Brother
Professional
- Messages
- 2,590
- Reaction score
- 541
- Points
- 113
28 fake ad agencies were used to distribute malicious ads

Malicious ads, through which attackers redirect users to various malicious and fraudulent sites, have long been a big problem, but in the past year this mechanism of delivering malware and luring victims to fake tech support sites has been used especially frequently. Part of the blame, it turns out, lies with the malicious Zirconium campaign, which acquired over 1,000,000 placements of dangerous ads.
Confiant specialists spoke about the large-scale operation Zirconium, which began in February 2017. According to the researchers, the attackers created a network of 28 fake ad agencies and gradually managed to establish relationships with the largest ad platforms, earning a good reputation. The criminals even bothered to create a website for every non-existent company, invented fake executives and developers, creating fake identities for them on social networks, including profiles on LinkedIn and Twitter.
Fake CEO profile of a fake company
As the phony firms were in full swing, the Zirconium campaign operators began to use them to buy space for malicious advertisements on mainstream popular sites. The attackers used a technique called forced redirects (also known as tab-under), by which the victim was first redirected to an intermediate domain, which examined and sorted the incoming traffic, and then sent the user to the next domain, also owned by the Zirconium operators. ... Where the victim went later depended on who exactly the attackers sold the traffic to. The chain of redirects could lead to the site of a fake antivirus or technical support, to a page offering to install malware under the guise of an update for Flash Player, and so on.
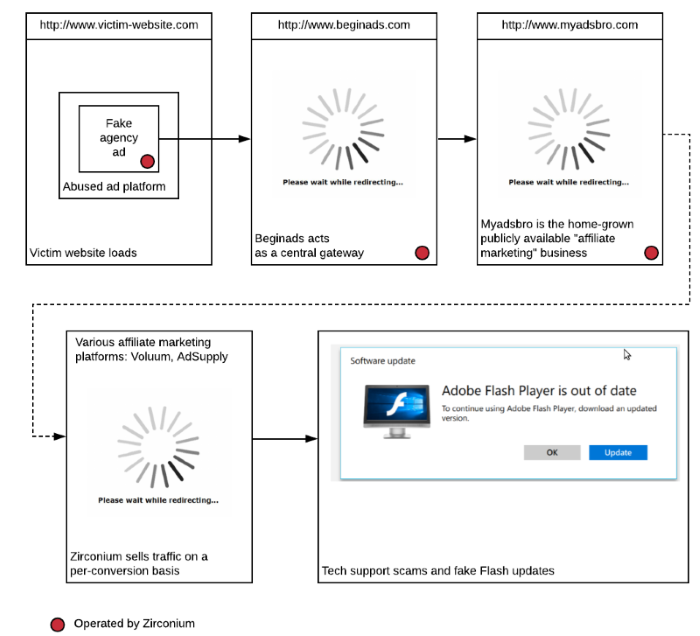
How Zirconium works
At the peak of Operation Zirconium, the group's purchases of advertising reached 62% of sites that monetize through advertising each week, according to Confiant researchers. According to experts, a total of about 2.5 million users were affected at the hands of cybercriminals, and 95% of the victims were in the United States. Some examples of the pages that the affected users came to can be seen below.

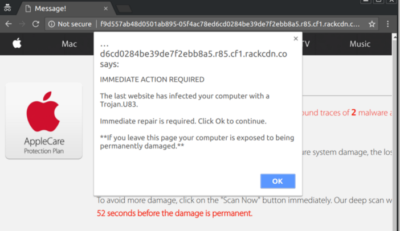

Interestingly, the Zirconium operators completely ignored mobile traffic - the attackers were only interested in desktop browsers, and the criminals also did not take into account the operating system, making no distinction between users of Windows, Linux or macOS.
Of the 28 ad agencies created by the attackers, only 20 were involved in the Zirconium operation, but Confiant researchers have published a full list of fake firms, including the dormant ones. At the same time, experts refused to name 16 advertising platforms with which the criminals collaborated.

In conclusion, Confiant analysts point out one interesting fact. The fact is that the Zirconium malicious campaign was hardly used to redirect traffic to various sets of exploits, as was usually the case in the past. According to experts, this is due to the fact that almost all modern browsers have abandoned the use of Flash by default and have become much better protected, which is why the classic scheme for delivering explolot kits has lost its effectiveness. It is worth noting here that browser developers are really trying by all means to prevent cybercriminals, for example, Chrome 64 released this week protects users from the "forced redirects" that Zirconium exploited.
xakep.ru
