Carding
Professional
- Messages
- 2,870
- Reaction score
- 2,522
- Points
- 113
The new attack method could make the iPhone almost unusable.
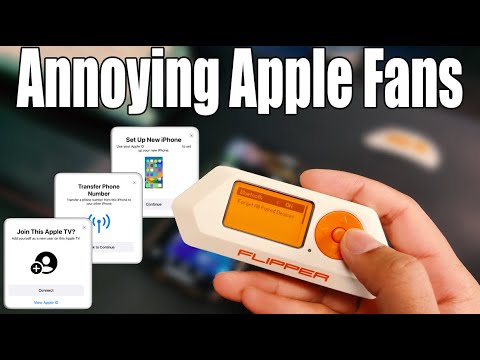
A cybersecurity researcher known as Anthony has demonstrated a new method of attacking the iPhone. With Flipper Zero, Anthony was able to block the iPhone's operation by sending annoying pop-ups with suggestions to connect to nearby Apple Bluetooth devices, such as AirTag, Apple TV, and AirPods.
Anthony called this method of attack " Bluetooth Advertising Assault "(Attack through Bluetooth advertising messages). Anthony wrote on his blog that the attack is not just a minor inconvenience, it can disrupt the user experience that Apple users are used to.
Anthony modified the Flipper Zero firmware to broadcast so-called "Bluetooth Advertisements" - signals that devices use to announce their presence and capabilities. Such signals are part of the Bluetooth Low Energy protocol, which Apple uses to connect various devices of the company to each other.
 www.youtube.com
www.youtube.com
TechCrunch experts were able to reproduce the attack on the iPhone 8 and iPhone 14 Pro. They used the code provided by Anthony and uploaded it to the Flipper Zero device. Then, turning on Bluetooth on Flipper Zero, the specialists began broadcasting pop-ups to the nearest iPhone. The exploit worked on the iPhone both when enabling and disabling Bluetooth in the Control Center, but it didn't work if Bluetooth was completely disabled in the settings.

Replaying the TechCrunch attack
Anthony claims that the attack can work from "thousands of feet away" with a "reinforced board", but he does not disclose the details of the technique due to fears of malicious use of the exploit to send spam over long distances. According to Anthony, Apple can mitigate the consequences of such attacks by implementing a mechanism that will make sure that the connected devices are legitimate, and reducing the distance for connecting via Bluetooth. At the moment, Apple has not commented on the situation.
A cybersecurity researcher known as Anthony has demonstrated a new method of attacking the iPhone. With Flipper Zero, Anthony was able to block the iPhone's operation by sending annoying pop-ups with suggestions to connect to nearby Apple Bluetooth devices, such as AirTag, Apple TV, and AirPods.
Anthony called this method of attack " Bluetooth Advertising Assault "(Attack through Bluetooth advertising messages). Anthony wrote on his blog that the attack is not just a minor inconvenience, it can disrupt the user experience that Apple users are used to.
Anthony modified the Flipper Zero firmware to broadcast so-called "Bluetooth Advertisements" - signals that devices use to announce their presence and capabilities. Such signals are part of the Bluetooth Low Energy protocol, which Apple uses to connect various devices of the company to each other.
Annoying Apple Fans: The Flipper Zero Bluetooth Prank Revealed
Here's how to do it:https://techryptic.github.io/2023/09/01/Annoying-Apple-Fans/Twitter: https://twitter.com/TechWebsite: https://techryptic.github.io/GitHub...
TechCrunch experts were able to reproduce the attack on the iPhone 8 and iPhone 14 Pro. They used the code provided by Anthony and uploaded it to the Flipper Zero device. Then, turning on Bluetooth on Flipper Zero, the specialists began broadcasting pop-ups to the nearest iPhone. The exploit worked on the iPhone both when enabling and disabling Bluetooth in the Control Center, but it didn't work if Bluetooth was completely disabled in the settings.

Replaying the TechCrunch attack
Anthony claims that the attack can work from "thousands of feet away" with a "reinforced board", but he does not disclose the details of the technique due to fears of malicious use of the exploit to send spam over long distances. According to Anthony, Apple can mitigate the consequences of such attacks by implementing a mechanism that will make sure that the connected devices are legitimate, and reducing the distance for connecting via Bluetooth. At the moment, Apple has not commented on the situation.
