Mutt
Professional
- Messages
- 1,458
- Reaction score
- 1,299
- Points
- 113
You can spy on your phone using a SIM card. Here's how and why.
Several years ago, we talked about how a user can be tracked over cellular networks, even if he prefers a push-button phone to a smartphone. For this method to work, the attacker needs a carrier license and special equipment.
AdaptiveMobile Security has recently discovered attacks on mobile phones that can be carried out using a regular computer and a penny USB modem. The campaign was named Simjacker: spies took advantage of a vulnerability in ... SIM cards. We will tell you what kind of vulnerability it is and how it is dangerous.
It's all about the S @ T Browser
Most modern SIM cards issued since the early 2000s, including eSIMs, have an operator menu. It can be found in the menu of a push-button phone or among applications on a smartphone, where it is called, for example, "SIM-card tools", SIM-Media or MegafonPRO and is indicated by an icon in the form of a chip. It usually consists of several items, such as "Balance", "Technical support", "Weather" or "Horoscope". This menu allows you to request the account balance, change the tariff, connect various services, and so on.
This menu is essentially an application, more precisely, several applications under the general name STK (SIM Toolkit). Only these programs work not on the phone itself, but on the SIM card, although they are displayed among the programs of the device. Yes, your SIM card is a very, very small computer, with its own operating system and programs. STK reacts to commands from the outside, for example, to pressing buttons in the operator menu, and forces the phone to perform certain actions - for example, send SMS messages or USSD commands.
One of the STK applications is called S @ T Browser. It is designed to view web pages of a certain format and sites located in the operator's internal network. For example, using the S @ T Browser, you can get information about the account balance.
This application has not been updated since 2009: other programs perform its functions on modern devices. However, the S @ T Browser is still heavily used. Researchers do not name the specific regions and mobile operators selling SIM cards on which this application is installed, but they say that it is in use in at least 30 countries, whose total population exceeds a billion people. A vulnerability was discovered in S @ T Browser: it can be used to hack a SIM card and convince it to execute the commands received in SMS without notifying the user about it.
How the Simjacker attack works
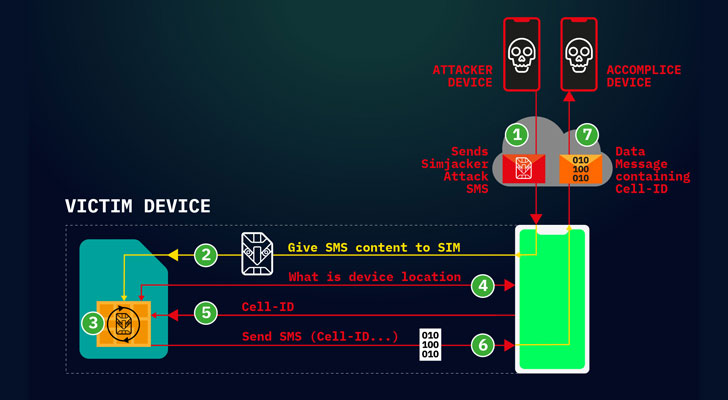
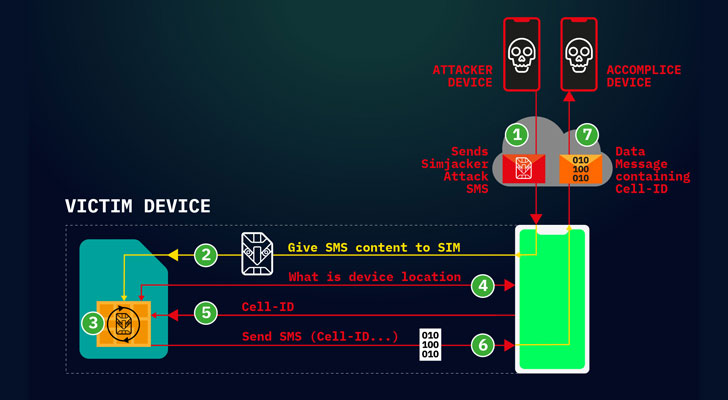
The attack begins with an SMS containing a set of instructions for a SIM card. Following these instructions, it asks the mobile phone for its serial number and the base station identifier (Cell ID), in the coverage area of which the subscriber is located, and then sends an SMS with this information to the attacker's number.
