Jollier
Professional
- Messages
- 1,139
- Reaction score
- 1,185
- Points
- 113
How does Wi-Fi work?
Introduction
It was back in 1998, and in a cozy radio lab in Australia, an experienced engineer John O'sullivan created a technology that, no less, changed the world.
How it works
Let's start, perhaps, with simple things. From the previous material about how the Internet works, we realized that the cable with the Internet ends its way in the connector of our router. How does wireless data exchange take place between the router and our device? Just the same, with the help of good old radio waves. The same antennas installed on the router distribute radio waves that the WIFI module of our smartphone picks up.

Encryption
This is the topic we are most interested in. The creators of Wi-Fi at one time foresaw the appearance of crooks who would try to catch the free Internet at someone else's expense, so they added encryption protocols to their technology. The encryption Protocol provides the access point with the same password that many attackers want to get hold of. If the network has no password, then it doesn't have encryption, and therefore it's dangerous to connect to it, since all data transfer is visible to experienced hackers in the palm of your hand.
All protocols work on the same principle - they hash the password of the access point and use cryptography to encrypt it.
The first Wi-Fi security Protocol was WEP and almost immediately showed its unreliability. Its cryptographic key was too unreliable, and 2 years after the Protocol was released, it was hacked. Therefore, today only WPA and WPA 2 are widely used. They are more reliable because their cryptographic keys are constantly changing. That's just, history shows that the current Protocol does not cause any special problems for hackers. But more on this in tomorrow's post.
Hacking Wi-Fi part 1
Introduction
We continue the topic of Wifi And go straight to the dessert-the actual hacking.
Disclaimer. All information is provided for educational purposes only.
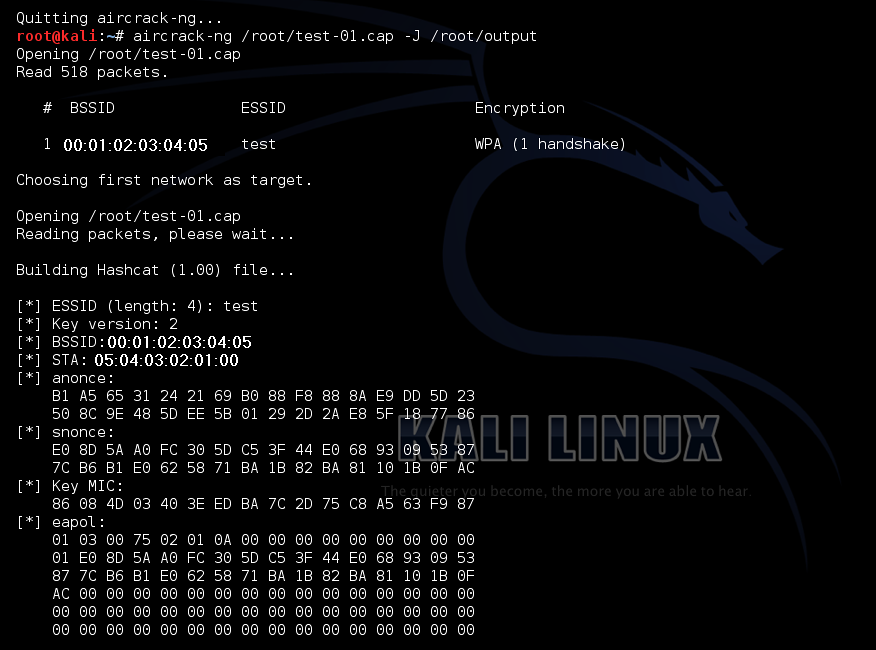
Handshake
Let's move on to the fundamental principle of hacking Wi-Fi. handshake"либо "рукопожатие". handshake several conditions must be met.

After the handshake data is received and saved, it is run through a special program that selects the desired password for WiFI using a dictionary or classic brute force. If you describe everything very briefly, then the hacking process looks something like this: monitoring the access point with special software-Handshake interception-password selection. Yes, the process is complicated. Yes, it does not guarantee 100% of the result, since we are dealing with selection. Nevertheless, this is the most popular method that is used all over the world. Plus, no one promised it would be easy.

