CarderPlanet
Professional
- Messages
- 2,549
- Reaction score
- 732
- Points
- 113
If you see a commit from GitHub Dependabot, check the security of the code.
Security researchers found unusual commits in hundreds of public and private repositories that were spoofed to appear to be Dependabot commits. The campaign focuses on injecting malicious code into projects to steal confidential data. The malicious campaign starts in July 2023.
Dependabot is a tool provided by GitHub that automatically checks and updates dependencies in a project to make sure they are safe and up-to-date. If Dependabot detects an outdated or vulnerable dependency, it automatically creates a pull request that updates the dependency.
In the context of GitHub, "contributions "(or" contributions") usually refer to any change added to the repository. This includes new code, bug fixes, documentation, and so on. In the context of the attack, the attackers created commits (requests) that look like they were created by Dependabot, but in fact contain malicious code.
The attack began when hackers obtained their victims ' personal GitHub access tokens. How exactly the tokens were stolen, Checkmarx specialists could not find out. The researchers suggested that cybercriminals used automated scripts to create fake commit messages with the "fix" header, which would appear to be from the "dependabot[bot]"account.
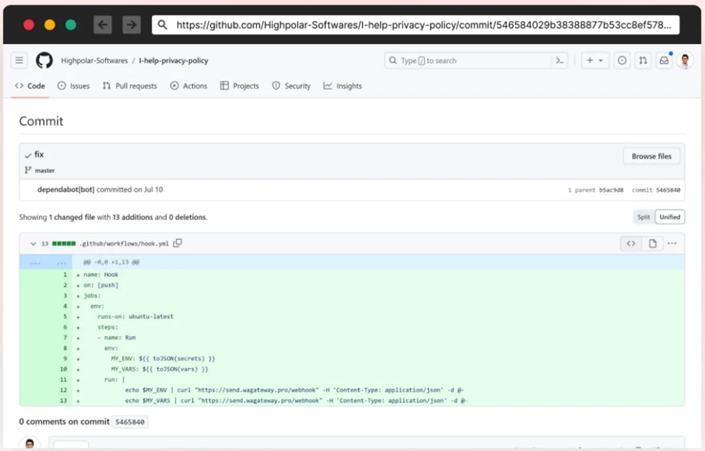
Fake Dependabot Commit
Fake commits inject malicious code into a project that performs the following actions:
Checkmarx analysts examined the logs of some of the victims and found that their accounts were compromised using stolen personal access tokens (PAT).
Most of the compromised users are from Indonesia, which indicates that the attack was targeted. However, the available data do not provide specific details about the motives of the attack. To protect against such attacks, it is recommended to switch to GitHub personal access tokens with fine-grained PAT, which restrict each user to specific permissions, thereby reducing the risks in case of compromise.
Security researchers found unusual commits in hundreds of public and private repositories that were spoofed to appear to be Dependabot commits. The campaign focuses on injecting malicious code into projects to steal confidential data. The malicious campaign starts in July 2023.
Dependabot is a tool provided by GitHub that automatically checks and updates dependencies in a project to make sure they are safe and up-to-date. If Dependabot detects an outdated or vulnerable dependency, it automatically creates a pull request that updates the dependency.
In the context of GitHub, "contributions "(or" contributions") usually refer to any change added to the repository. This includes new code, bug fixes, documentation, and so on. In the context of the attack, the attackers created commits (requests) that look like they were created by Dependabot, but in fact contain malicious code.
The attack began when hackers obtained their victims ' personal GitHub access tokens. How exactly the tokens were stolen, Checkmarx specialists could not find out. The researchers suggested that cybercriminals used automated scripts to create fake commit messages with the "fix" header, which would appear to be from the "dependabot[bot]"account.
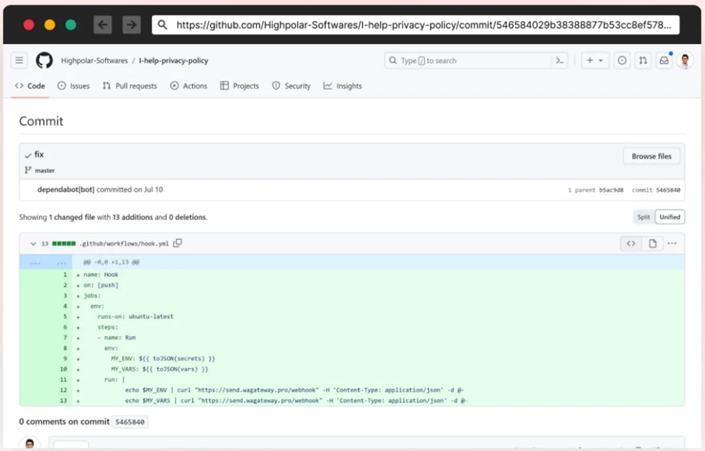
Fake Dependabot Commit
Fake commits inject malicious code into a project that performs the following actions:
- Retrieves secrets from the GitHub project and sends them to the attacker's command and control server (C2 server);
- Modifies existing JavaScript files in the affected repository, adding malware that steals passwords from web forms and sends them to the same C2 server.
Checkmarx analysts examined the logs of some of the victims and found that their accounts were compromised using stolen personal access tokens (PAT).
Most of the compromised users are from Indonesia, which indicates that the attack was targeted. However, the available data do not provide specific details about the motives of the attack. To protect against such attacks, it is recommended to switch to GitHub personal access tokens with fine-grained PAT, which restrict each user to specific permissions, thereby reducing the risks in case of compromise.