In the future, he can determine the location of the subscriber by Cell ID with a relatively small error of several hundred meters: the coordinates of the base stations are available on the Internet. They, in particular, rely on location services without satellites, for example indoors or with GPS turned off.
All manipulations with the hacked SIM card occur unnoticed by the user: messages with commands and data about the device's location are not displayed either in the "Inbox" or in the "Sent" SMS. So the victims of the Simjacker attacks most likely don't even know that they are being watched.
Who was affected by the Simjacker attacks
According to AdaptiveMobile Security, spies track the location of citizens of several countries. At the same time, in one of them, 100–150 numbers “break through” every day. Requests are sent to almost half of the phones no more than once a week, but there are some victims whose movements are being monitored quite closely - experts have noticed that several hundred malicious SMS are sent to some recipients per week.
Other potential attacks like Simjacker
The researchers note that the attackers did not use all the features of SIM cards with S @ T Browser. So, using SMS with commands, you can make the phone ring and send messages with free text to arbitrary numbers, open links in the browser and even disable the SIM card, leaving the victim without communication.
There are a lot of potential attack scenarios using the vulnerability: criminals can transfer money via SMS to a bank number, call paid short numbers, open phishing pages in a browser, or download Trojans.
The main danger of the vulnerability is that it does not depend on the device in which the SIM card is inserted: the STK command set is standardized and supported by any phone and even IoT devices with a SIM. Some gadgets for a number of operations, such as making a call, ask the user for confirmation, but many do not.
Can you defend against a Simjacker attack?
Unfortunately, the user cannot defend himself against an attack on a SIM card on his own. Mobile operators should take care of the safety of their customers. In particular, they should stop using outdated applications for the SIM-menu, as well as block SMS messages containing a set of commands.
There is, however, good news: although the attack does not require expensive equipment, it requires a fairly deep knowledge of the technique and special skills to carry it out. This means that this method will be the lot of a few advanced crackers.
In addition, the researchers reported the vulnerability to the S @ T Browser developer SIMalliance. In response, it has issued safety advisories for operators using the app. Simjacker and the GSM Association, an international organization representing the interests of mobile operators, were notified of the attacks. So one can hope that in the near future the companies will take the necessary measures to protect subscribers.
Simjacker attack has been used to spy on SIM card holders for two years
AdaptiveMobile Security researchers have described a Simjacker attack that uses SMS messages to send SIM Toolkit (STK) and S @ T Browser instructions to a SIM card.
Experts warned that this attack is not just a concept and has been regularly used in reality over the past two years. “We are confident that this exploit was developed by a specific private company that works with governments to monitor individuals,” the experts write.
AdaptiveMobile does not disclose the name of the company carrying out these attacks, and therefore it is unclear whether the problem is being used to spy on criminals or terrorists, or whether it is being used to track dissidents, activists and journalists.
According to the researchers, the same unnamed company has expanded access to the SS7 and Diameter core network, and the targets of Simjacker attacks are often victims of attacks through SS7. Apparently, SS7 attacks are a less preferable and fallback option in case Simjacker doesn't work. The fact is that recently, operators have been devoting much more time and effort to protecting their SS7 and Diameter infrastructures, while Simjacker's attacks are cheap and easy to execute.
The essence of the attack is that using a smartphone or a simple GSM modem, the attacker sends a special SMS message to the victim's device containing hidden instructions for the SIM Toolkit. These instructions are supported by the S @ T Browser application running on the device's SIM card.
STK and S @ T Browser are old technologies supported by many mobile networks and SIM cards. They can be used to perform various actions on the device, such as launching a browser, playing a sound, or showing pop-up windows. In the past, mobile operators have often used this to send advertisements or billing information to users.
The Simjacker attack implies that the attacker abuses this mechanism and orders the victim's device to transmit location data and IMEI, which the SIM card will send in an SMS message to a third-party device, and the attacker will eventually be able to find out the location of his target. At the same time, users affected by the attack do not see any SMS messages or other traces of compromise. That is, attackers can constantly inundate their victims with SMS-messages and thus track their location constantly, for weeks or even months. Since the Simjacker attack targets the SIM card, it is platform and device independent.
According to the Vice Motherboard, operators Sprint and T-Mobile said their users were not harmed, and AT&T officials say their American network is immune to such attacks.
