Man
Professional
- Messages
- 3,222
- Reaction score
- 1,228
- Points
- 113
When preventing intruders, one of the most important measures to enhance security is multi-factor authentication systems. Among the most effective approaches is the one-time password (OTP) method. However, there is still debate about how much its advantages outweigh the disadvantages. We present an overview of the global and Russian markets for authentication systems using one-time passwords.
As you know, there are many authentication methods. One of the most common options today is the OTP (One-Time Password) method, which will be discussed in this review.
To enhance security measures, a hybrid approach is increasingly being used, which involves the use of several authentication factors. OTP can be one of them.
To calculate the password, two parameters are accepted - a secret key (the initial value for the generator) and the current time value (or internal counter). The secret key is stored both in the device itself and on the authentication server. The means for generating one-time passwords can be divided into two groups: either the user has physical tools for such generation, such as hardware devices with a screen, keys, mobile applications, etc., or passwords come through a certain channel - in the form of an SMS message, push notification, etc.
Two-factor authentication is popular in many large organizations. This is due to the increase in the volume of online transactions due to the transition of customers to digital banking, the rapid growth of e-commerce, the use of online banking for the purchase of food and other goods. The spread of strong authentication is also facilitated by the launch of real-time payment systems and the introduction of POS systems at retail outlets for the convenience of users.
OTP, as one of the factors, is widely used in the banking sector, in e-commerce applications. Many of us encounter this technology almost daily, for example, when trying to transfer money from a card (a one-time password comes in an SMS message or as a push notification when trying to complete a transaction).
Among the OTP solutions, there are both commercial and completely free ones. Many providers provide free access to OTP applications with certain restrictions (for example, by the number of users), and if there is a need, it will be possible to purchase a version with advanced features. Thus, OTP protection technology has become available to anyone who wants to strengthen the protection of their data.
The One-Time Password method remains one of the most common in the two-factor authentication market today. By 2018, this sector was valued at $1.5 billion out of the total two-factor authentication market of $3.5 billion. According to Market Research, it will reach $3.2 billion (out of $8.9 billion) by 2024.
The global OTP token market is segmented by type, technology, and industry. Thus, devices can be divided into two main groups - physical (hard tokens) and software (soft tokens). Depending on the type of physical device, there are segments of SIM tokens, USB tokens, mini tokens. By technology type, there are sectors of physical devices with NFC support and biometric tokens. Software devices are applications for generating one-time passwords that can be built into two-factor authentication platforms. Applications are installed on a laptop, tablet, or mobile device. Depending on the industry, the OTP market is divided into the banking, financial services, and insurance (BFSI) sector, retail, government, defense, and others.
OTP technology has been around for a long time in the global market, and for a long time, one-time passwords were transmitted via SMS and push notifications. However, today, many companies and authoritative sources are calling for this type of OTP transmission to be abandoned in favor of methods where the user has a device to generate one-time passwords (such as a token or an app). Microsoft recently issued a statement that enterprises should abandon OTPs sent via SMS and voice calls. According to a blog post by Microsoft’s Chief Information Security Officer Alex Weinert, enterprises are urged to strengthen their solutions by abandoning unencrypted multi-factor authentication methods such as OTPs via SMS (as they can be intercepted or phishing).
In 2016, the Russian Ministry of Communications also stated that it was worth abandoning SMS messages in favor of other methods, such as sending push notifications. This recommendation applies in particular to the banking sector.
The global two-factor authentication market is highly competitive, with security and privacy of data playing a central role for clients and customers. The development of measures to prevent malware and other threats will likely drive product development, and competition between players will inevitably intensify. The main players in the global two-factor authentication market include Thales, Symantec, RSA, Fujitsu, Suprema, Google, and many others.
The most actively used OTP solutions today will be discussed below.

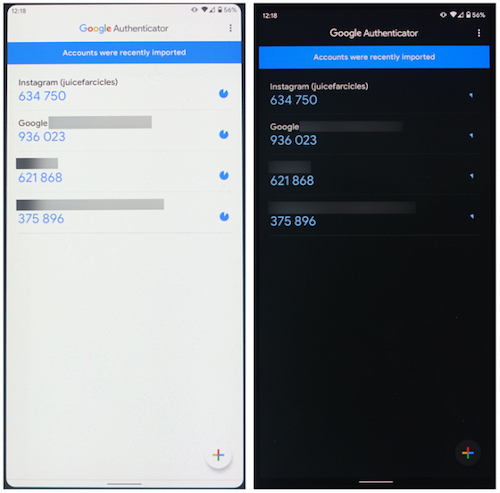
Google Authenticator interface
The advantages of the program include:
The disadvantages of the program include limited functionality.
More information about the product can be found here.
Yandex.Key interface

The advantages of the program include:
The disadvantages of the program include an interface that is not entirely convenient for use with a large number of tokens.
More information about the product can be found here.

JaCarta WebPass USB token

The advantages of JaCarta WebPass include:
It is worth noting that the token has broad functionality (for example, it can create and securely store complex, reusable passwords).
More information about the product can be found here .

