Carder
Professional
- Messages
- 2,635
- Reaction score
- 2,067
- Points
- 113
Hello everyone. I think many people are interested in the question of how the infrastructure of professional cyber groups works. Why can't the police block some dark business domains? What services are immune to the request of the authorities? We'll talk about this today.
Each cyber group has its own specific set of network infrastructure requirements. Some need temporary servers for password guessing, network scanning, or sending phishing emails, while others need "bulletproof" hosting hidden behind a chain of reverse proxies. However, all the variety comes down to a few typical scenarios:
Thus, the criminal network infrastructure generally consists of the following areas::
Anonymous cards with a security guarantee
Any illegal activity forces you to use anonymous cards or wallets. Such cards can be purchased from trusted merchants with a guarantee of the safety of funds.
For example, the laws of Belize and Seychelles allow companies that provide such hosting services to ignore all requests from law enforcement agencies related to resources hosted on their facilities. As a result, many bulletproof hosting services are hosted there.
Another example is the placement of criminal hosting in a private house. Such an illegal data center, which contained more than 100 servers, was recently discovered and eliminated by the Ukrainian police.
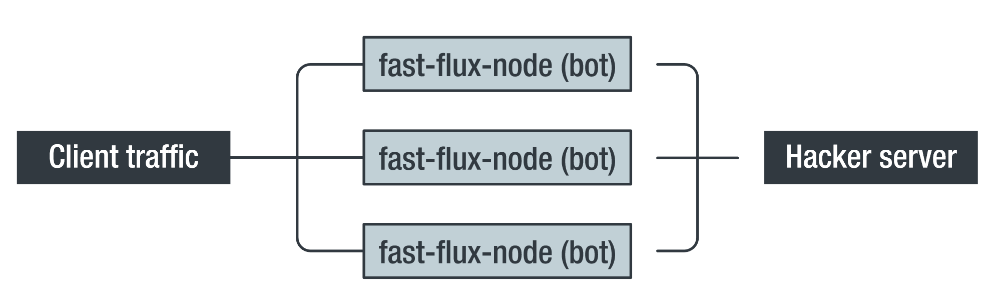
How fast-flux works as an intermediate-level service. Source (hereafter, unless otherwise stated): Trend Micro
The essence of the fast-flux method is to use short TTLS (time-to-live) for a-records in DNS. This prevents caching of the domain name on intermediate DNS servers and forces them to always request permission from declared domain name system (DNS) servers. Low TTL values allow attackers with high frequency to direct the domain to IP addresses in the dedicated pool and ensure the availability of the service, even if some of the addresses are compromised or banned by the provider.
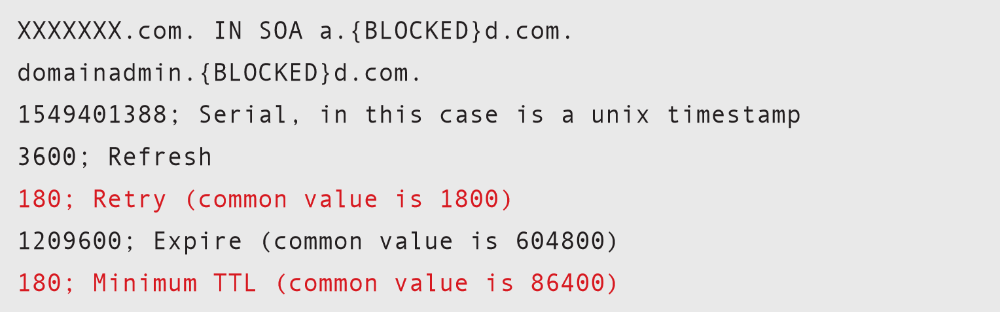
Fast-flux specific DNS records
The TTL values shown in red are set with an unusually low number of retries and a minimum TTL time (in seconds). Under normal circumstances, this will create additional load on the DNS server, but in the case of fast-flux, the goal is to suppress the caching mechanism so that the client is given an up-to-date IP address that is currently provided by the fast-flux infrastructure.
Fast-flux services are usually more expensive than bulletproof hosting, since their operator has to maintain a pool of IP addresses to provide a "fast-flux" infrastructure, and this requires additional costs.
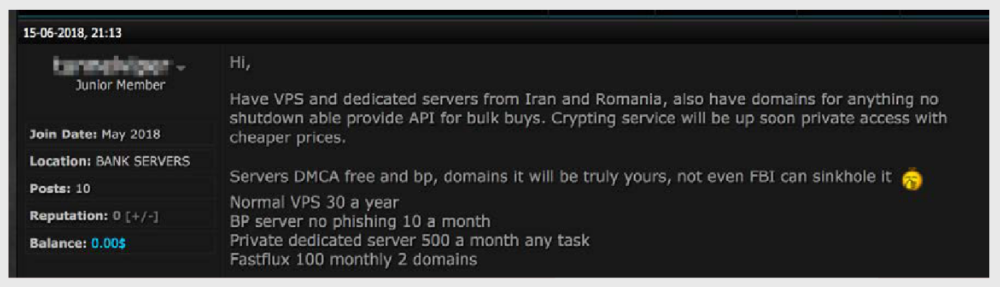
The cost of fast-flux services is $ 100 for two domains per month, while the monthly cost of renting a bulletproof server is $ 10
As a rule, such services are provided by placing a specialized resource like a WAF (Web Application Firewall) in front of the protected server.
To capture control, use:
Credentials for accessing the captured servers are subsequently sold on underground online stores:
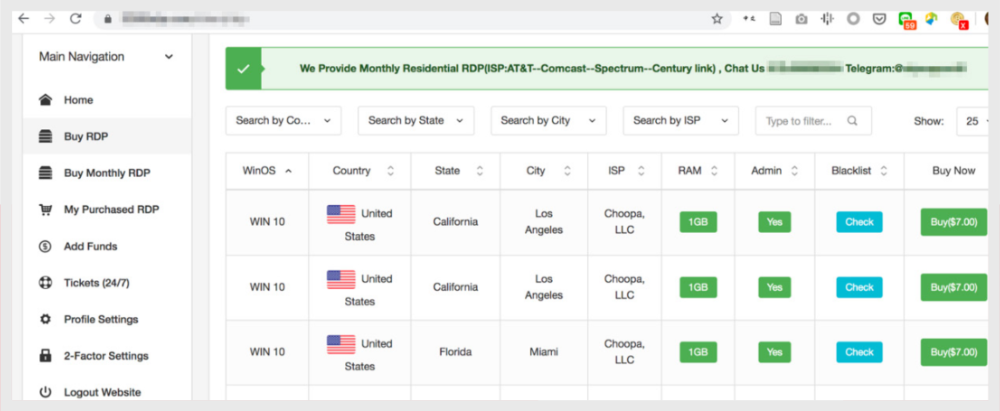
Online store of accounts for accessing compromised RDP servers
Taking over more secure servers may require zero-day vulnerabilities, which are also offered at cyberforums.