Worse, other commands supported by S @ T Browser include the ability to make calls, send messages, disable the SIM card, run AT modem commands, open browsers (with phishing links or open malicious sites), and much more. That is, using Simjacker attacks, you can not only track users, but also carry out financial fraud (calls to premium numbers), espionage (make a call and listen to conversations near the device), sabotage (disable the victim's SIM card), organize misleading campaigns (sending SMS / MMS with fake content) and so on.
It should be noted that Simjacker attacks are not such a new phenomenon. For example, the abuse of STK instructions at a theoretical level was described back in 2011 by information security specialist Bogdan Aleku. Then the expert warned that this can be used to send SMS to premium rates, or create difficulties when receiving regular text messages. Also, a similar attack was demonstrated in 2013 at the BlackHat conference.
Several years ago, we talked about how a user can be tracked over cellular networks, even if he prefers a push-button phone to a smartphone. For this method to work, the attacker needs a carrier license and special equipment.
AdaptiveMobile Security has recently discovered attacks on mobile phones that can be carried out using a regular computer and a penny USB modem. The campaign was named Simjacker: spies took advantage of a vulnerability in ... SIM cards. We will tell you what kind of vulnerability it is and how it is dangerous.
It's all about the S @ T Browser
Most modern SIM cards issued since the early 2000s, including eSIMs, have an operator menu. It can be found in the menu of a push-button phone or among applications on a smartphone, where it is called, for example, "SIM-card tools", SIM-Media or MegafonPRO and is indicated by an icon in the form of a chip. It usually consists of several items, such as "Balance", "Technical support", "Weather" or "Horoscope". This menu allows you to request the account balance, change the tariff, connect various services, and so on.
This menu is essentially an application, more precisely, several applications under the general name STK (SIM Toolkit). Only these programs work not on the phone itself, but on the SIM card, although they are displayed among the programs of the device. Yes, your SIM card is a very, very small computer, with its own operating system and programs. STK reacts to commands from the outside, for example, to pressing buttons in the operator menu, and forces the phone to perform certain actions - for example, send SMS messages or USSD commands.
One of the STK applications is called S @ T Browser. It is designed to view web pages of a certain format and sites located in the operator's internal network. For example, using the S @ T Browser, you can get information about the account balance.
This application has not been updated since 2009: other programs perform its functions on modern devices. However, the S @ T Browser is still heavily used. Researchers do not name the specific regions and mobile operators selling SIM cards on which this application is installed, but they say that it is in use in at least 30 countries, whose total population exceeds a billion people. A vulnerability was discovered in S @ T Browser: it can be used to hack a SIM card and convince it to execute the commands received in SMS without notifying the user about it.
How the Simjacker attack works
The attack begins with an SMS containing a set of instructions for a SIM card. Following these instructions, it asks the mobile phone for its serial number and the base station identifier (Cell ID), in the coverage area of which the subscriber is located, and then sends an SMS with this information to the attacker's number.
In the future, he can determine the location of the subscriber by Cell ID with a relatively small error of several hundred meters: the coordinates of the base stations are available on the Internet. They, in particular, rely on location services without satellites, for example indoors or with GPS turned off.
All manipulations with the hacked SIM card occur unnoticed by the user: messages with commands and data about the device's location are not displayed either in the "Inbox" or in the "Sent" SMS. So the victims of the Simjacker attacks most likely don't even know that they are being watched.
Who was affected by the Simjacker attacks
According to AdaptiveMobile Security, spies track the location of citizens of several countries. At the same time, in one of them, 100–150 numbers “break through” every day. Requests are sent to almost half of the phones no more than once a week, but there are some victims whose movements are being monitored quite closely - experts have noticed that several hundred malicious SMS are sent to some recipients per week.
Other potential attacks like Simjacker
The researchers note that the attackers did not use all the features of SIM cards with S @ T Browser. So, using SMS with commands, you can make the phone ring and send messages with free text to arbitrary numbers, open links in the browser and even disable the SIM card, leaving the victim without communication.
There are a lot of potential attack scenarios using the vulnerability: criminals can transfer money via SMS to a bank number, call paid short numbers, open phishing pages in a browser, or download Trojans.
The main danger of the vulnerability is that it does not depend on the device in which the SIM card is inserted: the STK command set is standardized and supported by any phone and even IoT devices with a SIM. Some gadgets for a number of operations, such as making a call, ask the user for confirmation, but many do not.
Can you defend against a Simjacker attack?
Unfortunately, the user cannot defend himself against an attack on a SIM card on his own. Mobile operators should take care of the safety of their customers. In particular, they should stop using outdated applications for the SIM-menu, as well as block SMS messages containing a set of commands.
