Lord777
Professional
- Messages
- 2,576
- Reaction score
- 1,565
- Points
- 113
What do Apple think about the new method of attacking a branded service?
German researchers have identified a vulnerability in Apple's Locator service that allows you to freely transfer confidential data, including passwords intercepted by keyloggers.
"Locator" is designed to help users of Apple products find lost or even planted spy devices, including iPhone, iPad, Mac, Apple Watch, AirPods and AirTag.
The possibility of abusing the Locator service to transmit arbitrary data was first discovered by researchers from Positive Security more than two years ago. Experts then even developed a tool parodically called " Send My "in response to the original name of the service"Find My". The tool allowed you to publish data on the Locator network, and then extract it from anywhere in the world. Soon, Apple fixed the vulnerability that allows its exploitation.
According to a new study by Fabian Braunlein, founder of Positive Security, experts have managed to create a proven hardware device that can compromise the Locator network via Bluetooth.
The researchers integrated a keylogger with an ESP32 Bluetooth transmitter into a USB keyboard to show that passwords and other sensitive data typed on the keyboard can be transmitted through the "Locator".
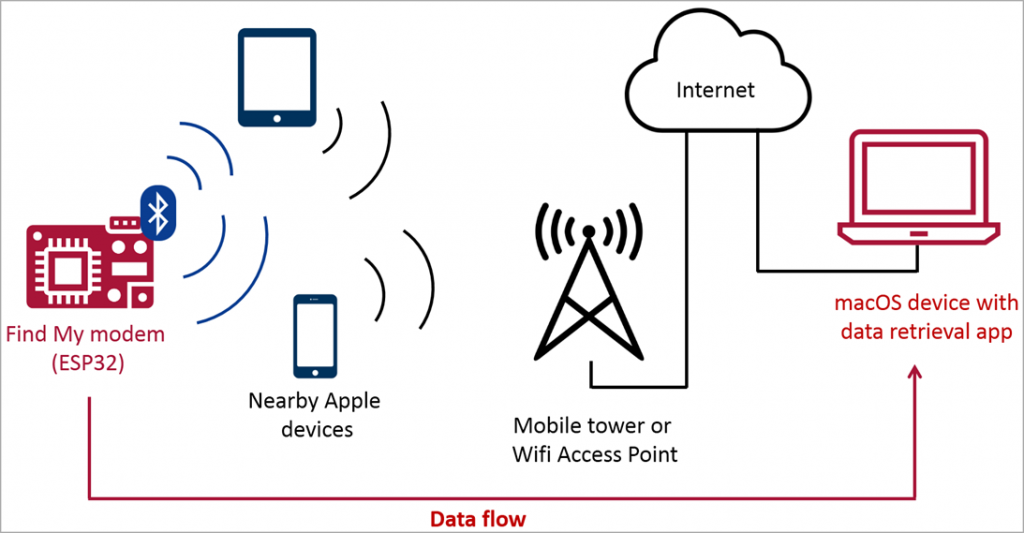
General attack pattern
The keylogger does not need to use AirTag or other officially supported chips, since Apple devices are configured to respond to any Bluetooth messages. Therefore, if the message sent by the attackers is formatted accordingly, the receiving Apple device will create a location report and upload it to the"Locator".

Unknown recordings from Apple devices
The sender needs to create a set of slightly different public encryption keys that mimic multiple AirTags, and encode arbitrary data into keys by assigning certain bits at pre-defined positions in the keys.
In this way, multiple reports received from the cloud can be combined and decoded on the receiving end to extract arbitrary data, in this case keylogger records.
Braunlein said that the total cost of a hardware device for data transmission was approximately $ 50 when using the EvilCrow keylogger with Bluetooth support and a standard USB keyboard.
