Lord777
Professional
- Messages
- 2,576
- Reaction score
- 1,564
- Points
- 113
Experts from ReasonLabs have discovered an unusual malicious scheme that has been working since 2019. According to researchers, hackers used it to steal millions of dollars from tens of thousands of victims. It turned out that the attackers operate a large network consisting of more than 200 fake dating and customer support sites, and use these resources to debit funds from other people's bank cards purchased on the darknet.

This campaign uses two types of domains: dating sites and customer support portals (the address lists can be found in the company's report). If you try to visit the websites of companies that supposedly own these fake resources, you may find that they do not exist at all, or they use non-existent email addresses, such as mail@example.com.
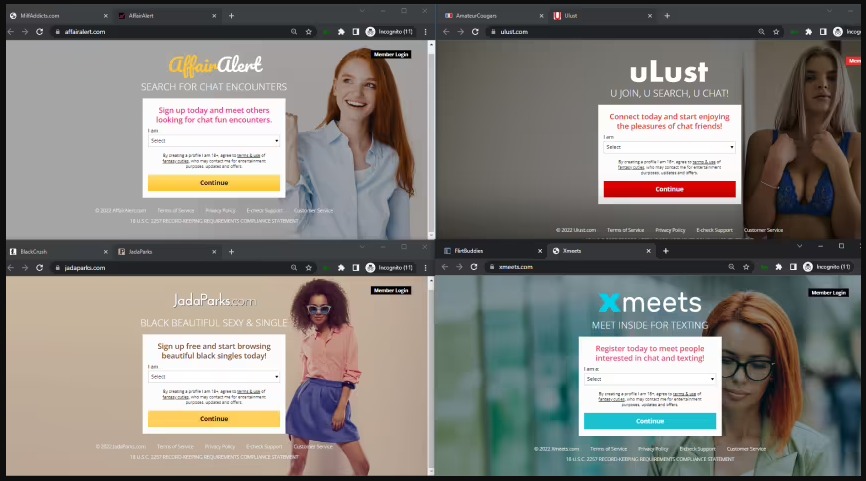
Fake dating sites
