
Medusa RAT 2026
Medusa RAT 2026 is an advanced Android Remote Access Trojan designed to give attackers full control over infected devices. Operating as a Malware-as-a-Service (MaaS) platform, it allows cybercriminals to build malicious apps, steal sensitive data, and monitor users remotely.
Its modular structure, stealth capabilities, and ease of use make it one of the most dangerous mobile threats in today’s cybersecurity landscape.
Key Features of Medusa RAT 2026
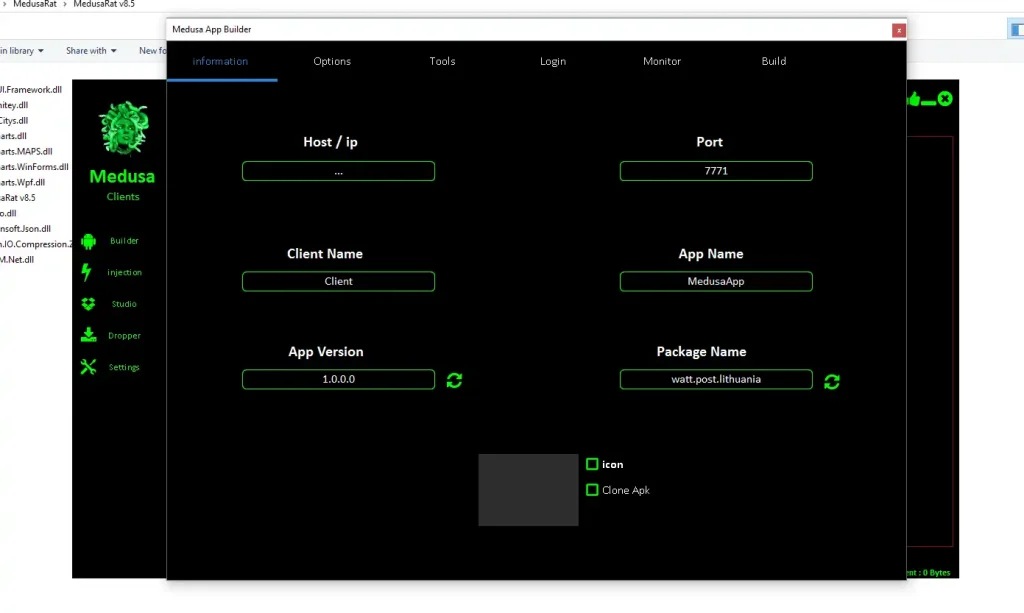
APK Builder System:
Allows attackers to generate customized malicious Android apps. They can define app behavior, permissions, and connection settings, making the malware adaptable for different attack scenarios.
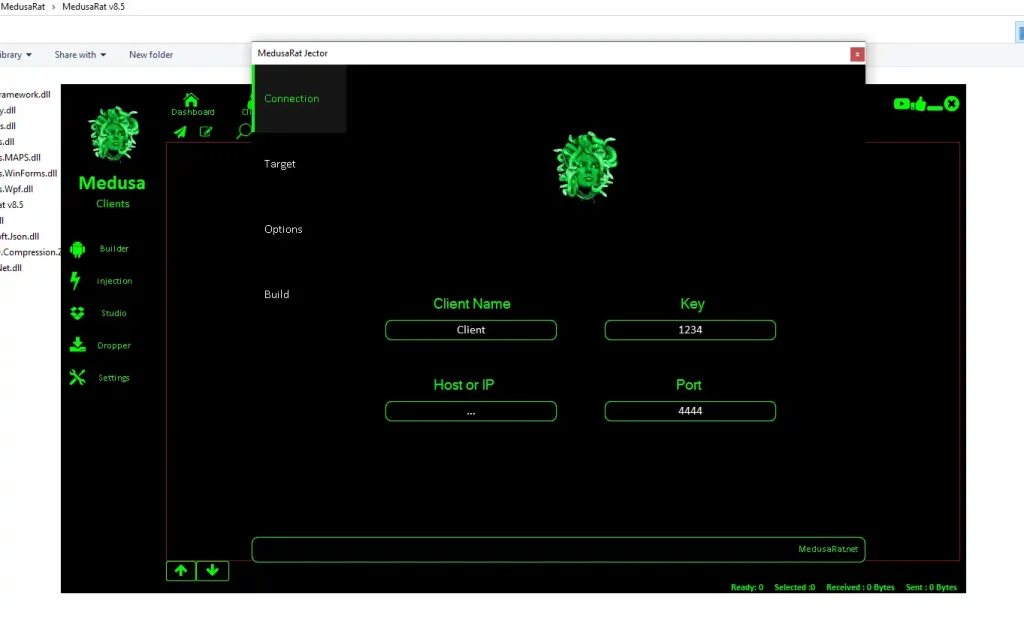
Code Injection Capability:
Enables embedding malicious payloads into legitimate apps such as banking or social media applications. This increases trust and improves infection success rates.
