Carding
Professional
- Messages
- 2,870
- Reaction score
- 2,522
- Points
- 113
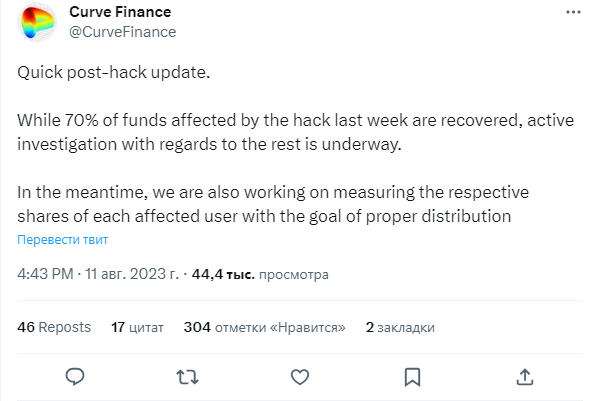
On July 30, an unknown person attacked DEX Curve Finance stablecoin pools and withdrew about $47 million using a vulnerability in the Vyper program code.
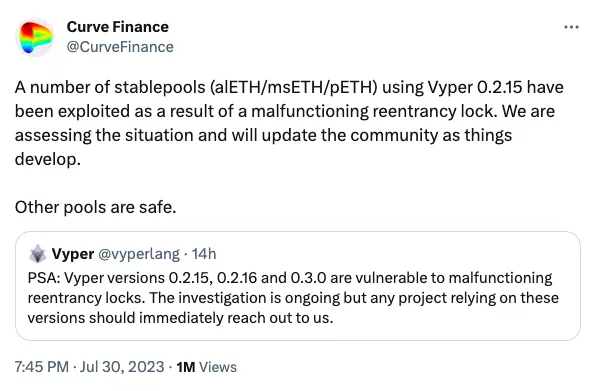
“Several stable pools (alETH/msETH/pETH) using Vyper 0.2.15 have been compromised due to a bug in the re-entry mechanism. We are evaluating the situation and will update the community as events unfold. Other pools are safe,” Curve wrote.
Vyper is a Python-based contract-oriented programming language designed for the Ethereum Virtual Machine. The developers acknowledged that the re-entry exploit is in versions 0.2.15, 0.2.16 and 0.3.0.
According to Ancilia analysts, about 460 protocols used vulnerable software.
According to Curve's investigation, some code compilers incorrectly implemented reentry protection, which prevented multiple functions from executing at the same time by locking the contract.
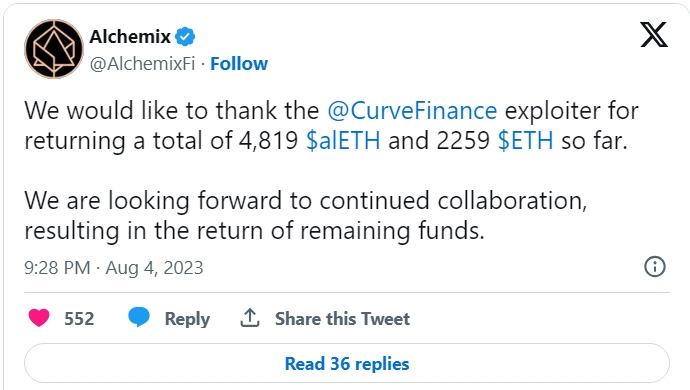
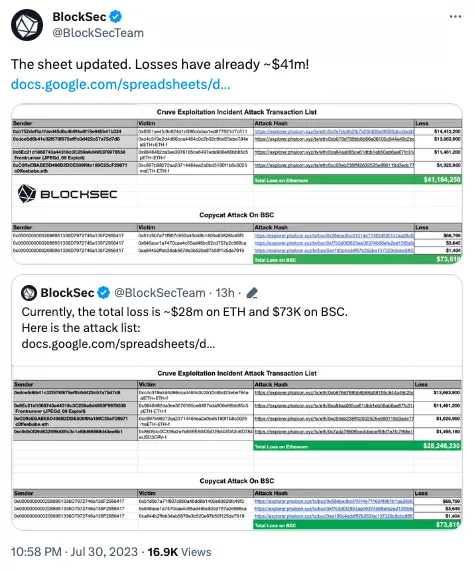
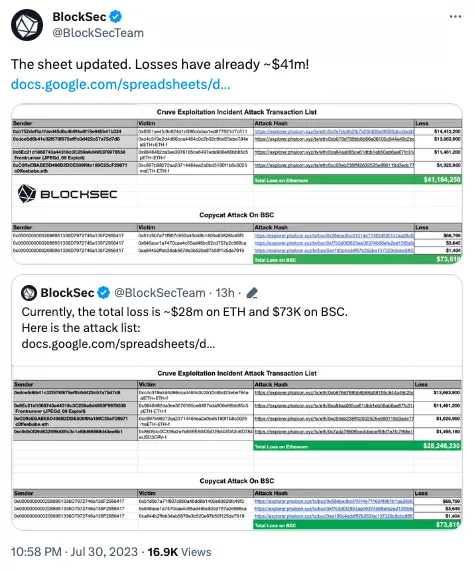
A number of Curve DeFi projects were affected by the attack, including JPEG'd, MetronomeDAO, deBridge, and Ellipsis. The alETH-ETH Alchemix pool lost the most — $13.6 million.
