Man
Professional
- Messages
- 3,222
- Reaction score
- 1,231
- Points
- 113
How attackers use far-fetched pretexts to compromise systems.
In the new ClickFix campaigns, scammers lure users to fake Google Meet pages, where they are shown fake connection errors to spread malware capable of infecting Windows and macOS systems.
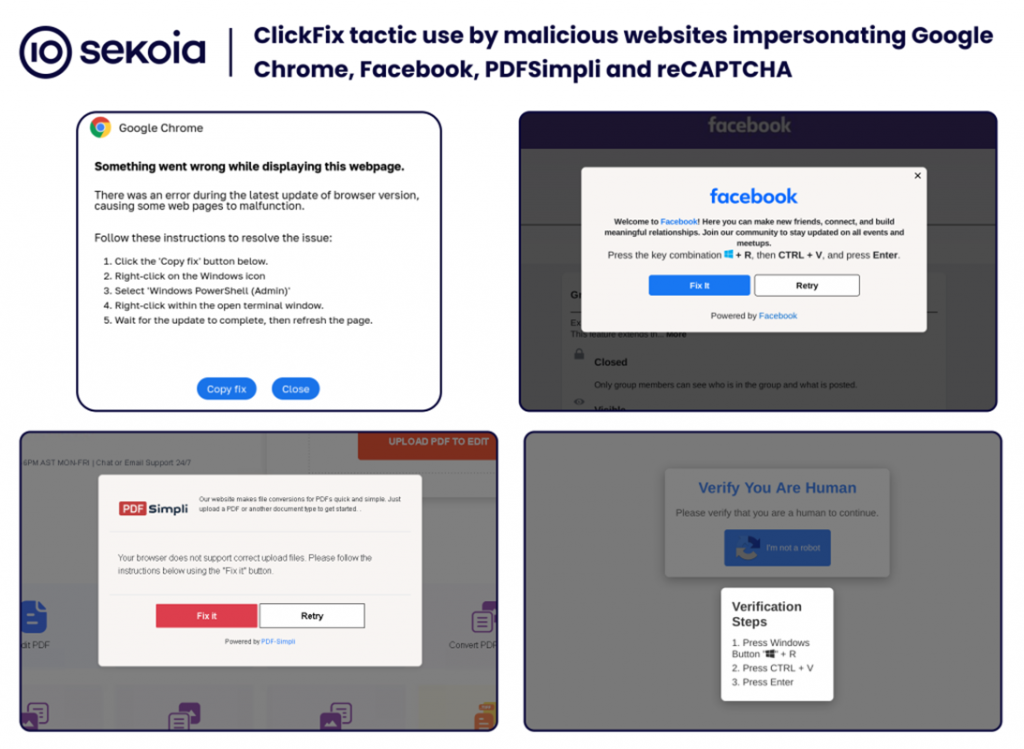
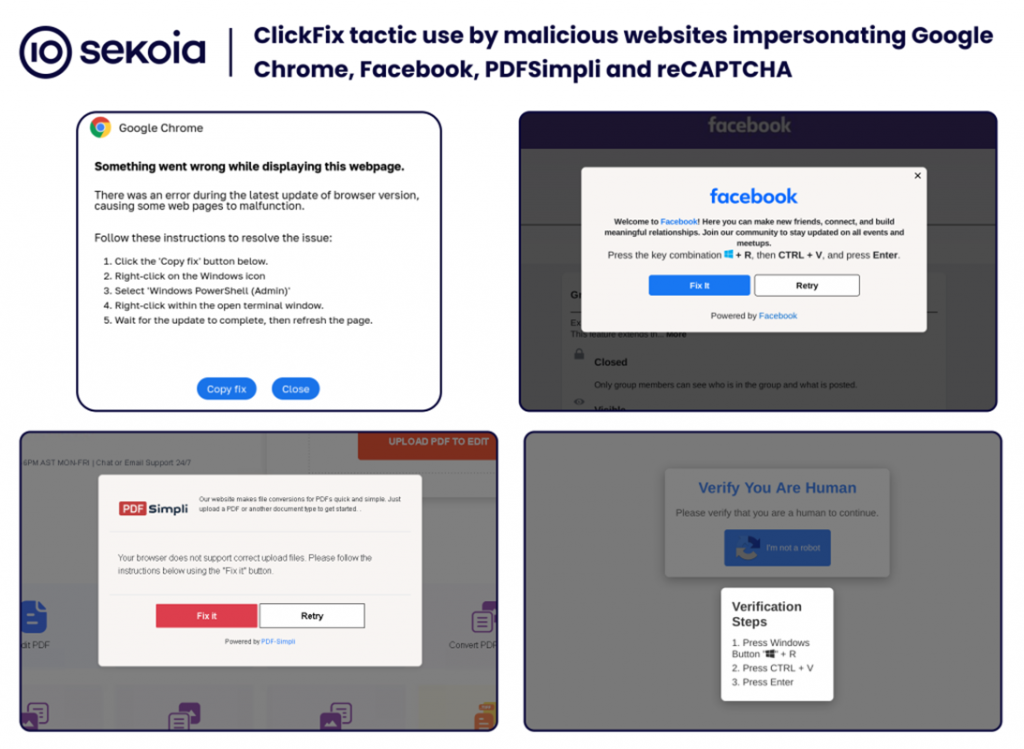
ClickFix came into existence in May when Proofpoint first reported its use by the TA571 group. Fake error messages in Google Chrome, Microsoft Word, and OneDrive were used for the attacks. Victims were prompted to insert code into the PowerShell command prompt to fix the alleged problem, which led to the infection of their devices.
