Carder
Professional
- Messages
- 2,620
- Reaction score
- 2,043
- Points
- 113
New browser trackers can track your activity even when you are connected to a VPN and activate incognito mode
The fact that a user's actions can be tracked by the sites they visit has led to the emergence of confidential browsers and extensions such as Privacy Badger. Users also turn on incognito mode while browsing the Internet and regularly delete cookies. However, all these precautions are useless against the new kind of trackers.
These trackers use favicons, tiny icons that appear along with the site in the browser tab and in the bookmark list. Researchers at the University of Illinois at Chicago said in a new article that most browsers cache these images in a folder separate from browsing history and cookie data. Sites can abuse this fact by loading a number of favicons into the user's browser that will track their activity over a long period of time.
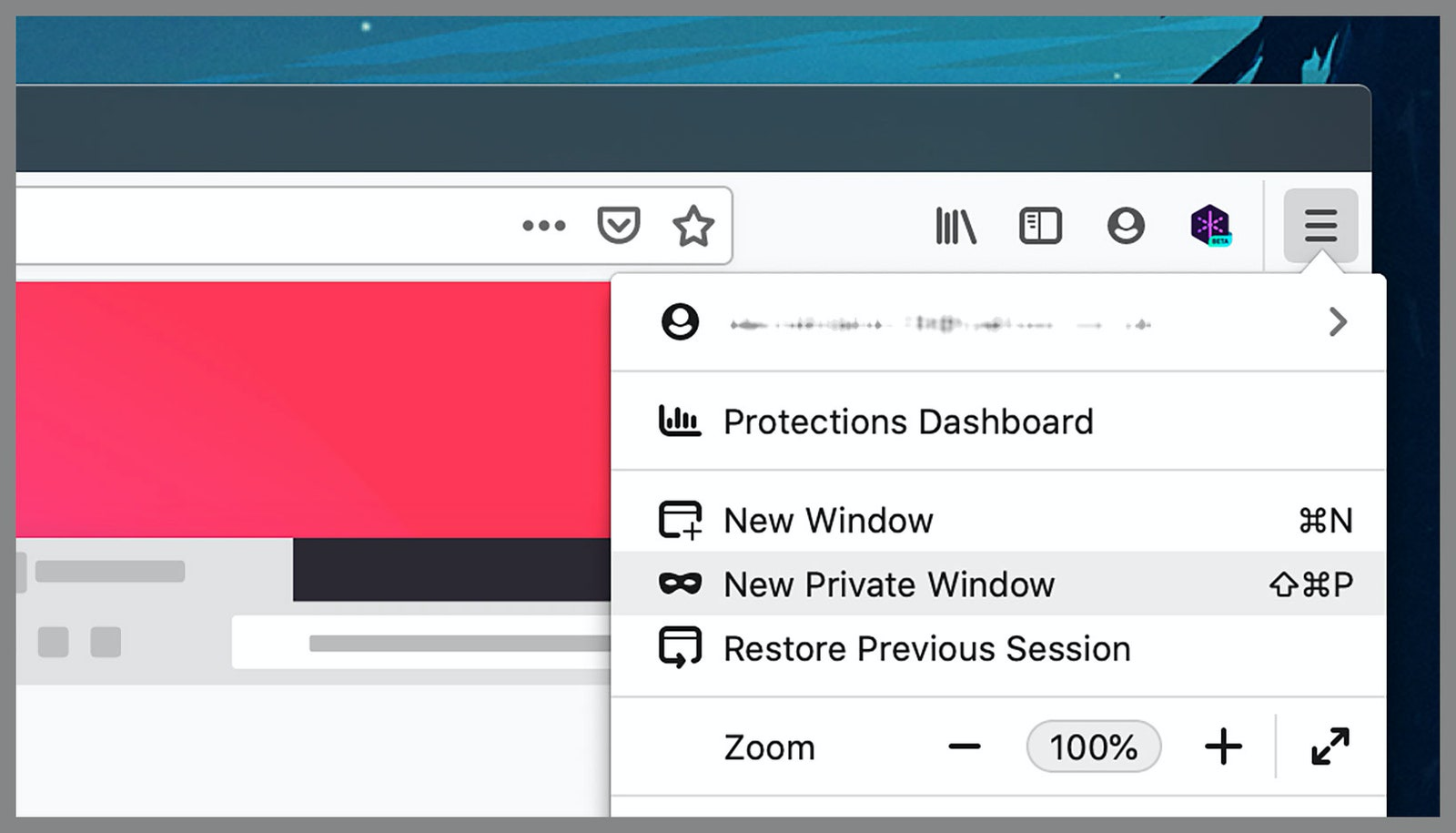
Your actions can be easily tracked if you use Chrome, Safari and Edge. It is worth noting that the Brave developers have already created effective countermeasures to this type of surveillance. They were only able to do this after receiving a private report from researchers at the University of Chicago.Firefox is not susceptible to this type of attack as it has a number of favicon caching bugs.