At the same time, the dating and customer support sites themselves seem to be working, but they receive almost no traffic, occupying low positions in Google search results. The fact is that they do not exist to attract users, but to serve as channels for money laundering.

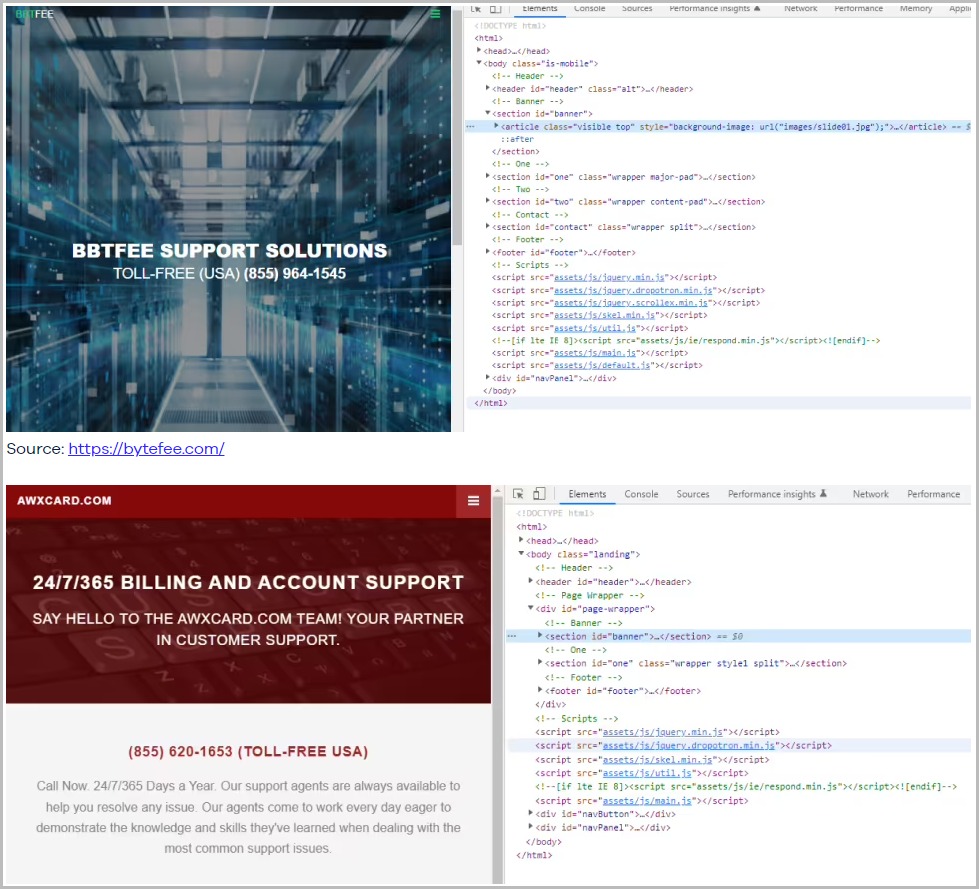
ReasonLabs analysts write that all sites have the same HTML structure and almost the same content, so it looks like they were created using automated tools. At the same time, fake customer support portals often use the names of non-existent organizations, or try to resemble real brands, such as McAfee, ReasonLabs, and other companies.
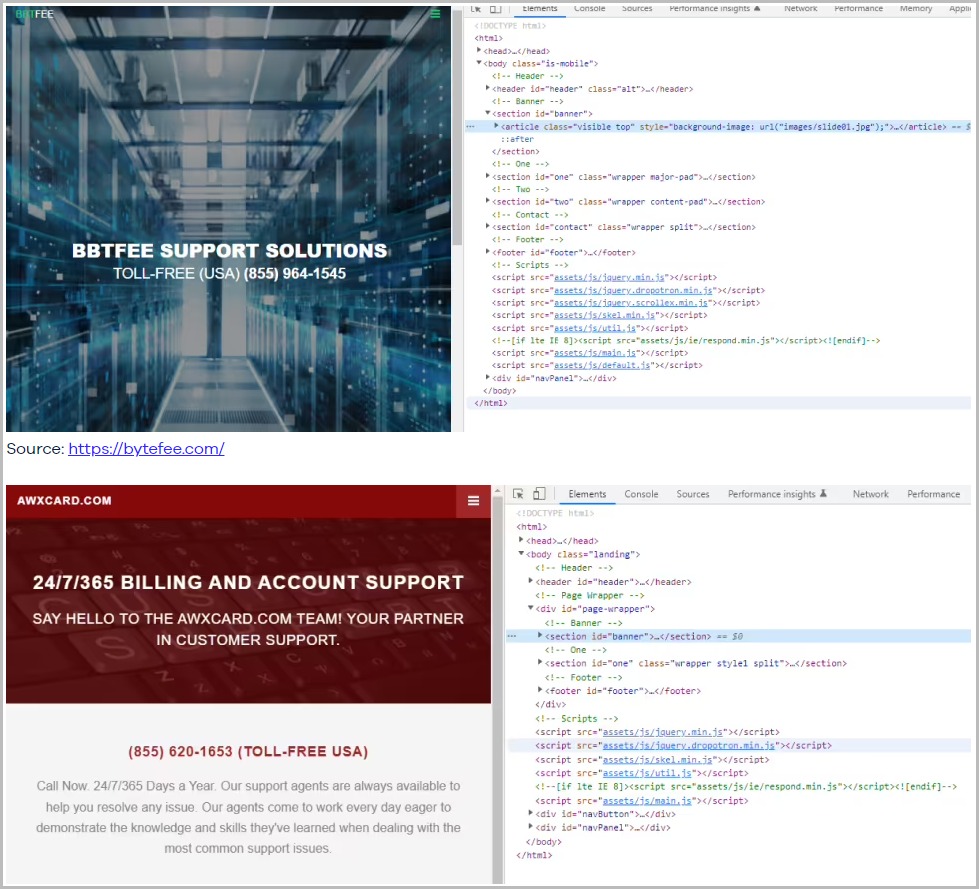
It is also noted that the operators of this campaign seem to have put a lot of effort into hiding all 75 fake support portals from indexing by search engines, using instructions to protect against crawlers in Robots.txt.