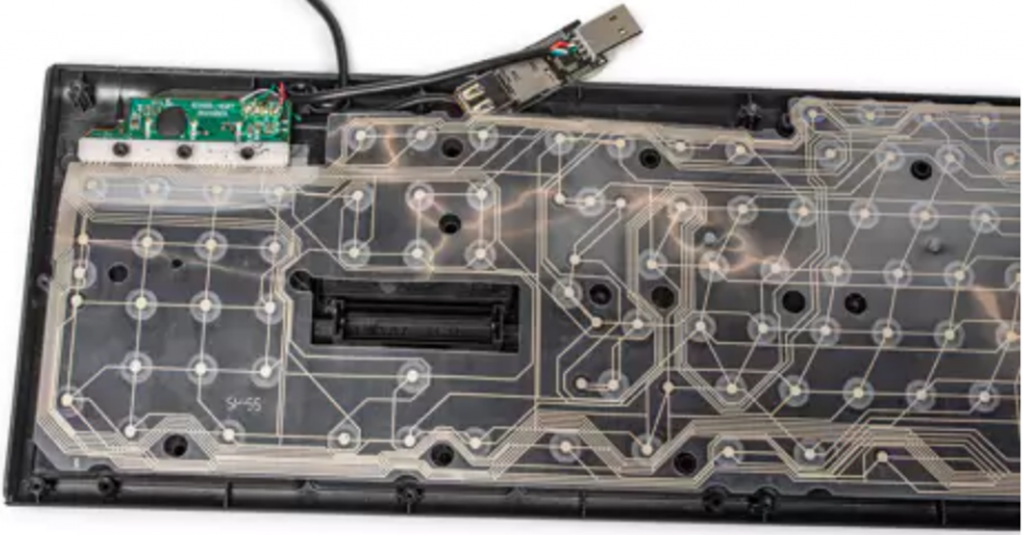
Modified keyboard used for attack
The Brownlein PoC attack reached a data transfer rate of 26 characters per second and a reception rate of 7 characters per second with a delay of from a minute to an hour, depending on whether Apple devices are in range of the keylogger.
It may not seem very fast, but if the hackers goal is to get valuable information, such as passwords, waiting for several hours or even days will not be a significant obstacle for them.
The most interesting thing is that Apple's tracking protection, which notifies users that someone is using AirTag for espionage, is not activated in this attack for some reason, so the very fact of the attack remains hidden and is unlikely to be detected at all by a potential victim.
Apple has not yet responded to the apparent vulnerability in their service. Let's hope that the company will soon release a corresponding fix that prevents unauthorized access to user data and actions.
German researchers have identified a vulnerability in Apple's Locator service that allows you to freely transfer confidential data, including passwords intercepted by keyloggers.
"Locator" is designed to help users of Apple products find lost or even planted spy devices, including iPhone, iPad, Mac, Apple Watch, AirPods and AirTag.
The possibility of abusing the Locator service to transmit arbitrary data was first discovered by researchers from Positive Security more than two years ago. Experts then even developed a tool parodically called " Send My "in response to the original name of the service"Find My". The tool allowed you to publish data on the Locator network, and then extract it from anywhere in the world. Soon, Apple fixed the vulnerability that allows its exploitation.
According to a new study by Fabian Braunlein, founder of Positive Security, experts have managed to create a proven hardware device that can compromise the Locator network via Bluetooth.
The researchers integrated a keylogger with an ESP32 Bluetooth transmitter into a USB keyboard to show that passwords and other sensitive data typed on the keyboard can be transmitted through the "Locator".