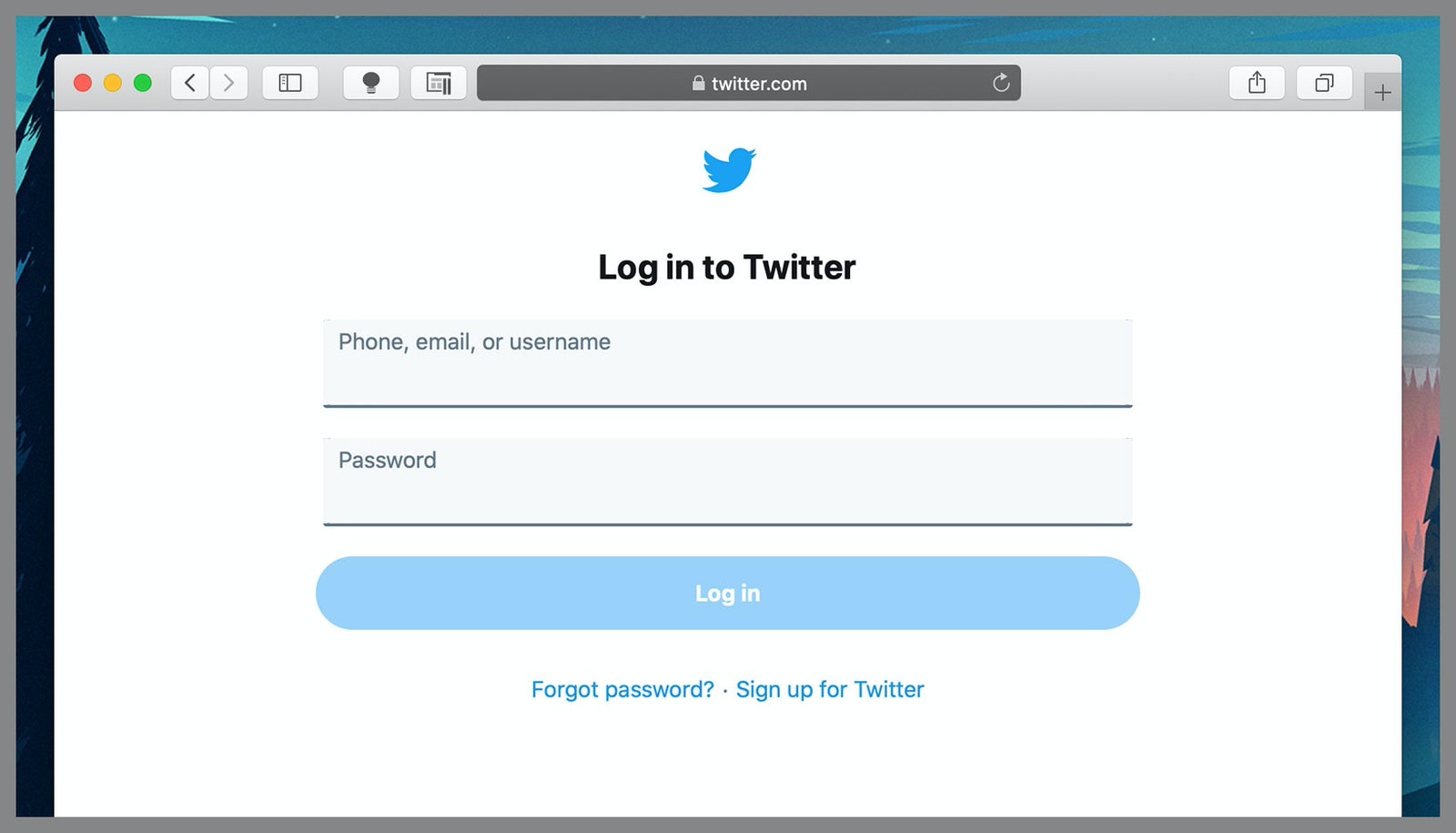
Browsers store favicons in a cache so they don't have to ask the website for them every time. This cache is not deleted when users clear their browser cache or cookies. It is actively used even if you switch to private browsing mode. The website saves a certain combination of favicons when a person first opens the resource pages. By checking for the presence of these images in the cache, a website can identify a specific user's browser when revisiting the resource. Even if a person uses proactive measures to prevent tracking, they will still be recognized.