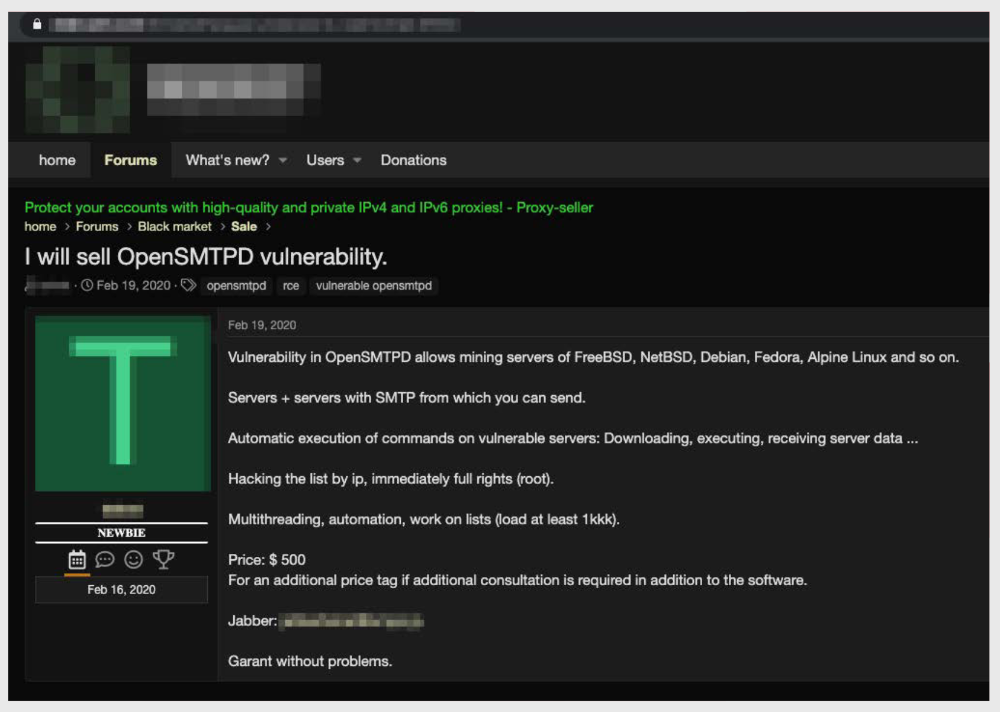
Announcement of the sale of a vulnerability in OpenSMTPD that allows you to compromise servers running on FreeBSD, NetBSD, Debian, Fedora and Alpine Linux and use them for hosting
For those who don't want to bother hacking their accounts, there are stores that offer already hacked Microsoft Azure and Google Cloud accounts.

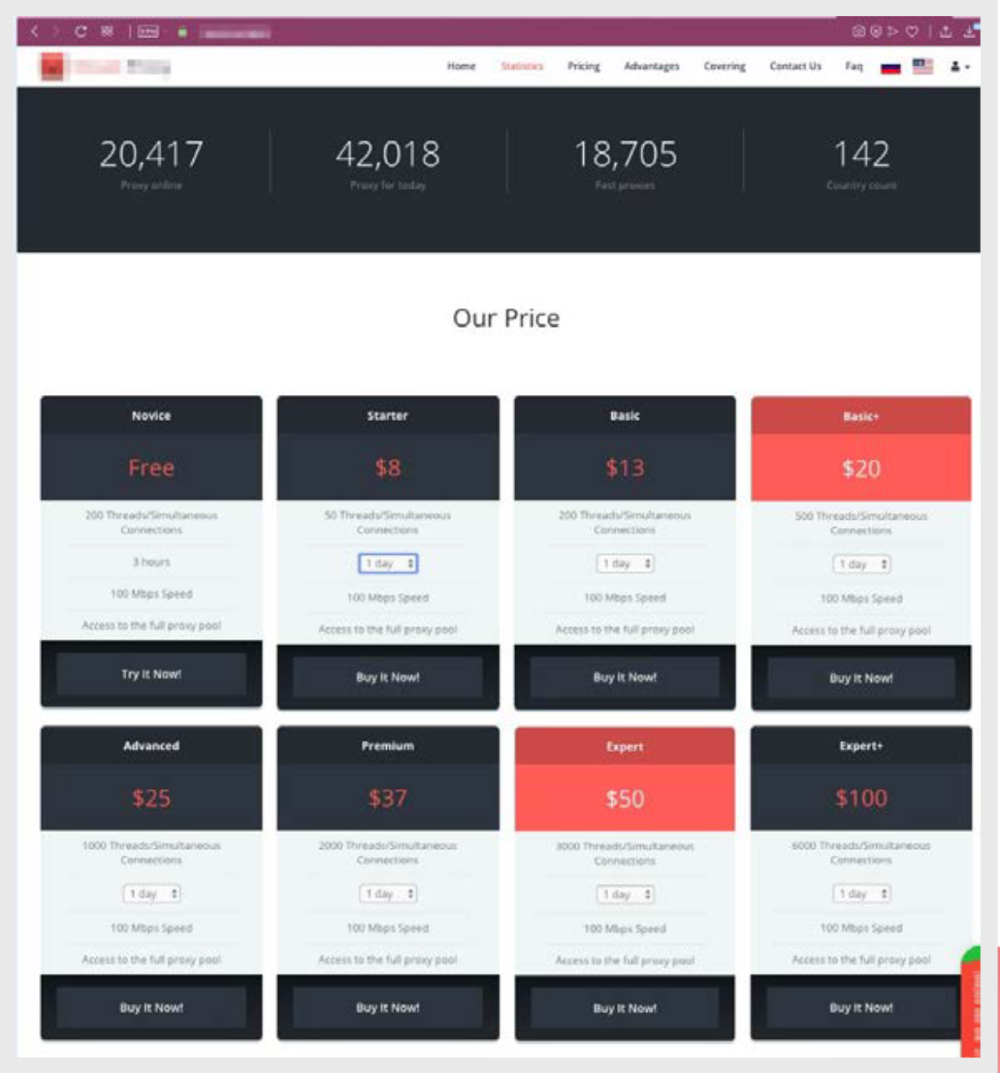
Due to the demand for this tool, it is relatively easy to find resources that offer to purchase SOCKS proxy, and you can pay for the purchase with cryptocurrency.
