Carding
Professional
- Messages
- 2,870
- Reaction score
- 2,522
- Points
- 113
Group-IB has revealed the underground W3LL Store market, which covers up cyber attacks on corporations.
A new report of the Group-IB information security company has attracted the attention of the international community. The study reveals details of the activities of W3LL, a threat actor that has so far remained in the shadows. The main focus of W3LL is Microsoft 365 corporate accounts.
The Group-IB team started tracking W3LL in 2017 and has been tracking the group's activity ever since. The report confirms that W3LL played a key role in compromising Microsoft 365 enterprise accounts. From October 2022 to July 2023, more than 56,000 such accounts were attacked in the United States, Australia, and Europe.
Underground Market W3LL Store
No less interesting is W3LL's creation of its own underground market — the W3LL Store. The platform offers a cybercrime community of at least 500 hackers a wide range of tools for cyber attacks. Among them is the W3LL Panel phishing suite, which can bypass two-factor authentication (2FA), and 16 other customizable tools for conducting BEC attacks (Business Email Compromise, BEC).
According to Group-IB estimates, the W3LL Store turnover over the past 10 months could reach about $500,000, which underlines the success and efficiency of the cybercrime group.
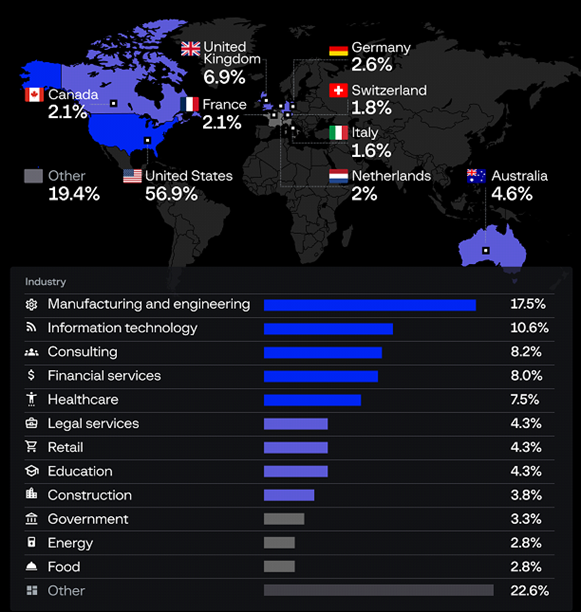
Victims of BEC attacks using W3LL tools
The Group-IB report also highlights security policy issues on the part of Microsoft. Experts criticize the company for its lack of transparency and responsibility in cybersecurity issues.
Group-IB stressed that the W3LL syndicate created not just an underground market, but an entire ecosystem for cybercrime. W3LL offers a comprehensive set of tools that can be used by cybercriminals of various levels of training. The Group-IB report is an important warning for the corporate sector and law enforcement agencies. The document focuses on the need to tighten security measures, especially for Microsoft 365 corporate accounts.
A new report of the Group-IB information security company has attracted the attention of the international community. The study reveals details of the activities of W3LL, a threat actor that has so far remained in the shadows. The main focus of W3LL is Microsoft 365 corporate accounts.
The Group-IB team started tracking W3LL in 2017 and has been tracking the group's activity ever since. The report confirms that W3LL played a key role in compromising Microsoft 365 enterprise accounts. From October 2022 to July 2023, more than 56,000 such accounts were attacked in the United States, Australia, and Europe.
Underground Market W3LL Store
No less interesting is W3LL's creation of its own underground market — the W3LL Store. The platform offers a cybercrime community of at least 500 hackers a wide range of tools for cyber attacks. Among them is the W3LL Panel phishing suite, which can bypass two-factor authentication (2FA), and 16 other customizable tools for conducting BEC attacks (Business Email Compromise, BEC).
According to Group-IB estimates, the W3LL Store turnover over the past 10 months could reach about $500,000, which underlines the success and efficiency of the cybercrime group.
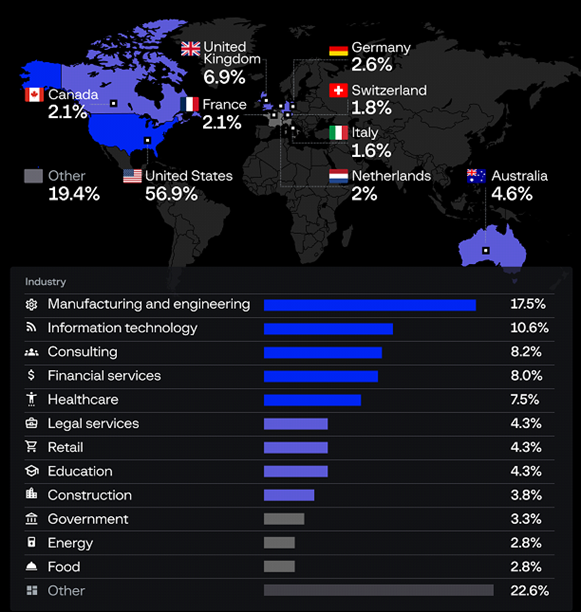
Victims of BEC attacks using W3LL tools
The Group-IB report also highlights security policy issues on the part of Microsoft. Experts criticize the company for its lack of transparency and responsibility in cybersecurity issues.
Group-IB stressed that the W3LL syndicate created not just an underground market, but an entire ecosystem for cybercrime. W3LL offers a comprehensive set of tools that can be used by cybercriminals of various levels of training. The Group-IB report is an important warning for the corporate sector and law enforcement agencies. The document focuses on the need to tighten security measures, especially for Microsoft 365 corporate accounts.