Malware such as DarkGate, Matanbuchus, NetSupport, Amadey Loader, XMRig, Lumma Stealer, and others were distributed through this method. In July, McAfee recorded an increase in the frequency of these attacks, especially in the United States and Japan.
According to a new report from Sekoia, ClickFix's tactics have recently changed, with attackers now using fake Google Meet invitations and sending phishing emails targeting transportation and logistics companies. Among the new tricks are fake Facebook pages and fake discussions on GitHub.
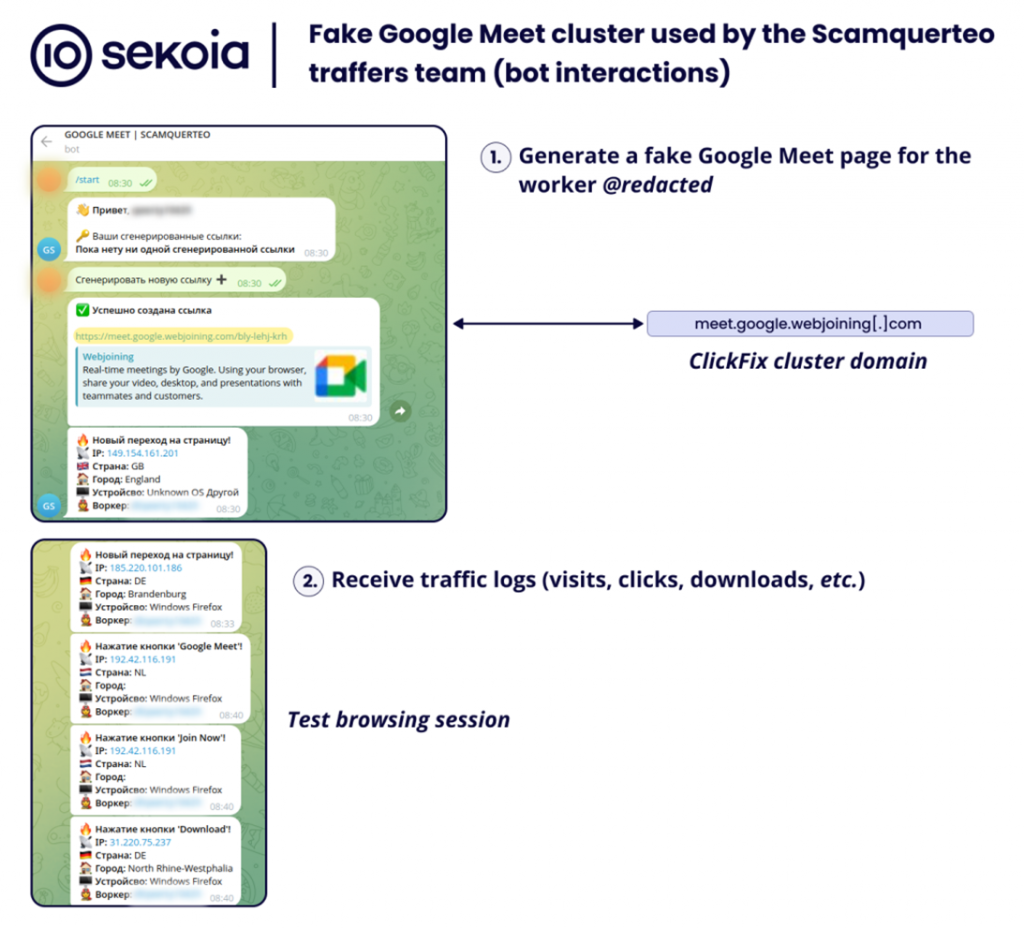
Sekoia also links the recent campaigns to two groups – Slavic Nation Empire (SNE) and Scamquerteo, which are allegedly part of the cryptocurrency scam groups Marko Polo and CryptoLove.
Attacks via Google Meet look especially convincing: attackers send emails with fake links that imitate official ones:
After going to such pages, users are shown a message about an alleged problem with the microphone or headphones. An attempt to "fix" the error activates the standard ClickFix script: malicious PowerShell code is executed via the command line, downloading malware from the domain "googiedrivers[.]com».
For Windows devices, Stealc or Rhadamanthys are downloaded, and on macOS, the AMOS Stealer is installed in the ".DMG" under the name "Launcher_v194". In addition to Google Meet, attackers use other platforms to spread malware, including Zoom, fake PDF readers, fake video games, and web3 projects.