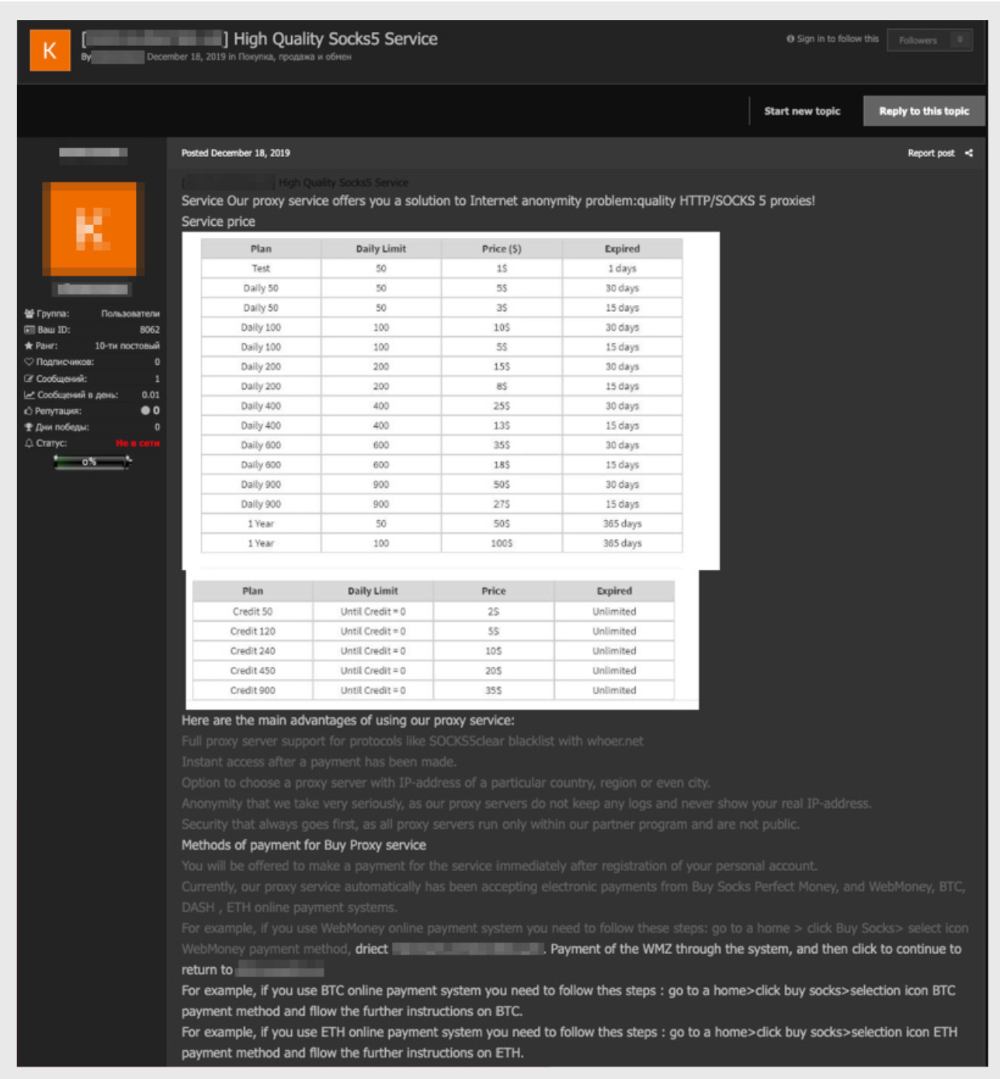
Price list for socks proxies that can be paid for using Bitcoin and Ethereum
Another way to hide communication is by tunneling into legitimate protocols, such as SSH:

Price list for SSH tunnels
The price of SSH tunnels depends on the country of their location. Location is very important for some illegal activities. For example, banks ' anti-fraud systems correlate information about the cardholder with the geolocation of the IP address at which it was attempted to be used. Therefore, criminals are willing to pay more to buy a tunnel that corresponds not only to the desired country, but also to the city.
One of the signs that indirectly indicates that compromised hosts are used to provide VPN services is the indication of the" availability guarantee period " of the service. The lower the numbers, the more suspicious these services are. It is unlikely that a legitimate VPN provider will write in the conditions that "in case the provided credentials do not work for the next 24 (48 or 72) hours, new credentials will be provided free of charge." But this is exactly what is usually present in the offers of illegal services.
Ad for the sale of short-lived VPNs
Another suspicious sign of a possible criminal nature of anonymization of services is the term of the agreement. Legal VPN providers provide services for at least a month, while in the criminal environment there are offers of VPN services for a period of no more than one day. It is difficult to imagine cases of legitimate use for which such a small amount of time is sufficient. However, for a criminal, this is quite enough to
Although the policy of this site formally prohibits the distribution of malware, we found ads on the forum hinting that other malicious actions are acceptable.:
The proposal mentions complete anonymity, the inability to determine the user's location, a high-speed Internet connection, DDoS protection, an outgoing traffic mixer, and five different VPNs. Despite the fact that direct port scanning, brute-forcing, and malware distribution are not allowed, an attacker can also commit other criminal acts using such workstations.
Custom services are also available for combining VPN connections, Tor, and geographically distributed router sets. These combinations allow you to create such a complex chain of hosts and redirectors that it is almost impossible to track them.
Traffic obfuscation chain suggestion
For example, one of the services offers to use the following chain::
Host → VPN1 → VPN2 → TOR → Bouncing traffic gateway → traffic mixer → geographically distributed routers for Bouncing traffic → remote desktop (RDP) for operation → connection via other geographically distributed routers → Tor servers → exit node → destination point.
Each cyber group has its own specific set of network infrastructure requirements. Some need temporary servers for password guessing, network scanning, or sending phishing emails, while others need "bulletproof" hosting hidden behind a chain of reverse proxies. However, all the variety comes down to a few typical scenarios:
- hosting sites with illegal or questionable content,
- hosting of the management infrastructure,
- hosting of service applications and components,
- hosting anonymizers, direct and reverse proxies,
- dedicated servers for scanning and brute-force attacks,
- platforms for phishing and sending spam.
Thus, the criminal network infrastructure generally consists of the following areas::
- special hosting services,
- hosting based on compromised servers,
- privacy and anonymity services,
- DNS services.
Anonymous cards with a security guarantee
Any illegal activity forces you to use anonymous cards or wallets. Such cards can be purchased from trusted merchants with a guarantee of the safety of funds.
