Lord777
Professional
- Messages
- 2,576
- Reaction score
- 1,565
- Points
- 113
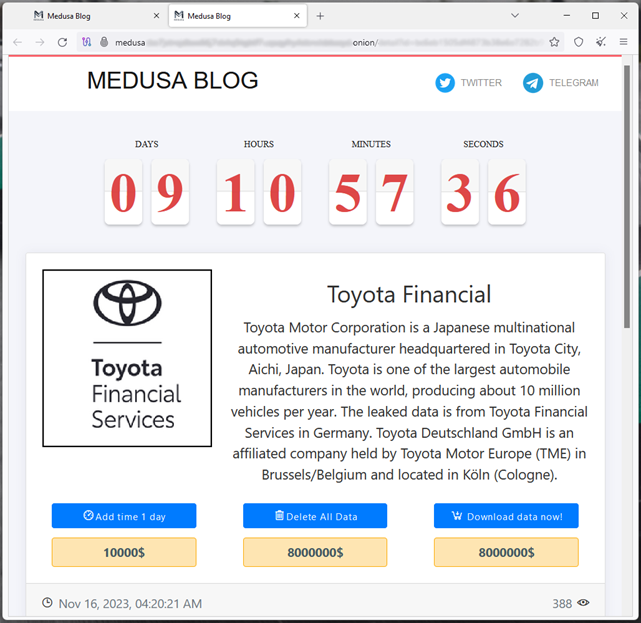
The Medusa group decided to borrow a time-tested method from Lockbit.
Toyota Financial Services (TFS), the financial arm of the world-famous auto giant Toyota, is facing a major cyber threat. Recently, the company discovered traces of unauthorized access to its systems in the regions of Europe and Africa. The ransomware group Medusa claimed responsibility for the hack.
TFS, a subsidiary of Toyota Motor Corporation, occupies a significant position in the global market, covering approximately 90% of the territories where Toyota cars are sold. The company offers its clients auto finance services.
Hackers demand a ransom of $ 8 million for deleting stolen data. Toyota has 10 days to make a decision, but the deadline can be extended for another day by paying an additional $ 10,000.
Despite threats from Medusa, Toyota Finance has not yet confirmed the leak.
As evidence, the attackers posted samples of data on their site, including financial documents, spreadsheets, hashed passwords from corporate accounts, user credentials, contracts, passport scans, estimates, employee email addresses, and much more.
They also provided a text document that shows the hierarchical structure of all data, including a list of files and folders. Most of the documents are in German.
A Toyota spokesperson told reporters:
"Toyota Financial Services Europe & Africa recently identified unauthorized activity in the systems of some divisions. We immediately shut down the systems to mitigate the risks, and also started cooperating with law enforcement agencies."
He also claims that in most countries the affected resources are already operating normally.
After Medusa announced the TFS hack, analyst Kevin Beaumont noted that the infrastructure of the German TFS division had an open Citrix Gateway access point, which has not been updated since August 2023. This means that the company's systems were affected by the known critical vulnerability Citrix Bleed (CVE-2023-4966).
Recently, experts confirmed that the Lockbit ransomware group used publicly available exploits for Citrix Bleed to attack organizations such as the Industrial and Commercial Bank of China (ICBC), DP World, Allen & Overy and Boeing.
There is reason to believe that other groups have followed Lockbit's example, so the risk of using Citrix Bleed will increase in the near future, covering thousands of potential victims around the world.
Toyota Financial Services (TFS), the financial arm of the world-famous auto giant Toyota, is facing a major cyber threat. Recently, the company discovered traces of unauthorized access to its systems in the regions of Europe and Africa. The ransomware group Medusa claimed responsibility for the hack.
TFS, a subsidiary of Toyota Motor Corporation, occupies a significant position in the global market, covering approximately 90% of the territories where Toyota cars are sold. The company offers its clients auto finance services.
Hackers demand a ransom of $ 8 million for deleting stolen data. Toyota has 10 days to make a decision, but the deadline can be extended for another day by paying an additional $ 10,000.
Despite threats from Medusa, Toyota Finance has not yet confirmed the leak.
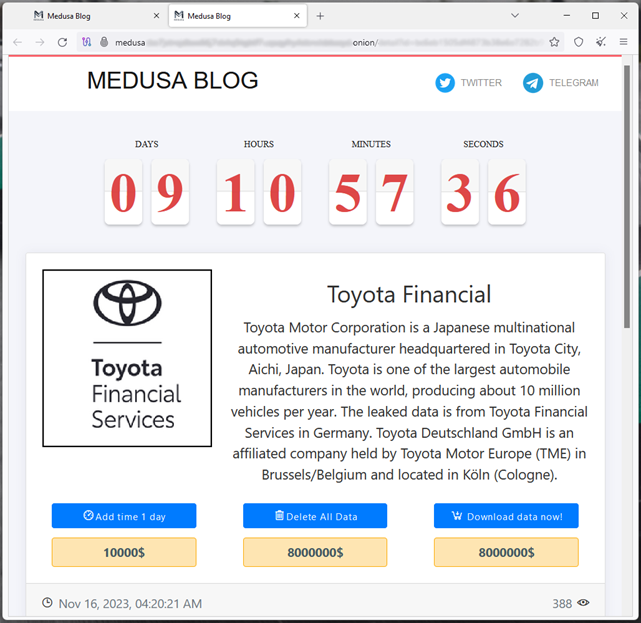
As evidence, the attackers posted samples of data on their site, including financial documents, spreadsheets, hashed passwords from corporate accounts, user credentials, contracts, passport scans, estimates, employee email addresses, and much more.
They also provided a text document that shows the hierarchical structure of all data, including a list of files and folders. Most of the documents are in German.
A Toyota spokesperson told reporters:
"Toyota Financial Services Europe & Africa recently identified unauthorized activity in the systems of some divisions. We immediately shut down the systems to mitigate the risks, and also started cooperating with law enforcement agencies."
He also claims that in most countries the affected resources are already operating normally.
After Medusa announced the TFS hack, analyst Kevin Beaumont noted that the infrastructure of the German TFS division had an open Citrix Gateway access point, which has not been updated since August 2023. This means that the company's systems were affected by the known critical vulnerability Citrix Bleed (CVE-2023-4966).
Recently, experts confirmed that the Lockbit ransomware group used publicly available exploits for Citrix Bleed to attack organizations such as the Industrial and Commercial Bank of China (ICBC), DP World, Allen & Overy and Boeing.
There is reason to believe that other groups have followed Lockbit's example, so the risk of using Citrix Bleed will increase in the near future, covering thousands of potential victims around the world.

