Brother
Professional
- Messages
- 2,590
- Reaction score
- 541
- Points
- 113
The international operation helped the victims save $68 million, and the group's competitors attract new customers.
The US Department of Justice announced the successful penetration of the FBI into the infrastructure of the ALPHV ransomware group (BlackCat). The operation allowed agents to monitor the actions of hackers and obtain keys to decrypt data.
The incident became known after the group's negotiation and data leakage sites on the Tor network suddenly stopped working on December 7 . ALPHV administrators blamed the problem on a hosting problem, but it soon became clear that the cause was a law enforcement operation. The operation was conducted by police and investigative agencies from the United States, Europol, Denmark, Germany, the United Kingdom, the Netherlands, Australia, Spain and Austria.
According to the court order, a key factor in the success of the operation was the involvement of a confidential source who responded to the group's public announcement about the recruitment of affiliates and, after interviewing cybercriminals, obtained credentials to access the ALPHV partner system on the Tor network. Gaining access allowed the police to study and monitor the group's online activities.
The FBI, having gained access to the group's servers, conducted surveillance for several months, simultaneously seizing decryption keys, which allowed restoring the data of about 500 victims of the ransomware program, avoiding paying ransoms totaling about $68 million.
As part of the operation, the FBI also seized the domain of the ALPHV data leak site, which now has a notice of its confiscation. The site's takeover became possible after the FBI obtained keys to access the hidden Tor services under which the site operated.
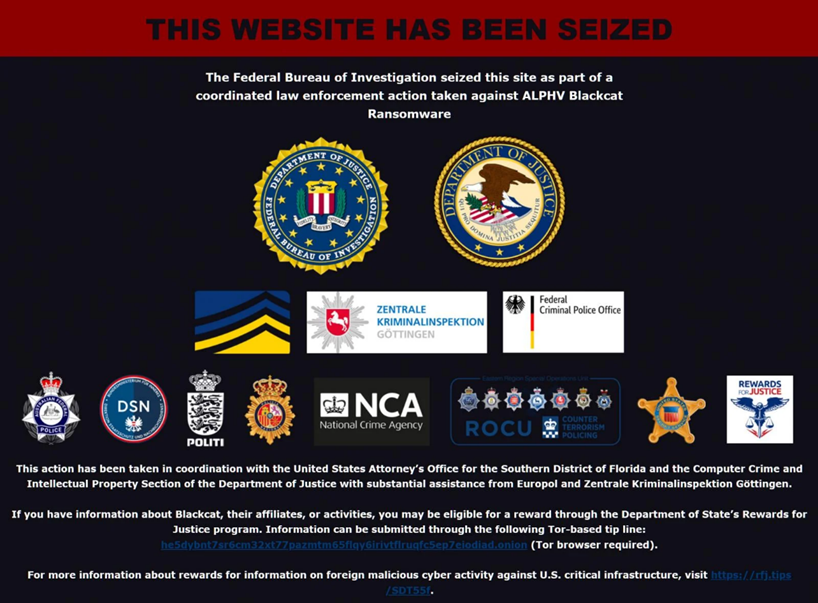
Banner on the ALPHV website
A public search warrant reveals that law enforcement agencies gained access to the BlackCat network by identifying and collecting 946 pairs of public and private keys. These keys were used to manage victim communication sites, data leak sites, and partner (affiliate) panels.
After the ALPHV servers were disrupted, partners trust in the group declined – some of them started contacting victims directly via email, bypassing the group's platform on the Tor network. This is due to concerns that the ALPHV infrastructure may have been compromised. It is also worth noting that the ransomware group LockBit took the situation as an opportunity to expand its activities, inviting ALPHV affiliates to join them.
Since its introduction in August 2020 under the name DarkSide, the group has repeatedly changed its names and tactics in response to law enforcement actions. After the attack on the Colonial Pipeline in May 2021, the group was forced to stop its activities, but soon resumed it under the name BlackMatter. However, this time the group had to retreat after Emsisoft found a vulnerability for creating a decryptor, and the group's servers were seized.
Since November 2021, the group has operated under the name ALPHV / BlackCat, constantly improving its extortion methods. It is likely that after this law enforcement operation, the group will again try to change its name and strategy.
