Brother
Professional
- Messages
- 2,590
- Reaction score
- 541
- Points
- 113
Written in C++, the Chinese malware has an extensive range of spy features.
According to a new report by Cisco Talos, a group of Chinese-speaking hackers has carried out a malicious campaign targeting the Ministry of Foreign Affairs of Uzbekistan, as well as private organizations in South Korea.
The malicious operation started approximately in August of this year and used a remote access Trojan (RAT) called SugarGh0st, a modification of the fairly well-known Gh0st RAT.
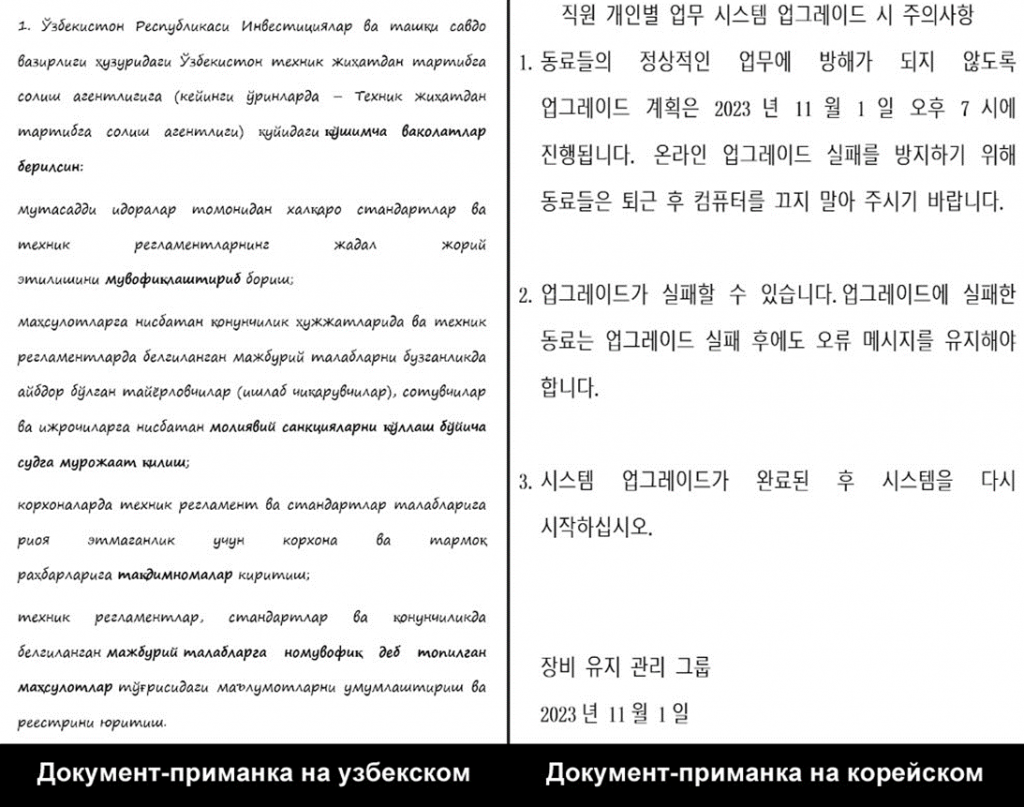
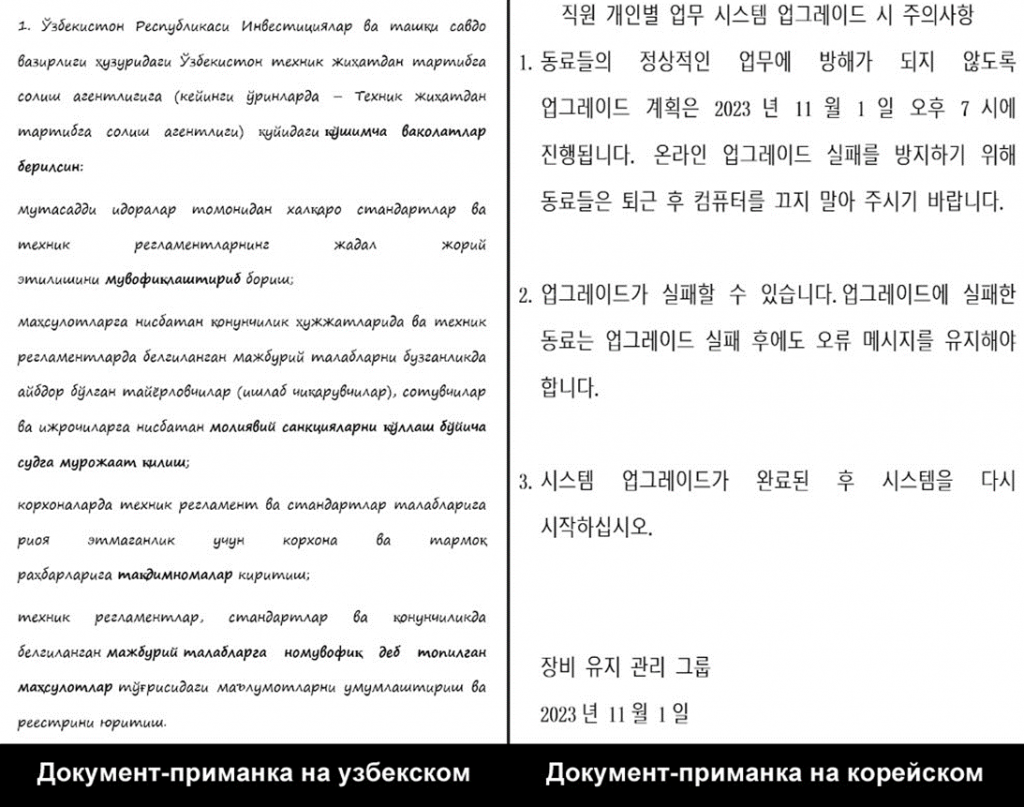
Talos specialists found four samples used in this campaign, targeting users in Uzbekistan and South Korea, based on the language of bait documents, bait content, and distribution indicators.
