Carding
Professional
- Messages
- 2,870
- Reaction score
- 2,522
- Points
- 113
When even hackers feel alone and decide to team up.
The Shadow and Twelve groups are united by a closer connection than previously thought, the experts of the F. A. C. C. T. company revealed. Both hacker groups turned out to be interconnected and operating under a common denominator. According to the study, Shadow and Twelve are part of the same hack group aimed at attacking Russian companies and organizations. Experts found that not only were the tactics, techniques, and tools of the attacks similar, but the network infrastructure used by both groups was also common. Shadow, which is aimed at financial gain, demands a ransom of 140-190 million rubles from its victims in order to decrypt encrypted data. While Twelve mainly seeks to sabotage and completely destroy the victim's IT infrastructure, without requiring money.
Sample message from Twelve
For the first time, the activities of the Shadow group, which attacked several large Russian companies, were noticed by experts from F. A. C. C. T. in February-March of this year. Over the past six months, they have focused on industrial, logistics and energy companies, demanding a ransom of $1.5-2 million (approximately 140-190 million rubles at the current exchange rate) for data decryption.
A characteristic feature of hackers is methodical preparation for attacks. They take over the victim's IT infrastructure, steal confidential information, and finally encrypt the system completely. In the case of Windows operating systems, they use an adapted version of the well-known LockBit ransomware, created on the basis of one of the builders published in September 2022. To encrypt Linux systems, attackers use a ransomware program built on the basis of open source Babuk codes.
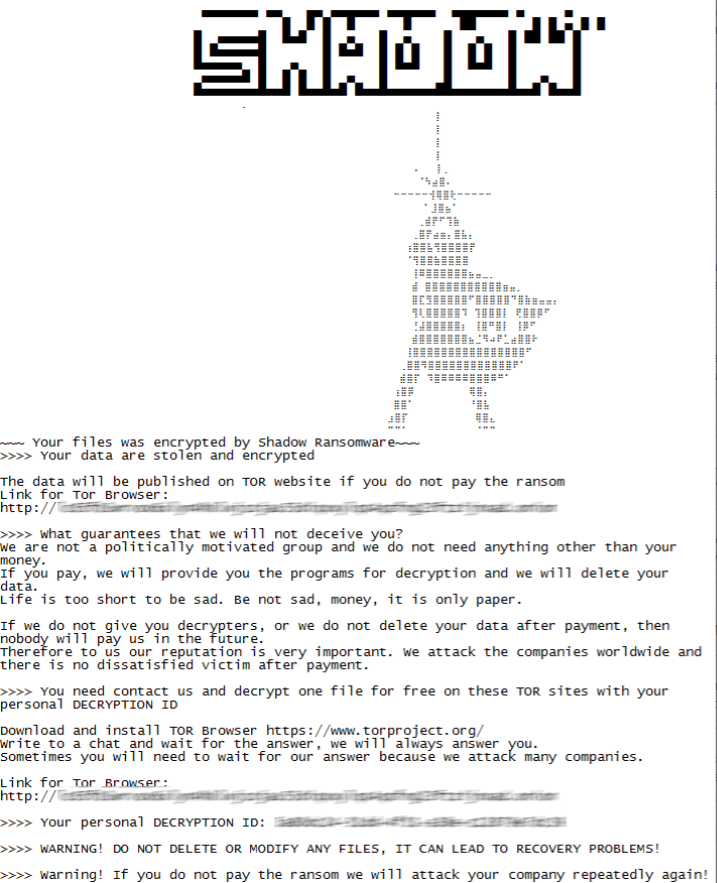
Contents of a text file with a ransom request
To communicate with victims, hackers use the Tor network, placing a chat panel there, access to which is provided to the attacked companies through a personal key from the ransom note. Later communication can go to the group's Telegram channel. It is interesting that hackers are able to steal Telegram sessions on the victim's computers, so that gang members can get information about her actions, a list of contacts of company employees, and also write directly to Telegram to the company's managers.
In parallel with Shadow, in February 2023, Twelve group attacks on Russian organizations were noted. Their goal was to completely destroy the victims information technology infrastructure. It was Twelve that in the spring of 2023 claimed responsibility for a cyberattack on the structures of the Federal customs Service of Russia, as well as in May of the same year – on a Russian manufacturer of hydraulic equipment.
Twelve also used an adapted version of the LockBit ransomware, but unlike Shadow, they specified the name of the Twelve group in text files for victims and did not provide their contacts to discuss the terms of the ransom. In their Telegram channel, hacktivists stated that their project is "the world's response to Russian cyber attacks."
While responding to attacks from the Shadow group, F. A. C. C. T. specialists found that the attackers ' actions were not always perfect. In one of the attacks, a digital footprint was found, which attracted the attention of analysts. Attackers ' errors were detected, for example, when entering the PowerShell command on the Ukrainian keyboard layout. Errors were also observed when encrypting the victim's system, but later the attackers adjusted their approach.
Analysis of the Shadow and Twelve attacks showed that the tactics, techniques and tools used in their attacks are almost identical, as if the attackers are acting in accordance with the developed internal "manuals". In addition, Twelve took into account the experience of mistakes made by Shadow when setting up its ransomware. Moreover, in one of the attacks, Twelve used the Shadow infrastructure.
