Mutt
Professional
- Messages
- 1,458
- Reaction score
- 1,299
- Points
- 113
Doctor Web detected the Android.BankBot.149.origin Trojan back in January 2016. After the cybercriminals published the source code of this banker, virus writers created many new modifications based on it, which are actively developing to this day. Some of them have turned into multifunctional malware capable of stealing usernames and passwords from cryptocurrency applications and spying on users.
At the time of its inception, Android.BankBot.149.origin was a banking Trojan with a typical feature set. He showed phishing windows, with which he stole logins and passwords from accounts of online banking systems of various credit organizations, stole information about bank cards, and could also intercept incoming SMS in order to gain access to one-time passwords to confirm money transfers. When the source code of this malicious application became available to everyone, virus writers began to create many similar Trojans based on it. At the same time, cybercriminals actively distributed them through the Google Play catalog. Among these bankers were Android.BankBot.179.origin, Android.BankBot.160.origin, Android.BankBot.163.origin, Android.BankBot.193.origin and Android.Banker.202.origin, which virus writers disguised as harmless and useful applications.
Another Trojan, in the creation of which cybercriminals used the previously published code, was added to the Dr.Web virus database as Android.BankBot.250.origin. He is also known as Anubis. Doctor Web virus analysts discovered the first versions of this malicious program in November 2017. These modifications of the Trojan almost completely copied the capabilities of Android.BankBot.149.origin. The banker could perform the following actions:
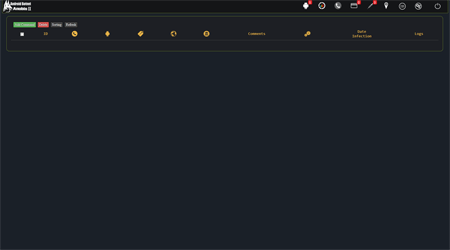
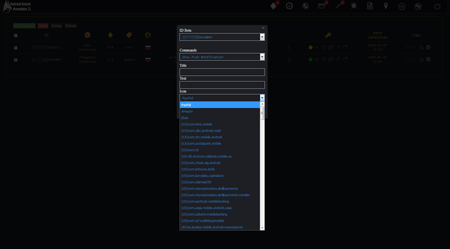
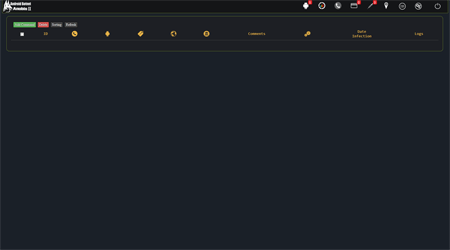
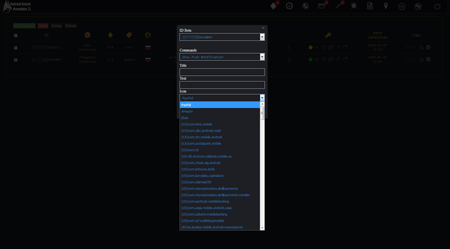
The illustrations below show an example of a control panel for one of the first versions of the Android.BankBot.250.origin Trojan:
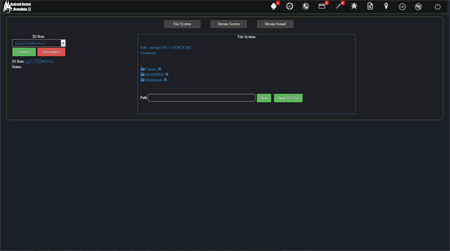
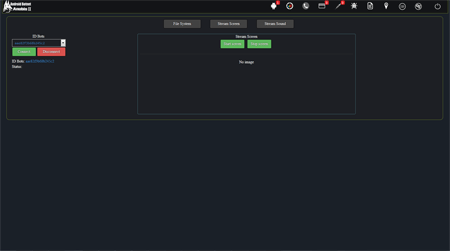
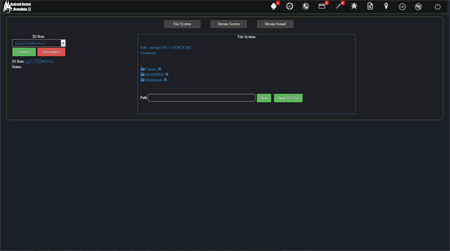
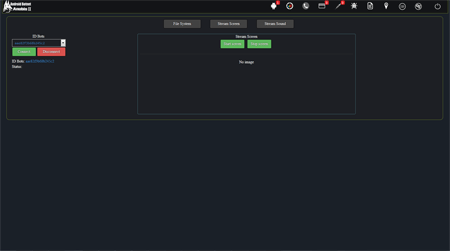
However, as Android.BankBot.250.origin updates were released, its functionality gradually expanded. One of the new modifications of the Trojan, dubbed Android.BankBot.325.origin, allows remote access to infected devices. As a result, the banker could work as a remote administration utility or RAT (Remote Administration Tool). One of its new functions is viewing the list of files that were stored in the memory of infected smartphones or tablets, uploading any of them to the control server, and deleting them. In addition, the Trojan could track everything that was happening on the screen, taking screenshots and sending them to the attackers. In addition, at the command of the virus writers Android.BankBot.325.origin listened to the environment using the built-in microphone. Therefore, it could also be used for cyber espionage. The following images show a section of the administration panel of the Trojan's command and control server, where attackers could have issued the appropriate command to the Trojan:
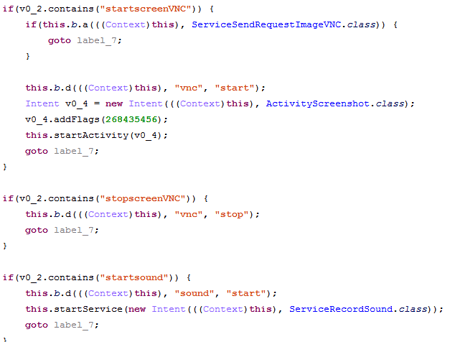
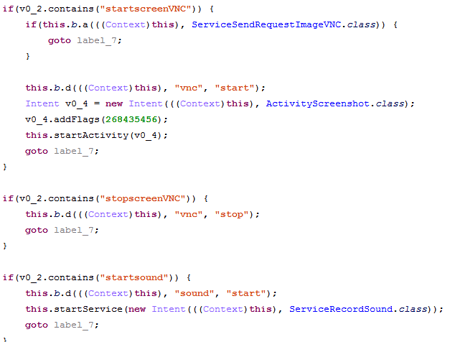
