Lord777
Professional
- Messages
- 2,576
- Reaction score
- 1,565
- Points
- 113
I will tell you about the favorite operating system of real hackers. Everything is exactly like in spy films!
2009 saw a modest revolution in the OS world. You probably haven't heard of it, but the guys from that same Tor Project released their own operating system, codenamed TAILS (The Amnesic Incognito Live System). She gained her fame mainly thanks to Edward Snowden, who was her active user at the time of the NSA data leak. Today we will analyze what is cool about it and why it is generally needed.

Tails is not a classic OS. The most important thing you need to know is that "tails" are launched directly from the USB stick. As for me, this is very cool and I immediately remember the scenes of hacking over computers from some Hollywood blockbusters. As for the base, this is Linux itself, and for those who fumble with the GNU / Linux distribution based on Debian and the granddaughter of Incognito OS, too.
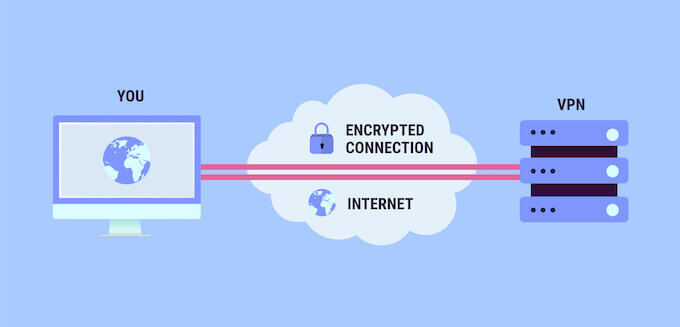
