Carding
Professional
- Messages
- 2,870
- Reaction score
- 2,522
- Points
- 113
4,000 popular packages were vulnerable to RepoJacking attacks for six months.
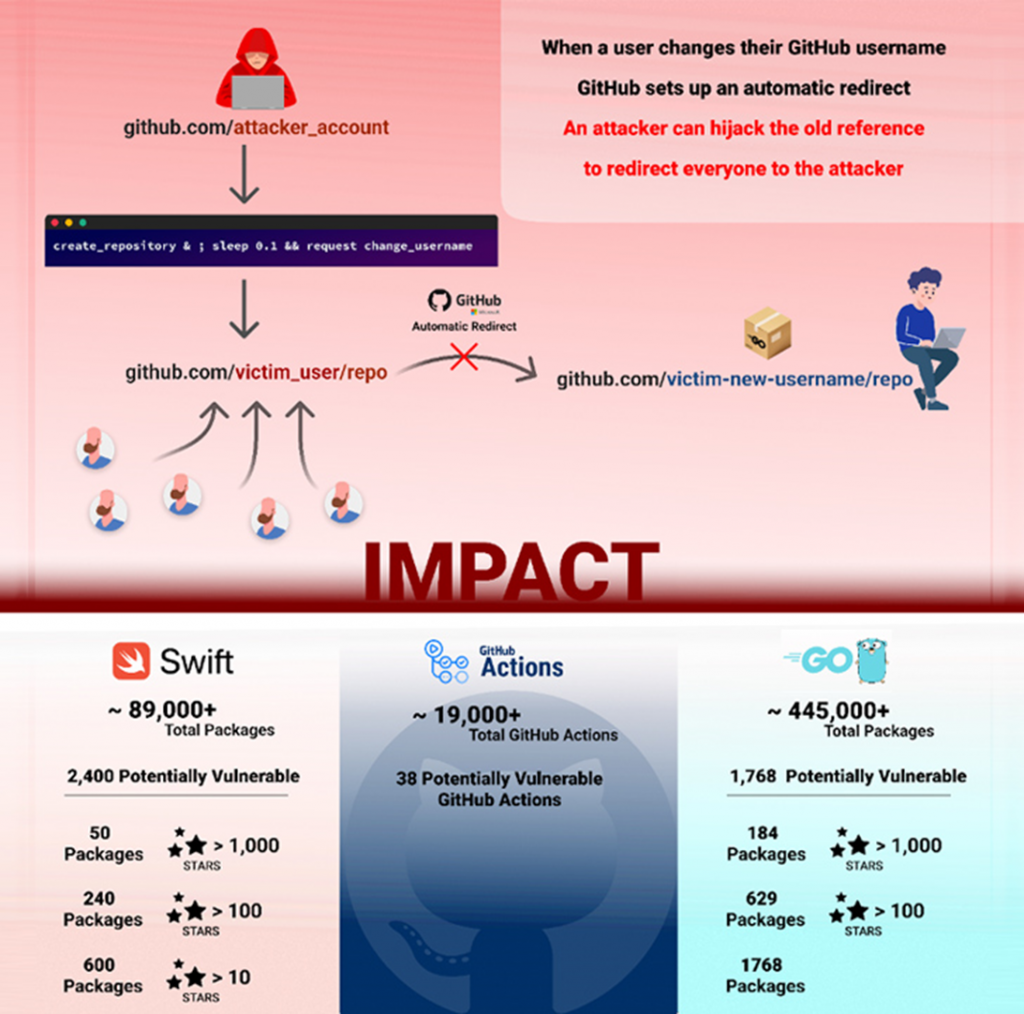
A new vulnerability has been discovered GitHub platform that could put thousands of repositories at risk. The vulnerability allows attackers to exploit the so-called "Race Condition" in the process of creating a repository and changing the user name.