At the same time, the analysis of the banker showed that virus writers use the abbreviation "VNC" in the names of methods, as well as in control commands, which stands for Virtual Network Computing and refers to the remote desktop access system. However, in the Trojan Android.BankBot.325.origin it is not implemented in any way, and the cybercriminals only use its name for their own convenience. Nevertheless, we can conclude that cybercriminals have begun to develop the ability to remotely control the screen of infected devices and turn the banker into a more versatile malicious application. Below is a snippet of the Android.BankBot.325.origin code where the specified abbreviation is used:
One of the latest modifications of Android.BankBot.325.origin, which was investigated by Doctor Web virus analysts, has received even more functions. The list of banker's features now includes:
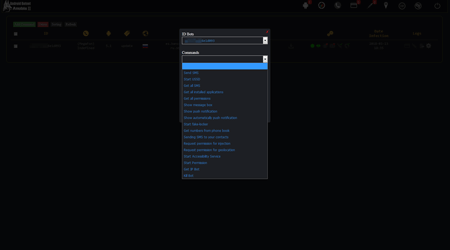
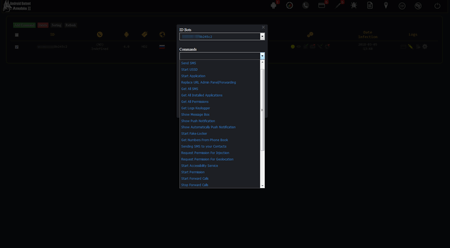
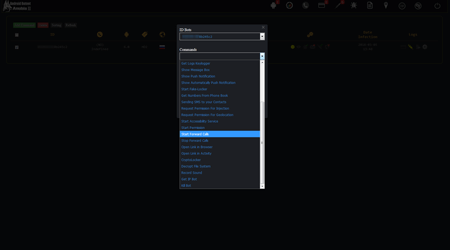
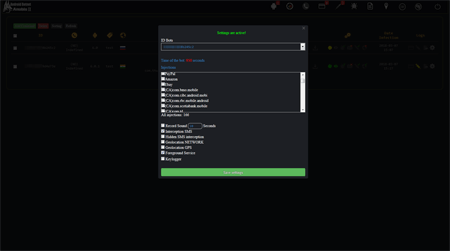
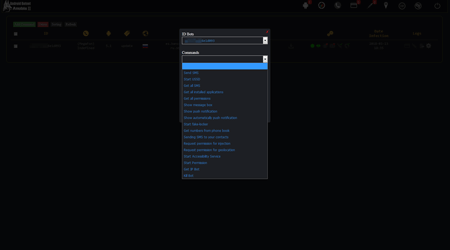
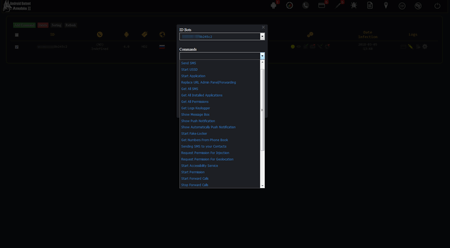
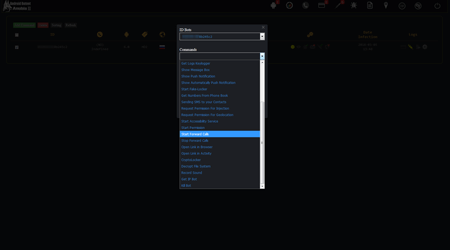
The following illustrations show the list of commands that cybercriminals can send to the banker through the administration panel:
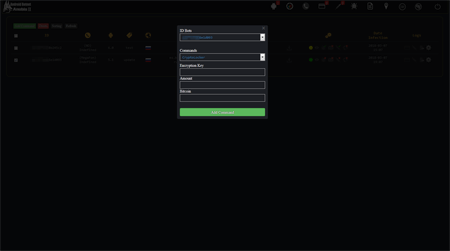
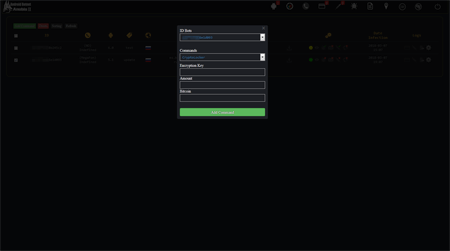
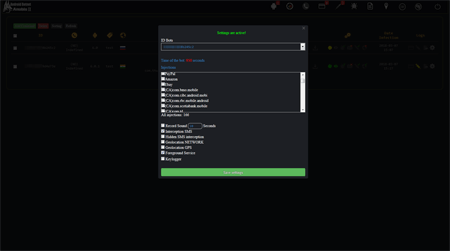
Most of the commands sent to the banker are configured in the same panel. For example, the image below shows the configuration of file encryption settings. Virus writers can set the encryption key, the ransom amount (for example, in bitcoins) that Android.BankBot.325.origin will ask the victim for, as well as their wallet number for transfer:
Fake notifications are also configured there to force the user to launch the application the cybercriminals need. Immediately after the target program starts, the Trojan displays a phishing form for entering a login, password and other secret information over its window and sends it to virus writers.
