Carding
Professional
- Messages
- 2,870
- Reaction score
- 2,522
- Points
- 113
Your favorite URL shortening tool may be used against you.
Cybersecurity experts from the nao-sec discovered a large-scale cyberattack campaign targeting Taiwanese government organizations. The attacks are reportedly being carried out by a Chinese hacking group, which is being tracked by experts under the code name "GroundPeony". The group has a lot of similarities with the cybercrime group "UNC33471", so it is likely that we are talking about the same hackers.
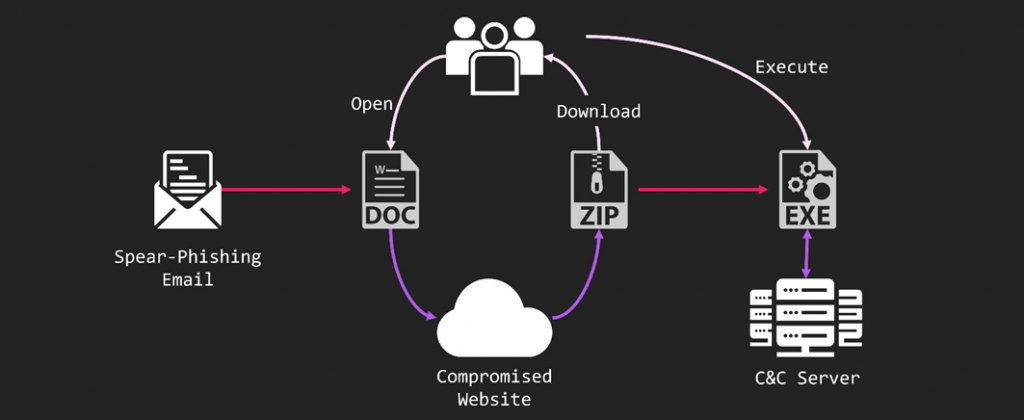
GroundPeony Attack Chain
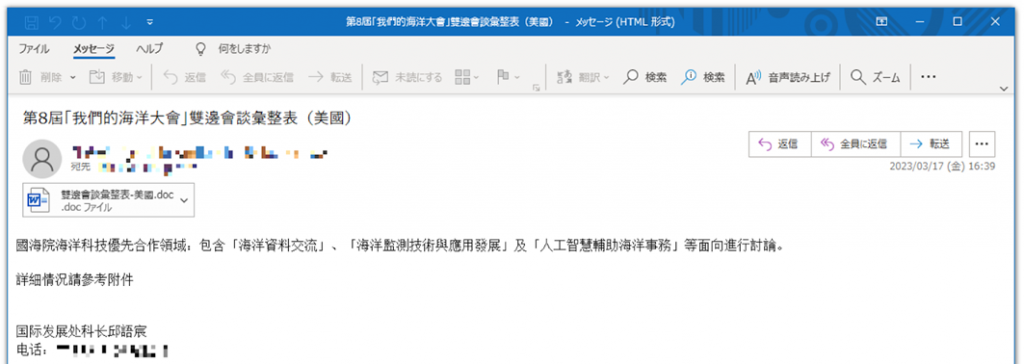
In most attacks, GroundPeony exploits the CVE-2022-30190 vulnerability, codenamed Folina. The attack chain starts with sending a phishing email with an attached DOC file. As the subject of their phishing emails, the GroundPeony hackers used sea traffic between Taiwan and the United States to make them more convincing to the victim.
