Friend
Professional
- Messages
- 2,677
- Reaction score
- 1,089
- Points
- 113
How the hacking machine and the "right hand" of the Chinese government work.
German intelligence has published a new report that continues the investigation of data leaks by the Chinese information security company I-Soon. The report shows how i-Soon is closely linked to Chinese government agencies and is involved in industrial espionage in the public interest.
I-Soon is actively engaged in so-called "vulnerability mining", playing a key role in creating and maintaining the Chinese National Vulnerability Database (CNNVD). In 2021, the Chinese government introduced mandatory regulations requiring all companies to report identified vulnerabilities within 48 hours, which are then collected in state databases.
i-Soon is registered as a technical partner of CNNVD, being at the third level of qualification, which obliges it to provide at least 5 new vulnerabilities annually. The found flaws are used to develop methods of cyber attacks, and i-Soon provides services for their implementation. This close relationship with government agencies underscores the importance of the company in the context of China's national security and demonstrates the level of integration into government cyber operations.
Particular attention is drawn to the company's training center — Anxun College, where more than 3,000 specialists are trained annually. Among the students are not only employees of i-Soon, but also representatives of other companies, government and public institutions in China. The training program covers a wide range of topics, from self-study to participation in cyber competitions, which allows the company to find and attract young talents.
In addition, i-Soon has many national certificates that allow it to perform specialized tasks and work with classified information, which further strengthens the company's position as a strategic partner of the state.
The leaks also contain information about employees of the company who work with confidential information. Interestingly, there are no people with contacts abroad among them, which may indicate strict security requirements for personnel. In addition, many of the company's employees have close ties to the Chinese authorities and are members of the Communist Party of China (CPC), which underlines its national character.
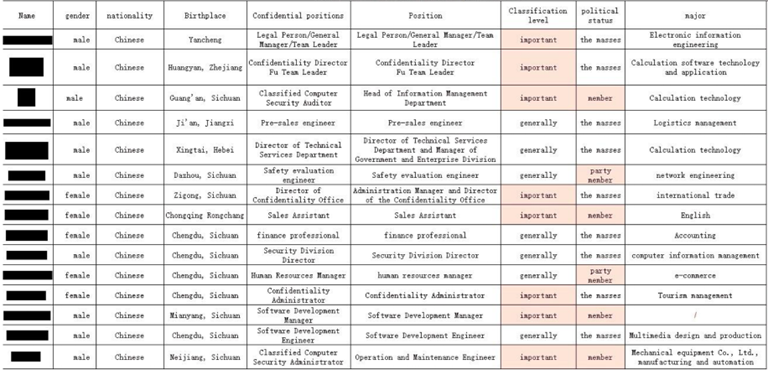
The list of "employees with access to classified information" also points to links betweeni-Soon and the Chinese state apparatus. The list also gives an idea of the structure of individual company jobs
In addition, the leak provides insight into i-Soon's ties to other information security companies in China. In particular, evidence was found that the founder of i-Soon, known under the pseudonym "shutd0wn", maintains ties with well-known APT groups and former members of the patriotic hacker community. Many of the former participants started their own companies that also provide services to Chinese government agencies.
The BfV report highlights that the market for cyber services in China is developing according to the laws of the market economy, which has created a competitive environment in which companies such as i-Soon strive to maximize the professionalization of their services. Chinese government agencies benefit from this development, as they can choose from a variety of companies offering a variety of services and technical expertise. This complicates the work of other countries ' intelligence agencies, which are finding it increasingly difficult to track specific campaigns conducted within China's extensive system.
Initially, the leak became known in February, when documents were leaked revealing details about the development of I-Soon spyware aimed at social networks, telecommunications companies and other organizations around the world. It is assumed that the Chinese government is behind the operations.
Source
German intelligence has published a new report that continues the investigation of data leaks by the Chinese information security company I-Soon. The report shows how i-Soon is closely linked to Chinese government agencies and is involved in industrial espionage in the public interest.
I-Soon is actively engaged in so-called "vulnerability mining", playing a key role in creating and maintaining the Chinese National Vulnerability Database (CNNVD). In 2021, the Chinese government introduced mandatory regulations requiring all companies to report identified vulnerabilities within 48 hours, which are then collected in state databases.
i-Soon is registered as a technical partner of CNNVD, being at the third level of qualification, which obliges it to provide at least 5 new vulnerabilities annually. The found flaws are used to develop methods of cyber attacks, and i-Soon provides services for their implementation. This close relationship with government agencies underscores the importance of the company in the context of China's national security and demonstrates the level of integration into government cyber operations.
Particular attention is drawn to the company's training center — Anxun College, where more than 3,000 specialists are trained annually. Among the students are not only employees of i-Soon, but also representatives of other companies, government and public institutions in China. The training program covers a wide range of topics, from self-study to participation in cyber competitions, which allows the company to find and attract young talents.
In addition, i-Soon has many national certificates that allow it to perform specialized tasks and work with classified information, which further strengthens the company's position as a strategic partner of the state.
The leaks also contain information about employees of the company who work with confidential information. Interestingly, there are no people with contacts abroad among them, which may indicate strict security requirements for personnel. In addition, many of the company's employees have close ties to the Chinese authorities and are members of the Communist Party of China (CPC), which underlines its national character.
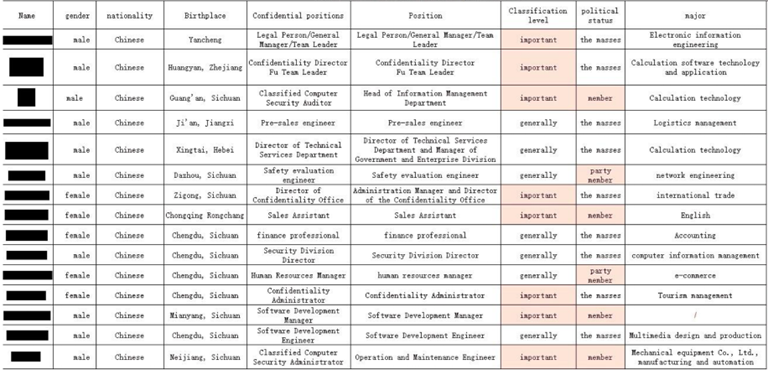
The list of "employees with access to classified information" also points to links betweeni-Soon and the Chinese state apparatus. The list also gives an idea of the structure of individual company jobs
In addition, the leak provides insight into i-Soon's ties to other information security companies in China. In particular, evidence was found that the founder of i-Soon, known under the pseudonym "shutd0wn", maintains ties with well-known APT groups and former members of the patriotic hacker community. Many of the former participants started their own companies that also provide services to Chinese government agencies.
The BfV report highlights that the market for cyber services in China is developing according to the laws of the market economy, which has created a competitive environment in which companies such as i-Soon strive to maximize the professionalization of their services. Chinese government agencies benefit from this development, as they can choose from a variety of companies offering a variety of services and technical expertise. This complicates the work of other countries ' intelligence agencies, which are finding it increasingly difficult to track specific campaigns conducted within China's extensive system.
Initially, the leak became known in February, when documents were leaked revealing details about the development of I-Soon spyware aimed at social networks, telecommunications companies and other organizations around the world. It is assumed that the Chinese government is behind the operations.
Source