RSA token

Recently, instead of tokens, smartphone applications are increasingly being used.
RSA SecurID application interface
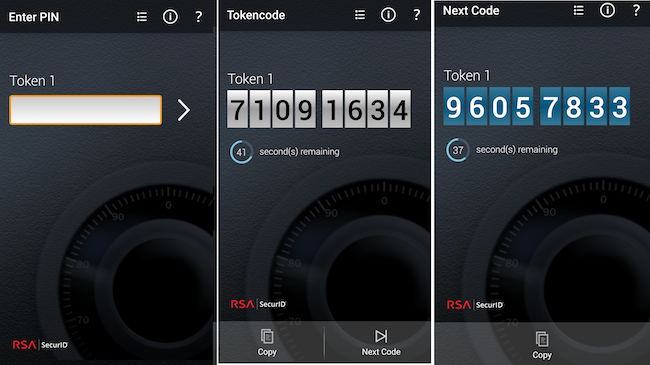
SecurID is used to protect VPNs, wireless networks, web applications, remote banking portals, Citrix and Windows terminal servers, privileged user access, local access to workstations.
The main advantage of the system is that SecurID works "out of the box" with more than 350 partner products, including web servers (Oracle Application Server, Microsoft IIS, Apache, etc.), VPN and other network devices (Cisco, Check Point, Microsoft, etc.), terminal servers (Citrix, Microsoft), Windows OS. There is an API that allows you to integrate SecurID into almost any system.
More information about the product can be found here .

Example of SafeNet OTP 110 token and SafeNet smart card


The advantages of SafeNet include:
The following should be noted as disadvantages:
More information about the product can be found here .

Example of Duo authentication window
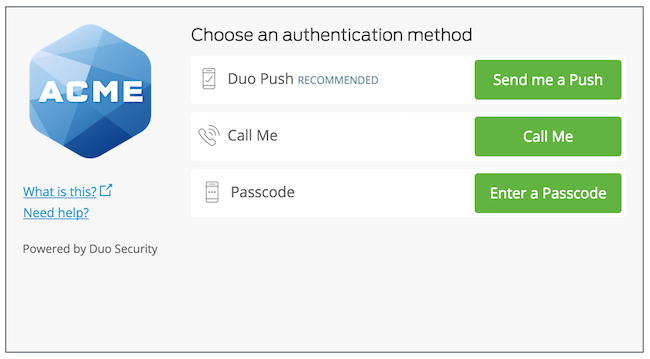
The advantages of DUO Mobile include:
The disadvantages of the system include:
More information about the product can be found here .

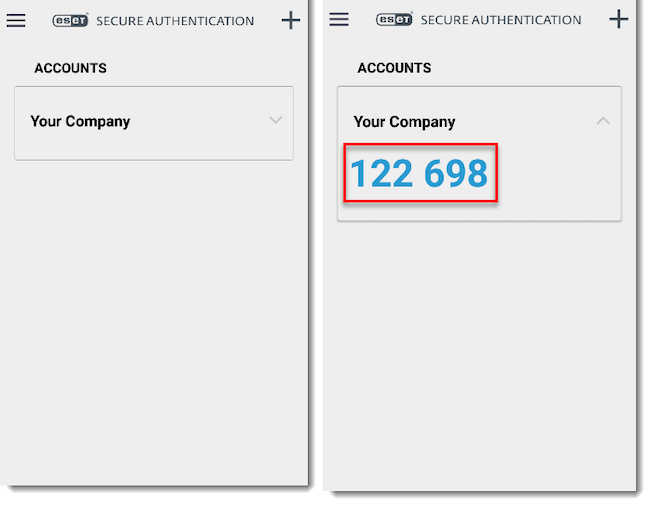
ESET Secure Authentication interface
The advantages of the system include:
The disadvantages of the system include:
You can read more about the solution in our review .

GateKeeper application appearance
The advantages of the system include:
The disadvantages of the system include:
More information about the product can be found here .

