Teacher
Professional
- Messages
- 2,669
- Reaction score
- 829
- Points
- 113
Attackers are seeking to take advantage of the recent Pegasus spyware scandal. Under the guise of a security scanner that looks for traces of Pegasus in the system, hackers distribute RAT Sarwent.
Let me remind you that in June 2021, the human rights organization Amnesty International, the non-profit Forbidden Stories project, as well as more than 80 journalists from a consortium of 17 media organizations in ten countries published the results of a joint investigation, which was named the Pegasus Project. Then experts said that they discovered large-scale abuse of Pegasus spyware created by the Israeli company NSO Group. According to their report, the company's spyware is actively used to violate human rights and monitor politicians, activists, journalists and human rights defenders around the world.
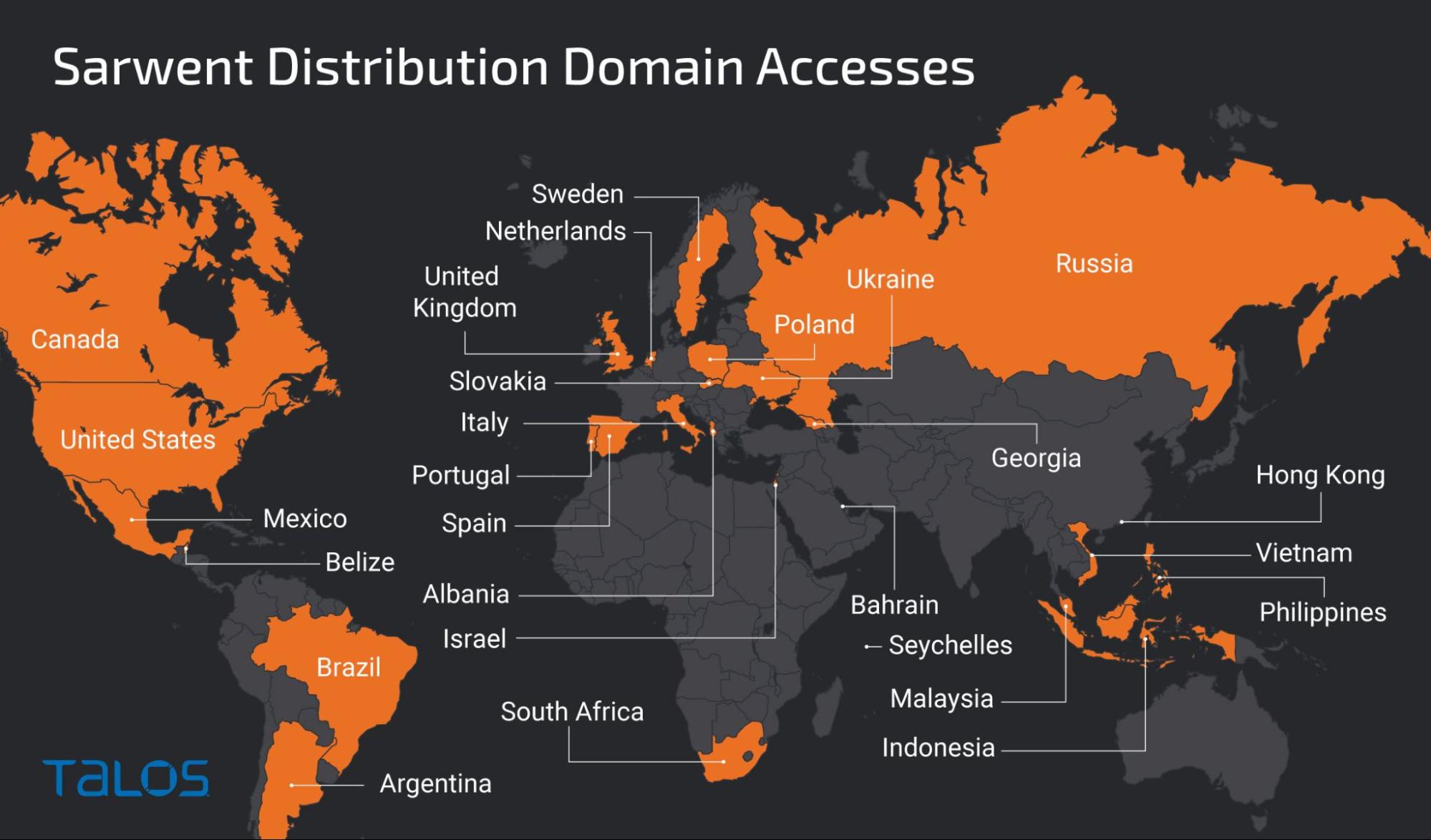
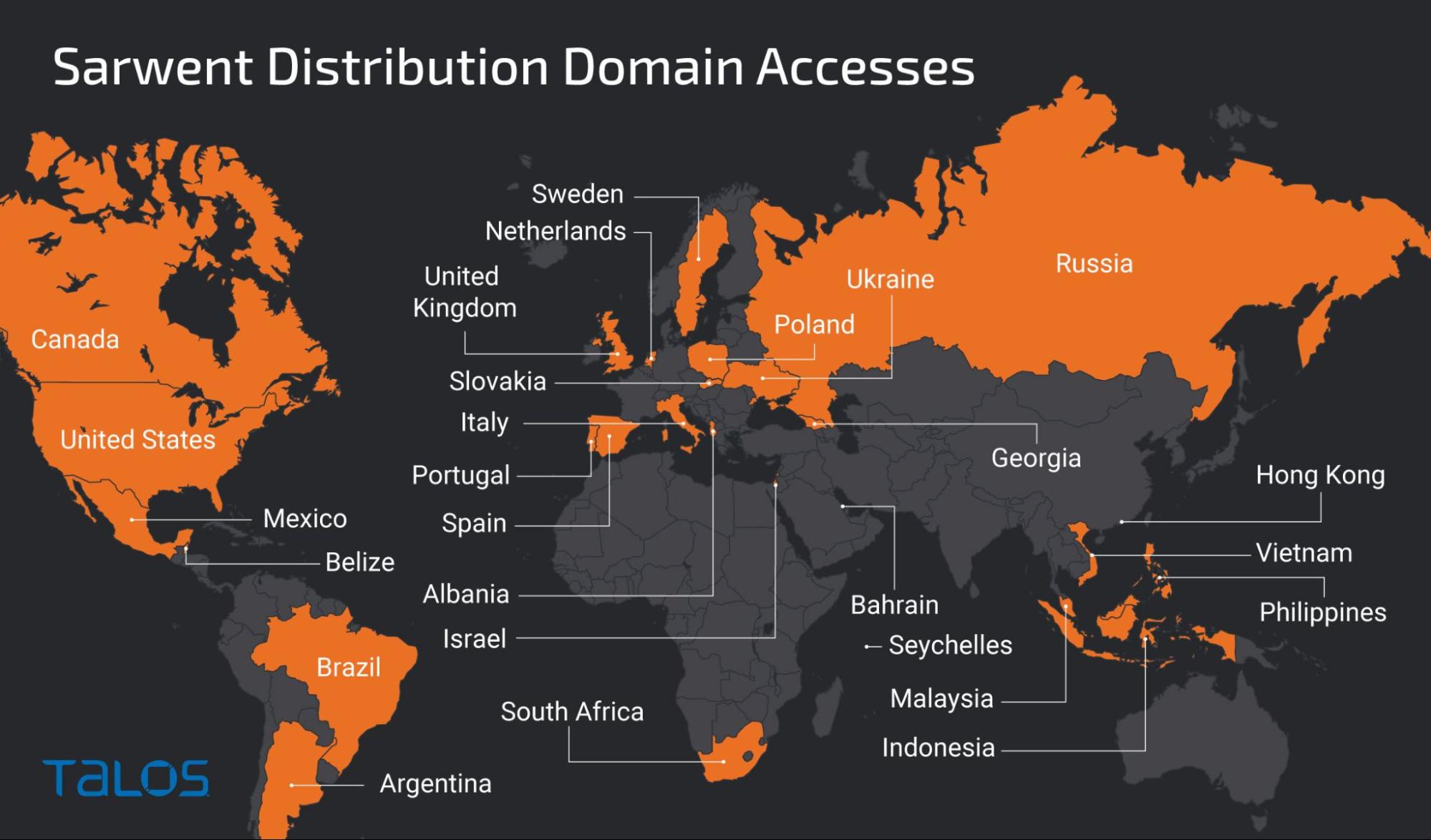
Эксперты Cisco Talos report that attacks using Sarwent have been carried out since the beginning of this year, and they target the most victims in several countries around the world. It is not known what decoys were used by attackers in past campaigns, but now analysts have discovered that Sarwent is distributed through the fake website Amnesty International and is advertised as a protective solution against Pegasus. In fact, Malvari tried to give the appearance of a real antivirus, even developing an appropriate graphical interface.

So far, researchers have not been able to understand exactly how hackers lure visitors to this fake site, but an analysis of the domains of this campaign showed that users from all over the world were accessing them, although no signs of a large-scale campaign were found.
In addition to copies of the Amnesty International website, Sarwent has also registered the following domains::
Sarwent is written in Delphi, which is not often found among modern Malware. Like other rats, it provides its operators with access to the infected machine. It provides direct access to the system by activating RDP or via Virtual Network Computing (VNC). However, malware can also use other methods, including shells and PowerShell execution.
