Brother
Professional
- Messages
- 2,590
- Reaction score
- 541
- Points
- 113
Anyone can use this information if the buyer is not found in 7 days.
The Abdali Hospital, located in the modern-day Al-Abdali district of Amman, Jordan, has become another victim of the hacking group Rhysida. This is a multidisciplinary clinic that provides medical services in many areas.
In addition to the surgical department, the hospital has specialists in orthopedics and rheumatology, gynecology, urology and endocrinology, neurology, nephrology, pulmonology, therapy, oncology, infectious diseases and anesthesiology. Aesthetic areas are also represented: plastic surgery, dermatology, and the Women's Health Center.
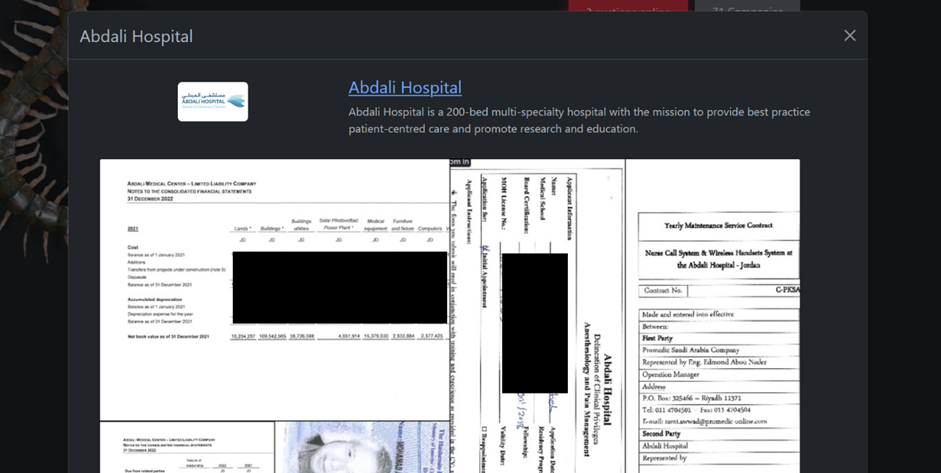
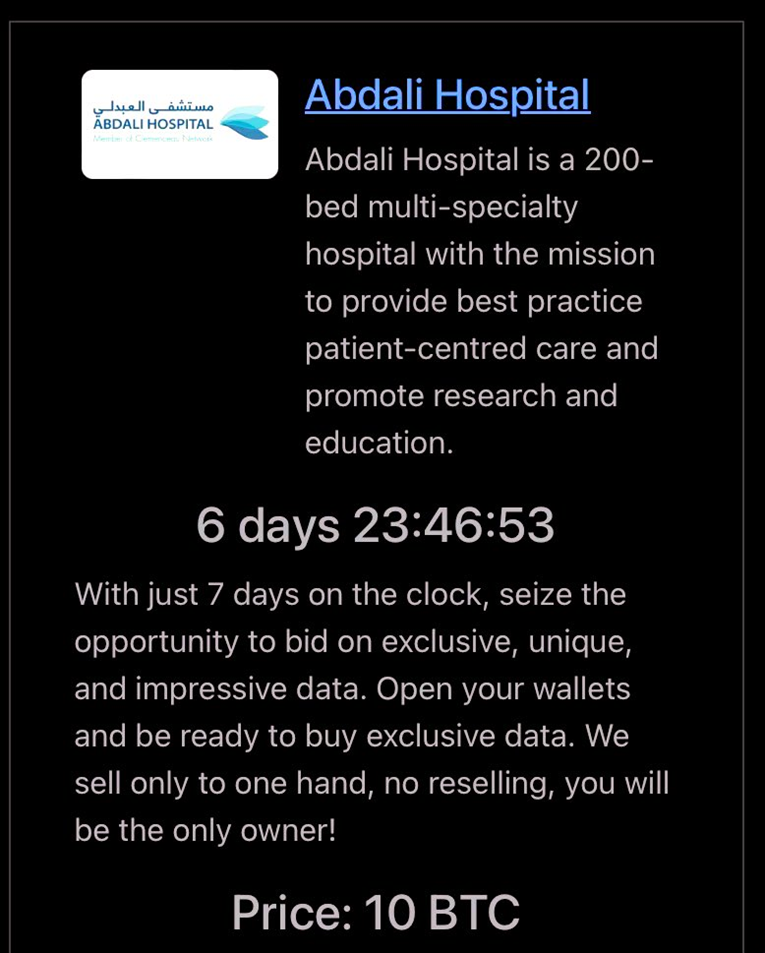
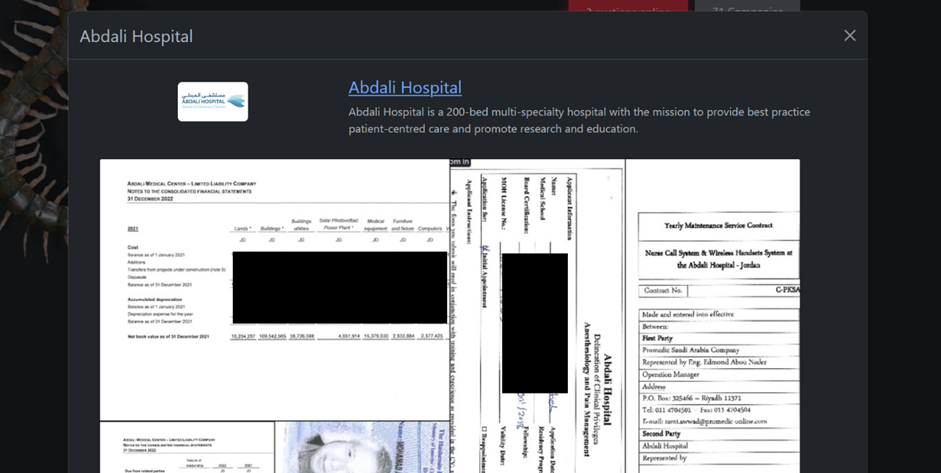
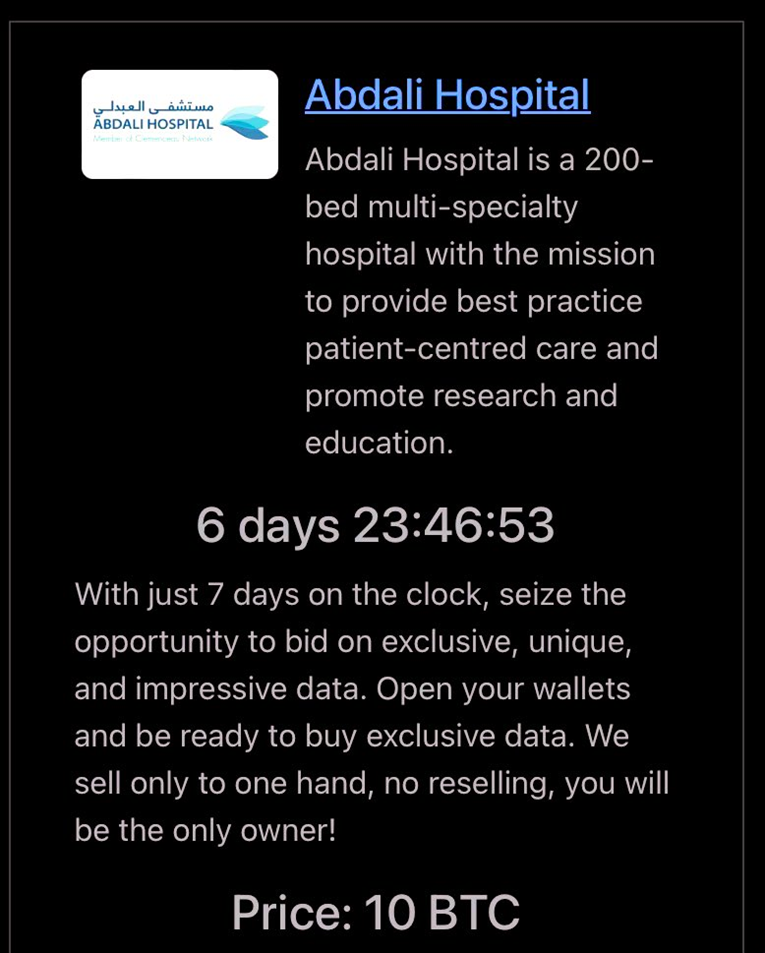
Hackers posted screenshots of stolen medical documents and employee ID cards on the darknet as proof of the attack. The data has already been put up for auction with a minimum value of 10 bitcoins.
The announcement posted on the site reads: "You only have 7 days to purchase exclusive and unique data. We sell information only in one hand, resale is prohibited. You will be the sole owner!".
Rhysida claims that in 7 days the stolen information will be publicly available.
In late November, they claimed to have hacked the King Edward VII Hospital in London, the British Library, and the Chinese Energy Engineering Corporation (CEEC).
Rhysida is effective from May 2023. According to the criminals themselves, during this time their victims were at least 62 companies in the fields of education, healthcare, manufacturing, IT and the public sector.
Last week, the FBI and the U.S. Cybersecurity Agency (CISA) issued a joint alert about the threat posed by this group. The document specifies the methods and indicators of compromise used.
It is noted that the attackers operate on the Ransomware-as-a-Service (RaaS) model, providing their tools and infrastructure for rent. The repurchases received are divided between the group and its affiliates.