Phishing windows themselves are configured in the same way, along with additional parameters:
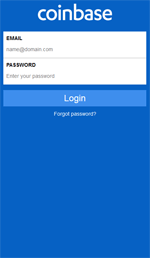
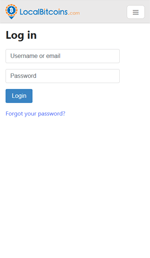
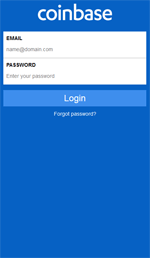
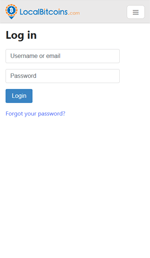
Android.BankBot.325.origin shows fake login forms when launching over 160 programs, including software for accessing banking services, payment systems and social networks. At the same time, popular applications for working with cryptocurrencies were added to them. Android.BankBot.325.origin is not the first banker to try to steal logins and passwords from such programs, but it was here that cybercriminals tried to make the appearance of phishing windows as similar as possible to the interface of real applications. Examples of such fraudulent login forms are shown in the following images:
Virus analysts have found that the Trojan attacks users from Russia, Ukraine, Turkey, England, Germany, France, India, USA, Hong Kong, Hungary, Israel, Japan, New Zealand, Kenya, Poland and Romania. However, at any time, this list can be replenished by other states, if cybercriminals show interest in them. Doctor Web specialists expect that the authors of Android.BankBot.325.origin will continue to improve the Trojan's functionality and add new capabilities to remotely control infected smartphones and tablets. It is possible that additional spyware functions will appear in the Trojan. Dr.Web anti-virus products for Android successfully detect all known modifications of this malicious application, so it is not dangerous for our users.


drweb.com
At the time of its inception, Android.BankBot.149.origin was a banking Trojan with a typical feature set. He showed phishing windows, with which he stole logins and passwords from accounts of online banking systems of various credit organizations, stole information about bank cards, and could also intercept incoming SMS in order to gain access to one-time passwords to confirm money transfers. When the source code of this malicious application became available to everyone, virus writers began to create many similar Trojans based on it. At the same time, cybercriminals actively distributed them through the Google Play catalog. Among these bankers were Android.BankBot.179.origin, Android.BankBot.160.origin, Android.BankBot.163.origin, Android.BankBot.193.origin and Android.Banker.202.origin, which virus writers disguised as harmless and useful applications.
Another Trojan, in the creation of which cybercriminals used the previously published code, was added to the Dr.Web virus database as Android.BankBot.250.origin. He is also known as Anubis. Doctor Web virus analysts discovered the first versions of this malicious program in November 2017. These modifications of the Trojan almost completely copied the capabilities of Android.BankBot.149.origin. The banker could perform the following actions:
- send SMS with the specified text to the number specified in the command;
- execute USSD requests;
- send copies of SMS stored on the device to the control server;
- receive information about installed applications;
- show dialog boxes with the text specified in the command;
- request additional permissions for work;
- Demonstrate push notifications, the content of which was specified in the command;
- show a push notification, the content of which is specified in the Trojan's code;
- block the device screen with the WebView window, which displayed the content of the web page received from the server;
- transfer all numbers from the phone book to the server;
- send SMS to all numbers from the phone book;
- access information about the device and its location;
- Request access to Accessibility Service
- find out the IP address of an infected smartphone or tablet;
- clear your config file and stop your own work.
