Editor's note: There is no denying that ransomware is currently generating huge revenues for cybercriminals.
Some groups seeking to get rich are aggressively pushing the boundaries. They raise their demands to seven or eight figures, threaten to publish data online if payments are not made, and target hospitals and other vulnerable organizations.
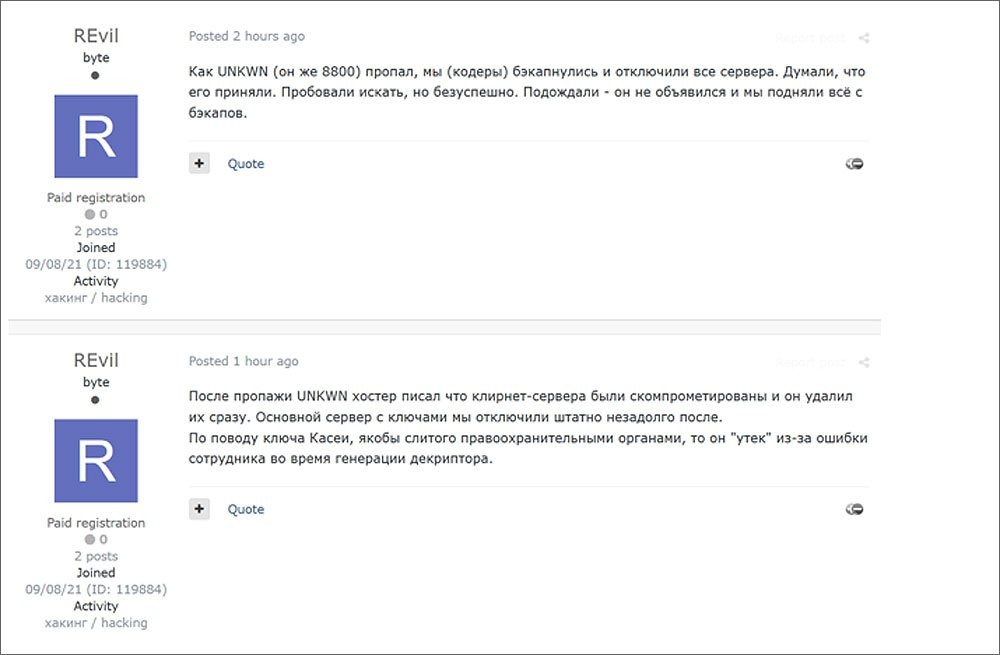
One such group that has gained fame for its bold and lucrative tactics is REvil, also known as Sodinokibi. The group provides "ransomware as a service". Developers sell malware to partners who use it to block the organization's data and devices.
In addition to publishing victim data online in cases where companies fail to meet the requirements, REvil has attracted attention for its
extortion attempts against then-President Donald Trump and claims to have generated $ 100 million in revenue from its operations. According to a representative of REvil, who uses the pseudonym Unknown, the group has big plans for 2021.
Some of Unknown's claims, such as the presence of affiliates with access to ballistic missile launch systems and nuclear power plants, seem improbable-until you read the
reports that make them seem eerily
plausible. Record cannot verify the veracity of these statements. Unknown recently spoke with Dmitry Smilyants, a threat analysis expert at Recorded Future, about using ransomware as a weapon, non-interference in politics, experimenting with new tactics, and much more. The interview was conducted in Russian, translated into English by a professional translator, and edited for clarity.
Dmitry Smilyanets: Unknown, how did you decide to engage in blackmail?
UNK: To be honest, it was a long time ago. Since 2007, when winlockers and SMS appeared. Even then, it brought a good profit.
DS: You made a $ 1 million deposit on a hacker forum and mentioned $ 100 million in revenue-given that you receive payments in cryptocurrency, you probably have half a billion dollars today. How much will be enough for you to stop using ransomware?
UNK: You did the math right. The deposit was withdrawn precisely because of the exchange rate. For me personally, there is no ceiling on the amount. I just love doing it and making a profit from it. There is never too much money, but there is always the risk of running out of it. Although, if we talk about advertisers, one felt that $ 50 million was enough, and retired. However, four months later he returned — the money was not enough. Think about it.
DS: Earlier, you said that you remain apolitical and have a purely financial motivation. But if you decide that you have made enough money, can your point of view change and you decide to influence geopolitics?
UNK: I really don't want to be a bargaining chip. We took a swing at politics, and nothing good came of it – only losses. With the current geopolitical relations, we are making good money without any interference.
DS: What makes REvil so special? Code? Affiliated companies? Media attention?
UNK: I think it all works together. For example, this interview. It seems, why is this even necessary? On the other hand, it is better to give it to us than our competitors. Unusual ideas, new methods, and brand reputation all produce good results. As I said, we are creating a new branch of ransomware development. If you look at the competitors, unfortunately, many simply copy our ideas and, most surprisingly, the style of the text of our messages. This is good — they try to show that they are not worse than us, try to reach our level and even try to surpass us in some ways. For example, with these versions of Linux and so on. But this is only temporary. Of course, we are also working on all this, but with one caveat – everything will be much better. So a little slower.
REvil uses its" Happy Blog " on the darknet to advertise auctions of data for ransomware victims who have not paid their claims.
DS: Elliptic Curve Cryptography (ECC) was a really good choice [Editor's note: ECC has a smaller key size than the RSA-based public key system, which makes it attractive to affiliates] What else are you proud of, what part of the code? How do you decide when it's time to add new features to your code?