While the researchers are not sure whether Sarwent operators are pursuing financial benefits, or whether we are talking, for example, about espionage.
xakep.ru
Let me remind you that in June 2021, the human rights organization Amnesty International, the non-profit Forbidden Stories project, as well as more than 80 journalists from a consortium of 17 media organizations in ten countries published the results of a joint investigation, which was named the Pegasus Project. Then experts said that they discovered large-scale abuse of Pegasus spyware created by the Israeli company NSO Group. According to their report, the company's spyware is actively used to violate human rights and monitor politicians, activists, journalists and human rights defenders around the world.
Эксперты Cisco Talos report that attacks using Sarwent have been carried out since the beginning of this year, and they target the most victims in several countries around the world. It is not known what decoys were used by attackers in past campaigns, but now analysts have discovered that Sarwent is distributed through the fake website Amnesty International and is advertised as a protective solution against Pegasus. In fact, Malvari tried to give the appearance of a real antivirus, even developing an appropriate graphical interface.

So far, researchers have not been able to understand exactly how hackers lure visitors to this fake site, but an analysis of the domains of this campaign showed that users from all over the world were accessing them, although no signs of a large-scale campaign were found.
In addition to copies of the Amnesty International website, Sarwent has also registered the following domains::
- amnestyinternationalantipegasus[.]com;
- amnestyvspegasus[.]com;
- antipegasusamnesty[.]com.
Sarwent is written in Delphi, which is not often found among modern Malware. Like other rats, it provides its operators with access to the infected machine. It provides direct access to the system by activating RDP or via Virtual Network Computing (VNC). However, malware can also use other methods, including shells and PowerShell execution.
While the researchers are not sure whether Sarwent operators are pursuing financial benefits, or whether we are talking, for example, about espionage.
xakep.ru