But the biggest challenge for attackers is to register these sites with payment operators, who usually classify them as "high-risk" (even if we are talking about a legitimate resource) due to the high percentage of chargebacks. To avoid being blacklisted, each site submits an application individually, as campaign operators are afraid of losing all their resources at once if fraud is detected.
If resources need to prove their legitimacy, then all sites have a 24-hour chat with support and a working phone number that is outsourced to a real call center. In addition, all sites provide a toll-free number in case users want to cancel a payment, which scammers usually do not offer.
As soon as the payment provider approves the request, hackers use millions of stolen payment cards purchased on the darknet and charge money from them through their fake sites. Most of the cards belong to residents of the United States, but it is also reported that hackers bought cards from French-speaking countries.
Withdrawals are made either via the API or manually. At the same time, site operators are very careful and try not to attract attention to themselves. They withdraw small amounts, use common names that can get lost among other expenses of the victim, use repeated payments with the same amount, and avoid test transactions.
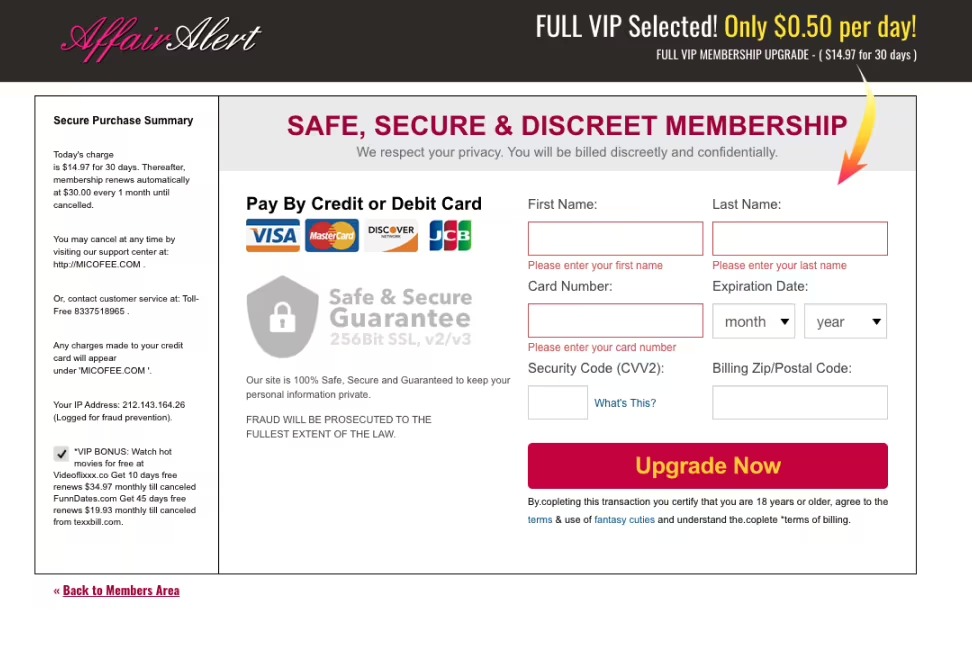
Payment page on one of the scam sites
Moreover, in some cases, hackers even return money to victims, which makes their operations more authentic, and the charge-back coefficient seems low.
Although many of the 275 fake websites are still operating, ReasonLabs experts have already notified payment system representatives and law enforcement agencies about their findings.
(c) https://xakep.ru/2022/09/23/fake-carding-sites/

This campaign uses two types of domains: dating sites and customer support portals (the address lists can be found in the company's report). If you try to visit the websites of companies that supposedly own these fake resources, you may find that they do not exist at all, or they use non-existent email addresses, such as mail@example.com.
Fake dating sites
At the same time, the dating and customer support sites themselves seem to be working, but they receive almost no traffic, occupying low positions in Google search results. The fact is that they do not exist to attract users, but to serve as channels for money laundering.