Browser tracking has been a problem since the advent of the internet. Once users learned to delete cookies with ease, websites came up with new ways to identify their visitors.
One such method is known as tracking collecting digital fingerprint (or fingerprinting). This is a process during which information is collected about the screen size, the list of available fonts, the software version, and other properties of the user's computer. Thus, based on the collected data, a profile is created that is assigned to a specific machine. A 2013 study found that 1.5% of the world's most popular websites use this tracking method. Device fingerprinting is effective even when people use multiple browsers. As a countermeasure, some browsers have tried to limit this tracking, but often without success.
The article explains this as follows:
Researchers who dealt with this issue: Konstantinos Solomos, John Kristoff, Chris Kanich and Jason Polakis. They all work at the University of Illinois, Chicago.
A Google spokesman said the company is already aware of this type of tracking and is working on countermeasures. Meanwhile, an Apple spokesman says the company is only studying the results of the study. Researchers in Chicago have also contacted Microsoft and Brave, who have not provided any comment so far.
As noted earlier, Brave can block this kind of tracking.
The fact that a user's actions can be tracked by the sites they visit has led to the emergence of confidential browsers and extensions such as Privacy Badger. Users also turn on incognito mode while browsing the Internet and regularly delete cookies. However, all these precautions are useless against the new kind of trackers.
These trackers use favicons, tiny icons that appear along with the site in the browser tab and in the bookmark list. Researchers at the University of Illinois at Chicago said in a new article that most browsers cache these images in a folder separate from browsing history and cookie data. Sites can abuse this fact by loading a number of favicons into the user's browser that will track their activity over a long period of time.
"Powerful Tracking Vector"
“Although favicons have been considered for many years to be just a decorative addition to a site's name, because the browser shows them to the user to better remember the company's brand, research proves that they represent a 'powerful tracking vector'. This type of tracking hides a significant threat to user privacy, "- said the researchers in Chicago. Moreover, in their words:"With the help of favicons, tracking can be easily implemented by any website without the need for any user interaction or consent. The tracker will collect information about human actions even when using popular anti-tracking extensions. Moreover, the caching method in modern browsers makes such an attack on user data especially dangerous, as favicons are displayed (and cached) even when browsing in incognito mode. This is due to the application of incorrect privacy protection methods in all major browsers."
Your actions can be easily tracked if you use Chrome, Safari and Edge. It is worth noting that the Brave developers have already created effective countermeasures to this type of surveillance. They were only able to do this after receiving a private report from researchers at the University of Chicago.Firefox is not susceptible to this type of attack as it has a number of favicon caching bugs.
Browsers store favicons in a cache so they don't have to ask the website for them every time. This cache is not deleted when users clear their browser cache or cookies. It is actively used even if you switch to private browsing mode. The website saves a certain combination of favicons when a person first opens the resource pages. By checking for the presence of these images in the cache, a website can identify a specific user's browser when revisiting the resource. Even if a person uses proactive measures to prevent tracking, they will still be recognized.
Browser tracking has been a problem since the advent of the internet. Once users learned to delete cookies with ease, websites came up with new ways to identify their visitors.
One such method is known as tracking collecting digital fingerprint (or fingerprinting). This is a process during which information is collected about the screen size, the list of available fonts, the software version, and other properties of the user's computer. Thus, based on the collected data, a profile is created that is assigned to a specific machine. A 2013 study found that 1.5% of the world's most popular websites use this tracking method. Device fingerprinting is effective even when people use multiple browsers. As a countermeasure, some browsers have tried to limit this tracking, but often without success.