Hackers use vulnerabilities in external remote services, such as VPN and RDP, as well as compromised credentials to gain access to systems. Cases of Zerologon vulnerability exploitation in phishing attacks have been noted. In addition, Rhysida often uses the built-in network tools of operating systems.
The Abdali Hospital, located in the modern-day Al-Abdali district of Amman, Jordan, has become another victim of the hacking group Rhysida. This is a multidisciplinary clinic that provides medical services in many areas.
In addition to the surgical department, the hospital has specialists in orthopedics and rheumatology, gynecology, urology and endocrinology, neurology, nephrology, pulmonology, therapy, oncology, infectious diseases and anesthesiology. Aesthetic areas are also represented: plastic surgery, dermatology, and the Women's Health Center.
Hackers posted screenshots of stolen medical documents and employee ID cards on the darknet as proof of the attack. The data has already been put up for auction with a minimum value of 10 bitcoins.
The announcement posted on the site reads: "You only have 7 days to purchase exclusive and unique data. We sell information only in one hand, resale is prohibited. You will be the sole owner!".
Rhysida claims that in 7 days the stolen information will be publicly available.
In late November, they claimed to have hacked the King Edward VII Hospital in London, the British Library, and the Chinese Energy Engineering Corporation (CEEC).
Rhysida is effective from May 2023. According to the criminals themselves, during this time their victims were at least 62 companies in the fields of education, healthcare, manufacturing, IT and the public sector.
Last week, the FBI and the U.S. Cybersecurity Agency (CISA) issued a joint alert about the threat posed by this group. The document specifies the methods and indicators of compromise used.
It is noted that the attackers operate on the Ransomware-as-a-Service (RaaS) model, providing their tools and infrastructure for rent. The repurchases received are divided between the group and its affiliates.
Hackers use vulnerabilities in external remote services, such as VPN and RDP, as well as compromised credentials to gain access to systems. Cases of Zerologon vulnerability exploitation in phishing attacks have been noted. In addition, Rhysida often uses the built-in network tools of operating systems.