Benefits of using JAS:
JAS is registered in the Unified Register of Russian Programs for Electronic Computers and Databases (No. 2128).
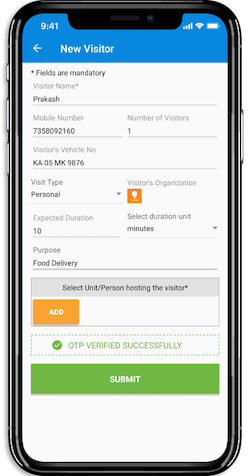
Aladdin 2FA is a mobile application for generating one-time passwords based on time (TOTP) or event (HOTP). In terms of functionality, the Aladdin 2FA application is as simple and intuitive as Google Authenticator, but when using Aladdin 2FA in corporate environments together with the JaCarta Authentication Server, the application reliably protects the secret transmitted to the user. In addition, Aladdin 2FA protects the account (data for generating one-time passwords) from cloning during transmission and activation.
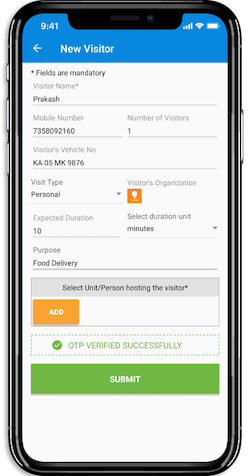
Aladdin 2FA application interface and message about impossibility of account reactivation
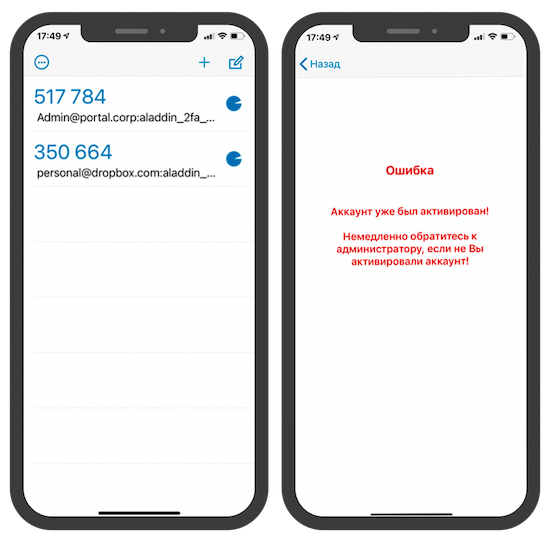
Aladdin 2FA allows you to protect application data using biometrics or a PIN code. You can try and compare different scenarios of the Aladdin 2FA application (open, similar to Google Authenticator, and protected Aladdin 2FA) on the demo portal .
The advantages of the system include:
The disadvantages of the system include:

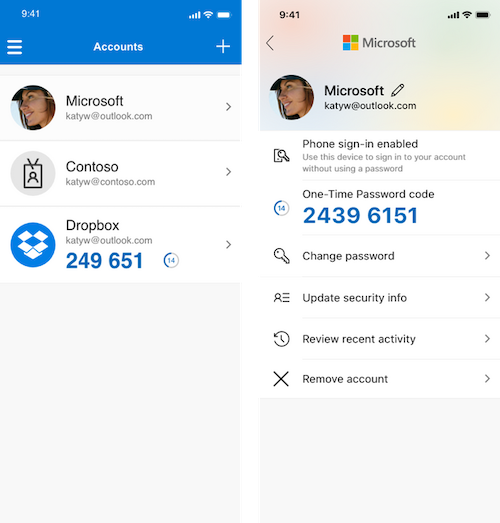
Microsoft Authenticator application interface
The system also integrates with Active Directory, which allows for easy implementation at the enterprise level using Microsoft Domain Services, and can function as a standalone cloud service.
The advantages of the system include:
The disadvantages of the system include:
More information about the product can be found here .
The mobile application implements intelligent adaptive authentication technology with a combination of one-touch push access request and one-time TOTP code to ensure maximum security and ease of use.
Multifactor application interface
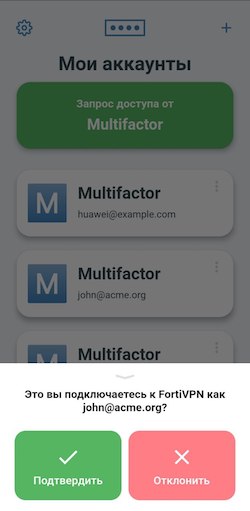

The advantages of the Multifactor application include:
The disadvantages of the system include the following:

SafeNet MobilePASS OTP generation application is compatible with a wide range of mobile clients and also provides convenient management of remote access systems such as VPN, Citrix applications, cloud applications and web portals.
SafeNet MobilePASS application interface
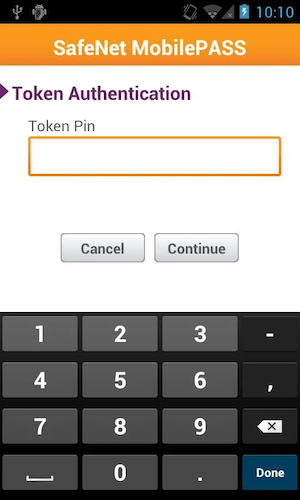
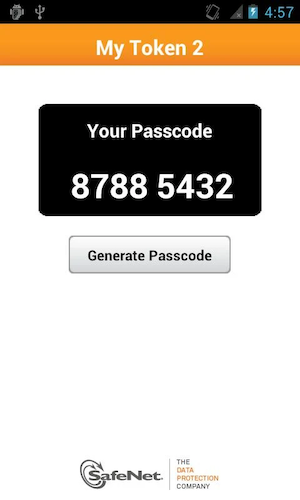
In addition to MobilePASS, you can also use Google Authenticator as an application for generating OTP in STA.
The advantages of the system include:
Systems that send one-time passwords to your phone are not secure. A better way is to use hardware devices. Mobile apps are a compromise between security and convenience.
Source
Introduction
More and more often, news appears about new attempts to hack one organization or another, and sometimes successful attempts lead to irreversible consequences, from the compromise of critical data to fines and other unpleasant consequences, up to demands for a multi-million ransom (as in the case of Garmin). With the advent of quarantine in our lives and the general transition to remote work, attackers have more room to maneuver, which has increased the needs of organizations to ensure the security of network segments. The need to prevent unauthorized access is especially acute - strengthening user authentication measures.As you know, there are many authentication methods. One of the most common options today is the OTP (One-Time Password) method, which will be discussed in this review.
To enhance security measures, a hybrid approach is increasingly being used, which involves the use of several authentication factors. OTP can be one of them.
Algorithm for working with one-time password authentication
OTP is an authentication method in which the user receives a password that is available only for one login session or one transaction in an information system or application. OTP is based on the principle that the generated password is valid for one session. Additionally, it can be limited in time (usually the password is changed within 30-60 seconds).To calculate the password, two parameters are accepted - a secret key (the initial value for the generator) and the current time value (or internal counter). The secret key is stored both in the device itself and on the authentication server. The means for generating one-time passwords can be divided into two groups: either the user has physical tools for such generation, such as hardware devices with a screen, keys, mobile applications, etc., or passwords come through a certain channel - in the form of an SMS message, push notification, etc.
Two-factor authentication is popular in many large organizations. This is due to the increase in the volume of online transactions due to the transition of customers to digital banking, the rapid growth of e-commerce, the use of online banking for the purchase of food and other goods. The spread of strong authentication is also facilitated by the launch of real-time payment systems and the introduction of POS systems at retail outlets for the convenience of users.
OTP, as one of the factors, is widely used in the banking sector, in e-commerce applications. Many of us encounter this technology almost daily, for example, when trying to transfer money from a card (a one-time password comes in an SMS message or as a push notification when trying to complete a transaction).
Among the OTP solutions, there are both commercial and completely free ones. Many providers provide free access to OTP applications with certain restrictions (for example, by the number of users), and if there is a need, it will be possible to purchase a version with advanced features. Thus, OTP protection technology has become available to anyone who wants to strengthen the protection of their data.
The Global One-Time Password (OTP) Market
Over the past decade, many companies have begun to actively strengthen their authentication measures. The number of organizations using multi-factor authentication using cryptography has tripled for consumer applications and almost doubled for enterprise applications. Much of this growth is due to the rise of cybercrime. In the last few years alone, there have been a number of incidents that have affected major organizations such as Facebook, Google, Garmin, and others.The One-Time Password method remains one of the most common in the two-factor authentication market today. By 2018, this sector was valued at $1.5 billion out of the total two-factor authentication market of $3.5 billion. According to Market Research, it will reach $3.2 billion (out of $8.9 billion) by 2024.
The global OTP token market is segmented by type, technology, and industry. Thus, devices can be divided into two main groups - physical (hard tokens) and software (soft tokens). Depending on the type of physical device, there are segments of SIM tokens, USB tokens, mini tokens. By technology type, there are sectors of physical devices with NFC support and biometric tokens. Software devices are applications for generating one-time passwords that can be built into two-factor authentication platforms. Applications are installed on a laptop, tablet, or mobile device. Depending on the industry, the OTP market is divided into the banking, financial services, and insurance (BFSI) sector, retail, government, defense, and others.
OTP technology has been around for a long time in the global market, and for a long time, one-time passwords were transmitted via SMS and push notifications. However, today, many companies and authoritative sources are calling for this type of OTP transmission to be abandoned in favor of methods where the user has a device to generate one-time passwords (such as a token or an app). Microsoft recently issued a statement that enterprises should abandon OTPs sent via SMS and voice calls. According to a blog post by Microsoft’s Chief Information Security Officer Alex Weinert, enterprises are urged to strengthen their solutions by abandoning unencrypted multi-factor authentication methods such as OTPs via SMS (as they can be intercepted or phishing).
In 2016, the Russian Ministry of Communications also stated that it was worth abandoning SMS messages in favor of other methods, such as sending push notifications. This recommendation applies in particular to the banking sector.
The global two-factor authentication market is highly competitive, with security and privacy of data playing a central role for clients and customers. The development of measures to prevent malware and other threats will likely drive product development, and competition between players will inevitably intensify. The main players in the global two-factor authentication market include Thales, Symantec, RSA, Fujitsu, Suprema, Google, and many others.
The most actively used OTP solutions today will be discussed below.
Most popular OTP systems
This section will cover the most commonly used OTP-enabled products and platforms, divided into two groups based on their type of use: corporate and consumer.Custom Products
These developments are intended for personal use, but they can also be used as part of third-party systems.
Google Authenticator
Google's OTP app is the easiest and most intuitive to use compared to the others. It is responsible for generating 6- or 8-digit codes and can be integrated with third-party apps such as password managers. Recently, the app allows you to transfer accounts from one device to another. The export-import tool creates a QR code that needs to be scanned on the recipient device.Google Authenticator interface
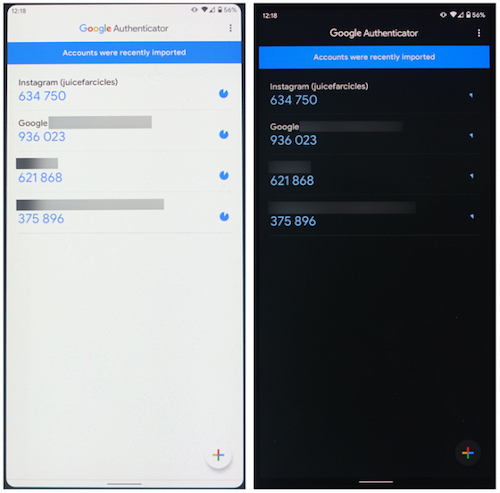
The advantages of the program include:
- Simplicity and ease of use.
- Possibility to transfer account data to other devices.
- Possibility of integration with third-party applications.
The disadvantages of the program include limited functionality.
More information about the product can be found here.
Yandex.Key
Yandex has launched a two-factor authentication mechanism and the Yandex.Key application, which generates an access code to a Yandex account on a mobile device. It can be said that the application is very similar to the Google Authenticator discussed above. To access the application, you need a four-digit PIN, the one-time password is valid for 30 seconds. Authorization in the application using a QR code is also available.Yandex.Key interface

