Carding
Professional
- Messages
- 2,870
- Reaction score
- 2,522
- Points
- 113
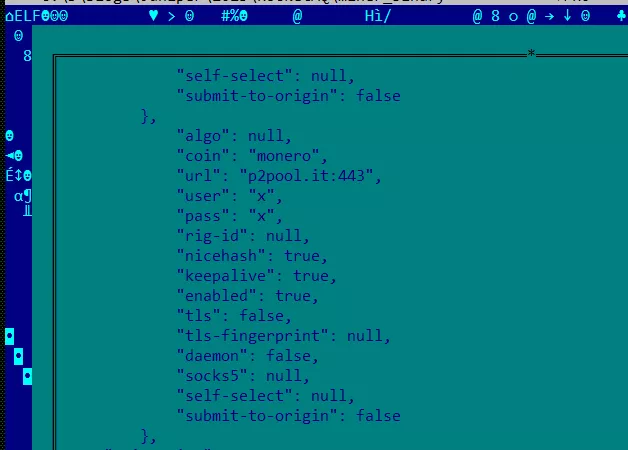
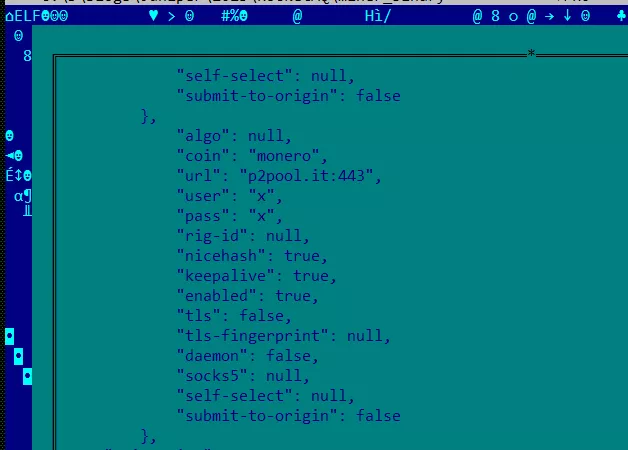
The DreamBus malware, which has not been active since 2021, has again begun attacking Linux users to install a hidden XMRig miner for mining the Monero cryptocurrency. Juniper Threat Labs experts drew attention to this.
DreamBus exploits a recently patched vulnerability in the Apache RocketMQ messaging application that allows attackers to remotely execute commands.
Data: Juniper Threat Labs.
Although Monero mining is the main target of attacks, the modular nature of the malware allows it to be extended and potentially used to steal confidential communications.
DreamBus exploits a recently patched vulnerability in the Apache RocketMQ messaging application that allows attackers to remotely execute commands.
Data: Juniper Threat Labs.
Although Monero mining is the main target of attacks, the modular nature of the malware allows it to be extended and potentially used to steal confidential communications.