Bulletproof hosting
Any illegal activity sooner or later leads to the fact that the resources associated with it become the object of attention of law enforcement agencies. And then the IP addresses of these resources are blocked, servers are seized, and domains are stripped. This situation leads to disruption of cyber attacks and the need to spend money on organizing new infrastructure. To avoid this situation, illegal structures resort to the services of services that are immune to police requests.For example, the laws of Belize and Seychelles allow companies that provide such hosting services to ignore all requests from law enforcement agencies related to resources hosted on their facilities. As a result, many bulletproof hosting services are hosted there.
Another example is the placement of criminal hosting in a private house. Such an illegal data center, which contained more than 100 servers, was recently discovered and eliminated by the Ukrainian police.
Fast-flux services
Fast-flux is a completely legal technology that is used to provide increased availability of services and load balancing by constantly switching domain name resolution to a pool of IP addresses. For criminals, this approach allows them to achieve increased resistance to hacking and interception, allowing them to hide the location of their server. A pool of IP addresses is often used to organize a chain of reverse proxy servers and can be provided with several resources: leased cloud VPS, botnet nodes, or compromised machines.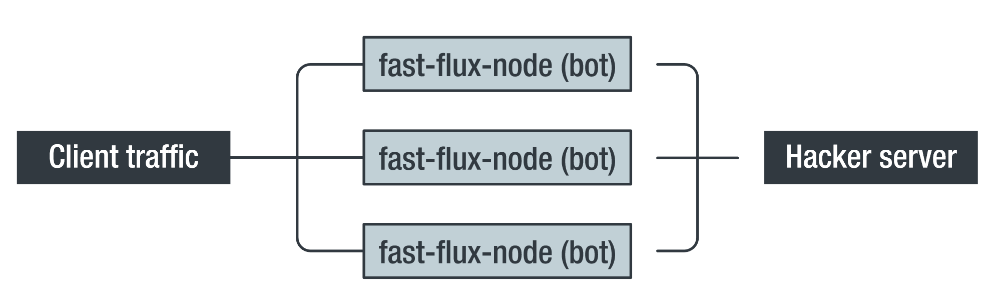
How fast-flux works as an intermediate-level service. Source (hereafter, unless otherwise stated): Trend Micro
The essence of the fast-flux method is to use short TTLS (time-to-live) for a-records in DNS. This prevents caching of the domain name on intermediate DNS servers and forces them to always request permission from declared domain name system (DNS) servers. Low TTL values allow attackers with high frequency to direct the domain to IP addresses in the dedicated pool and ensure the availability of the service, even if some of the addresses are compromised or banned by the provider.
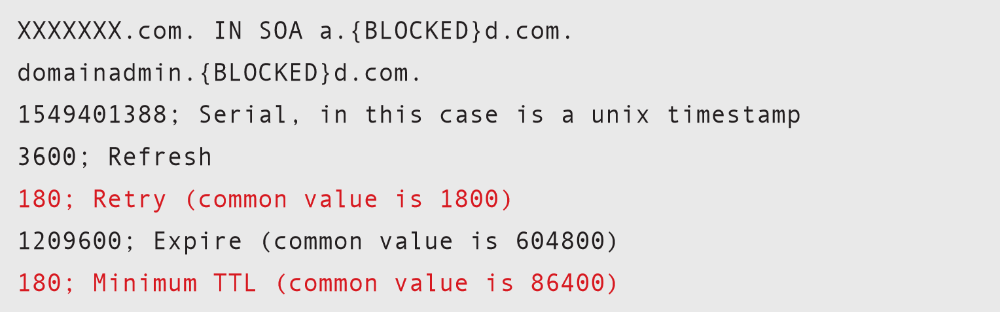
Fast-flux specific DNS records
The TTL values shown in red are set with an unusually low number of retries and a minimum TTL time (in seconds). Under normal circumstances, this will create additional load on the DNS server, but in the case of fast-flux, the goal is to suppress the caching mechanism so that the client is given an up-to-date IP address that is currently provided by the fast-flux infrastructure.
Fast-flux services are usually more expensive than bulletproof hosting, since their operator has to maintain a pool of IP addresses to provide a "fast-flux" infrastructure, and this requires additional costs.
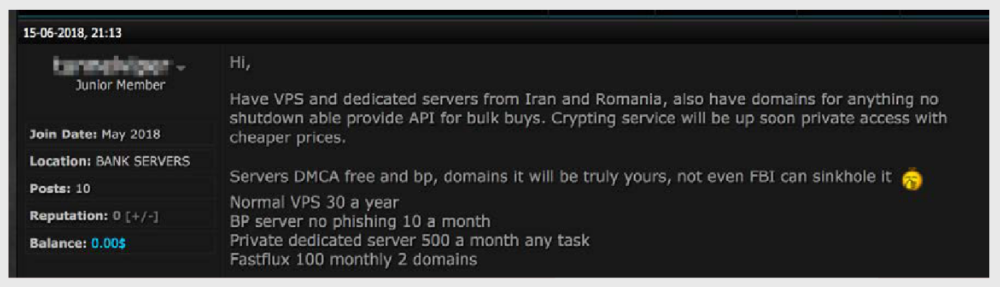
The cost of fast-flux services is $ 100 for two domains per month, while the monthly cost of renting a bulletproof server is $ 10
Protection against DDoS attacks
Cybercrime groups compete with each other no less than legal organizations, and as a means of competition, they arrange attacks on denial of service to competitors ' resources using Layer4 and Layer7 methods. That is why many bulletproof services offer hosting with protection against DDoS attacks or a DDoS protection service that you can use for your resource.As a rule, such services are provided by placing a specialized resource like a WAF (Web Application Firewall) in front of the protected server.
VDS from compromised hosts
Compromised servers are often used for hosting during one or more stages of their criminal monetization lifecycle.To capture control, use:
- vulnerabilities in server SOFTWARE,
- bruteforce-атаки,
- stolen API keys,
- the theft of account through the connected servers,
- phishing and fraudulent campaigns.
