Friend
Professional
- Messages
- 2,671
- Reaction score
- 1,104
- Points
- 113
A fundamental security vulnerability that cannot be fixed has been exposed.
SquareX and its founder Vivek Ramachandran, a well-known cybersecurity expert, recently discovered a vulnerability in the Secure Web Gateway (SWG) systems used to protect corporate networks. It turned out that all SWGs included in the Gartner Magic Quadrant rating for SASE and SSE can be bypassed and malware can be downloaded to the system without arousing suspicion from security systems.
Ramachandran has developed over 25 different SWG traversal methods. The hacking technique is called "Last Mile Reassembly". All methods of circumvention are reduced to one basic exploit — modern browsers remain out of sight of SWG systems.
SWGs were created more than 15 years ago and were originally used as an SSL proxy to intercept traffic, but with the development of cloud technologies, their functionality has become much broader. This is where the main problem lies.
Most SWGs rely on the ability to detect application-level attacks from network traffic before the traffic reaches the browser. If the traffic is not recognized as malicious, SWG passes it to the user's browser, and it is at this stage that an attacker can perform an attack. Ramachandran argues that such architecture vulnerabilities are so fundamental that they cannot be fixed.
The "last-step build" technique uses a simple idea: a cybercriminal has access to a computer, which in this case is a browser, and can "build" an attack at the last moment using various techniques.
For example, a hacker can break up malware, use Web Assembly files, hide the malware in other files, and in other ways divide it into many small, unrecognizable parts. After splitting it into parts, an attacker can deliver malware and force the browser to assemble it without the security system's knowledge.
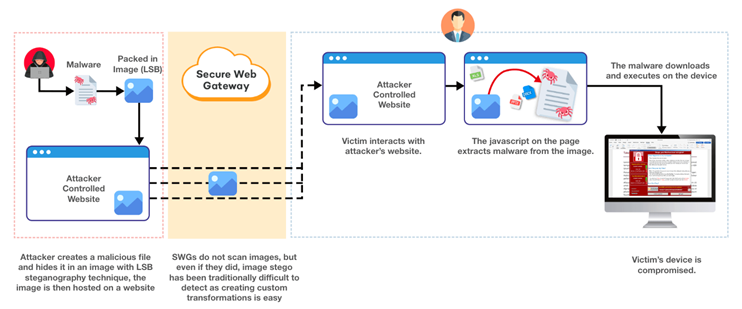
The malicious file is rebuilt directly in the browser, bypassingSWG
One of the reasons for this vulnerability is the age of the SWG. Systems are not able to cope with the modern complexity of web browsers, having a lot of uncontrolled channels, such as gRPC, WebRTC, WebSocket and WebTorrent, which go completely unnoticed.
Ramachandran claims that SWG vendors are aware of the existence of some of the vulnerabilities discovered, but a fix would undermine their approach to security. The expert noted that SWGs can only stop the most basic attacks. To fully detect all attacks, a full emulation of each open browser window would be required, so that the gateway is aware of the application context, which is almost impossible.
Although Ramachandran did not name specific manufacturers, so as not to create a negative background, the expert strongly recommends that information security specialists and company managers realize that the systems they rely on to protect users ' web activity may not be able to cope with their task.
Ramachandran also suspects some of the attacks (featured at Def Con) they are already actively used in real conditions. In this regard, SquareX has released a free tool to check the vulnerability of existing SWG settings.
To protect against such attacks, companies should focus on end-device protection. It is in the browser that attacks occur, and only here can they be detected. However, many SWG customers may not have sufficient protection on their end devices, as they rely on vendors claims that cloud solutions can fully protect against malware. Last-step build attacks are becoming a strong argument for the need to rethink approaches to protecting endpoints.
Source
SquareX and its founder Vivek Ramachandran, a well-known cybersecurity expert, recently discovered a vulnerability in the Secure Web Gateway (SWG) systems used to protect corporate networks. It turned out that all SWGs included in the Gartner Magic Quadrant rating for SASE and SSE can be bypassed and malware can be downloaded to the system without arousing suspicion from security systems.
Ramachandran has developed over 25 different SWG traversal methods. The hacking technique is called "Last Mile Reassembly". All methods of circumvention are reduced to one basic exploit — modern browsers remain out of sight of SWG systems.
SWGs were created more than 15 years ago and were originally used as an SSL proxy to intercept traffic, but with the development of cloud technologies, their functionality has become much broader. This is where the main problem lies.
Most SWGs rely on the ability to detect application-level attacks from network traffic before the traffic reaches the browser. If the traffic is not recognized as malicious, SWG passes it to the user's browser, and it is at this stage that an attacker can perform an attack. Ramachandran argues that such architecture vulnerabilities are so fundamental that they cannot be fixed.
The "last-step build" technique uses a simple idea: a cybercriminal has access to a computer, which in this case is a browser, and can "build" an attack at the last moment using various techniques.
For example, a hacker can break up malware, use Web Assembly files, hide the malware in other files, and in other ways divide it into many small, unrecognizable parts. After splitting it into parts, an attacker can deliver malware and force the browser to assemble it without the security system's knowledge.
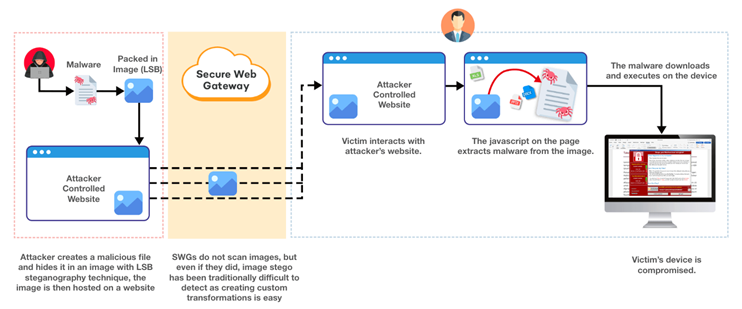
The malicious file is rebuilt directly in the browser, bypassingSWG
One of the reasons for this vulnerability is the age of the SWG. Systems are not able to cope with the modern complexity of web browsers, having a lot of uncontrolled channels, such as gRPC, WebRTC, WebSocket and WebTorrent, which go completely unnoticed.
Ramachandran claims that SWG vendors are aware of the existence of some of the vulnerabilities discovered, but a fix would undermine their approach to security. The expert noted that SWGs can only stop the most basic attacks. To fully detect all attacks, a full emulation of each open browser window would be required, so that the gateway is aware of the application context, which is almost impossible.
Although Ramachandran did not name specific manufacturers, so as not to create a negative background, the expert strongly recommends that information security specialists and company managers realize that the systems they rely on to protect users ' web activity may not be able to cope with their task.
Ramachandran also suspects some of the attacks (featured at Def Con) they are already actively used in real conditions. In this regard, SquareX has released a free tool to check the vulnerability of existing SWG settings.
To protect against such attacks, companies should focus on end-device protection. It is in the browser that attacks occur, and only here can they be detected. However, many SWG customers may not have sufficient protection on their end devices, as they rely on vendors claims that cloud solutions can fully protect against malware. Last-step build attacks are becoming a strong argument for the need to rethink approaches to protecting endpoints.
Source