One of the identified samples was sent to the Ministry of Foreign Affairs of Uzbekistan with a decoy that allegedly duplicates the decree of the local president aimed at improving public administration in the field of technical regulation. The other three samples were distributed in South Korea and targeted small private organizations.
The attack itself began with a phishing email containing disguised documents that, when opened, trigger a multi-step process leading to the deployment of SugarGh0st RAT. The virus includes features to " facilitate remote administration and a modified communication protocol."
In the attachment to the phishing email, disguised documents are embedded in a heavily obfuscated JavaScript dropper contained in a Windows shortcut file packaged in a RAR file.
JavaScript decrypts and transfers attached files to a temporary folder, including the script, a custom DLL loader, and the encrypted SugarGh0st payload.
When a victim opens a fake document, a script runs in the background that starts the DLL loader. This loader in turn uses a copy of the legitimate Windows executable, rundll32.exe, to decrypt and launch the SugarGh0st payload.
SugarGh0st, written in C++, communicates with a hard-coded C2 domain, allowing you to pass system metadata to the server, run a reverse shell, and execute arbitrary commands. It can also list and terminate processes, take screenshots, perform file operations, and even clear the computer's event logs in an attempt to hide its tracks and avoid detection.
The campaign was linked to China due to the Chinese origin of the original Gh0st RAT and its widespread use by Chinese hackers, especially after the source code was published in 2008. Another confirmation is the use of Chinese names in the "last modified" field of metadata files detected during the attack.
In addition, it was noted that Chinese cybercriminals also have a history of targeted attacks on Uzbekistan. Over the past six months, Chinese APT groups have also increased their activity against Taiwan, using home routers to mask their intrusions.
According to a new report by Cisco Talos, a group of Chinese-speaking hackers has carried out a malicious campaign targeting the Ministry of Foreign Affairs of Uzbekistan, as well as private organizations in South Korea.
The malicious operation started approximately in August of this year and used a remote access Trojan (RAT) called SugarGh0st, a modification of the fairly well-known Gh0st RAT.
Talos specialists found four samples used in this campaign, targeting users in Uzbekistan and South Korea, based on the language of bait documents, bait content, and distribution indicators.
One of the identified samples was sent to the Ministry of Foreign Affairs of Uzbekistan with a decoy that allegedly duplicates the decree of the local president aimed at improving public administration in the field of technical regulation. The other three samples were distributed in South Korea and targeted small private organizations.
The attack itself began with a phishing email containing disguised documents that, when opened, trigger a multi-step process leading to the deployment of SugarGh0st RAT. The virus includes features to " facilitate remote administration and a modified communication protocol."
In the attachment to the phishing email, disguised documents are embedded in a heavily obfuscated JavaScript dropper contained in a Windows shortcut file packaged in a RAR file.
JavaScript decrypts and transfers attached files to a temporary folder, including the script, a custom DLL loader, and the encrypted SugarGh0st payload.
When a victim opens a fake document, a script runs in the background that starts the DLL loader. This loader in turn uses a copy of the legitimate Windows executable, rundll32.exe, to decrypt and launch the SugarGh0st payload.
SugarGh0st, written in C++, communicates with a hard-coded C2 domain, allowing you to pass system metadata to the server, run a reverse shell, and execute arbitrary commands. It can also list and terminate processes, take screenshots, perform file operations, and even clear the computer's event logs in an attempt to hide its tracks and avoid detection.
The campaign was linked to China due to the Chinese origin of the original Gh0st RAT and its widespread use by Chinese hackers, especially after the source code was published in 2008. Another confirmation is the use of Chinese names in the "last modified" field of metadata files detected during the attack.
In addition, it was noted that Chinese cybercriminals also have a history of targeted attacks on Uzbekistan. Over the past six months, Chinese APT groups have also increased their activity against Taiwan, using home routers to mask their intrusions.

