Teacher
Professional
- Messages
- 2,669
- Reaction score
- 829
- Points
- 113
Michael Buzzel's story on how to protect your personal data from leaks. Michael – an iconic figure in the field of OSINT, worked in the US government and the FBI, he was invited as a technical expert in the series "Mr. Robot", which is considered worthy from the point of view of authenticity. In his personal life, the expert adheres to such strict rules regarding information hygiene that some consider him "inadequate". There may be several opinions on whether this is true.
One of the factors that convinces Michael of the right approach is that the risks of finding your data on the Internet have become significantly higher, because cryptographers indiscriminately merge everything they can reach into the network during attacks on businesses.
Corporations attack, but people suffer
Most people do not think about how they are affected by the problem of the spread of cryptographic viruses. The logic is as follows: we are talking about the problems of companies, they are forced to pay a ransom. What does it have to do with seemingly ordinary people?!
And despite the fact that criminals have changed their tactics: now they not only encrypt data, but also download it, put it in the public domain, if the companies do not pay them a ransom. Now let's think about what's in these merged databases? A lot of data about employees, clients, and contractors that the victim company works with.
I want to clarify right away: I'm not writing this because I'm in favor of paying a ransom. I am in favor of resisting excessive data collection where it is not necessary. We treat our personal data negligently, distributing them on demand.
Below are examples of how such credulity can turn out.
Disenfranchised car owners and dealers
I once said that I never buy cars in my own name (only in the name of an LLC or trust) and do not allow car dealerships to keep copies of my personal driver's license. After that, I was called paranoid. In my defense, I cite the history of customers of a Mercedes dealership attacked by the hacker group Dopple. Car buyers can now view their ID scans on the Dopple Tor website. And not only they, but also everyone who wants to earn extra money on confidential information. Below is one of countless driver's license samples.

Even worse, the entire world can now see loan applications, reports on them, approvals and refusals. These documents, in addition to the vehicle's characteristics, disclose the owner's full name, date of birth, social Security number (SSN), address, and employer information.

A credit report also discloses a person's credit score, bank account numbers, and credit card balances.

So my paranoia doesn't seem so paranoid anymore?
I use the same scheme with an LLC or trust when I need to rent or rent a property. Everyone who has come across this case knows that you have to sign a lot of contracts. And those, as practice shows, can easily be freely available. Below is a screenshot of the contract, which was freely available after the Canadian real estate management company ignored the hackers' demands to pay the ransom.

Pay your taxes and sleep restlessly
Accountants also like to make copies of clients documents. My financial lawyer rolls his eyes in horror when I insist that he store the data in encrypted form and send it only via encrypted email. If it can't do that, then I should be responsible for storing the data myself.
I believe that these precautions are justified. This is confirmed by the data published on the network of clients of a California law firm, disclosed by the hacker group Clop.

The database of leaks turned out to contain tax return forms indicating the payer's name, date of birth and social security number.

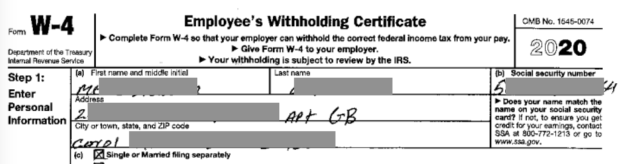
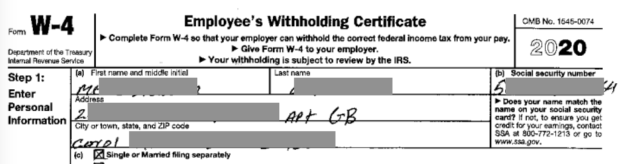
The same problem with the employer's accounting department. Confidential documents are often stored as ordinary, unimportant files. The result is shown in the screenshot where you can see the form W-4 (filled out to receive tax discounts in the United States), which belongs to an employee of a food production company. The document was made publicly available as a result of an attack by a cryptographer of the same Clop group.
I conduct all transactions on behalf of a legal entity and provide the employer only with an EIN (the American equivalent of an INN).
[Comment by searchinform_team: we are not strong in the subtleties of the document flow of American companies, let's trust the author that it is possible to build relationships with the employer in this way, unfortunately, he does not give details]
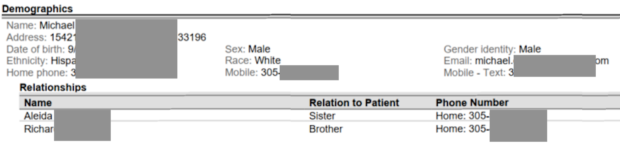
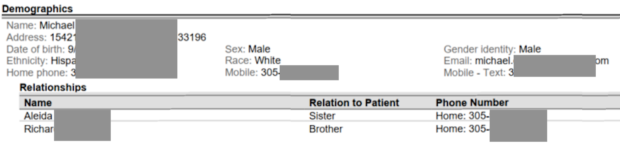
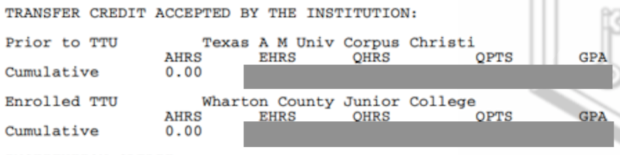
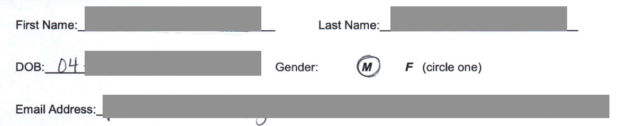
Universities and colleges also request personal data, store it, and send it out insecurely. Below is a student application form from the University of Miami. It contains the full name, address, date of birth, ethnicity, landline and mobile phone number, email address of the person and relatives.
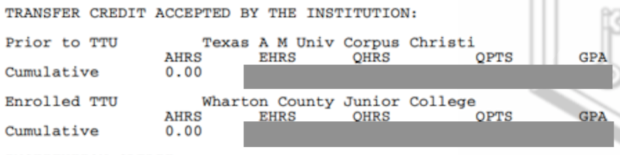
Documents of Colorado school students are also available on the Internet, in which both the class schedule and grades are available.