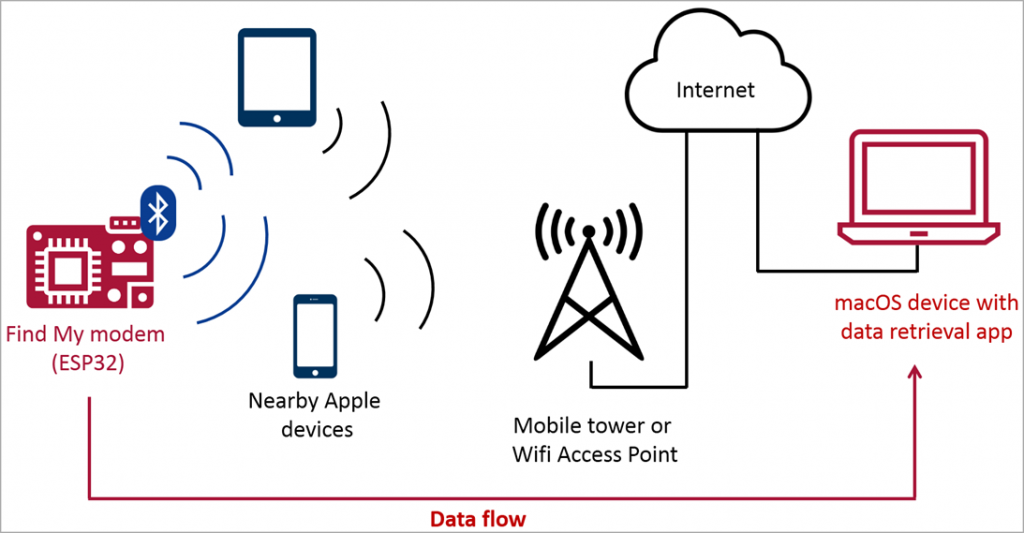
General attack pattern
The keylogger does not need to use AirTag or other officially supported chips, since Apple devices are configured to respond to any Bluetooth messages. Therefore, if the message sent by the attackers is formatted accordingly, the receiving Apple device will create a location report and upload it to the"Locator".

Unknown recordings from Apple devices
The sender needs to create a set of slightly different public encryption keys that mimic multiple AirTags, and encode arbitrary data into keys by assigning certain bits at pre-defined positions in the keys.
In this way, multiple reports received from the cloud can be combined and decoded on the receiving end to extract arbitrary data, in this case keylogger records.
Braunlein said that the total cost of a hardware device for data transmission was approximately $ 50 when using the EvilCrow keylogger with Bluetooth support and a standard USB keyboard.
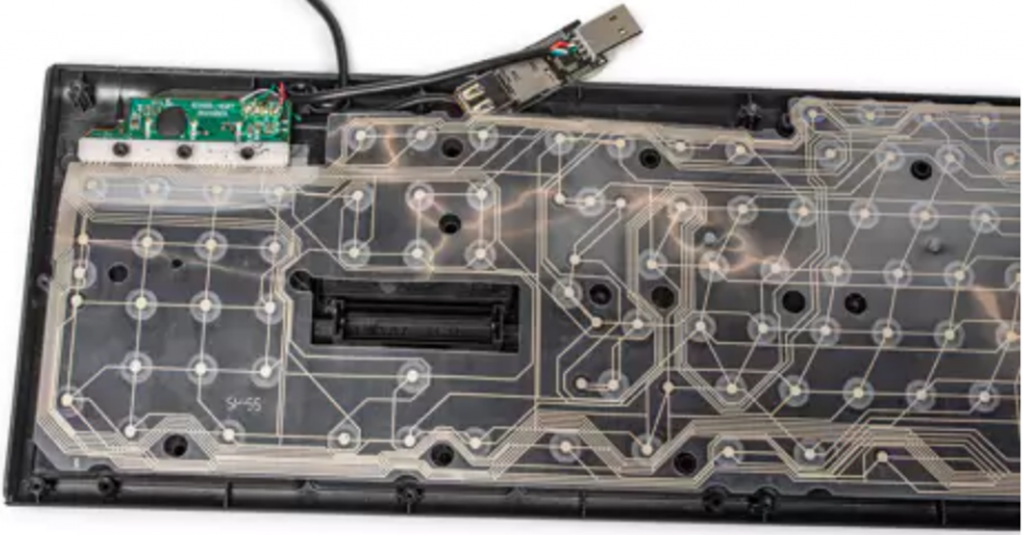
Modified keyboard used for attack
The Brownlein PoC attack reached a data transfer rate of 26 characters per second and a reception rate of 7 characters per second with a delay of from a minute to an hour, depending on whether Apple devices are in range of the keylogger.
It may not seem very fast, but if the hackers goal is to get valuable information, such as passwords, waiting for several hours or even days will not be a significant obstacle for them.
The most interesting thing is that Apple's tracking protection, which notifies users that someone is using AirTag for espionage, is not activated in this attack for some reason, so the very fact of the attack remains hidden and is unlikely to be detected at all by a potential victim.
Apple has not yet responded to the apparent vulnerability in their service. Let's hope that the company will soon release a corresponding fix that prevents unauthorized access to user data and actions.