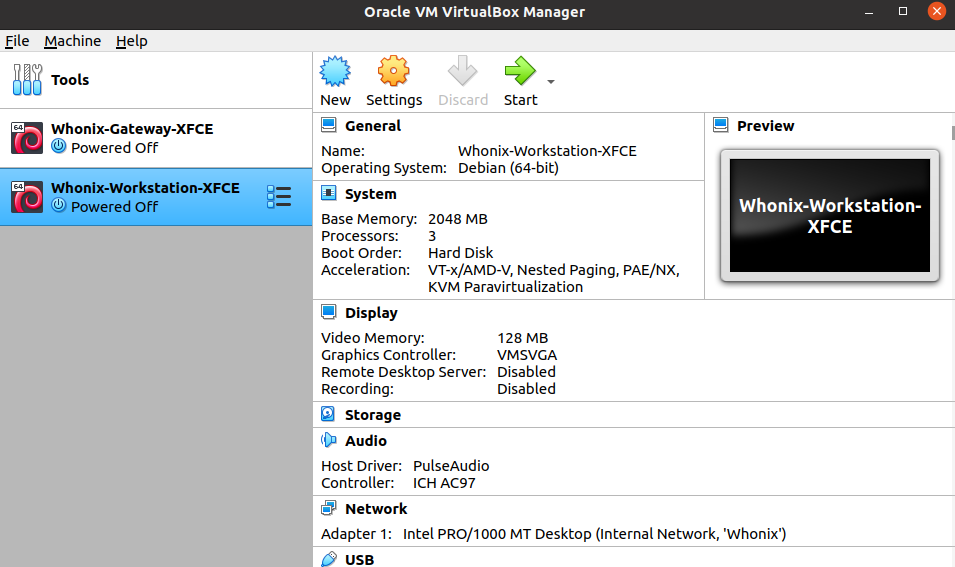
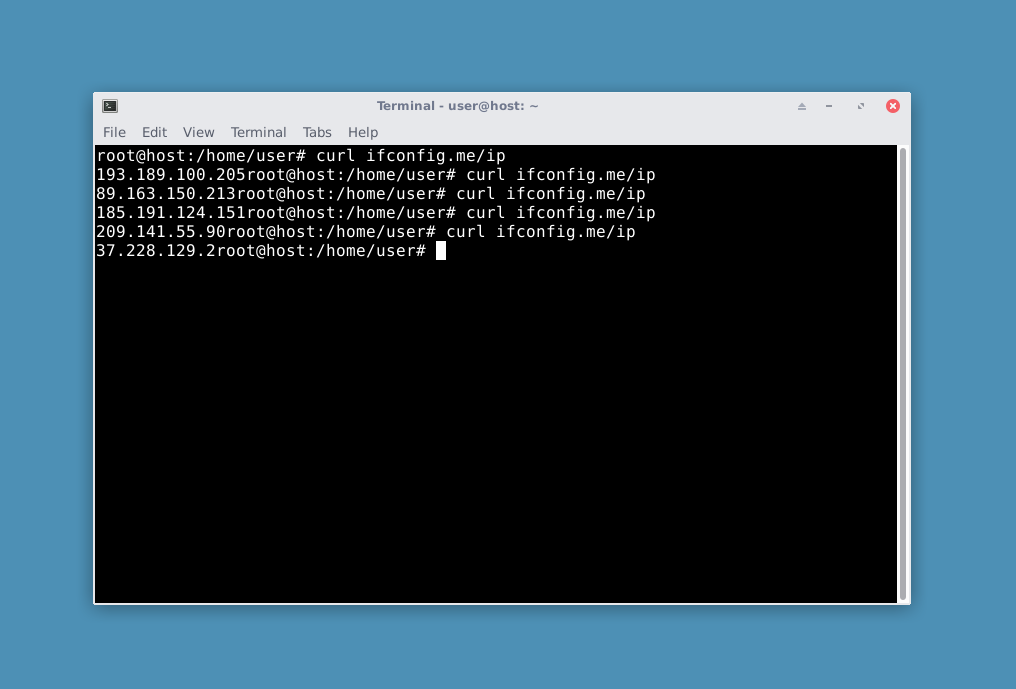
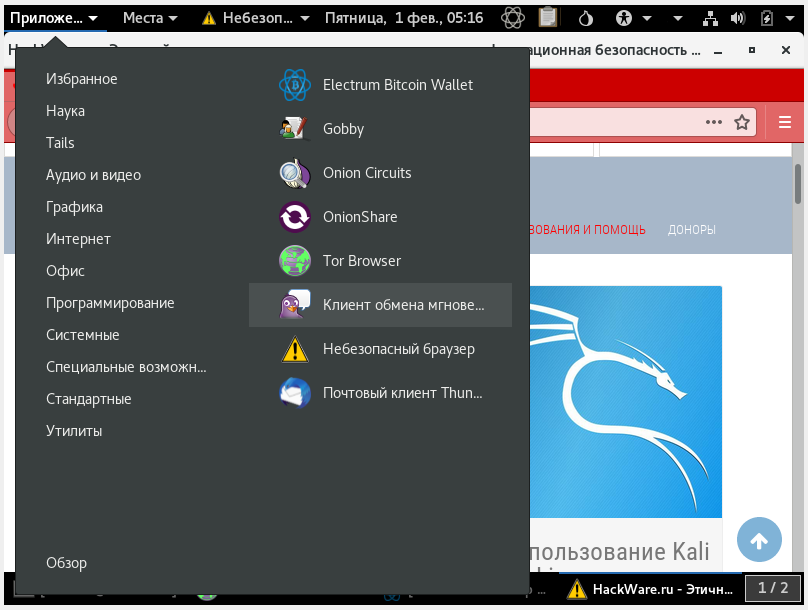
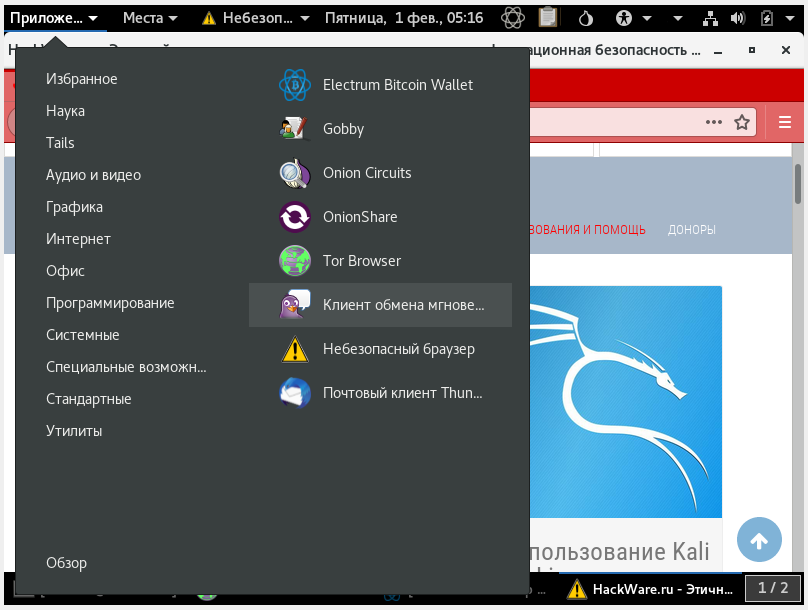
But this is all a waste of time. We are interested in what this baby can do. Let's go straight to the key features. When launched from a flash drive, Tails works exclusively in RAM, which means it leaves no traces of its activities. That is, as soon as you shut down the computer, or pulled out the USB flash drive, all OS files disappear from the RAM, which opens up a whole field of new spy capabilities. Further, the OS automatically replaces the Mac-address of the device + the entire Internet connection is via TOR. As for the secondary, in Tails, of course, the most necessary hacker utilities are preinstalled, such as Internet traffic analyzers for the same WiFi hack. Well, and where without the basic functions. It has its own cut-down photo / video editors, Chinese paints, fake Word, and more. In short, everything you need for normal work is available.