You can find out the overall GPA of each student.
And I can't give you any advice here, because as users, we can't influence what information educational institutions collect and how they store it.
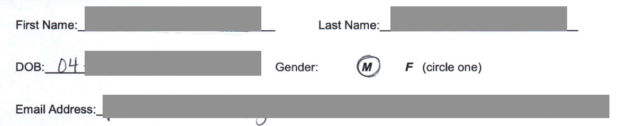
The same problem exists in healthcare institutions. All the forms that your doctor suggests you sign are rarely stored securely. Below is a screenshot of the patient's medical record, which hackers shared after his dentist refused to pay a ransom to the Conti group. Terabytes of patient data were published online.
I always resist requests from doctors to sign unnecessary documents and carefully study forms and questionnaires for compliance with HIPAA standards (the law that defines the rules for storing and using medical data in the United States-approx. Searchinform_team). We can't give up everything that doctors ask of us, but we can minimize the risk of important data leaks.
Leaks concern not only medical records, but also photos of patients. Doctors often make them to record changes in the patient's condition. Hackers of the Vice Society group did not hesitate to post all images of patients on the Internet after they were refused to pay the ransom.

Knowing about this risk, I ask doctors to either not make unnecessary images, or delete them immediately after the procedure is completed.
Mail – and nothing personal
Many ransomware data leaks contain complete Outlook PST files, which include all incoming and outgoing email messages. Below is a list of these files, each several gigabytes in size, uploaded to the network after the victim refused to pay the ransom.

Therefore, I always assume that an email = a public email and never send an email that should not be available online. To exchange confidential information, I use instant messengers with end-to-end encryption.
What else comes across in public drains
Passwords. Many people believe that if your home or work computer is not connected to the Internet, then it is normal to store passwords there in a special unprotected folder. This is a common misconception, since attackers can gain access to such folders during the attack development process. We then see these passwords in public leaks. If you are so self-confident and store your password on a local computer, then at least store it in the password manager with encrypted data.
What else? Chats, including messages from victims and extortionists themselves. The result of these drains can even be useful and instructive. Below is an excerpt from the dialogue between a representative of the Cuba group and an employee of the attacked medical organization. Maybe this will serve as a lesson to someone and help in negotiations with criminals.

The next time an organization asks you to send your personal data or a copy of your ID card by mail, please read this post. If the organization ignores your refusal to provide confidential information, claiming that it is necessary, explain your concern with the examples described above. And more. If your friends or family think you're paranoid and fixated on protecting your sensitive data, you're not alone.
How do you like this scrupulous attitude to your data? Are you paranoid in your personal information security life, or do you prefer not to worry your head?
habrastorage.org
One of the factors that convinces Michael of the right approach is that the risks of finding your data on the Internet have become significantly higher, because cryptographers indiscriminately merge everything they can reach into the network during attacks on businesses.
Corporations attack, but people suffer
Most people do not think about how they are affected by the problem of the spread of cryptographic viruses. The logic is as follows: we are talking about the problems of companies, they are forced to pay a ransom. What does it have to do with seemingly ordinary people?!
And despite the fact that criminals have changed their tactics: now they not only encrypt data, but also download it, put it in the public domain, if the companies do not pay them a ransom. Now let's think about what's in these merged databases? A lot of data about employees, clients, and contractors that the victim company works with.
I want to clarify right away: I'm not writing this because I'm in favor of paying a ransom. I am in favor of resisting excessive data collection where it is not necessary. We treat our personal data negligently, distributing them on demand.
Below are examples of how such credulity can turn out.
Disenfranchised car owners and dealers
I once said that I never buy cars in my own name (only in the name of an LLC or trust) and do not allow car dealerships to keep copies of my personal driver's license. After that, I was called paranoid. In my defense, I cite the history of customers of a Mercedes dealership attacked by the hacker group Dopple. Car buyers can now view their ID scans on the Dopple Tor website. And not only they, but also everyone who wants to earn extra money on confidential information. Below is one of countless driver's license samples.

