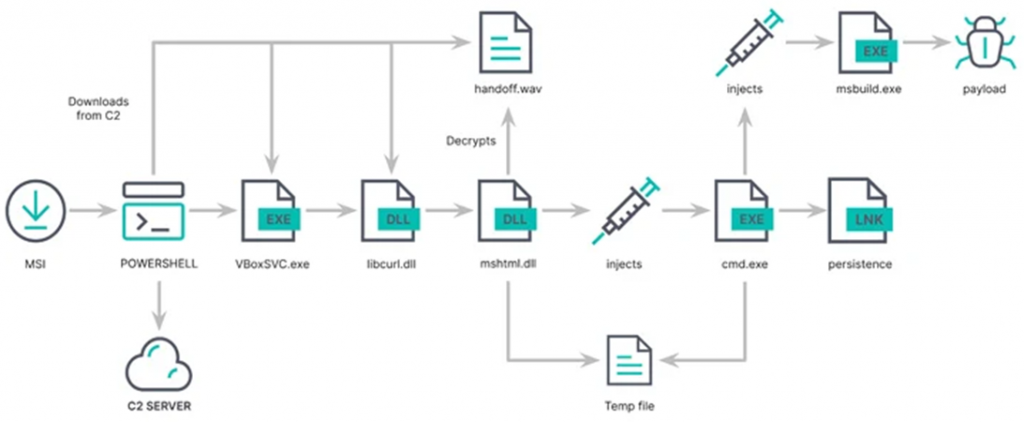
Infection scheme
GHOSTPULSE acts as a loader and uses a technique called "Process Doppelganging" to start executing the final malicious software, including SectopRAT, Rhadamanthys, Vidar, Lumma, and NetSupport RAT.