There is, however, good news: although the attack does not require expensive equipment, it requires a fairly deep knowledge of the technique and special skills to carry it out. This means that this method will be the lot of a few advanced crackers.
In addition, the researchers reported the vulnerability to the S @ T Browser developer SIMalliance. In response, it has issued safety advisories for operators using the app. Simjacker and the GSM Association, an international organization representing the interests of mobile operators, were notified of the attacks. So one can hope that in the near future the companies will take the necessary measures to protect subscribers.
Simjacker attack has been used to spy on SIM card holders for two years
AdaptiveMobile Security researchers have described a Simjacker attack that uses SMS messages to send SIM Toolkit (STK) and S @ T Browser instructions to a SIM card.
Experts warned that this attack is not just a concept and has been regularly used in reality over the past two years. “We are confident that this exploit was developed by a specific private company that works with governments to monitor individuals,” the experts write.
AdaptiveMobile does not disclose the name of the company carrying out these attacks, and therefore it is unclear whether the problem is being used to spy on criminals or terrorists, or whether it is being used to track dissidents, activists and journalists.
According to the researchers, the same unnamed company has expanded access to the SS7 and Diameter core network, and the targets of Simjacker attacks are often victims of attacks through SS7. Apparently, SS7 attacks are a less preferable and fallback option in case Simjacker doesn't work. The fact is that recently, operators have been devoting much more time and effort to protecting their SS7 and Diameter infrastructures, while Simjacker's attacks are cheap and easy to execute.
The essence of the attack is that using a smartphone or a simple GSM modem, the attacker sends a special SMS message to the victim's device containing hidden instructions for the SIM Toolkit. These instructions are supported by the S @ T Browser application running on the device's SIM card.
STK and S @ T Browser are old technologies supported by many mobile networks and SIM cards. They can be used to perform various actions on the device, such as launching a browser, playing a sound, or showing pop-up windows. In the past, mobile operators have often used this to send advertisements or billing information to users.
The Simjacker attack implies that the attacker abuses this mechanism and orders the victim's device to transmit location data and IMEI, which the SIM card will send in an SMS message to a third-party device, and the attacker will eventually be able to find out the location of his target. At the same time, users affected by the attack do not see any SMS messages or other traces of compromise. That is, attackers can constantly inundate their victims with SMS-messages and thus track their location constantly, for weeks or even months. Since the Simjacker attack targets the SIM card, it is platform and device independent.
AdaptiveMobile experts note that Simjacker attacks occur daily in large numbers. Most often, phone numbers are tracked several times a day, over a long period of time.“We have noticed that devices from almost all manufacturers successfully allow us to find out the user's location data: Apple, ZTE, Motorola, Samsung, Google, Huawei and even IoT devices with SIM cards,” the researchers write.
Analysts also point out that Simjacker attacks can be easily prevented if operators pay attention to which code works on their SIM-cards. The fact is that the S @ T Browser specification has not been updated since 2009, and the original functionality, such as obtaining information about the account balance via a SIM card, has long been outdated, and other technologies have replaced it. However, the outdated S @ T Browser is still in use and is present on SIM cards of mobile operators in at least 30 countries around the world. Together, these countries are home to more than one billion people, and all of them are at risk of undetected surveillance by Simjacker."The patterns and number of tracking devices indicate that this is not a massive mass tracking operation, but an operation to track large numbers of people for various purposes, with the goals and priorities of operators changing over time," experts say.
According to the Vice Motherboard, operators Sprint and T-Mobile said their users were not harmed, and AT&T officials say their American network is immune to such attacks.
Worse, other commands supported by S @ T Browser include the ability to make calls, send messages, disable the SIM card, run AT modem commands, open browsers (with phishing links or open malicious sites), and much more. That is, using Simjacker attacks, you can not only track users, but also carry out financial fraud (calls to premium numbers), espionage (make a call and listen to conversations near the device), sabotage (disable the victim's SIM card), organize misleading campaigns (sending SMS / MMS with fake content) and so on.
It should be noted that Simjacker attacks are not such a new phenomenon. For example, the abuse of STK instructions at a theoretical level was described back in 2011 by information security specialist Bogdan Aleku. Then the expert warned that this can be used to send SMS to premium rates, or create difficulties when receiving regular text messages. Also, a similar attack was demonstrated in 2013 at the BlackHat conference.