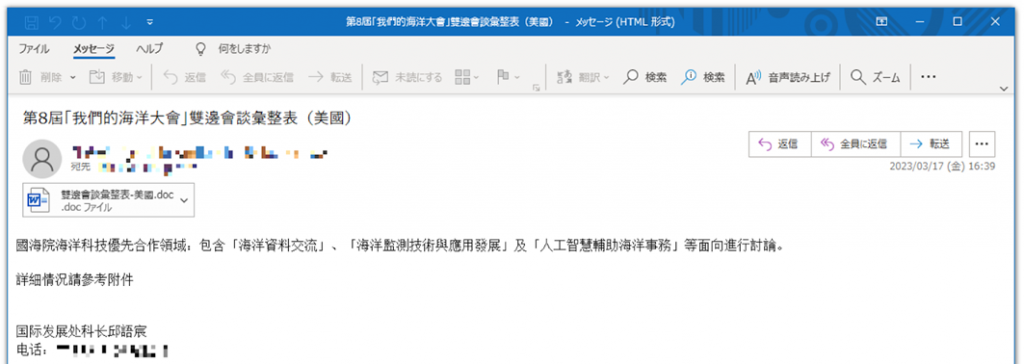
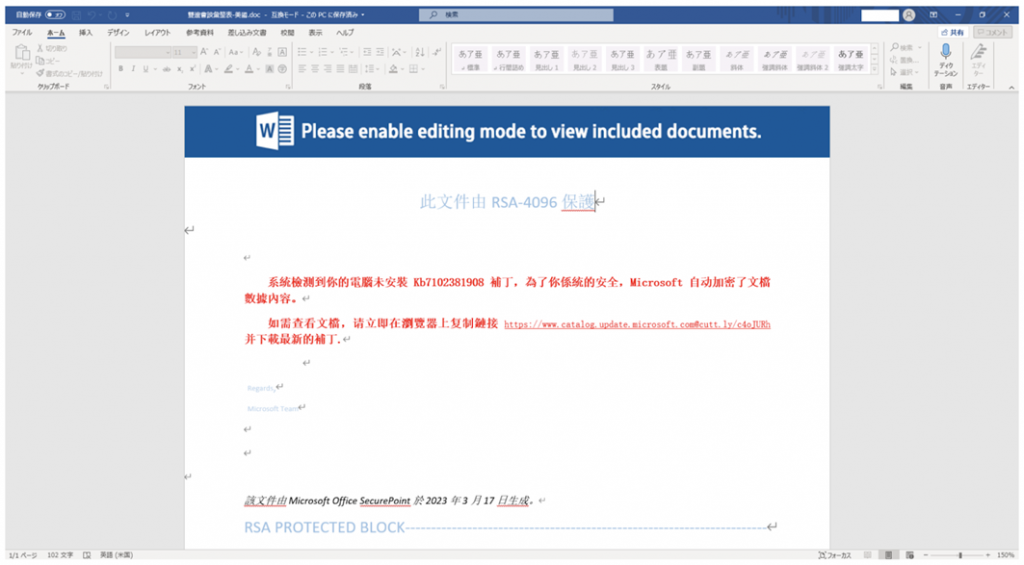
A harmless attachment with a "surprise" inside
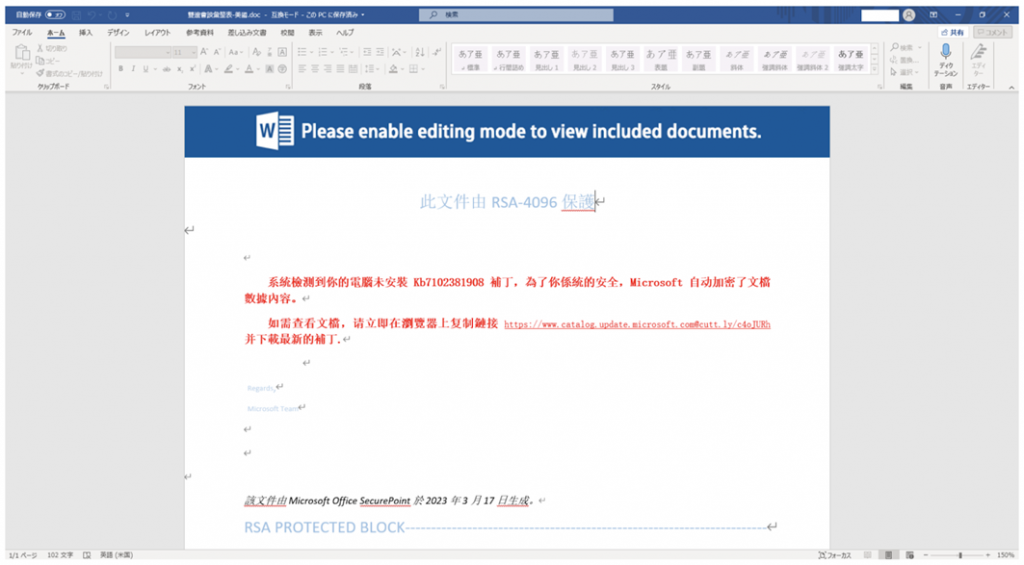
When you run the attached file, the potential victim sees an error notification that the contents of the file cannot be viewed without installing a special update. The same "notification" contains a link to the supposedly official Microsoft website, where you can download the necessary update. But in fact, the directory belongs to fraudsters, and hackers used the link shortening service Cuttly to mask the URL.
