Carding
Professional
- Messages
- 2,870
- Reaction score
- 2,522
- Points
- 113
Leaked last year, the LockBit 3.0 constructor served as the start of a real extortionate cyberpandemic.
Kaspersky Lab recently identified cases of LockBit ransomware infecting its customers with significant changes to ransom demands.
Instead of the usual ransom text, the attackers used a new message on behalf of the previously unknown NATIONAL HAZARD AGENCY group. It immediately indicated a fixed amount for decrypting data of $ 3 million, as well as contacts for communicating with attackers using the Tox protocol or email.
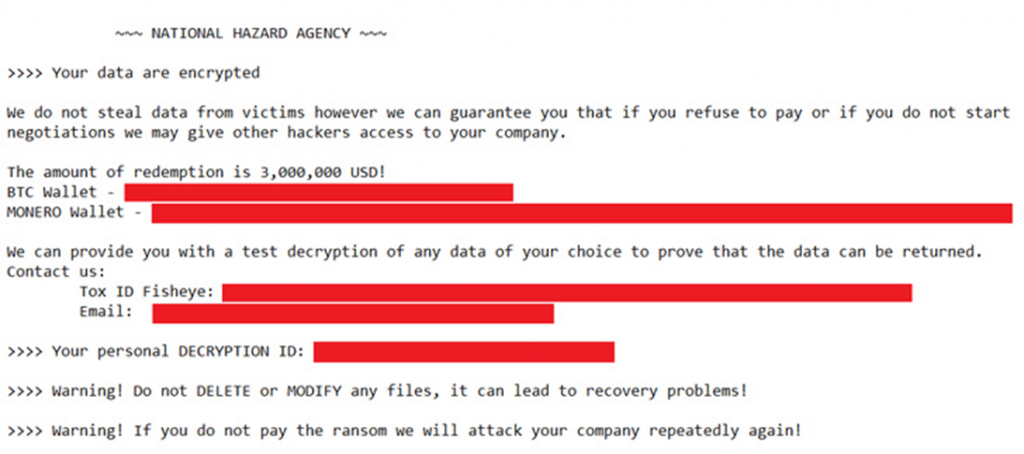
NATIONAL HAZARD AGENCY ransom note
Many other cybercriminals who took advantage of the LockBit 3.0 constructor leak last year do the same. For example, hackers Bl00dy and Buhti.
Experts have already found 396 different samples of LockBit, of which 312 were created using a merged builder. In 77 cases, the extortionate note did not even mention the LockBit group itself.
Many modifications mainly relied on the standard builder configuration. Only occasionally did hackers change some minor parameters, which indicates the haste or laziness of most attackers.
Leaked malware creation tools are always dangerous because they allow cybercriminals of all levels to create and distribute their own versions of known threats.
Companies should be especially vigilant after such incidents and pay close attention to protecting corporate networks, timely software updates and data backup.
Kaspersky Lab recently identified cases of LockBit ransomware infecting its customers with significant changes to ransom demands.
Instead of the usual ransom text, the attackers used a new message on behalf of the previously unknown NATIONAL HAZARD AGENCY group. It immediately indicated a fixed amount for decrypting data of $ 3 million, as well as contacts for communicating with attackers using the Tox protocol or email.
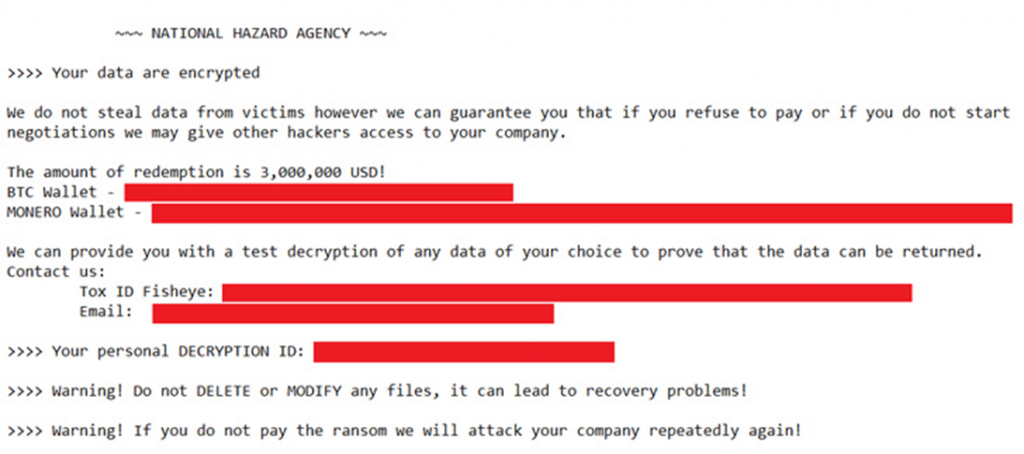
NATIONAL HAZARD AGENCY ransom note
Many other cybercriminals who took advantage of the LockBit 3.0 constructor leak last year do the same. For example, hackers Bl00dy and Buhti.
Experts have already found 396 different samples of LockBit, of which 312 were created using a merged builder. In 77 cases, the extortionate note did not even mention the LockBit group itself.
Many modifications mainly relied on the standard builder configuration. Only occasionally did hackers change some minor parameters, which indicates the haste or laziness of most attackers.
Leaked malware creation tools are always dangerous because they allow cybercriminals of all levels to create and distribute their own versions of known threats.
Companies should be especially vigilant after such incidents and pay close attention to protecting corporate networks, timely software updates and data backup.