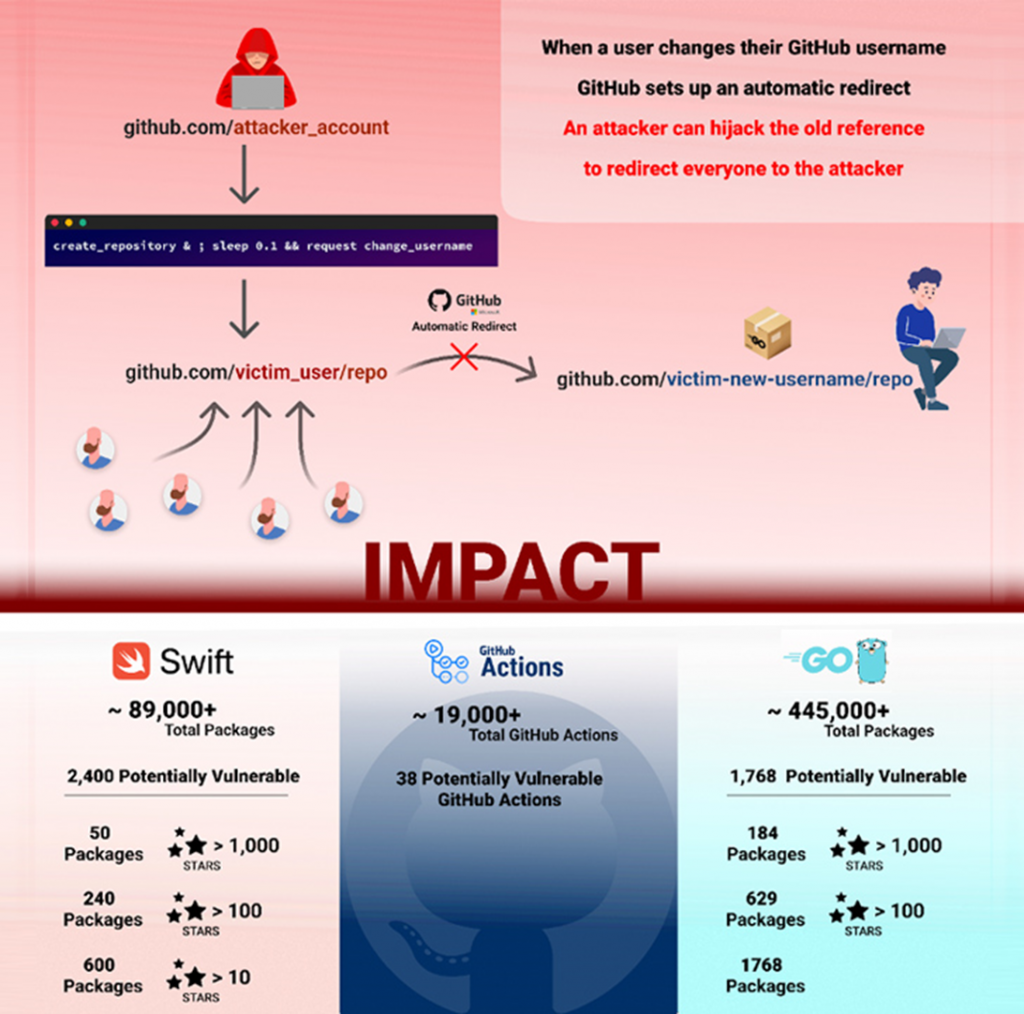
Elad Rapoport, a security researcher at Checkmarx, stated the following: "The successful exploitation of this vulnerability affects open source software, allowing you to capture more than 4,000 code packages in the Go, PHP, and Swift languages, as well as GitHub Actions."
After the responsible disclosure of the vulnerability on March 1, 2023, the Microsoft-controlled code hosting platform fixed the problem on September 1, 2023, so now GitHub users are not in any danger.
The term "RepoJacking" describes a technique in which a potential attacker can bypass the security mechanism of the hosting platform and gain control of the desired repository.
In the case of the described GitHub vulnerability, attackers could create redirects to their malicious repositories using legitimate but outdated namespaces. This method could potentially lead to attacks on the software supply chain.
Scheme and potential damage of the attack
The existing protection introduced by the service back in 2018 prevents the creation of a new repository with the same name, if the repository already has more than 100 clones at the time of renaming the user's account. However, as it turned out, this defense mechanism could be circumvented due to the vulnerability described above.
It is noteworthy that at the end of last year, GitHub representatives already fixed a similar vulnerability , which could also lead to "RepoJacking"attacks.
In general, experts believe that the mechanism of renaming repositories involves a whole lot of risks and, who knows, maybe in the future attackers will find new ways to exploit this mechanism.
A new vulnerability has been discovered GitHub platform that could put thousands of repositories at risk. The vulnerability allows attackers to exploit the so-called "Race Condition" in the process of creating a repository and changing the user name.
Elad Rapoport, a security researcher at Checkmarx, stated the following: "The successful exploitation of this vulnerability affects open source software, allowing you to capture more than 4,000 code packages in the Go, PHP, and Swift languages, as well as GitHub Actions."
After the responsible disclosure of the vulnerability on March 1, 2023, the Microsoft-controlled code hosting platform fixed the problem on September 1, 2023, so now GitHub users are not in any danger.
The term "RepoJacking" describes a technique in which a potential attacker can bypass the security mechanism of the hosting platform and gain control of the desired repository.
In the case of the described GitHub vulnerability, attackers could create redirects to their malicious repositories using legitimate but outdated namespaces. This method could potentially lead to attacks on the software supply chain.
Scheme and potential damage of the attack
The existing protection introduced by the service back in 2018 prevents the creation of a new repository with the same name, if the repository already has more than 100 clones at the time of renaming the user's account. However, as it turned out, this defense mechanism could be circumvented due to the vulnerability described above.
It is noteworthy that at the end of last year, GitHub representatives already fixed a similar vulnerability , which could also lead to "RepoJacking"attacks.
In general, experts believe that the mechanism of renaming repositories involves a whole lot of risks and, who knows, maybe in the future attackers will find new ways to exploit this mechanism.