The advantages of the program include:
- Simplicity and ease of use.
- Create backup copies of tokens in the cloud for use on multiple devices and migration to new ones.
- The ability to quickly transfer data to other devices.
The disadvantages of the program include an interface that is not entirely convenient for use with a large number of tokens.
More information about the product can be found here.
Corporate products
OTP hardware tokens

JaCarta WebPass
The device from the Russian manufacturer allows implementing two-factor user authentication in secure information systems using a one-time or multiple-use password. JaCarta WebPass can work together with the standalone high-performance authentication server JaCarta Authentication Server to ensure secure connection to remote access gateways (Microsoft, Citrix, Palo Alto, Check Point, VMware, Fortinet, etc. - the list is constantly growing), corporate systems (CRM, portals, e-mail, etc.), including Microsoft SharePoint and Microsoft Outlook Web App, web applications, sites and cloud services, remote banking systems.JaCarta WebPass USB token

The advantages of JaCarta WebPass include:
- Possibility of automatic substitution of passwords into fields of on-screen forms.
- The ability to store addresses of protected web resources and automatically launch a web browser with a transition to the saved address when pressing a button on the token.
- Full compatibility with classic OTP tokens (eToken PASS, eToken NG-OTP, etc.) according to RFC 4226.
- Support for all popular operating systems: Microsoft Windows, Linux, macOS, Google Android, Apple iOS (via Camera Connection Kit).
- The ability to store cryptocontainers of software cryptographic information protection tools, which allows the token to be used not only for authentication, but also for working with an electronic signature.
It is worth noting that the token has broad functionality (for example, it can create and securely store complex, reusable passwords).
More information about the product can be found here .

RSA SecurID
The generator (keychain) contains a built-in high-precision clock, which is used every 60 seconds to calculate a new password. The second parameter used to generate a one-time password is the initialization vector (Seed). It is "flashed" into the generator during its production. For authentication, the Authentication Manager server calculates the user's current password using the system clock and the initialization vector (each hardware token comes with a file with the Seed, which is uploaded to the server).RSA token

Recently, instead of tokens, smartphone applications are increasingly being used.
RSA SecurID application interface
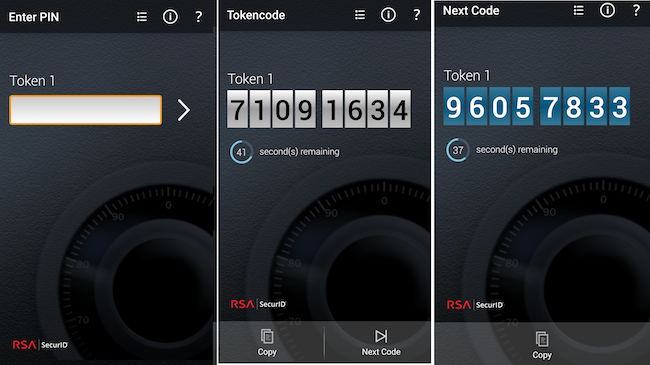
SecurID is used to protect VPNs, wireless networks, web applications, remote banking portals, Citrix and Windows terminal servers, privileged user access, local access to workstations.
The main advantage of the system is that SecurID works "out of the box" with more than 350 partner products, including web servers (Oracle Application Server, Microsoft IIS, Apache, etc.), VPN and other network devices (Cisco, Check Point, Microsoft, etc.), terminal servers (Citrix, Microsoft), Windows OS. There is an API that allows you to integrate SecurID into almost any system.
More information about the product can be found here .