Credentials for accessing the captured servers are subsequently sold on underground online stores:
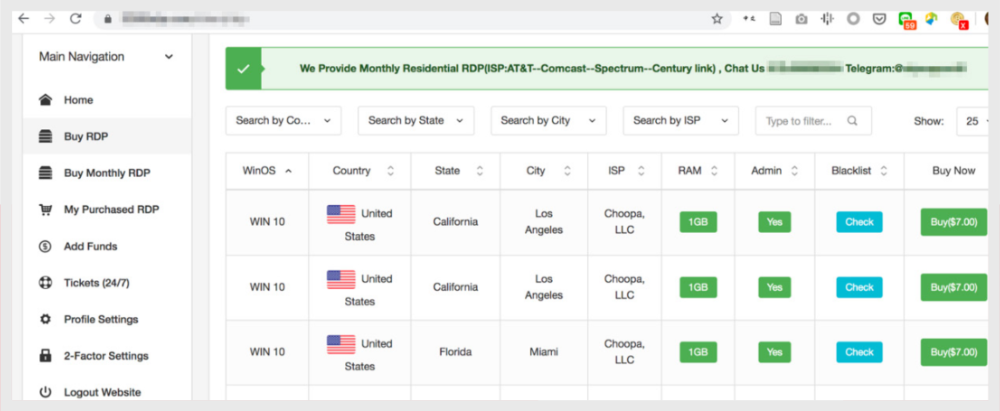
Online store of accounts for accessing compromised RDP servers
Taking over more secure servers may require zero-day vulnerabilities, which are also offered at cyberforums.
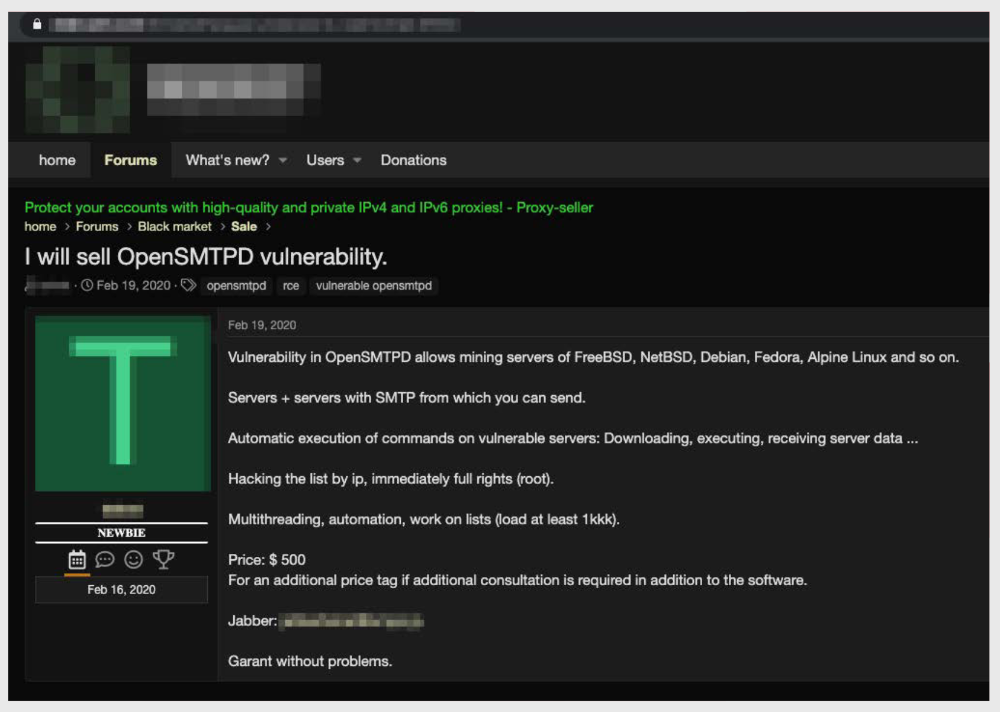
Announcement of the sale of a vulnerability in OpenSMTPD that allows you to compromise servers running on FreeBSD, NetBSD, Debian, Fedora and Alpine Linux and use them for hosting
Compromising cloud hosting services
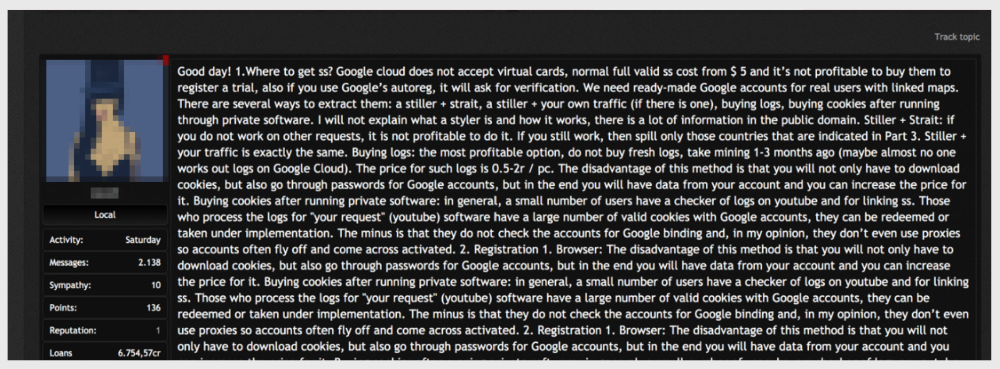
From the attacker's point of view, Google Cloud and Microsoft Azure are extremely affordable resources, since both allow users with a Bank card connected to their account to try out services for free. This led to the fact that attackers actively collect data from Google accounts with connected Bank cards, and then use them to run instances of dedicated servers. Detailed tutorials are published for novice hackers: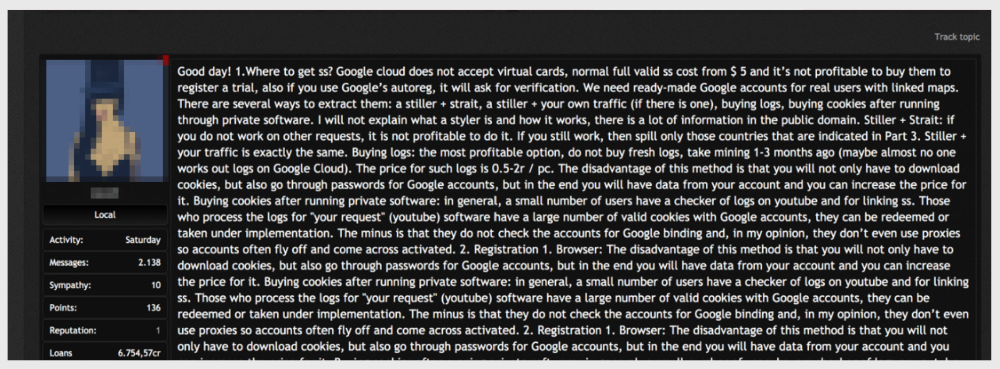
For those who don't want to bother hacking their accounts, there are stores that offer already hacked Microsoft Azure and Google Cloud accounts.