Two seconds is enough
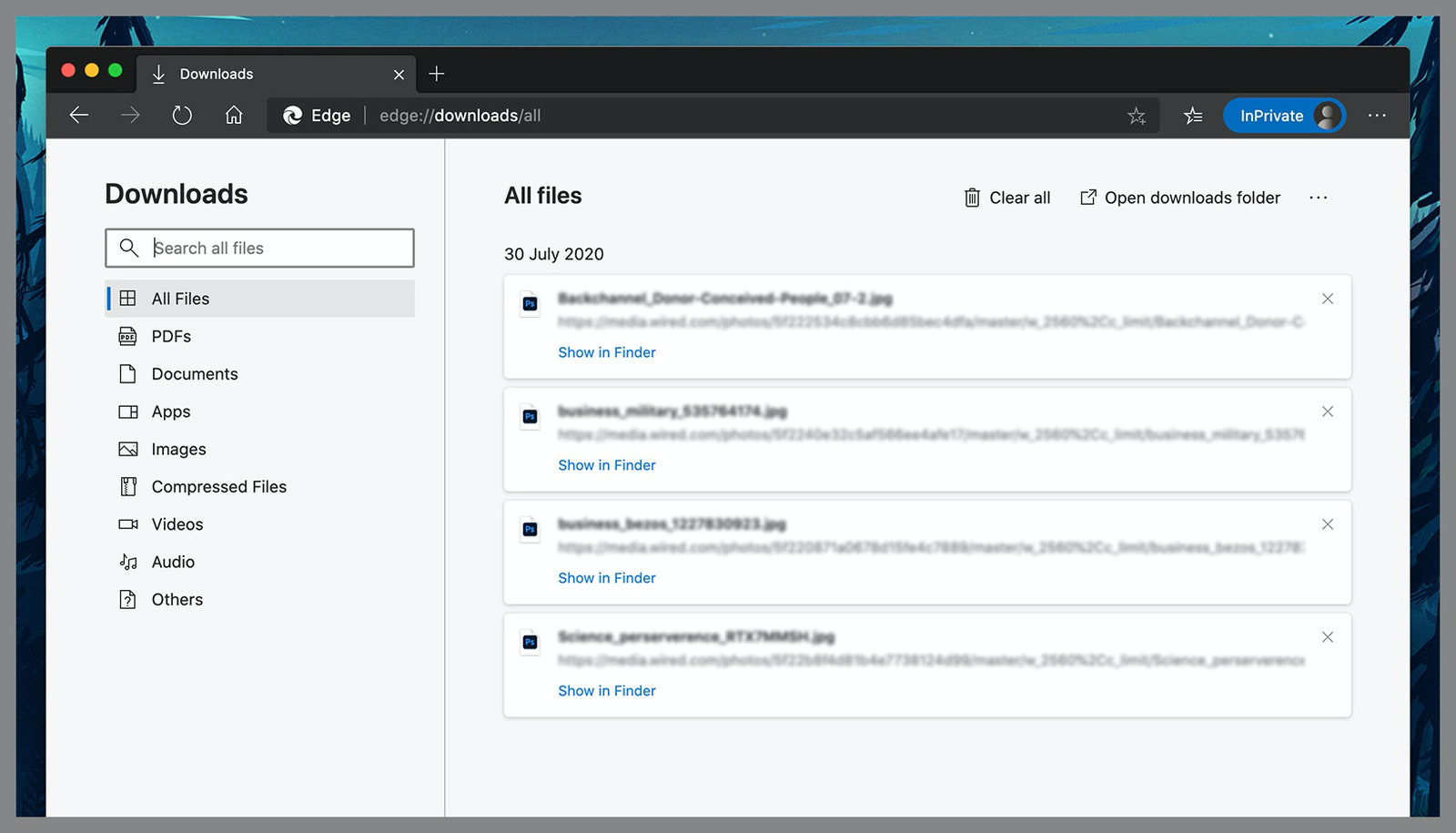
Websites can use this method by redirecting users through a range of subdomains (each with their own favicon) before they land on the requested page. The number of redirects required varies depending on the number of unique site visitors. To be able to track 4.5 billion unique browsers, a website would need to redirect a user 32 times. Each such redirect takes 1 bit of entropy. This adds about 2 seconds to the total load time of the page the user wants. Websites can reduce this latency by using custom settings.The article explains this as follows:
Taking into account the properties of modern browsers, we see a new mechanism for constantly tracking user activity, which makes it possible for websites to identify a person when he revisits a resource, even if he is using incognito mode or has previously cleared the cache. Specifically, websites can create and store a unique browser identifier using a combination of cache favicon entries. Moreover, this tracking can be done by any website. It only needs to redirect the user appropriately through a series of subdomains. These subdomains have different favicons and thus create their own favicon cache entries. A set of n-subdomains can be used to create an n-bit identifier that is unique to each browser.Since the attacker has complete control over the website, he can redirect the user through hundreds of subdomains without any interaction with it. In fact, the presence of a favicon in the subdomain cache corresponds to a value of 1 in the identifier bit, and its absence will result in a value of 0.
Researchers who dealt with this issue: Konstantinos Solomos, John Kristoff, Chris Kanich and Jason Polakis. They all work at the University of Illinois, Chicago.
A Google spokesman said the company is already aware of this type of tracking and is working on countermeasures. Meanwhile, an Apple spokesman says the company is only studying the results of the study. Researchers in Chicago have also contacted Microsoft and Brave, who have not provided any comment so far.
As noted earlier, Brave can block this kind of tracking.