Option for hackers
Why an option for hackers? Because you need to code, as well as use the main hacker OS-Kali Linux. This is the most common and free hacking method that can be done even from your phone. The whole process will take place in a classic black-and-white square with a bunch of incomprehensible text. As promised, there will be no direct commands, but I will describe the process itself.
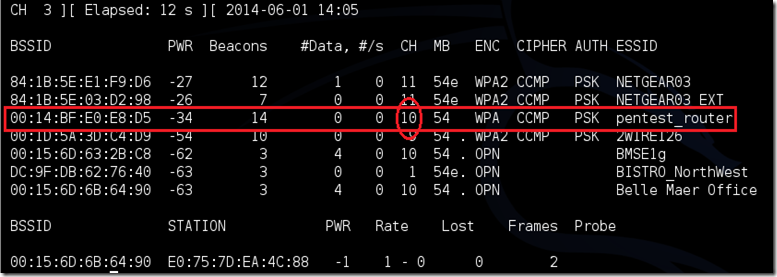
Use the code to switch the Wi-Fi module to monitoring mode, then scan available access points.
And a small bonus, in order to simplify the hacking process, a whole bunch of utilities have been made for Kali Linux that simplify the whole process. airgeddon, Wifite.
Option for Windows
Frankly, Windows is not the best platform for hacking Wi-Fi. You can do this, but there are pros and cons. The whole problem is in monitoring. Third-party software is required to scan WIFI networks and intercept Handshake. Such programs are mainly used by administrators and are paid solutions. What is nice is that they are easier to understand since you do not need to code anything , and there is also a relatively clear interface.
Software links: Commview,Acrylic WiFi Professional
[/QUOTE]
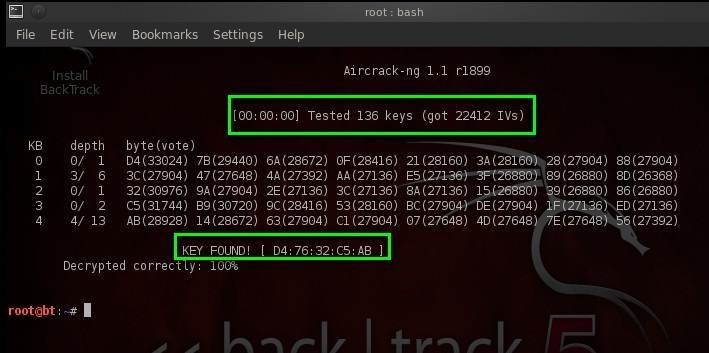
Aircrack
I decided to allocate a separate paragraph for software, which you can't do without either on Linux or on Windows. This is actually a program that selects the password from the dictionary thanks to the received handshake. In addition, it has built-in monitoring functions and is already pre-installed in the Kali Linux repository. Nevertheless, I advise you to regularly update the air crack from the official website. The selection process itself is very simple. Choose handshake, the dictionary database, and launch it. If the selection is successful, you will see the exclamation mark key found ! You should also say a few words about the password database.
Link to Aircrack
Conclusion
Well, I hope you liked this information and will be useful. In the following articles from the same series, we'll talk about Router Scan, data interception through a compromised network, and home WIFI security.
Hacking WIFI part 2
Introduction
In the first part of our article, you learned about the most common method of hacking Wi-Fi, which is mainly used only by system administrators or real hackers. Now we have, so to speak, a popular issue. We will tell you about the easiest ways to hack Wi-Fi, which can be used by each of you. You don't need to code anything in these methods. The only caveat is that they may not work in every case, and you are unlikely to break any well-protected Wi-Fi point. But as an option for neighbors, it is quite suitable.
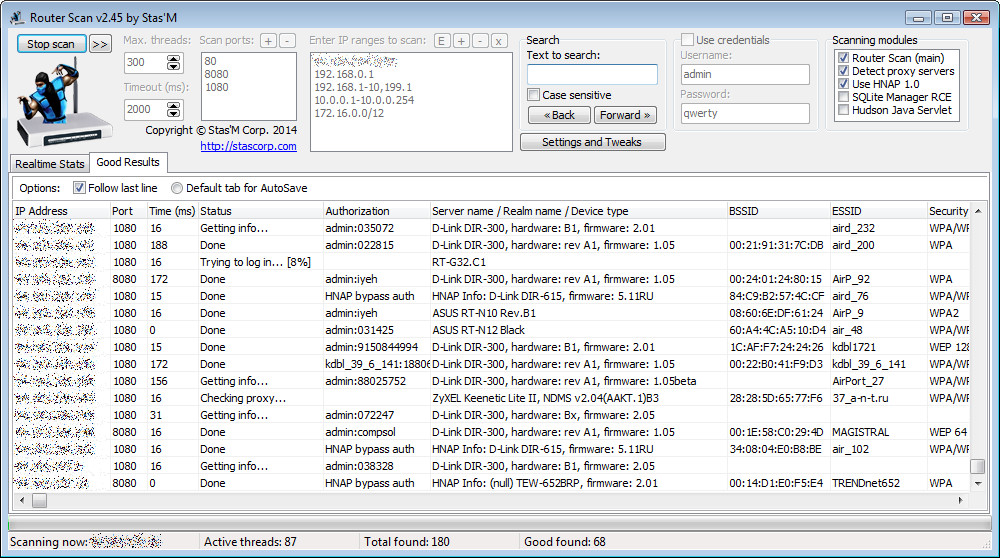
Router Scan
So, the first method from our selection is to use the sensational software called Router Scan a couple of years ago. The program is free, easy to use, as well as basically its own robots. This program does not search for passwords or run through a dictionary. It works according to a slightly different scheme. So to speak, it approaches the issue from a different angle. Router Scan scans external Ip addresses and selects passwords for the routers themselves.
Link to Router Scan