The US Department of Justice announced the successful penetration of the FBI into the infrastructure of the ALPHV ransomware group (BlackCat). The operation allowed agents to monitor the actions of hackers and obtain keys to decrypt data.
The incident became known after the group's negotiation and data leakage sites on the Tor network suddenly stopped working on December 7 . ALPHV administrators blamed the problem on a hosting problem, but it soon became clear that the cause was a law enforcement operation. The operation was conducted by police and investigative agencies from the United States, Europol, Denmark, Germany, the United Kingdom, the Netherlands, Australia, Spain and Austria.
According to the court order, a key factor in the success of the operation was the involvement of a confidential source who responded to the group's public announcement about the recruitment of affiliates and, after interviewing cybercriminals, obtained credentials to access the ALPHV partner system on the Tor network. Gaining access allowed the police to study and monitor the group's online activities.
The FBI, having gained access to the group's servers, conducted surveillance for several months, simultaneously seizing decryption keys, which allowed restoring the data of about 500 victims of the ransomware program, avoiding paying ransoms totaling about $68 million.
As part of the operation, the FBI also seized the domain of the ALPHV data leak site, which now has a notice of its confiscation. The site's takeover became possible after the FBI obtained keys to access the hidden Tor services under which the site operated.
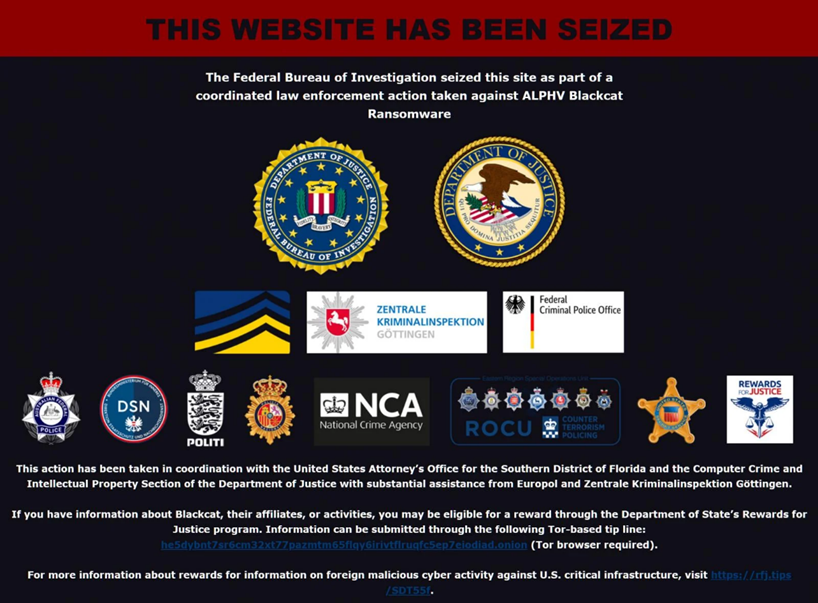
Banner on the ALPHV website
A public search warrant reveals that law enforcement agencies gained access to the BlackCat network by identifying and collecting 946 pairs of public and private keys. These keys were used to manage victim communication sites, data leak sites, and partner (affiliate) panels.
After the ALPHV servers were disrupted, partners trust in the group declined – some of them started contacting victims directly via email, bypassing the group's platform on the Tor network. This is due to concerns that the ALPHV infrastructure may have been compromised. It is also worth noting that the ransomware group LockBit took the situation as an opportunity to expand its activities, inviting ALPHV affiliates to join them.
Since its introduction in August 2020 under the name DarkSide, the group has repeatedly changed its names and tactics in response to law enforcement actions. After the attack on the Colonial Pipeline in May 2021, the group was forced to stop its activities, but soon resumed it under the name BlackMatter. However, this time the group had to retreat after Emsisoft found a vulnerability for creating a decryptor, and the group's servers were seized.
Since November 2021, the group has operated under the name ALPHV / BlackCat, constantly improving its extortion methods. It is likely that after this law enforcement operation, the group will again try to change its name and strategy.