Source
In the new ClickFix campaigns, scammers lure users to fake Google Meet pages, where they are shown fake connection errors to spread malware capable of infecting Windows and macOS systems.
ClickFix came into existence in May when Proofpoint first reported its use by the TA571 group. Fake error messages in Google Chrome, Microsoft Word, and OneDrive were used for the attacks. Victims were prompted to insert code into the PowerShell command prompt to fix the alleged problem, which led to the infection of their devices.
Malware such as DarkGate, Matanbuchus, NetSupport, Amadey Loader, XMRig, Lumma Stealer, and others were distributed through this method. In July, McAfee recorded an increase in the frequency of these attacks, especially in the United States and Japan.
According to a new report from Sekoia, ClickFix's tactics have recently changed, with attackers now using fake Google Meet invitations and sending phishing emails targeting transportation and logistics companies. Among the new tricks are fake Facebook pages and fake discussions on GitHub.
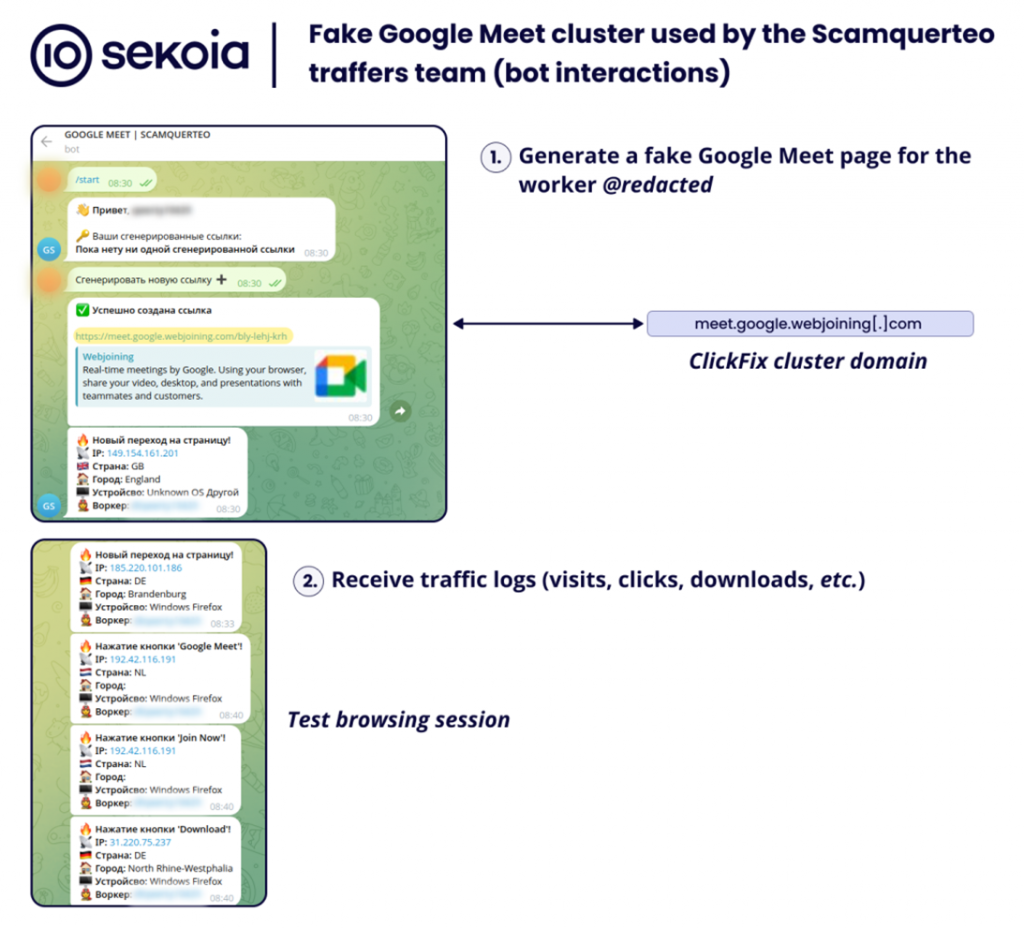
Sekoia also links the recent campaigns to two groups – Slavic Nation Empire (SNE) and Scamquerteo, which are allegedly part of the cryptocurrency scam groups Marko Polo and CryptoLove.
Attacks via Google Meet look especially convincing: attackers send emails with fake links that imitate official ones:
- meet[.]google[.]us-join[.]com
- meet[.]google[.]web-join[.]com
- meet[.]googie[.]com-join[.]us
After going to such pages, users are shown a message about an alleged problem with the microphone or headphones. An attempt to "fix" the error activates the standard ClickFix script: malicious PowerShell code is executed via the command line, downloading malware from the domain "googiedrivers[.]com».
For Windows devices, Stealc or Rhadamanthys are downloaded, and on macOS, the AMOS Stealer is installed in the ".DMG" under the name "Launcher_v194". In addition to Google Meet, attackers use other platforms to spread malware, including Zoom, fake PDF readers, fake video games, and web3 projects.
Source