Hacking through the router PIN code
The next method is to select the Pin code from the router. All devices have such a function as OSS, which allows you to set an additional Pin code to connect to the access point. In other words, you can set both a code and a password. If you forgot one thing, you connect via another. The most popular program for hacking this Pin code is Dummper+Jumpstart. Its functionality is more extensive, but today we are only interested in the Pin code. The interface of the programs is as simple as possible.
Link to Dummper

Options for smartphones
You can also hack Wi-Fi From your smartphone, but only if you have Android. To do this, you need to install Kali Linux Net Hunter on your phone (the same Kali functionality, only on Android) and use the first method indicated in the previous article. Since I don't really believe in all sorts of Wi-Fi hacking programs from the app store, I recommend using only the hacker method. But even for those who don't really want to code something, there is a way out. These are applications with free databases of passwords from various networks.
Option for Android and IOS - WI-FI Map, WI-FI Finder
Wi-Fi Protection
Introduction
From previous releases, we learned how attackers can gain full access to our home networks, which means that after a little brainstorming, we thought about some ways to protect Wi-Fi from various hacker attacks.
Nevertheless, for those who have not read, or read inattentively, I have prepared a small selection of ways to protect your home Wi-Fi From intruders and other freebie seekers.
Passwords
The first and most important thing in protecting your Wi-Fi is, of course, passwords.
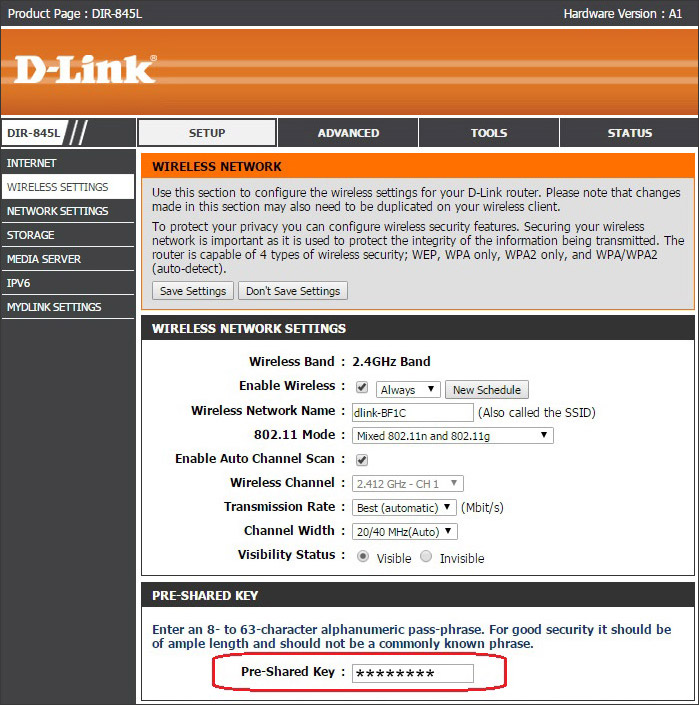
Encryption mode
This is a very important point, because if you have an old router, the old WPA encryption method may be installed on it, or even worse, WEP.

Calculate and disable pests
And now it's time to deal with the dishonest neighbors. Go to the item "Connected devices" and look. In order to accurately calculate connected devices and compare them with your own, you can check the Mac addresses. You can find them in the settings of your devices and they are automatically displayed in the router settings. Have you found a pest? Great, disable it just by clicking on the button. Well, so that strangers never connect to your WI-FI again, you can enable filtering by MAC addresses.

