Papa Carder
Professional
- Messages
- 188
- Reaction score
- 176
- Points
- 43
Introduction and History
Ploutus is a family of ATM malware first identified in Mexico in 2013, designed specifically for jackpotting attacks—exploiting ATMs to dispense cash without legitimate transactions, bank cards, or customer accounts. It has evolved over the years, with variants like Ploutus-D becoming prominent in global campaigns. By 2025-2026, Ploutus has been linked to over 1,900 jackpotting incidents in the US since 2020, including more than 700 in 2025 alone, resulting in losses exceeding $20 million (some reports cite up to $40 million). The malware targets financial institutions' ATMs, exploiting both physical and software vulnerabilities. Notable campaigns include those attributed to the Tren de Aragua (TdA) transnational criminal organization, indicted in December 2025 for a scheme involving 54 individuals and $40.73 million in losses. Ploutus attacks the ATM itself rather than customer accounts, enabling rapid cash-outs in minutes that are hard to detect until after the fact.Variants
The Ploutus family includes several iterations:- Early Variants (e.g., Ploutus, Ploutus.B): First spotted in 2013, these used CD-ROM drives for infection and SMS for remote control via USB-enabled cell phones.
- Ploutus-D: A highly specialized variant targeting Diebold Nixdorf and KAL Kalignite multi-vendor software suites. It supports over 40 ATM vendors with minimal code adjustments, using modular, obfuscated .NET code. It was observed in Latin America before spreading to the US in 2025, including regions like the Pacific Northwest, Texas, and the Southeast. Ploutus-D leverages keyboard hooks for control and requires an 8-digit activation code valid for 24 hours. Later versions, like those analyzed by Mandiant in 2017, added features such as hardware ID tracking and activation states.
Technical Architecture and How It Works
Ploutus is built on the Microsoft .NET framework, making it decompilable but heavily obfuscated. It exploits the eXtensions for Financial Services (XFS) middleware, an open-standard API that interfaces banking software with ATM hardware (e.g., cash dispensers, printers). By issuing custom commands to XFS, Ploutus bypasses bank authorization, directly controlling hardware to dispense cash on demand.- Core Components: Modular design with hooks into keyboard inputs (e.g., F-keys like F3 for dispensing). It interacts with the Kalignite platform's abstraction layer for cross-vendor compatibility. The malware runs as a Windows service or executable, using encrypted resources for persistence.
- Activation and Control: Requires a unique code (e.g., hardware ID-based) for activation. Once active, it displays status via minimal UI, showing cassette counts, hardware IDs, and dispensation options. Earlier variants used SMS; Ploutus-D focuses on physical keyboard or external devices.
- Compatibility: Exploits Windows OS (XP, 7, 8, 10) vulnerabilities, with little adjustment needed for different manufacturers.
Here's an example screenshot of a Ploutus interface showing activation and status:
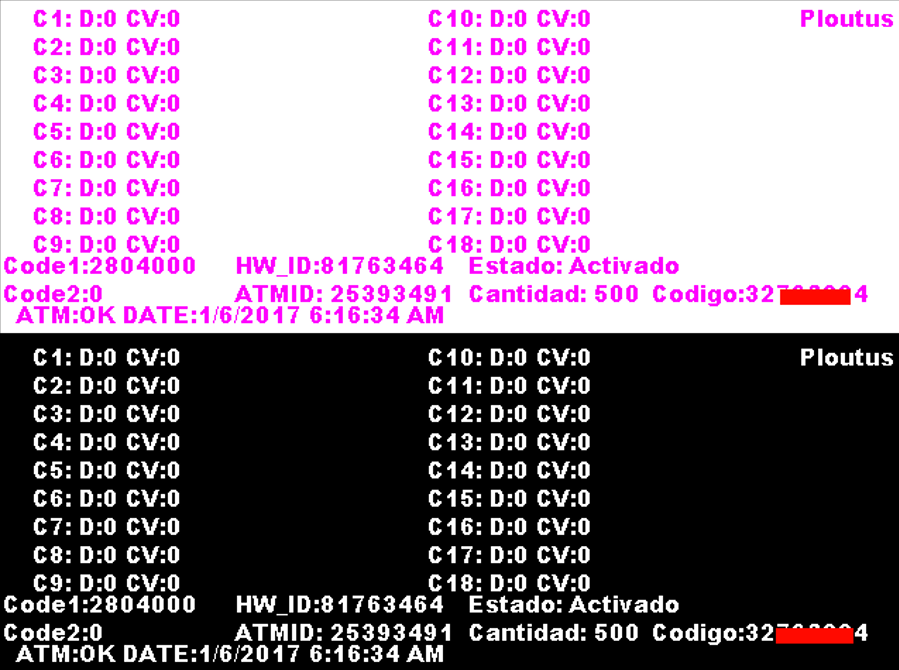
New Variant of Ploutus ATM Malware Observed in the Wild in Latin America | Mandiant | Google Cloud Blog
Obfuscation Techniques
Ploutus uses .NET Reactor for protection, including:- String Encryption: Hardcoded keys encrypt strings.
- Method Proxying and CFG Obfuscation: Obscures function calls and execution flow, complicating debugging.
