Brother
Professional
- Messages
- 2,590
- Reaction score
- 541
- Points
- 113
Mobile game developer Ateam has warned customers about a cloud security snag.
Japanese game developer Ateam Entertainment has proven that a simple Google Drive configuration error can lead to the potential but unlikely disclosure of confidential information to almost a million people within 6 years and 8 months. The Japanese firm is a maker of mobile games and productivity apps.
Ateam informed its app and service users, employees, and business partners about its discovery on November 21, 2023. According to the company, since March 2017, the company instance in Google Drive has been incorrectly set to " All on the Internet: Anyone can find a file in Google and open it without logging in to a Google account."
The insecure Google Drive instance contained 1,369 files containing personal information about Ateam customers, Ateam business partners, former and current employees, and even interns and people who applied for a position with the company. Ateam confirmed that the data of 935,779 people was disclosed, of which 98.9% were customers.
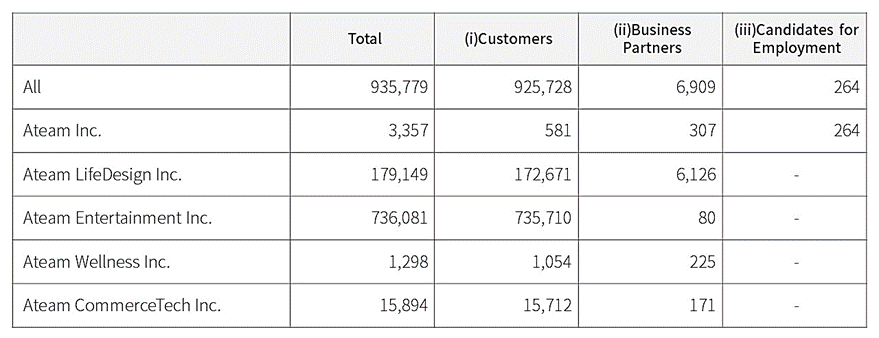
Analysis of exposed individuals
The data provided by an incorrect configuration varies depending on the type of relationship each person has with the company and may include the following:
The company says it has not seen concrete evidence that attackers stole the disclosed information, but encourages people to remain vigilant against unsolicited and suspicious messages.
If you set a file in Google Drive to "All on the Web", the file will only be available for viewing by those who have the exact URL, which is usually intended for collaboration between people who work with non-confidential data. If an employee or other user who has a link publishes it publicly by mistake, it can be indexed by search engines and become publicly available.
While it is unlikely that anyone found the public Google Drive URL on their own, this notice demonstrates the need for companies to properly protect their cloud services to prevent erroneous data disclosure.
Japanese game developer Ateam Entertainment has proven that a simple Google Drive configuration error can lead to the potential but unlikely disclosure of confidential information to almost a million people within 6 years and 8 months. The Japanese firm is a maker of mobile games and productivity apps.
Ateam informed its app and service users, employees, and business partners about its discovery on November 21, 2023. According to the company, since March 2017, the company instance in Google Drive has been incorrectly set to " All on the Internet: Anyone can find a file in Google and open it without logging in to a Google account."
The insecure Google Drive instance contained 1,369 files containing personal information about Ateam customers, Ateam business partners, former and current employees, and even interns and people who applied for a position with the company. Ateam confirmed that the data of 935,779 people was disclosed, of which 98.9% were customers.
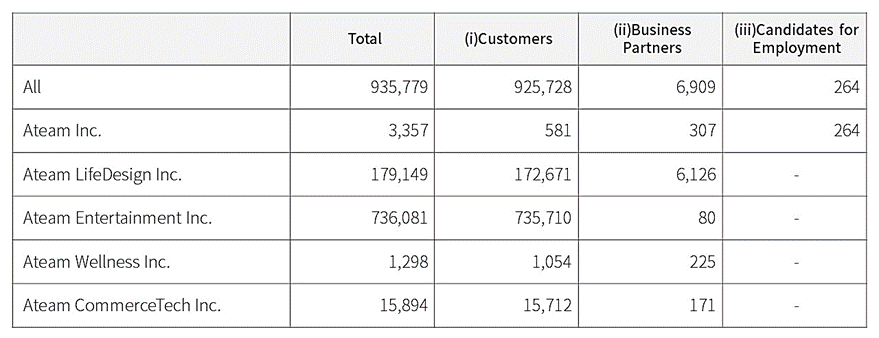
Analysis of exposed individuals
The data provided by an incorrect configuration varies depending on the type of relationship each person has with the company and may include the following:
- Full names;
- Email address;
- Phone numbers;
- Client numbers;
- Identification numbers of the terminal (device).
The company says it has not seen concrete evidence that attackers stole the disclosed information, but encourages people to remain vigilant against unsolicited and suspicious messages.
If you set a file in Google Drive to "All on the Web", the file will only be available for viewing by those who have the exact URL, which is usually intended for collaboration between people who work with non-confidential data. If an employee or other user who has a link publishes it publicly by mistake, it can be indexed by search engines and become publicly available.
While it is unlikely that anyone found the public Google Drive URL on their own, this notice demonstrates the need for companies to properly protect their cloud services to prevent erroneous data disclosure.

