Carding 4 Carders
Professional
- Messages
- 2,724
- Reaction score
- 1,598
- Points
- 113
The user's inattention may result in the loss of confidential data.
Specialists of the information security company Malwarebytes discovered the Google Ads advertising campaign, which directs users to the fake KeePass site. To mask their malicious actions, attackers use the Punycode method to make their malicious domain look like the official KeePass domain.
Google has long struggled with such fraudulent advertising campaigns, where threats appear as ads above search results. Moreover, Google Ads can be used to display a legitimate KeePass domain in ads, making it difficult for even advanced users to detect the threat.
Attackers use Punycode, an encoding method to represent Unicode characters in ASCII format. This method allows you to convert domains that are not written in the Latin alphabet (Cyrillic, Arabic, Greek, etc.) to make them understandable for DNS.
In this case, the hackers used Punycode "xn-eepass-vbb.info" what is broadcast in "ķeepass.info – - almost identical to the real domain. Such a small visual error is unlikely to be noticed by the user, but it is a clear sign of using this technique.
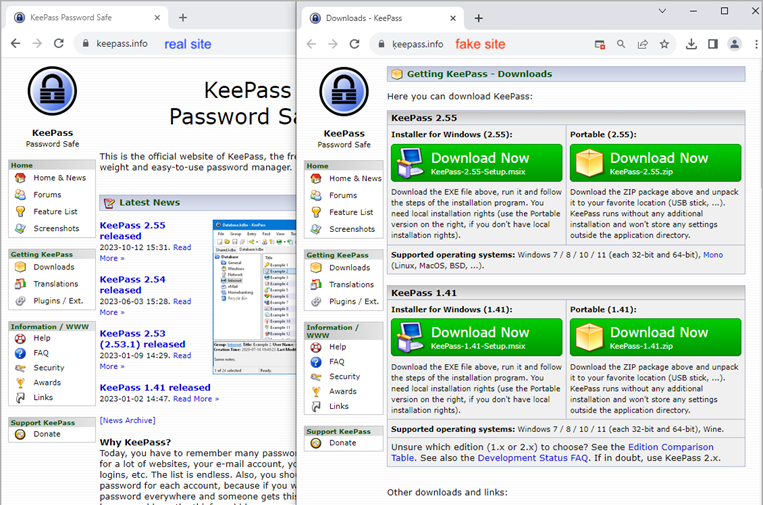
Real (left) and fake site (right)
The fake site contains download links leading to the file 'KeePass-2.55-Setup.msix', which contains a PowerShell script linked to the malicious FakeBat downloader. Although Google removed the original ad from Punycode, additional KeePass ads were found linked to the same malicious campaign.
FakeBat has previously been associated with malware-spreading ad campaigns since at least November 2022. The ultimate target of malware in the campaign detected by Malwarebytes has not yet been established, but FakeBat usually distributed Redline Stealer, Ursnif, and Rhadamathys infostilers in its campaigns.
Specialists of the information security company Malwarebytes discovered the Google Ads advertising campaign, which directs users to the fake KeePass site. To mask their malicious actions, attackers use the Punycode method to make their malicious domain look like the official KeePass domain.
Google has long struggled with such fraudulent advertising campaigns, where threats appear as ads above search results. Moreover, Google Ads can be used to display a legitimate KeePass domain in ads, making it difficult for even advanced users to detect the threat.
Attackers use Punycode, an encoding method to represent Unicode characters in ASCII format. This method allows you to convert domains that are not written in the Latin alphabet (Cyrillic, Arabic, Greek, etc.) to make them understandable for DNS.
In this case, the hackers used Punycode "xn-eepass-vbb.info" what is broadcast in "ķeepass.info – - almost identical to the real domain. Such a small visual error is unlikely to be noticed by the user, but it is a clear sign of using this technique.
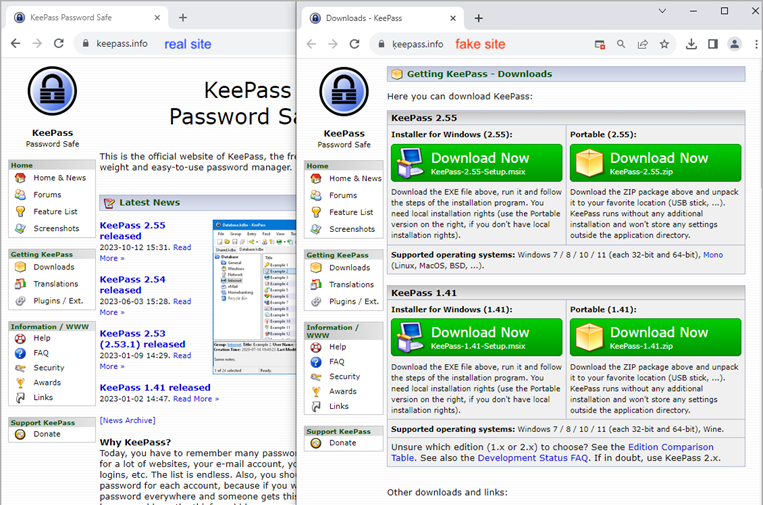
Real (left) and fake site (right)
The fake site contains download links leading to the file 'KeePass-2.55-Setup.msix', which contains a PowerShell script linked to the malicious FakeBat downloader. Although Google removed the original ad from Punycode, additional KeePass ads were found linked to the same malicious campaign.
FakeBat has previously been associated with malware-spreading ad campaigns since at least November 2022. The ultimate target of malware in the campaign detected by Malwarebytes has not yet been established, but FakeBat usually distributed Redline Stealer, Ursnif, and Rhadamathys infostilers in its campaigns.