The Shadow and Twelve groups are united by a closer connection than previously thought, the experts of the F. A. C. C. T. company revealed. Both hacker groups turned out to be interconnected and operating under a common denominator. According to the study, Shadow and Twelve are part of the same hack group aimed at attacking Russian companies and organizations. Experts found that not only were the tactics, techniques, and tools of the attacks similar, but the network infrastructure used by both groups was also common. Shadow, which is aimed at financial gain, demands a ransom of 140-190 million rubles from its victims in order to decrypt encrypted data. While Twelve mainly seeks to sabotage and completely destroy the victim's IT infrastructure, without requiring money.
Sample message from Twelve
For the first time, the activities of the Shadow group, which attacked several large Russian companies, were noticed by experts from F. A. C. C. T. in February-March of this year. Over the past six months, they have focused on industrial, logistics and energy companies, demanding a ransom of $1.5-2 million (approximately 140-190 million rubles at the current exchange rate) for data decryption.
A characteristic feature of hackers is methodical preparation for attacks. They take over the victim's IT infrastructure, steal confidential information, and finally encrypt the system completely. In the case of Windows operating systems, they use an adapted version of the well-known LockBit ransomware, created on the basis of one of the builders published in September 2022. To encrypt Linux systems, attackers use a ransomware program built on the basis of open source Babuk codes.
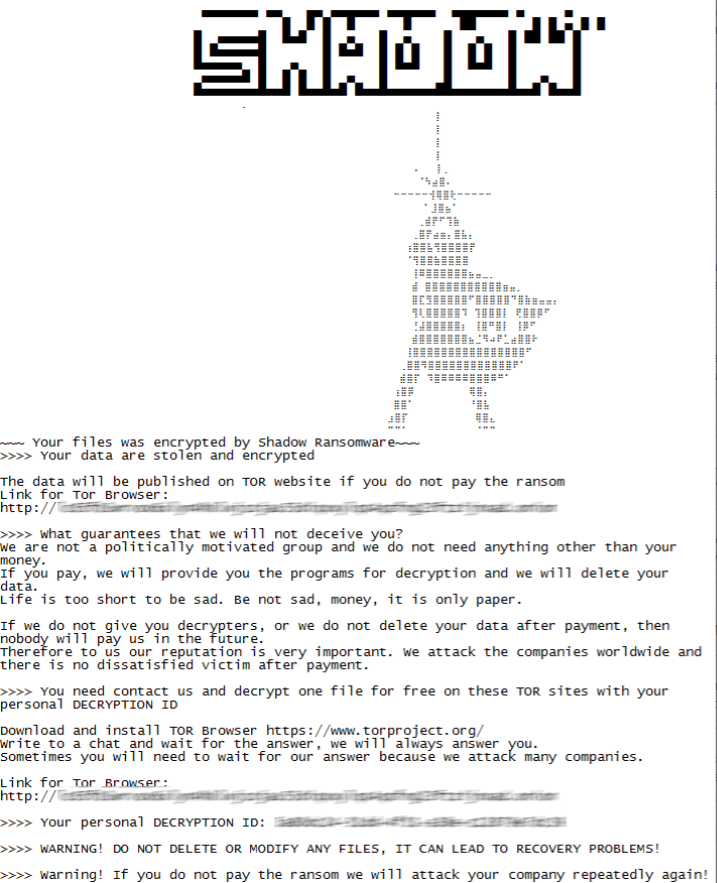
Contents of a text file with a ransom request
To communicate with victims, hackers use the Tor network, placing a chat panel there, access to which is provided to the attacked companies through a personal key from the ransom note. Later communication can go to the group's Telegram channel. It is interesting that hackers are able to steal Telegram sessions on the victim's computers, so that gang members can get information about her actions, a list of contacts of company employees, and also write directly to Telegram to the company's managers.
In parallel with Shadow, in February 2023, Twelve group attacks on Russian organizations were noted. Their goal was to completely destroy the victims information technology infrastructure. It was Twelve that in the spring of 2023 claimed responsibility for a cyberattack on the structures of the Federal customs Service of Russia, as well as in May of the same year – on a Russian manufacturer of hydraulic equipment.
Twelve also used an adapted version of the LockBit ransomware, but unlike Shadow, they specified the name of the Twelve group in text files for victims and did not provide their contacts to discuss the terms of the ransom. In their Telegram channel, hacktivists stated that their project is "the world's response to Russian cyber attacks."
While responding to attacks from the Shadow group, F. A. C. C. T. specialists found that the attackers ' actions were not always perfect. In one of the attacks, a digital footprint was found, which attracted the attention of analysts. Attackers ' errors were detected, for example, when entering the PowerShell command on the Ukrainian keyboard layout. Errors were also observed when encrypting the victim's system, but later the attackers adjusted their approach.
Analysis of the Shadow and Twelve attacks showed that the tactics, techniques and tools used in their attacks are almost identical, as if the attackers are acting in accordance with the developed internal "manuals". In addition, Twelve took into account the experience of mistakes made by Shadow when setting up its ransomware. Moreover, in one of the attacks, Twelve used the Shadow infrastructure.