SafeNet
SafeNet OTP from Thales is a hardware OTP token that provides two-factor authentication capabilities for a wide range of resources and supports OATH TOTP and HOTP protocol functions. The company has introduced several tokens: SafeNet OTP 110 (the main difference is the waterproof case), SafeNet eToken Pass and SafeNet Gold (this version implements an additional security mechanism in the form of a user PIN). There are also SafeNet OTP cards (OTP Display Card), which interact with SafeNet Trusted Access, a cloud access management service that offers single sign-on technology protected by fine-grained access policies.Example of SafeNet OTP 110 token and SafeNet smart card


The advantages of SafeNet include:
- Ease and simplicity of use.
- Lifetime warranty on select models (included for the duration of your SafeNet Trusted Access subscription, including free replacement).
- Secure remote access to networks (VPN), SaaS applications, VDI, web portals and custom applications.
- Easy operation thanks to lightweight internal configuration, low maintenance requirements and long battery life.
- Compliance with industry standards.
- Ability to work with different platforms - Eset, JaCarta Authentication Server, Microsoft MFA, SafeNet Authentication Services and others.
The following should be noted as disadvantages:
- Lack of user documentation in Russian.
- Insufficiently informative error messages and other user interface inaccuracies.
- Lack of FSTEC of Russia certificate for some models.
More information about the product can be found here .
Applications and platforms with OTP authentication capability

Duo Security
Duo Security is a multi-factor authentication system implemented using a cloud model. Currently acquired by Cisco. In addition to the widely used corporate version of the system, which also allows solving administrative tasks, there is a free version for home use. The Duo Mobile application allows you to choose a convenient authentication method: phone call, SMS message, Duo Mobile code, Duo Push, electronic key.Example of Duo authentication window
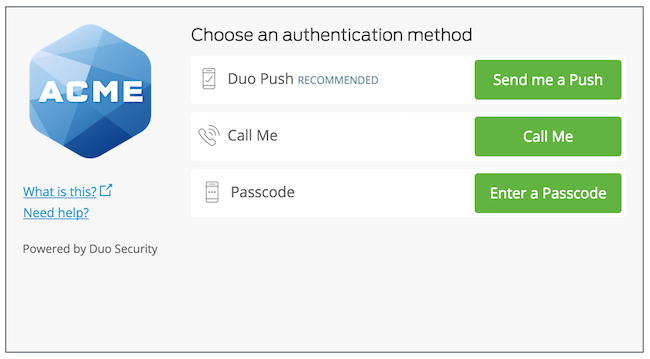
The advantages of DUO Mobile include:
- Speed of implementation.
- Flexible tariff plans.
- Scalability.
- The ability to implement a single entry point for an organization's information systems with SAML support to implement SSO across the enterprise.
- Ability to flexibly manage authentication in accordance with internal policies.
- Integration with a large number of cloud services, as well as with corporate applications and services.
- Ability to control the user's workstation and automate compliance with corporate requirements.
The disadvantages of the system include:
- Based on the infrastructure of the Amazon AWS public cloud, which may cause certain risks when implemented in the Russian Federation.
More information about the product can be found here .

ESET Secure Authentication
ESET Secure Authentication (ESA) offers the user a wide range of methods for delivering one-time passwords, from SMS messages to hardware tokens and push notifications. In addition, when the user receives a push notification on a mobile device or smartwatch, the message indicates the IP address from which the connection to the resources is made. It is also possible to add trusted IP addresses (subnets) of users to the exclusion lists, allowing them to connect to corporate resources only by login and password.ESET Secure Authentication interface
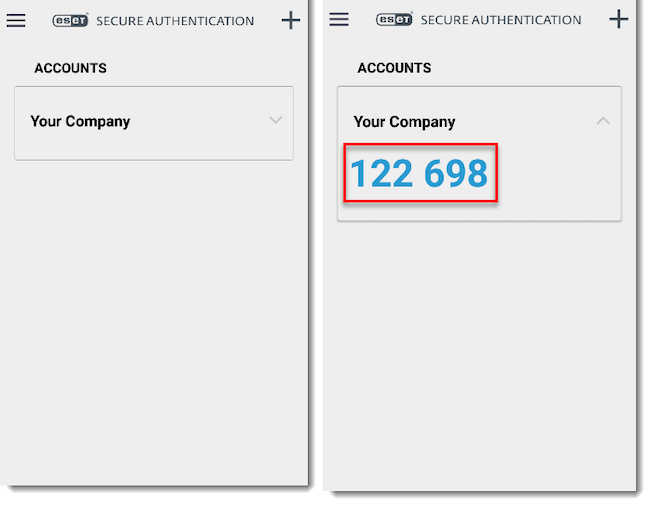
The advantages of the system include:
- The ability to easily implement two-factor authentication into the work of the enterprise's local network and provide access to web applications.
- High degree of integration with Active Directory and RADIUS services.
- Integration with other information security tools from ESET.
- Good localization and technical support in the Russian Federation.
- Integration with third-party authenticators that support the FIDO standard.
The disadvantages of the system include:
- Focus on Windows infrastructure.
- The traditional model of deploying the system on servers in a local network, the difficulty of scaling in large organizations.
You can read more about the solution in our review .