The illustrations below show an example of a control panel for one of the first versions of the Android.BankBot.250.origin Trojan:
However, as Android.BankBot.250.origin updates were released, its functionality gradually expanded. One of the new modifications of the Trojan, dubbed Android.BankBot.325.origin, allows remote access to infected devices. As a result, the banker could work as a remote administration utility or RAT (Remote Administration Tool). One of its new functions is viewing the list of files that were stored in the memory of infected smartphones or tablets, uploading any of them to the control server, and deleting them. In addition, the Trojan could track everything that was happening on the screen, taking screenshots and sending them to the attackers. In addition, at the command of the virus writers Android.BankBot.325.origin listened to the environment using the built-in microphone. Therefore, it could also be used for cyber espionage. The following images show a section of the administration panel of the Trojan's command and control server, where attackers could have issued the appropriate command to the Trojan:
At the same time, the analysis of the banker showed that virus writers use the abbreviation "VNC" in the names of methods, as well as in control commands, which stands for Virtual Network Computing and refers to the remote desktop access system. However, in the Trojan Android.BankBot.325.origin it is not implemented in any way, and the cybercriminals only use its name for their own convenience. Nevertheless, we can conclude that cybercriminals have begun to develop the ability to remotely control the screen of infected devices and turn the banker into a more versatile malicious application. Below is a snippet of the Android.BankBot.325.origin code where the specified abbreviation is used:
One of the latest modifications of Android.BankBot.325.origin, which was investigated by Doctor Web virus analysts, has received even more functions. The list of banker's features now includes:
- sending SMS with the specified text to the number specified in the command;
- execution of USSD requests;
- launching programs;
- changing the address of the command and control server;
- sending copies of SMS stored on the device to the control server;
- getting information about installed applications;
- interception of characters entered on the keyboard (keylogger);
- request for additional work permits;
- showing dialog boxes with the content specified in the command;
- showing push notifications, the content of which is specified in the command;
- displaying a push notification, the content of which is specified in the Trojan's code;
- sending to the server all numbers from the phone book;
- sending SMS to all numbers from the phone book;
- locking the device screen with a WebView window, which displays the content of the web page received from the server;
- Requesting access to Accessibility Service functions;
- call forwarding;
- opening in the browser the websites specified in the commands;
- opening links to web pages using WebView;
- file encryption and ransom demand;
- decryption of files;
- recording surroundings using the microphone of the device;
- gaining access to information about the device and its location;
- obtaining the IP address of the device;
- clearing the configuration file and stopping the Trojan.
The following illustrations show the list of commands that cybercriminals can send to the banker through the administration panel:
Most of the commands sent to the banker are configured in the same panel. For example, the image below shows the configuration of file encryption settings. Virus writers can set the encryption key, the ransom amount (for example, in bitcoins) that Android.BankBot.325.origin will ask the victim for, as well as their wallet number for transfer:
Fake notifications are also configured there to force the user to launch the application the cybercriminals need. Immediately after the target program starts, the Trojan displays a phishing form for entering a login, password and other secret information over its window and sends it to virus writers.
Phishing windows themselves are configured in the same way, along with additional parameters:
Android.BankBot.325.origin shows fake login forms when launching over 160 programs, including software for accessing banking services, payment systems and social networks. At the same time, popular applications for working with cryptocurrencies were added to them. Android.BankBot.325.origin is not the first banker to try to steal logins and passwords from such programs, but it was here that cybercriminals tried to make the appearance of phishing windows as similar as possible to the interface of real applications. Examples of such fraudulent login forms are shown in the following images:
Virus analysts have found that the Trojan attacks users from Russia, Ukraine, Turkey, England, Germany, France, India, USA, Hong Kong, Hungary, Israel, Japan, New Zealand, Kenya, Poland and Romania. However, at any time, this list can be replenished by other states, if cybercriminals show interest in them. Doctor Web specialists expect that the authors of Android.BankBot.325.origin will continue to improve the Trojan's functionality and add new capabilities to remotely control infected smartphones and tablets. It is possible that additional spyware functions will appear in the Trojan. Dr.Web anti-virus products for Android successfully detect all known modifications of this malicious application, so it is not dangerous for our users.


drweb.com