Even worse, the entire world can now see loan applications, reports on them, approvals and refusals. These documents, in addition to the vehicle's characteristics, disclose the owner's full name, date of birth, social Security number (SSN), address, and employer information.

A credit report also discloses a person's credit score, bank account numbers, and credit card balances.

So my paranoia doesn't seem so paranoid anymore?
I use the same scheme with an LLC or trust when I need to rent or rent a property. Everyone who has come across this case knows that you have to sign a lot of contracts. And those, as practice shows, can easily be freely available. Below is a screenshot of the contract, which was freely available after the Canadian real estate management company ignored the hackers' demands to pay the ransom.

Pay your taxes and sleep restlessly
Accountants also like to make copies of clients documents. My financial lawyer rolls his eyes in horror when I insist that he store the data in encrypted form and send it only via encrypted email. If it can't do that, then I should be responsible for storing the data myself.
I believe that these precautions are justified. This is confirmed by the data published on the network of clients of a California law firm, disclosed by the hacker group Clop.

The database of leaks turned out to contain tax return forms indicating the payer's name, date of birth and social security number.

The same problem with the employer's accounting department. Confidential documents are often stored as ordinary, unimportant files. The result is shown in the screenshot where you can see the form W-4 (filled out to receive tax discounts in the United States), which belongs to an employee of a food production company. The document was made publicly available as a result of an attack by a cryptographer of the same Clop group.
I conduct all transactions on behalf of a legal entity and provide the employer only with an EIN (the American equivalent of an INN).
[Comment by searchinform_team: we are not strong in the subtleties of the document flow of American companies, let's trust the author that it is possible to build relationships with the employer in this way, unfortunately, he does not give details]
Universities and colleges also request personal data, store it, and send it out insecurely. Below is a student application form from the University of Miami. It contains the full name, address, date of birth, ethnicity, landline and mobile phone number, email address of the person and relatives.
Documents of Colorado school students are also available on the Internet, in which both the class schedule and grades are available.

You can find out the overall GPA of each student.
And I can't give you any advice here, because as users, we can't influence what information educational institutions collect and how they store it.
The same problem exists in healthcare institutions. All the forms that your doctor suggests you sign are rarely stored securely. Below is a screenshot of the patient's medical record, which hackers shared after his dentist refused to pay a ransom to the Conti group. Terabytes of patient data were published online.
I always resist requests from doctors to sign unnecessary documents and carefully study forms and questionnaires for compliance with HIPAA standards (the law that defines the rules for storing and using medical data in the United States-approx. Searchinform_team). We can't give up everything that doctors ask of us, but we can minimize the risk of important data leaks.
Leaks concern not only medical records, but also photos of patients. Doctors often make them to record changes in the patient's condition. Hackers of the Vice Society group did not hesitate to post all images of patients on the Internet after they were refused to pay the ransom.

Knowing about this risk, I ask doctors to either not make unnecessary images, or delete them immediately after the procedure is completed.
Mail – and nothing personal
Many ransomware data leaks contain complete Outlook PST files, which include all incoming and outgoing email messages. Below is a list of these files, each several gigabytes in size, uploaded to the network after the victim refused to pay the ransom.

Therefore, I always assume that an email = a public email and never send an email that should not be available online. To exchange confidential information, I use instant messengers with end-to-end encryption.
What else comes across in public drains
Passwords. Many people believe that if your home or work computer is not connected to the Internet, then it is normal to store passwords there in a special unprotected folder. This is a common misconception, since attackers can gain access to such folders during the attack development process. We then see these passwords in public leaks. If you are so self-confident and store your password on a local computer, then at least store it in the password manager with encrypted data.
What else? Chats, including messages from victims and extortionists themselves. The result of these drains can even be useful and instructive. Below is an excerpt from the dialogue between a representative of the Cuba group and an employee of the attacked medical organization. Maybe this will serve as a lesson to someone and help in negotiations with criminals.

The next time an organization asks you to send your personal data or a copy of your ID card by mail, please read this post. If the organization ignores your refusal to provide confidential information, claiming that it is necessary, explain your concern with the examples described above. And more. If your friends or family think you're paranoid and fixated on protecting your sensitive data, you're not alone.
How do you like this scrupulous attitude to your data? Are you paranoid in your personal information security life, or do you prefer not to worry your head?
habrastorage.org