GateKeeper Enterprise
Another solution for multifactor authentication with OTP is GateKeeper. In addition to standard functionality, it offers automatic device locking when an employee leaves the workplace. The corporate version of the system allows for integration with other security and authentication systems, such as Azure AD ADFS.GateKeeper application appearance
The advantages of the system include:
- Flexibility through cloud deployment model.
- Support for a wide range of network technologies for integration with existing corporate network infrastructure.
- Possibility of multi-factor authentication, including using hardware tokens.
The disadvantages of the system include:
- Low degree of localization.
- Dependency on cloud service provider.
More information about the product can be found here .

JaCarta Authentication Server (JAS) + Aladdin 2FA
JaCarta Authentication Server (JAS) is a standalone high-performance authentication server that supports both hardware OTP tokens (e.g. JaCarta WebPass) and mobile applications that implement OTP token functionality: Aladdin 2FA, developed by Aladdin R.D., as well as third-party products, such as Google Authenticator, Yandex.Key, and any others that work on the same standard. Using JAS together with Aladdin 2FA provides an increased level of security.Benefits of using JAS:
- Enhanced user authentication using one-time passwords (OTP).
- Providing authentication on desktop computers, laptops (JAS OTP Logon).
- Easy integration with application software via standard protocols and remote access gateways.
- High performance (more than 1000 authentications per second).
JAS is registered in the Unified Register of Russian Programs for Electronic Computers and Databases (No. 2128).
Aladdin 2FA is a mobile application for generating one-time passwords based on time (TOTP) or event (HOTP). In terms of functionality, the Aladdin 2FA application is as simple and intuitive as Google Authenticator, but when using Aladdin 2FA in corporate environments together with the JaCarta Authentication Server, the application reliably protects the secret transmitted to the user. In addition, Aladdin 2FA protects the account (data for generating one-time passwords) from cloning during transmission and activation.
Aladdin 2FA application interface and message about impossibility of account reactivation
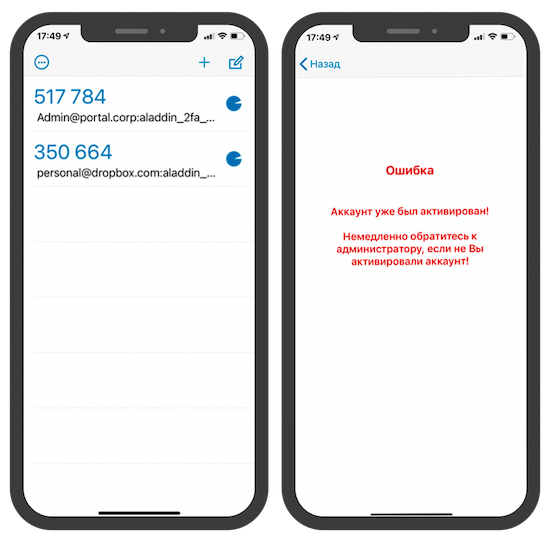
Aladdin 2FA allows you to protect application data using biometrics or a PIN code. You can try and compare different scenarios of the Aladdin 2FA application (open, similar to Google Authenticator, and protected Aladdin 2FA) on the demo portal .
The advantages of the system include:
- Ease of integration and use.
- Support in Aladdin 2FA of the enhanced security mechanism during the secret (initialization vector) transfer process together with the JAS authentication server.
The disadvantages of the system include:
- Mobile application limitation by minimum operating system version: iOS 12 and above, Android 5 and above.

Microsoft MFA
This authentication complex is part of the Microsoft Azure and Office 365 ecosystem of services. When a user signs in to an application or service and receives a multi-factor authentication request, they can choose one of the registered forms of additional verification: Microsoft Authenticator app, OATH hardware token, SMS, voice call.Microsoft Authenticator application interface
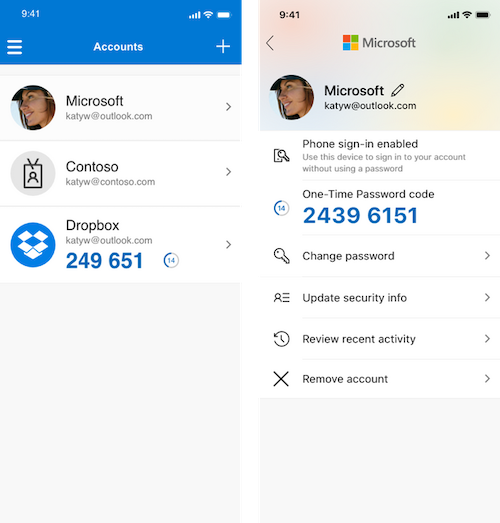
The system also integrates with Active Directory, which allows for easy implementation at the enterprise level using Microsoft Domain Services, and can function as a standalone cloud service.
The advantages of the system include:
- Available to Azure and Office 365 service users.
- Information and technical support.
- Having a good public cloud infrastructure.
- Possibility of integration with Active Directory.
The disadvantages of the system include:
- Traditional focus on the Microsoft ecosystem.
More information about the product can be found here .
Multifactor
"Multifactor" is a cloud-based multifactor authentication system with support for corporate SSO for any number of users and information resources. The system is designed to protect sites, applications, VPN/VDI/RDP connections, Windows and Linux infrastructure with an additional access factor.The mobile application implements intelligent adaptive authentication technology with a combination of one-touch push access request and one-time TOTP code to ensure maximum security and ease of use.
Multifactor application interface
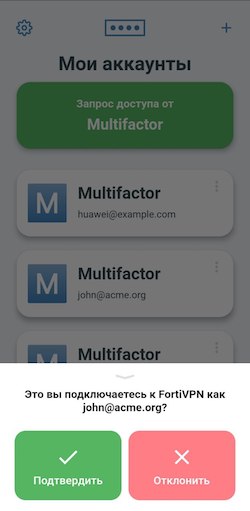