Don't burn the router
If you don't want to bother with Mac addresses, there is another way to hide your network from outsiders. To do this, disable the "broadcast ssid" function in the access point Name section. In this case, when scanning networks on any device, your network will be invisible. The disadvantage of this method is that you will need to remember the name of your network and connect new devices manually. It is advisable to change the network name even before that.
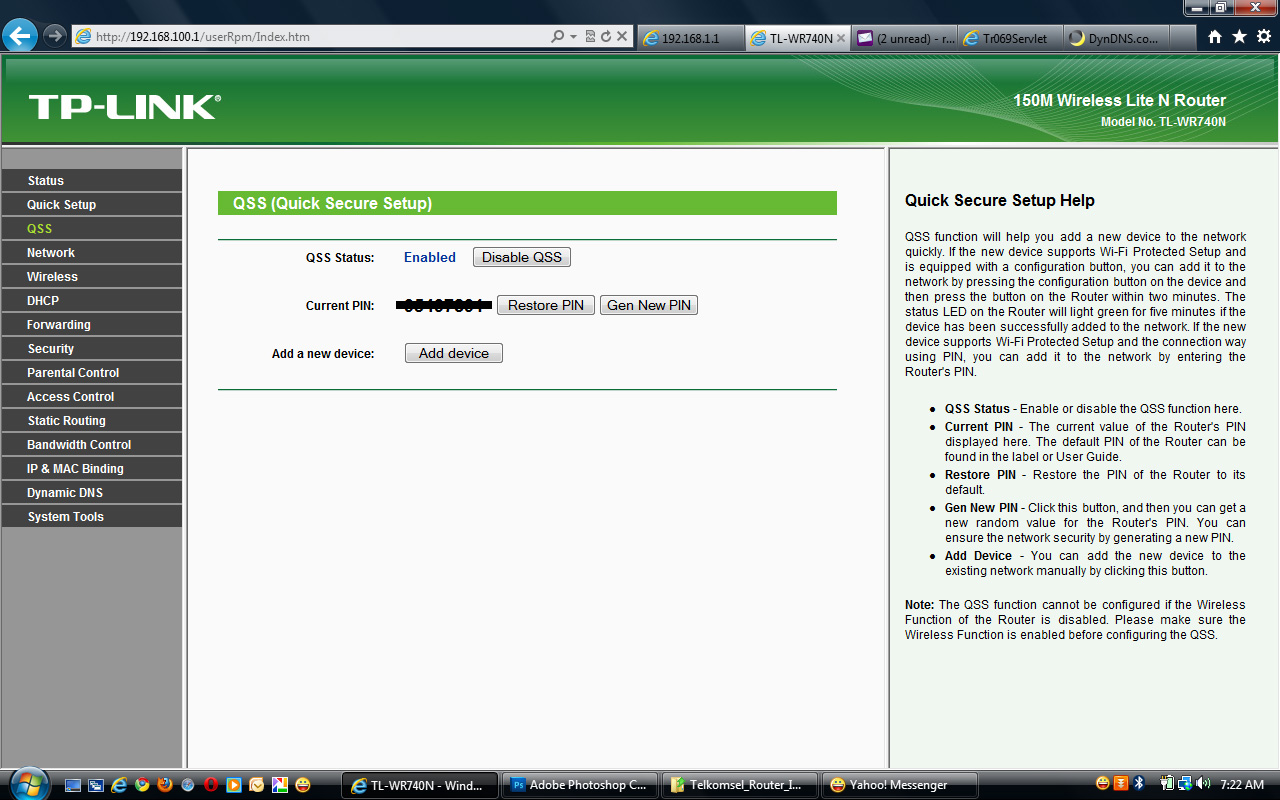
Disabling WPS / QSS and remote access
Do you remember the Pin code hacking method? So in order to avoid hacking using this method, you must disable OSS in the settings. In addition, you also need to disable WPS and other functions of remote access or quick connection.
Updating the firmware
Finally, don't forget to update the router's firmware. With the new firmware, old vulnerabilities can be fixed in the router or the encryption Protocol is updated, so do not neglect this.
Well, that's all for me, I hope this post was useful for you. Yes, these security principles are very simple, but they are more than enough for you. If you want more detailed posts about protection using the sysadmin's Arsenal, write in the comments.