Link to the malware archive
The downloaded ZIP archive contains an executable EXE file and a DLL library for infecting your computer with malware. Running the program opens a channel for attackers to use to deliver any payload to a compromised device, whether it's infostealers, ransomware, vipers, or other malicious programs.
Analysis of the technical details of the attacks showed that the GroundPeony group has been operating since 2021 and is primarily aimed at government organizations in Taiwan and Nepal. Experts believe that hackers have a high level of skill and access to 0-day vulnerabilities.
Cybersecurity professionals whose organizations are at risk should strengthen their anti-phishing measures and carefully check suspicious files and links. However, only increased vigilance will definitely help you avoid becoming a victim of clever scammers.
(c) https://www.securitylab.ru/news/541176.php
Cybersecurity experts from the nao-sec discovered a large-scale cyberattack campaign targeting Taiwanese government organizations. The attacks are reportedly being carried out by a Chinese hacking group, which is being tracked by experts under the code name "GroundPeony". The group has a lot of similarities with the cybercrime group "UNC33471", so it is likely that we are talking about the same hackers.
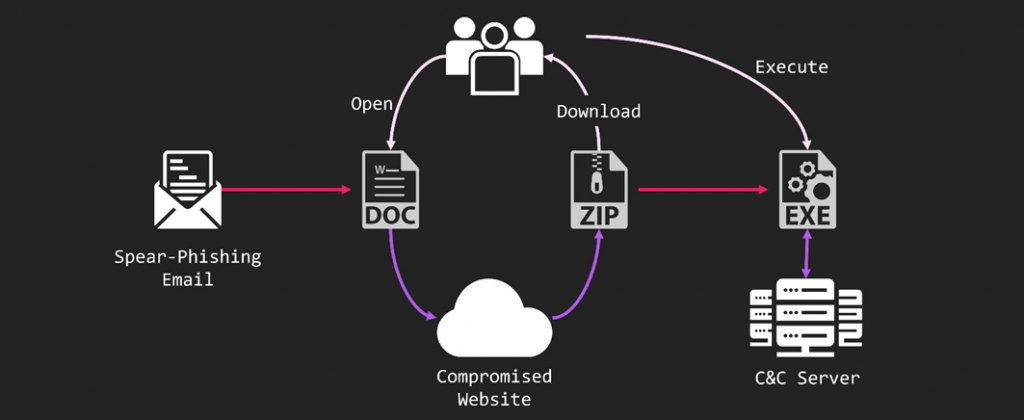
GroundPeony Attack Chain
In most attacks, GroundPeony exploits the CVE-2022-30190 vulnerability, codenamed Folina. The attack chain starts with sending a phishing email with an attached DOC file. As the subject of their phishing emails, the GroundPeony hackers used sea traffic between Taiwan and the United States to make them more convincing to the victim.
A harmless attachment with a "surprise" inside
When you run the attached file, the potential victim sees an error notification that the contents of the file cannot be viewed without installing a special update. The same "notification" contains a link to the supposedly official Microsoft website, where you can download the necessary update. But in fact, the directory belongs to fraudsters, and hackers used the link shortening service Cuttly to mask the URL.
Link to the malware archive
The downloaded ZIP archive contains an executable EXE file and a DLL library for infecting your computer with malware. Running the program opens a channel for attackers to use to deliver any payload to a compromised device, whether it's infostealers, ransomware, vipers, or other malicious programs.
Analysis of the technical details of the attacks showed that the GroundPeony group has been operating since 2021 and is primarily aimed at government organizations in Taiwan and Nepal. Experts believe that hackers have a high level of skill and access to 0-day vulnerabilities.
Cybersecurity professionals whose organizations are at risk should strengthen their anti-phishing measures and carefully check suspicious files and links. However, only increased vigilance will definitely help you avoid becoming a victim of clever scammers.
(c) https://www.securitylab.ru/news/541176.php
