Carding
Professional
- Messages
- 2,870
- Reaction score
- 2,524
- Points
- 113
Hacking programs - searching for and using vulnerabilities in software, including with the aim of penetrating the computer system of any organization. The goals are varied: from simple curiosity to the desire to cash in. By breaking into software, an attacker can write an exploit that will be used later to illegally enter the victim's computer; thus, a cybercriminal can compromise an enterprise's resources to steal sensitive data that could be valuable on the black market.
Classification of ways to hack programs
The list of the main methods of malicious activity associated with hacking programs can include the following items.
1. Brute force.
2. Social engineering.
3. Vulnerabilities.
4. Configuration errors.
Brute force is a method of cracking password protection, in which a computer program tries different passwords until the correct one is found. As a rule, the selection is carried out using a dictionary, but it can also be performed by the usual one-by-one checking of all possible combinations of characters.
Social engineering is psychological manipulation based on knowledge of human weaknesses and patterns of thinking. A whole range of tricks is used to obtain the necessary data: phishing, spam, espionage, etc.
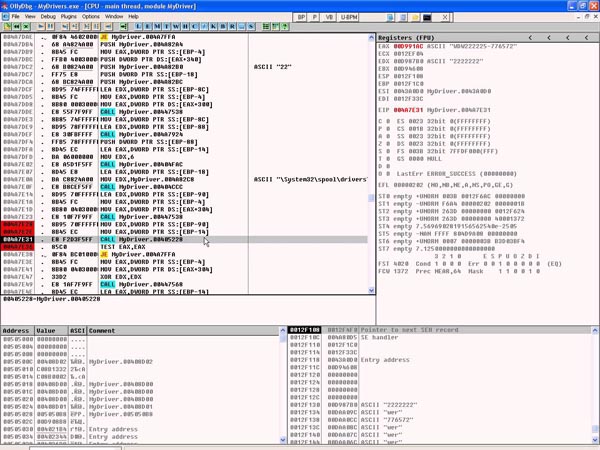
Search for vulnerabilities in software allows you to exploit errors made by programmers in the development of applications and services in order to further penetrate the computer system. Despite the fact that many software developers use tools to identify potential flaws in their code, there are always loopholes that can be exploited by cybercriminals.
Errors in software configuration make it possible to gain access to confidential information and corporate resources, and lead to a weakening of the company's cyber defense.
Hacked objects
An attacker could target any program used in a home or corporate environment. Common targets are games and applications that are distributed on a paid basis: pirates hack them in order to make them public for free. However, programs are often hacked in order to detect vulnerabilities and then penetrate through them into the computer systems of the victim companies.
Source of hacking
Professional cybercriminals are involved in hacking programs with the aim of organizing mass or targeted attacks. In addition, the search for vulnerabilities is carried out by researchers of information security problems who are looking for holes for the sake of professional interest or for reward from developers.
Risk analysis
Any high priority vulnerability found in software entails risks of being exploited by hackers. Manufacturers try to respond to publications about vulnerabilities and to the facts of hacking of their programs as quickly as possible, issuing recommendations to minimize the risk, and then fixes (patches). Therefore, timely software updates become the cornerstone of information security and the only sure way to defend against known attack methods through software weaknesses.
Classification of ways to hack programs
The list of the main methods of malicious activity associated with hacking programs can include the following items.
1. Brute force.
2. Social engineering.
3. Vulnerabilities.
4. Configuration errors.
Brute force is a method of cracking password protection, in which a computer program tries different passwords until the correct one is found. As a rule, the selection is carried out using a dictionary, but it can also be performed by the usual one-by-one checking of all possible combinations of characters.
Social engineering is psychological manipulation based on knowledge of human weaknesses and patterns of thinking. A whole range of tricks is used to obtain the necessary data: phishing, spam, espionage, etc.
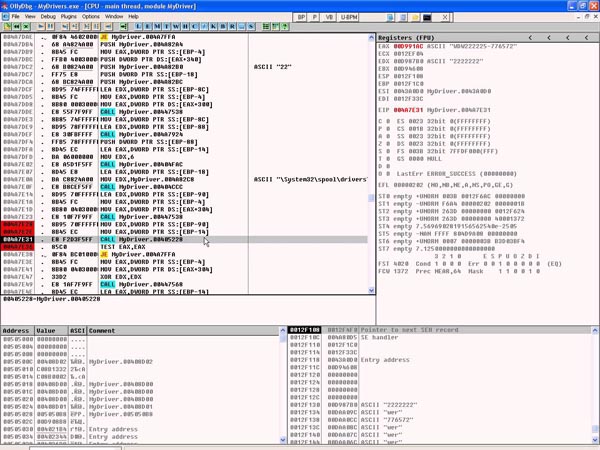
Search for vulnerabilities in software allows you to exploit errors made by programmers in the development of applications and services in order to further penetrate the computer system. Despite the fact that many software developers use tools to identify potential flaws in their code, there are always loopholes that can be exploited by cybercriminals.
Errors in software configuration make it possible to gain access to confidential information and corporate resources, and lead to a weakening of the company's cyber defense.
Hacked objects
An attacker could target any program used in a home or corporate environment. Common targets are games and applications that are distributed on a paid basis: pirates hack them in order to make them public for free. However, programs are often hacked in order to detect vulnerabilities and then penetrate through them into the computer systems of the victim companies.
Source of hacking
Professional cybercriminals are involved in hacking programs with the aim of organizing mass or targeted attacks. In addition, the search for vulnerabilities is carried out by researchers of information security problems who are looking for holes for the sake of professional interest or for reward from developers.
Risk analysis
Any high priority vulnerability found in software entails risks of being exploited by hackers. Manufacturers try to respond to publications about vulnerabilities and to the facts of hacking of their programs as quickly as possible, issuing recommendations to minimize the risk, and then fixes (patches). Therefore, timely software updates become the cornerstone of information security and the only sure way to defend against known attack methods through software weaknesses.

