Carding 4 Carders
Professional
- Messages
- 2,724
- Reaction score
- 1,598
- Points
- 113
The LinkedIn tool has once again become an unwitting accomplice of hackers.
Hackers have once again started abusing the Smart Links feature of the LinkedIn service by sending phishing emails. Their goal is to steal credentials from Microsoft accounts.
Smart Links is a paid tool that allows you to create unique email addresses to track traffic statistics and audience engagement. This provides marketers with valuable insights to analyze the effectiveness of their campaigns.
Since the links use the LinkedIn domain and a unique 8-character code, they seem legitimate and easily bypass the protection of email services.
This isn't the first time the feature has been abused. At the end of 2022, Cofense discovered a similar campaign aimed at users from Slovakia.
Experts identified more than 800 emails on various topics with links to phishing pages.
According to Cofense , the attacks lasted from July to August 2023. Hackers used 80 links generated from hacked or newly created LinkedIn business accounts.
The main targets were the financial sector, manufacturing, energy, construction and healthcare. The message topics included payments, personnel, documents, and notifications from security systems. The link led the user through a chain of redirects from a "trusted" domain.
To create the illusion of reliability, the victim's email address was inserted into the phishing link in advance. On the fake Microsoft account login page, this address was already specified in the email field, and the person only had to enter the password.
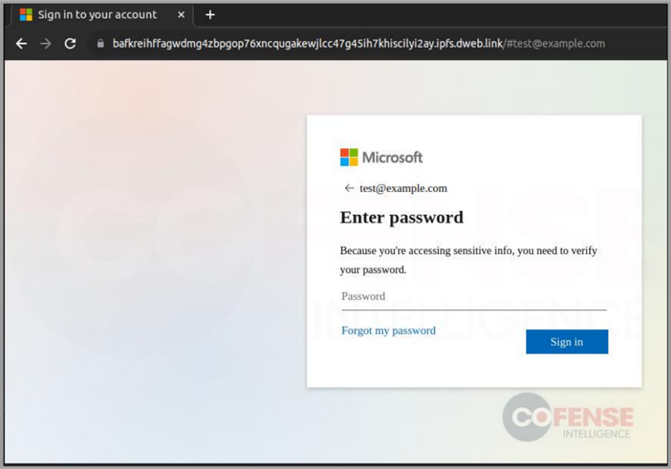
The page resembled standard authorization in Microsoft, without the company's corporate design. This expanded the range of goals, but it could alert experienced employees. At the same time, it was apparently important for hackers to collect as many credentials as possible — they did not target specific organizations.
Users should understand that email filters do not guarantee protection against phishing. Attackers continue to use legitimate services to circumvent them.
Hackers have once again started abusing the Smart Links feature of the LinkedIn service by sending phishing emails. Their goal is to steal credentials from Microsoft accounts.
Smart Links is a paid tool that allows you to create unique email addresses to track traffic statistics and audience engagement. This provides marketers with valuable insights to analyze the effectiveness of their campaigns.
Since the links use the LinkedIn domain and a unique 8-character code, they seem legitimate and easily bypass the protection of email services.
This isn't the first time the feature has been abused. At the end of 2022, Cofense discovered a similar campaign aimed at users from Slovakia.
Experts identified more than 800 emails on various topics with links to phishing pages.
According to Cofense , the attacks lasted from July to August 2023. Hackers used 80 links generated from hacked or newly created LinkedIn business accounts.
The main targets were the financial sector, manufacturing, energy, construction and healthcare. The message topics included payments, personnel, documents, and notifications from security systems. The link led the user through a chain of redirects from a "trusted" domain.
To create the illusion of reliability, the victim's email address was inserted into the phishing link in advance. On the fake Microsoft account login page, this address was already specified in the email field, and the person only had to enter the password.
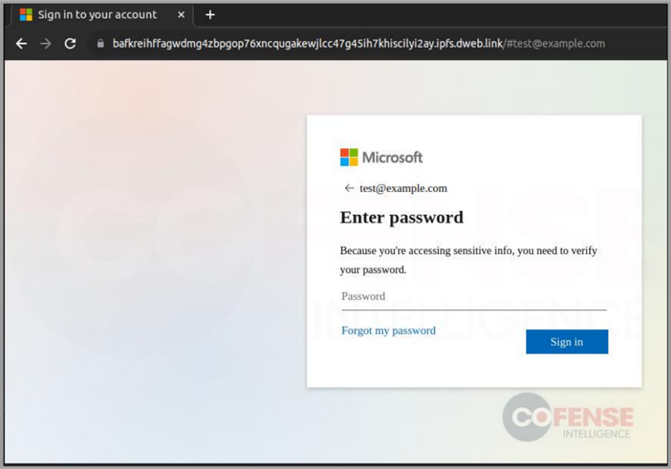
The page resembled standard authorization in Microsoft, without the company's corporate design. This expanded the range of goals, but it could alert experienced employees. At the same time, it was apparently important for hackers to collect as many credentials as possible — they did not target specific organizations.
Users should understand that email filters do not guarantee protection against phishing. Attackers continue to use legitimate services to circumvent them.