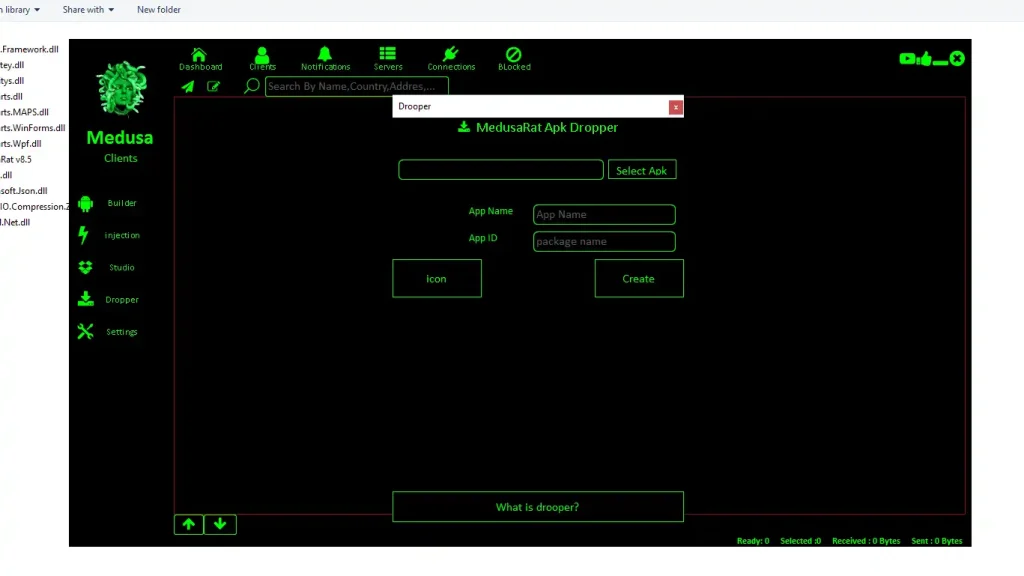
Dropper Mechanism:
Uses a lightweight app to download the full malware after installation. This helps bypass antivirus detection and security scanning tools.
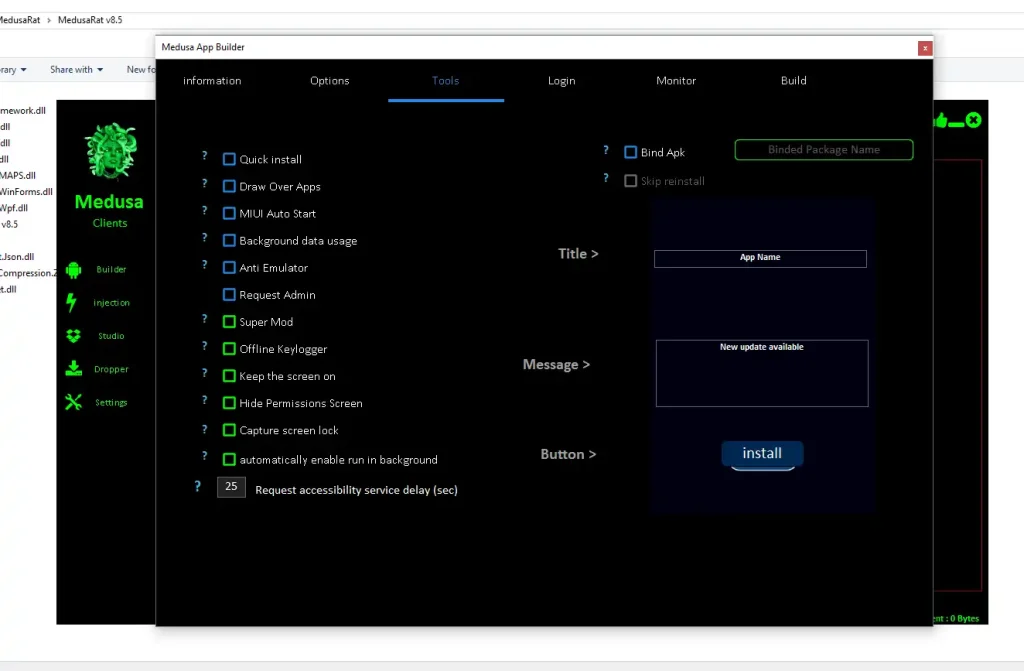
Anti-Detection Technology:
Includes anti-emulator and sandbox evasion features, ensuring the malware avoids analysis by cybersecurity tools and researchers.