ReasonLabs analysts write that all sites have the same HTML structure and almost the same content, so it looks like they were created using automated tools. At the same time, fake customer support portals often use the names of non-existent organizations, or try to resemble real brands, such as McAfee, ReasonLabs, and other companies.
It is also noted that the operators of this campaign seem to have put a lot of effort into hiding all 75 fake support portals from indexing by search engines, using instructions to protect against crawlers in Robots.txt.
But the biggest challenge for attackers is to register these sites with payment operators, who usually classify them as "high-risk" (even if we are talking about a legitimate resource) due to the high percentage of chargebacks. To avoid being blacklisted, each site submits an application individually, as campaign operators are afraid of losing all their resources at once if fraud is detected.
If resources need to prove their legitimacy, then all sites have a 24-hour chat with support and a working phone number that is outsourced to a real call center. In addition, all sites provide a toll-free number in case users want to cancel a payment, which scammers usually do not offer.
As soon as the payment provider approves the request, hackers use millions of stolen payment cards purchased on the darknet and charge money from them through their fake sites. Most of the cards belong to residents of the United States, but it is also reported that hackers bought cards from French-speaking countries.
Withdrawals are made either via the API or manually. At the same time, site operators are very careful and try not to attract attention to themselves. They withdraw small amounts, use common names that can get lost among other expenses of the victim, use repeated payments with the same amount, and avoid test transactions.
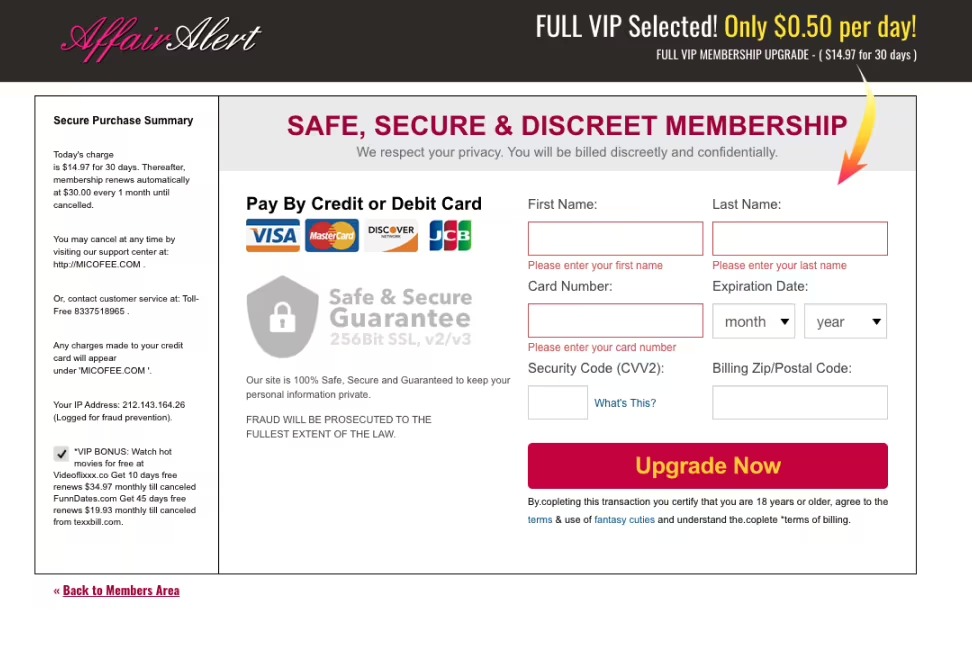
Payment page on one of the scam sites
Moreover, in some cases, hackers even return money to victims, which makes their operations more authentic, and the charge-back coefficient seems low.
Although many of the 275 fake websites are still operating, ReasonLabs experts have already notified payment system representatives and law enforcement agencies about their findings.
"We reported this scam to more than a dozen parties who were involved in one way or another. These include Visa and Mastercard, as well as many other services, including AWS, GoDaddy, and various registrars. We also notified you about fraud Fraud.org This is a project of the non — profit human rights organization "National League of Consumers", which shares consumer complaints with a network of more than 200 partners in law enforcement agencies.
(c) https://xakep.ru/2022/09/23/fake-carding-sites/