How to install?
First you need to get at least an 8 GB flash drive. Then you will need a program to transfer the OS image to a USB flash drive, for example Etcher. Then we import the whole thing into the desired PC and install it. Then there is nothing complicated, MAC settings, password setting and so on. The most important thing to remember is the Persistent Volume setting. This is the function of saving any files, since after each shutdown, the entire history of the OS is reset. I will not sign about it, you will find guides on the Internet. Just pay attention to it.
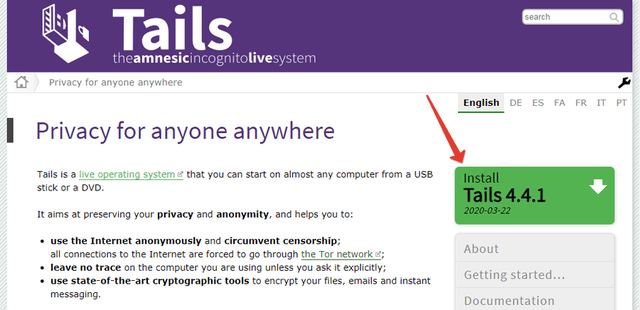
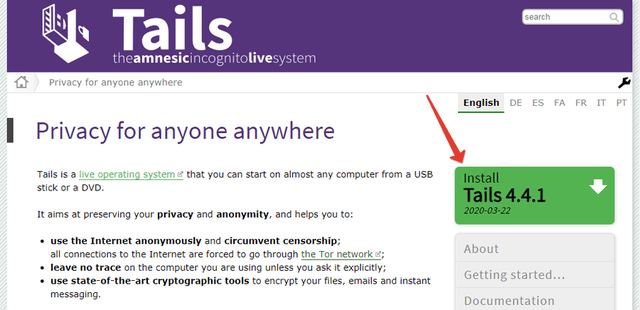
Download the OS itself here:
https://tails.boum.org/

Outcome
So, we give a verdict to our tailed friend. The thing is cool and even despite its age, relevant, as it is regularly updated. This OS is undoubtedly one of the most secure in terms of information confidentiality, but nuances can arise with anonymity.
2009 saw a modest revolution in the OS world. You probably haven't heard of it, but the guys from that same Tor Project released their own operating system, codenamed TAILS (The Amnesic Incognito Live System). She gained her fame mainly thanks to Edward Snowden, who was her active user at the time of the NSA data leak. Today we will analyze what is cool about it and why it is generally needed.

Tails is not a classic OS. The most important thing you need to know is that "tails" are launched directly from the USB stick. As for me, this is very cool and I immediately remember the scenes of hacking over computers from some Hollywood blockbusters. As for the base, this is Linux itself, and for those who fumble with the GNU / Linux distribution based on Debian and the granddaughter of Incognito OS, too.
But this is all a waste of time. We are interested in what this baby can do. Let's go straight to the key features. When launched from a flash drive, Tails works exclusively in RAM, which means it leaves no traces of its activities. That is, as soon as you shut down the computer, or pulled out the USB flash drive, all OS files disappear from the RAM, which opens up a whole field of new spy capabilities. Further, the OS automatically replaces the Mac-address of the device + the entire Internet connection is via TOR. As for the secondary, in Tails, of course, the most necessary hacker utilities are preinstalled, such as Internet traffic analyzers for the same WiFi hack. Well, and where without the basic functions. It has its own cut-down photo / video editors, Chinese paints, fake Word, and more. In short, everything you need for normal work is available.
How to install?
First you need to get at least an 8 GB flash drive. Then you will need a program to transfer the OS image to a USB flash drive, for example Etcher. Then we import the whole thing into the desired PC and install it. Then there is nothing complicated, MAC settings, password setting and so on. The most important thing to remember is the Persistent Volume setting. This is the function of saving any files, since after each shutdown, the entire history of the OS is reset. I will not sign about it, you will find guides on the Internet. Just pay attention to it.
Download the OS itself here:
https://tails.boum.org/

Outcome
So, we give a verdict to our tailed friend. The thing is cool and even despite its age, relevant, as it is regularly updated. This OS is undoubtedly one of the most secure in terms of information confidentiality, but nuances can arise with anonymity.