BlockSec experts also reported that a similar exploit affected three projects in the BNB Smart Chain. In total, the attacker withdrew about $73,000 from protocols on the network.
A white hat hacker and MEV bot operator c0ffebabe.eth was able to secure approximately $5.4 million worth of 2,879 ETH stolen from Curve pools by asking affiliated protocols to contact him to recover the assets. He later transferred another 1,000 ETH (~$1.8 million) to a cold wallet.
According to DeFi Llama, Curve Finance’s total locked value almost halved overnight, from $3.25 million to $1.73 million.
The utility token of the Curve DAO (CRV) project fell by 11.5% in 24 hours, according to CoinGecko. At the time of writing, the asset is trading at $0.6492.
The largest South Korean exchange, Upbit, announced that the volatility of CRV increased due to the attack, so the platform suspended all deposits and withdrawals on the coin.
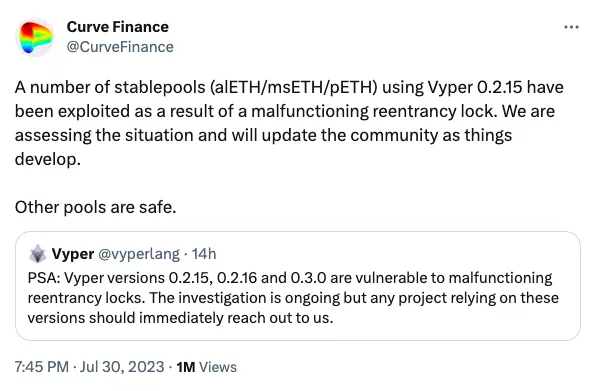
“Several stable pools (alETH/msETH/pETH) using Vyper 0.2.15 have been compromised due to a bug in the re-entry mechanism. We are evaluating the situation and will update the community as events unfold. Other pools are safe,” Curve wrote.
Vyper is a Python-based contract-oriented programming language designed for the Ethereum Virtual Machine. The developers acknowledged that the re-entry exploit is in versions 0.2.15, 0.2.16 and 0.3.0.
According to Ancilia analysts, about 460 protocols used vulnerable software.
According to Curve's investigation, some code compilers incorrectly implemented reentry protection, which prevented multiple functions from executing at the same time by locking the contract.
A number of Curve DeFi projects were affected by the attack, including JPEG'd, MetronomeDAO, deBridge, and Ellipsis. The alETH-ETH Alchemix pool lost the most — $13.6 million.
BlockSec experts also reported that a similar exploit affected three projects in the BNB Smart Chain. In total, the attacker withdrew about $73,000 from protocols on the network.
A white hat hacker and MEV bot operator c0ffebabe.eth was able to secure approximately $5.4 million worth of 2,879 ETH stolen from Curve pools by asking affiliated protocols to contact him to recover the assets. He later transferred another 1,000 ETH (~$1.8 million) to a cold wallet.
According to DeFi Llama, Curve Finance’s total locked value almost halved overnight, from $3.25 million to $1.73 million.
The utility token of the Curve DAO (CRV) project fell by 11.5% in 24 hours, according to CoinGecko. At the time of writing, the asset is trading at $0.6492.
The largest South Korean exchange, Upbit, announced that the volatility of CRV increased due to the attack, so the platform suspended all deposits and withdrawals on the coin.