Socks, Proxy, and SSH tunnels
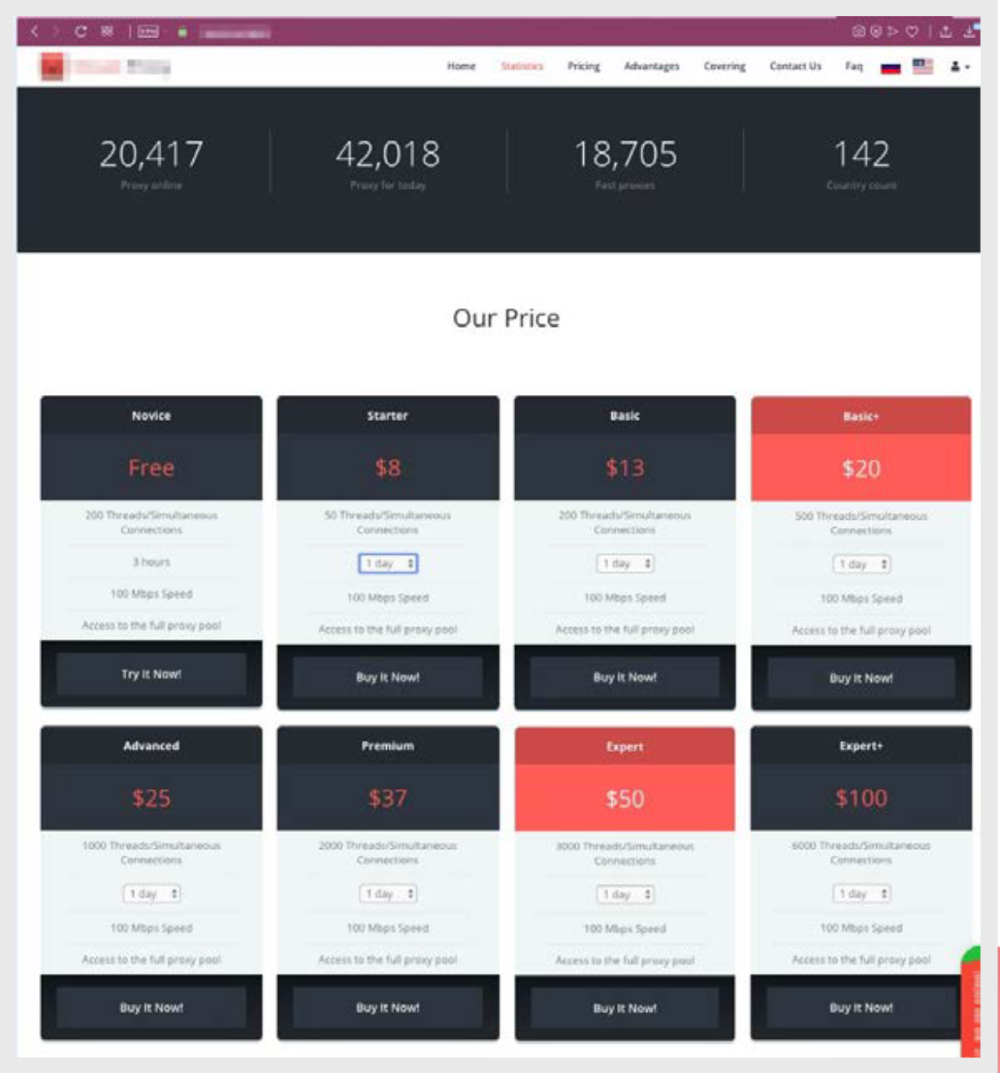
SOCKS and proxy services allow attackers to hide without attracting too much attention or causing detection by network security monitoring tools.Due to the demand for this tool, it is relatively easy to find resources that offer to purchase SOCKS proxy, and you can pay for the purchase with cryptocurrency.
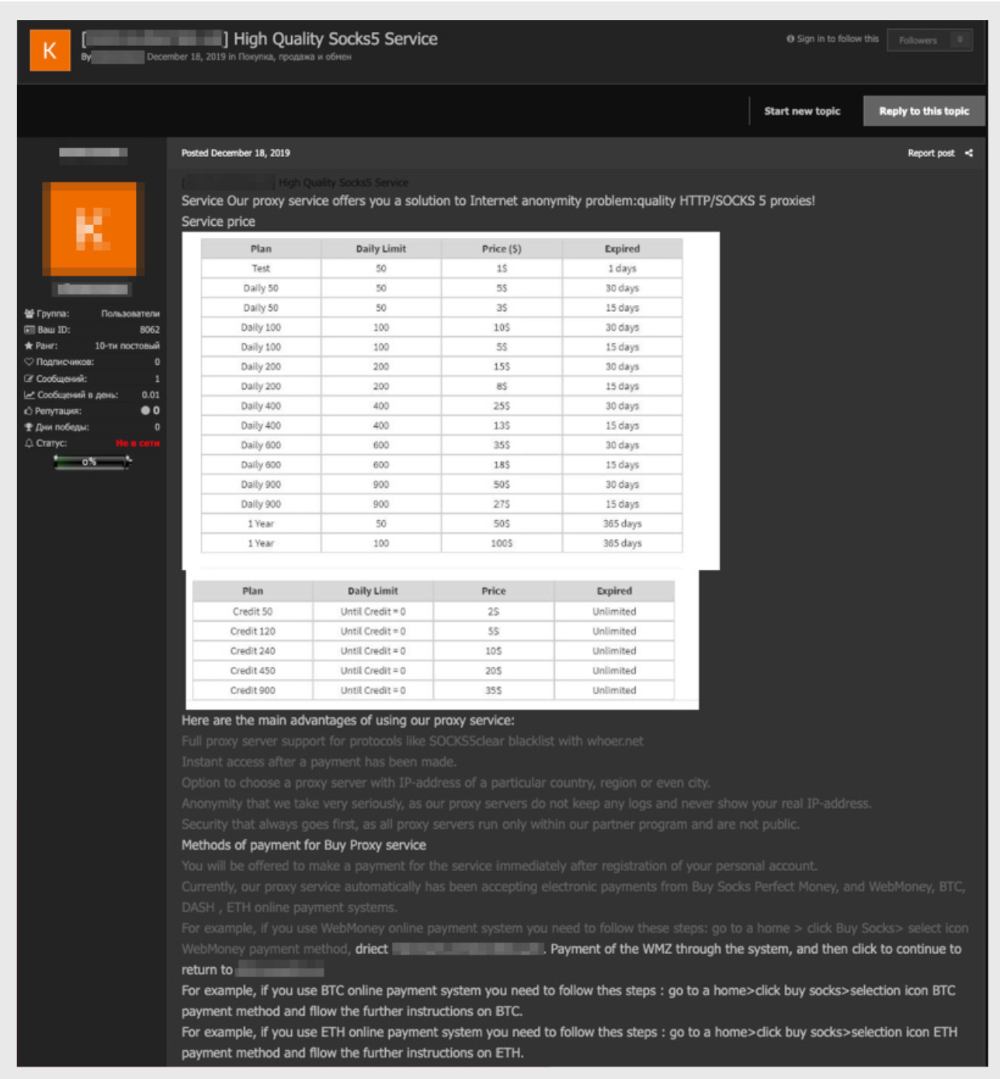
Price list for socks proxies that can be paid for using Bitcoin and Ethereum
Another way to hide communication is by tunneling into legitimate protocols, such as SSH:

Price list for SSH tunnels
The price of SSH tunnels depends on the country of their location. Location is very important for some illegal activities. For example, banks ' anti-fraud systems correlate information about the cardholder with the geolocation of the IP address at which it was attempted to be used. Therefore, criminals are willing to pay more to buy a tunnel that corresponds not only to the desired country, but also to the city.