UNK: IOCP search, reverse connection borrowed from crabs [carders], server-side protection system – there are many advantages, it's better to read reviews. Personally, I really like the encryption system. It was almost perfect.
DS: I was impressed by the variety of packers and cryptographers that I found in your malware. Do you sell them to others? I once saw one of them used in a sample of the Maze malware. Do you sell them, or did one of your employees move to a competitor?
UNK: Partners often switch, and this is why there is such a variety.
DS: Pavel Sitnikov said that you bought the GandCrab code from Maxim Plakhti, is that true?
UNK: It's true that we bought it, but we don't know the names or anything.
DS: Do you believe that ransomware is the perfect weapon for cyber warfare? Are you not afraid that one day a real war may start?
UNK: Yes, these weapons can be very destructive. Well, I know from Po that a number of affiliates have access to a ballistic missile launch system, one to a US Navy cruiser, a third to a nuclear power plant, and a fourth to a weapons factory. It is quite realistic to start a war. But it's not worth it — the consequences are unprofitable.
DS: What other regions besides the CIS [mostly made up of post-Soviet republics] do you try to avoid? Which organizations never pay?
UNK: All CIS countries, including Georgia and Ukraine. First of all, because of geopolitics. Secondly, because of the laws. Third, we avoid some of them out of patriotism. Very poor countries don't pay: India, Pakistan, Afghanistan and so on.
DS: You mentioned earlier that you and your partners understand the risks of going abroad and don't travel. Do you think that a "wind of change" may blow and local law enforcement agencies will pay attention to your operations?
UNK: If we go into politics, yes. If we look at the CIS countries, yes. Otherwise, we remain neutral.
DS: Do old-school criminals cause any problems?
UNK: No.
DS: What is your usual reaction when you see a ransomware gang or its affiliate get charged or arrested? Netwalker and Egregor reduced their operations after the raids, how do you feel about this?
UNK: Neutral. This is a normal workflow. Due to the closure of Maze, we have only increased the number of partners. So for us, I would say that this is in some ways positive.
DS: What is the maximum number of affiliates that worked with you at the same time?
UNK: 60.
DS: Are they leaving because they're getting involved with ransomware, or because they're starting to work with other programs to get better rates? Do you face a problem when a partner moves to a competitor?
UNK: There are two options. 30% leave because they have earned enough. But, of course, they always come back sooner or later. In the second case, yes, they go to competitors who dump (up to 90% , etc.). Of course, this is unpleasant, but it is competition. This means that we must make sure that people come back. Give them what others don't.
DS: Some groups give a percentage of their earnings to charity. What is your opinion on this issue? Who would you like to donate a million dollars to?
UNK: Free projects for developing anonymization tools.
DS: How has your interaction with victim organizations changed since the beginning of the pandemic?
UNK: A lot has changed. There is a crisis, they can't pay the amounts that were there before. Except for pharmaceutical companies. I think they should be given more attention. They're doing fine. We need to help them.
DS: Do your operators target organizations that have cyber insurance?
UNK: Yes, this is one of the most delicious dishes. Especially if you first hack insurers – get their customer base and work purposefully. And after we go through the list, you can take on the insurer itself.
DS: How do you feel about the ransomware negotiators? Is it easier to deal with professionals? Do they help or complicate the task?
UNK: 70% is only needed to bring down the price. Very often, they complicate the task. Well, for example, the company has revenue of $ 1 billion. They are being extorted $ 1 million. The negotiator comes and says: we don't care, we won't give you more than $ 15,000. We are reducing the price to $ 900,000. He's offering $ 20,000. Well, then we understand that a conversation with him is meaningless, and we start publishing data so that the network owners will give him a blow on the head for such negotiations. And, of course, after such tricks, the price only increases. Instead of 1 million dollars, they will pay one and a half. No one likes hucksters, especially with show-offs. So more often than not, they cause more harm. They only help when buying BTC or Monero. Everything else is harmful.
DS: Do you recommend any specific negotiators to compromised companies, or do they look for them on their own? Not everyone has 100 BTC to buy back data, and it's not so easy to get them in a short time.
UNK: We write to decent intermediaries so that they know the goal and can establish a dialogue. We give good discounts to good intermediaries so that they get a small profit, and companies pay less. As for deadlines — we can always allocate additional time. In general, if there is an understanding that you need to pay, but not so much, we will find a common language. But if we get delusional messages like "There's no money" or "We'll pay one-tenth," you have no one to blame but yourself.
Links to the REvil attacks are collected from private and clandestine sources. Courtesy of Recorded Future.
DS: You said that you want to apply additional pressure through DDoS. How effective is this scheme?
UNK: We don't use it often, unlike calls. Calling gives a very good result. We call each target, as well as their partners and journalists – the pressure increases significantly. And after that, if you start posting files, well, that's just great. But to end DDoS is to kill the company. Literally. I think we'll go after CEOs and / or founders of companies. Personal OSINT, bullying. I think this will also be a very interesting option. But victims should understand that the more resources we spend before paying the ransom – the more they will have to pay.
DS: Tell me a secret.
UNK: When I was a kid, I used to go through garbage cans and smoke cigarette butts. I walked 10 km one way to school. I wore the same clothes for six months. In my youth, I didn't eat in a communal apartment for two or three days. I'm a millionaire now.