Permission Abuse & Persistence:
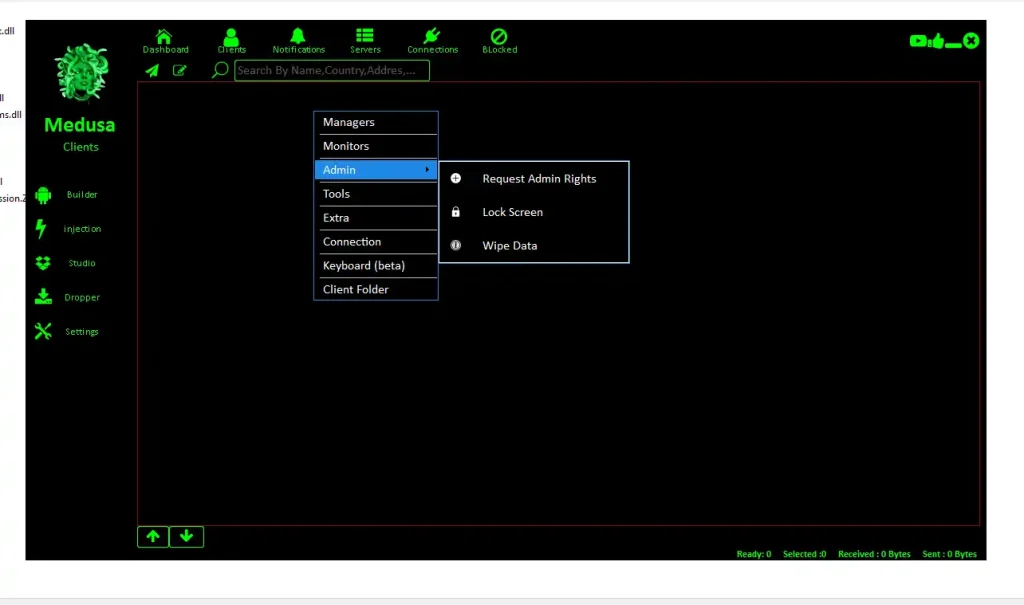
Requests device administrator access and hides permission prompts, making it difficult for users to detect or uninstall the malware.
Overlay Attack System:
Displays fake login screens over real apps to capture sensitive information like passwords and banking credentials.
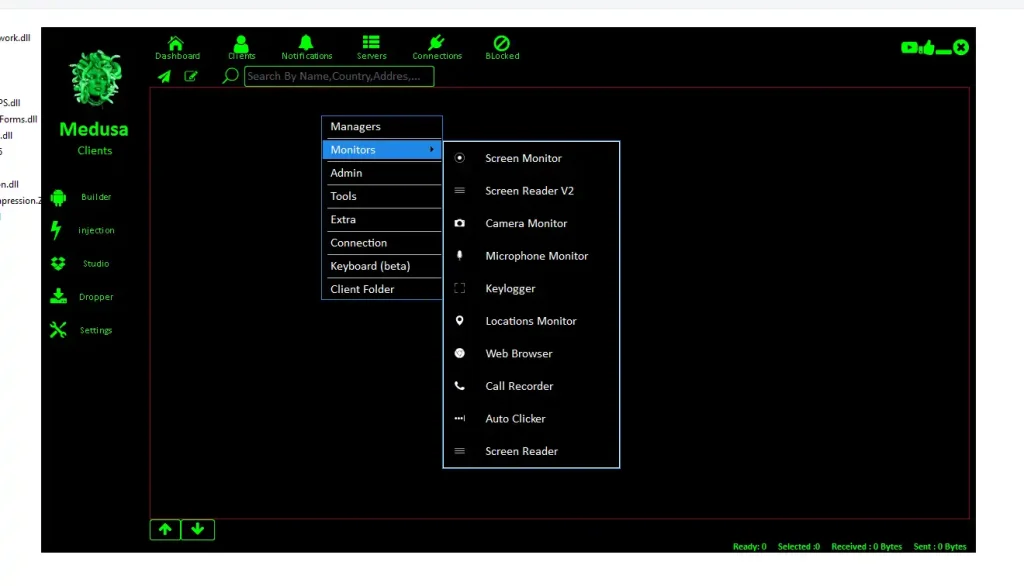
Offline Keylogger:
Records keystrokes even without internet access and uploads the data once connectivity is restored.
Surveillance Tools:
Activates microphone, records calls, and captures screen activity, turning the device into a remote spying tool.
Full File Access:
Allows attackers to manage files on the device, including downloading, uploading, or deleting data remotely.
Remote Command Execution:
Provides shell access to execute system-level commands, giving attackers deep control over the device.
MedusaRat v8.5
MediaFire is a simple to use free service that lets you put all your photos, documents, music, and video in a single place so you can access them anywhere and share them everywhere.
www.mediafire.com