Anonymizing VPNs
Another popular service in the cybercriminal environment is anonymous VPNs, and in this part the preferences of groups are divided: some prefer to use legal commercial VPNs like NordVPN or ProtonVPN, others rent similar services on the underground market, and others independently create an infrastructure based on OpenVPN, WireGuard or SoftEther.One of the signs that indirectly indicates that compromised hosts are used to provide VPN services is the indication of the" availability guarantee period " of the service. The lower the numbers, the more suspicious these services are. It is unlikely that a legitimate VPN provider will write in the conditions that "in case the provided credentials do not work for the next 24 (48 or 72) hours, new credentials will be provided free of charge." But this is exactly what is usually present in the offers of illegal services.
Ad for the sale of short-lived VPNs
Another suspicious sign of a possible criminal nature of anonymization of services is the term of the agreement. Legal VPN providers provide services for at least a month, while in the criminal environment there are offers of VPN services for a period of no more than one day. It is difficult to imagine cases of legitimate use for which such a small amount of time is sufficient. However, for a criminal, this is quite enough to
- check the validity of compromised Bank cards,
- verify the validity of compromised accounts,
- register accounts on cloud platforms or on a content hosting platform,
- make a fraudulent newsletter in social networks,
- launch a malicious ad campaign.
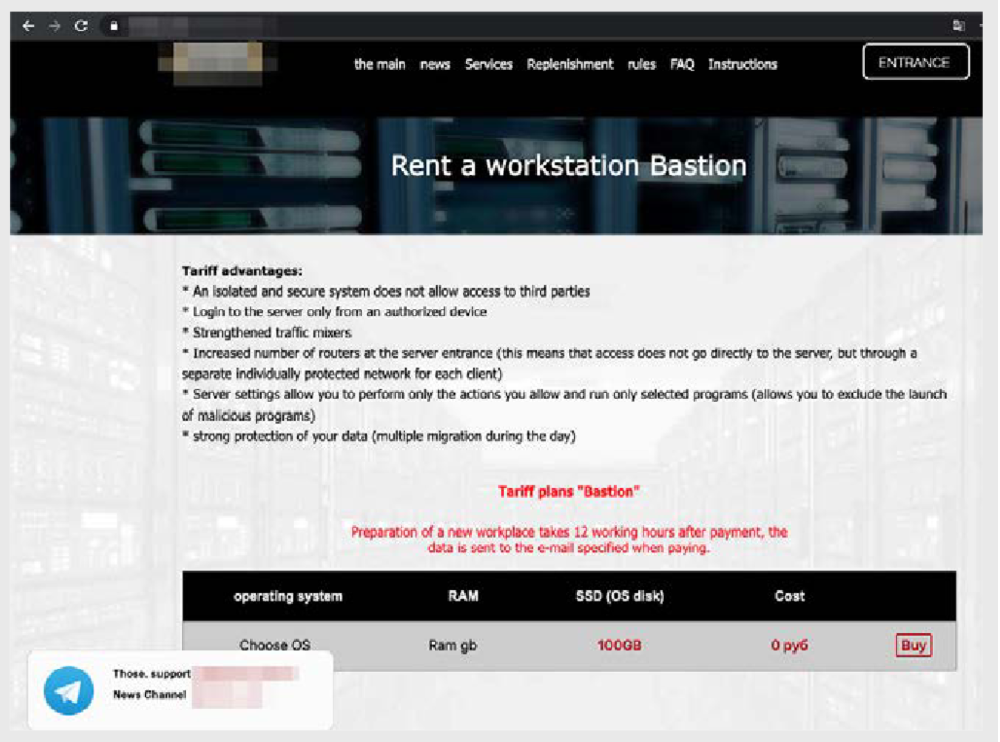
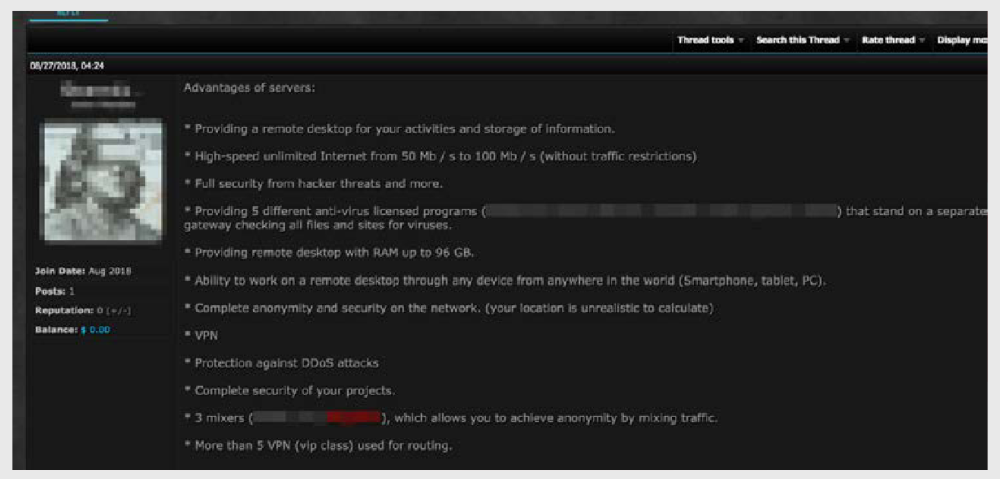
Mobile jobs
Some vendors offer those who want to use "bulletproof" mobile workplaces, which can not be accessed by outsiders.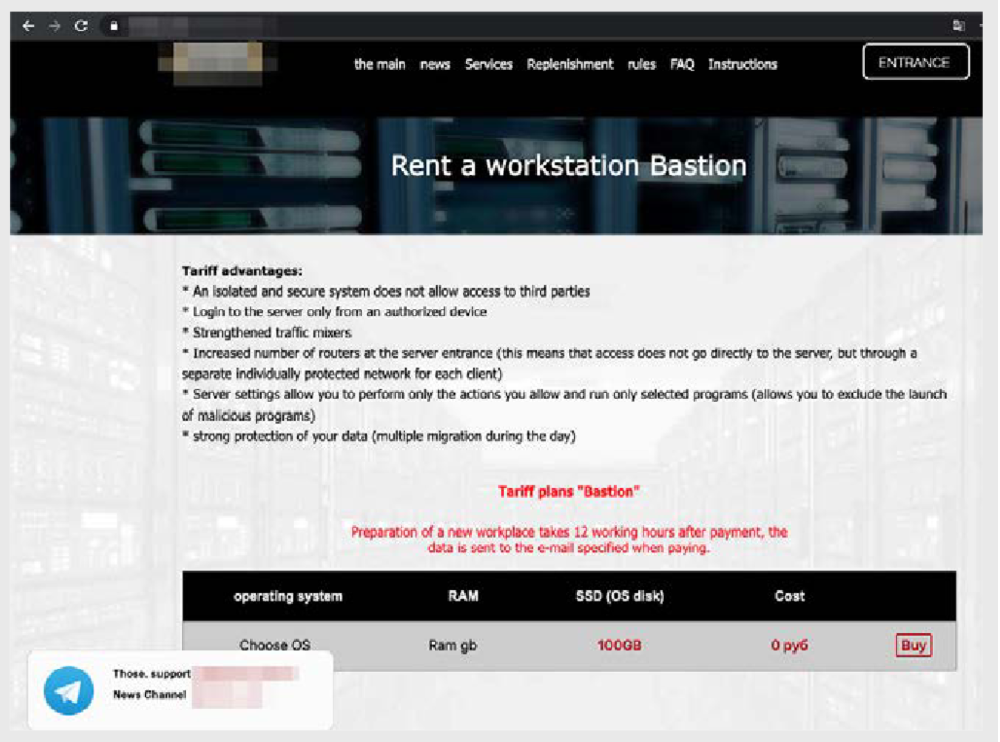