The advantages of the Multifactor application include:
- Cross-platform (iOS, Android, Huawei).
- Simple one-touch authentication from push access request.
- Support for the second factor registration mode in dialog mode with the user in VPN and VDI clients.
- Authentication server in the Russian Federation (DataLine data center).
- Additional access protection with a one-time TOTP code.
- Reliable protection against phishing attacks thanks to a combination of Push and TOTP.
- Possibility of unlimited use of external TOTP accounts.
The disadvantages of the system include the following:
- The intelligent combined Push and TOTP solution is provided free of charge for up to three users only.

SafeNet Authentication Services
SafeNet Trusted Access (STA) is a cloud-based solution that simplifies access management for both cloud services and enterprise applications. STA supports OTP authentication methods via in-app push notification, SMS, or hardware tokens.SafeNet MobilePASS OTP generation application is compatible with a wide range of mobile clients and also provides convenient management of remote access systems such as VPN, Citrix applications, cloud applications and web portals.
SafeNet MobilePASS application interface
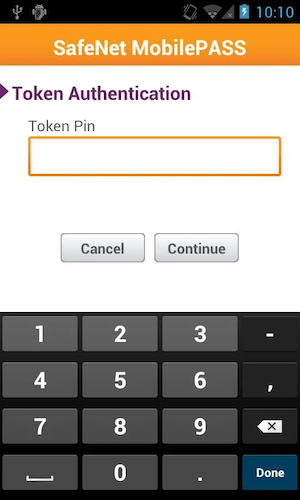
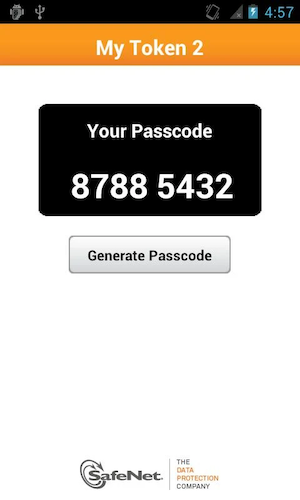
In addition to MobilePASS, you can also use Google Authenticator as an application for generating OTP in STA.
The advantages of the system include:
- Cloud implementation with the ability to create independent full-fledged authentication servers.
- Integration via RADIUS, OpenID and SAML, interaction with AD.
- User login to different applications through a single point of entry (SSO).
- The ability to implement the requirements of the main Russian regulators in terms of ensuring information security when managing user access.
Disadvantages of One-Time Password (OTP) Technology
Like any other technology, OTP has a number of drawbacks that are worth taking into account.- In some cases, using one-time passwords increases the risk of compromising the entire system's data , since when an attacker accesses the OTP authentication server, all components of the system will trust this server.
- The risk of one-time passwords being transferred to an attacker, for example if the token is lost. It is worth mentioning here that in addition to a one-time password, a reusable password should often be entered in the application, but it can also be compromised in the same way as a regular password.
- Incorrect functioning of OTP systems , which can lead to the presence of vulnerabilities - for example, to an increase in the validity period of a one-time password, which will allow an attacker to guess the password during this time.
- The possibility of obtaining one-time passwords through phishing, as happened in 2005 at the Bank of Sweden and in 2006 at Citibank (USA).
- Desync between OTP tokens and authentication servers over time, which means that at a given moment there may be several “correct” one-time passwords on the server. As an example, let’s assume that the approximate desync time is 5 minutes and the OTP change period is 30 seconds; in such a situation, up to 10 “correct” passwords may exist at the same time, which increases the likelihood of unauthorized access.
Conclusions
In summary, it should be noted that One-Time Password technology greatly increases the resistance of an information system to attack compared to traditional static password phrases. To increase the overall level of security, it is preferable to combine OTP with other methods, such as biometrics or PIN.Systems that send one-time passwords to your phone are not secure. A better way is to use hardware devices. Mobile apps are a compromise between security and convenience.
Source