- Necrobit Method Body Encryption: Replaces real method bodies with fake MSIL code; decrypts at JIT compilation using XOR/ADD with runtime-computed keys from constant unfolding (arithmetic ops like add, shift, XOR). Deobfuscation involves dynamic analysis (breakpoints on XOR patterns) and tools like dnLib to patch binaries.
Anti-forensics include log deletion, process termination (e.g., security monitors), and obfuscated mutexes.
Installation and Exploitation Tactics
Installation requires physical access:- Use generic/master keys, lockpicking, or force to open ATM cabinets.
- Methods: Remove hard drive, copy malware (e.g., AgilisConfigurationUtility.exe), reinsert and reboot; or replace with preloaded drive/USB. Attach external keyboard for control.
- Exploitation: Enter activation code; use F-keys to dispense (e.g., F3). Coordinated teams handle reconnaissance, installation, and cash-out. Targets include Diebold Opteva series with Kalignite on unsupported OS like Windows XP.
Diagram of a targeted ATM model (Diebold Opteva):
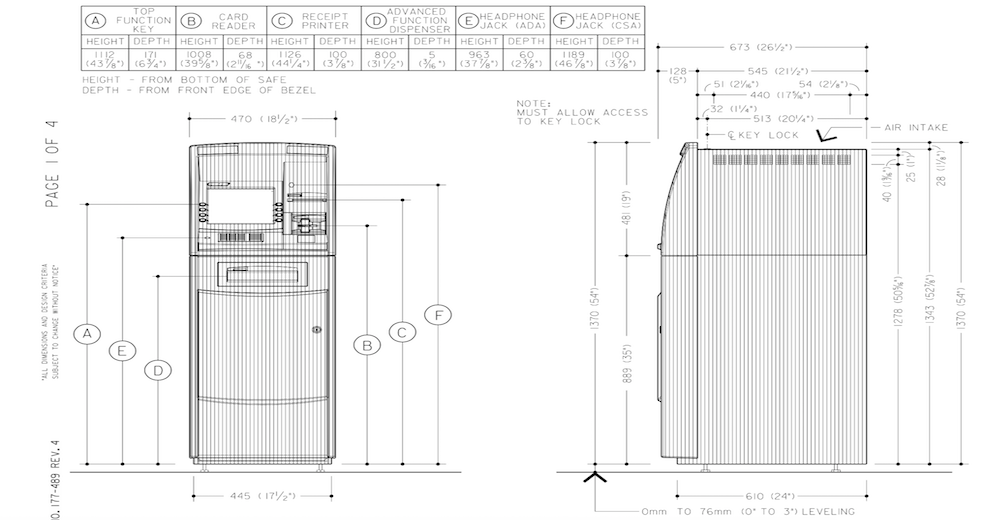
First ATM 'Jackpotting' Attacks Hit US - BankInfoSecurity
Indicators of Compromise (IOCs)
- Files: Newage.exe, Color.exe, Levantaito.exe, NCRApp.exe, sdelete.exe, Promo.exe, WinMonitor.exe, WinMonitorCheck.exe, Anydesk1.exe, AgilisConfigurationUtility.exe, Diebold.exe, Log.txt, Log2.txt, P.bin, PDLL.bin, C.dat, Restaurar.bat.
- Hashes (MD5): 2C2D16658D8DA6B389934273EF8F8E22, 5F177B84F3D92AB5711BE446125FDBE3, etc.
- Mutexes: Ploutos, DIEBOLDPL, KaligniteAPP.
- Registry: HKLM\Software\Microsoft\Windows\CurrentVersion\Run (autoruns), HKLM\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit (replaced with Diebold.exe).
- Services: DIEBOLDP, with non-standard paths.
- Event Logs: USB insertions (Event ID 2003, 6416, 4663), unauthorized remote tools like AnyDesk.
- Physical: Tampered locks, unexpected out-of-service status, low cash alerts.
Forensic Artifacts
Forensics reveal .NET binaries with encrypted resources and hooked JIT compilation. Artifacts include modified Winlogon registry, unauthorized services, and files like P.bin (containing "PLOUTUS-MADE-IN-LATIN-AMERICA-XD"). Use tools like de4dot for deobfuscation; check against gold images for deviations. No diagrams or code snippets were extracted from sources, but analysis involves XOR key extraction from static constructors.Impacts
- Financial: $20-40 million losses in 2025 US incidents; individual hits up to $300,000.
- Operational: ATM downtime, forensics costs, reputational damage.
- Broader: Funds terrorist/criminal activities like those of TdA. Also compromises admin credentials and sensitive data.
Mitigations
- Physical: Tamper sensors, unique locks, surveillance, keyed barriers. Regular inspections, two-factor for technicians.
- Hardware/Software: Device whitelisting, firmware checks, hard drive encryption, memory integrity. Update to latest (e.g., AFD v4.1.41+).
- Logging/Monitoring: Audit policies for USB/file access (Event IDs 6416, 4663, 4688), central log storage. EDR, IP whitelisting.
- General: Software whitelisting, penetration testing, threat intel sharing, employee training. Use supported OS, full disk encryption.