Although the policy of this site formally prohibits the distribution of malware, we found ads on the forum hinting that other malicious actions are acceptable.:
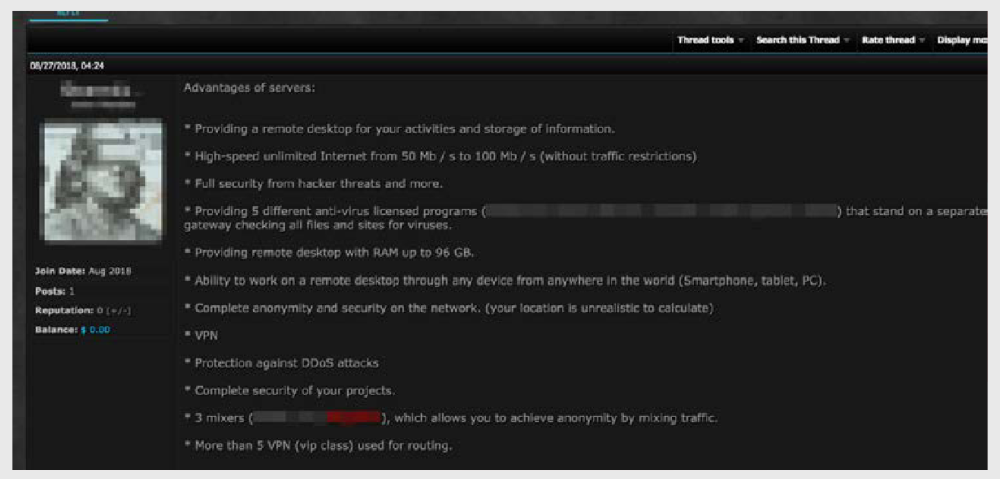
The proposal mentions complete anonymity, the inability to determine the user's location, a high-speed Internet connection, DDoS protection, an outgoing traffic mixer, and five different VPNs. Despite the fact that direct port scanning, brute-forcing, and malware distribution are not allowed, an attacker can also commit other criminal acts using such workstations.
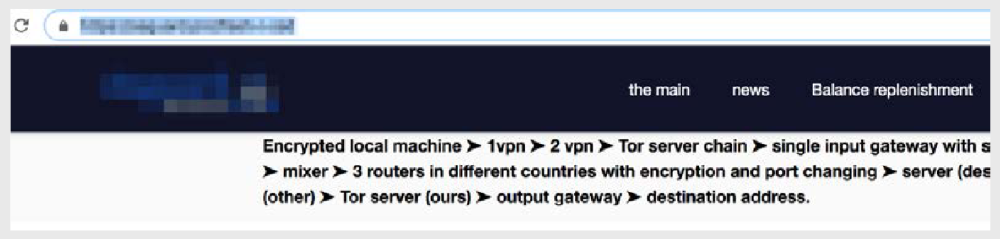
Anonymizing traffic mixers
Tor is not the only way to hide from the watchful eye of law enforcement and competitors. Services that offer "impenetrable" jobs have developed their own traffic mixers using a geographically distributed network of routers. This traffic is mixed with the traffic of anonymous VPS that periodically move between data centers located in different countries, which makes it even more difficult to trace such systems.Custom services are also available for combining VPN connections, Tor, and geographically distributed router sets. These combinations allow you to create such a complex chain of hosts and redirectors that it is almost impossible to track them.
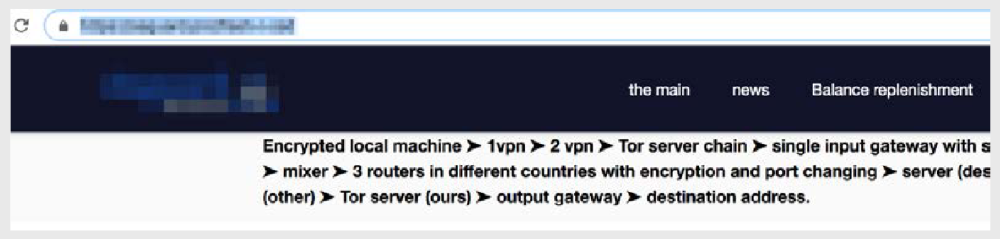
Traffic obfuscation chain suggestion
For example, one of the services offers to use the following chain::
Host → VPN1 → VPN2 → TOR → Bouncing traffic gateway → traffic mixer → geographically distributed routers for Bouncing traffic → remote desktop (RDP) for operation → connection via other geographically distributed routers → Tor servers → exit node → destination point.

