Tomcat
Professional
- Messages
- 2,695
- Reaction score
- 1,063
- Points
- 113

Researchers from the Israeli company ClearSky spoke about the CryptoCore hacking group, which has been active since 2018 and specializes in hacking cryptocurrency exchanges.
According to experts, the group is based somewhere in Eastern Europe, and to date it has managed to "earn" more than $ 200 million by compromising stock exchanges in different countries of the world.
CryptoCore has been linked to at least five successful hacks, as well as attempted attacks on another 10-20 cryptocurrency platforms. Thus, five confirmed victims of hackers are in the United States, Japan and the Middle East. Unfortunately, the names of the affected companies were not disclosed due to nondisclosure agreements with which the researchers are linked.
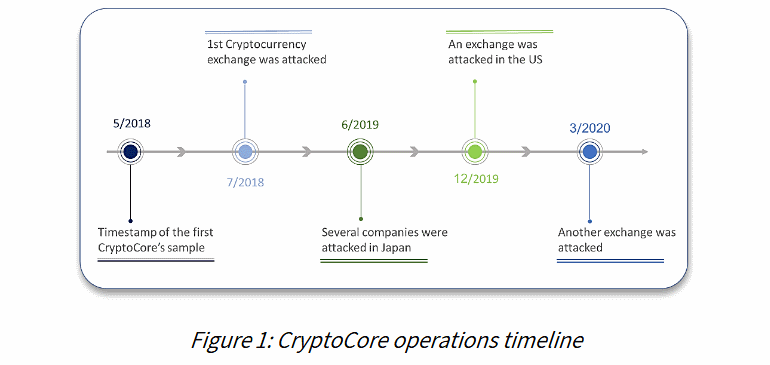
Chronology of attacks
Analysts say they are not the first to spot the group. Previously, some CryptoCore operations have already been included in the reports of other information security companies, for example, Dangerous Password and Leery Turtle. But, as it turns out now, the grouping operations were larger and more widespread and were not limited to these isolated, documented cases.
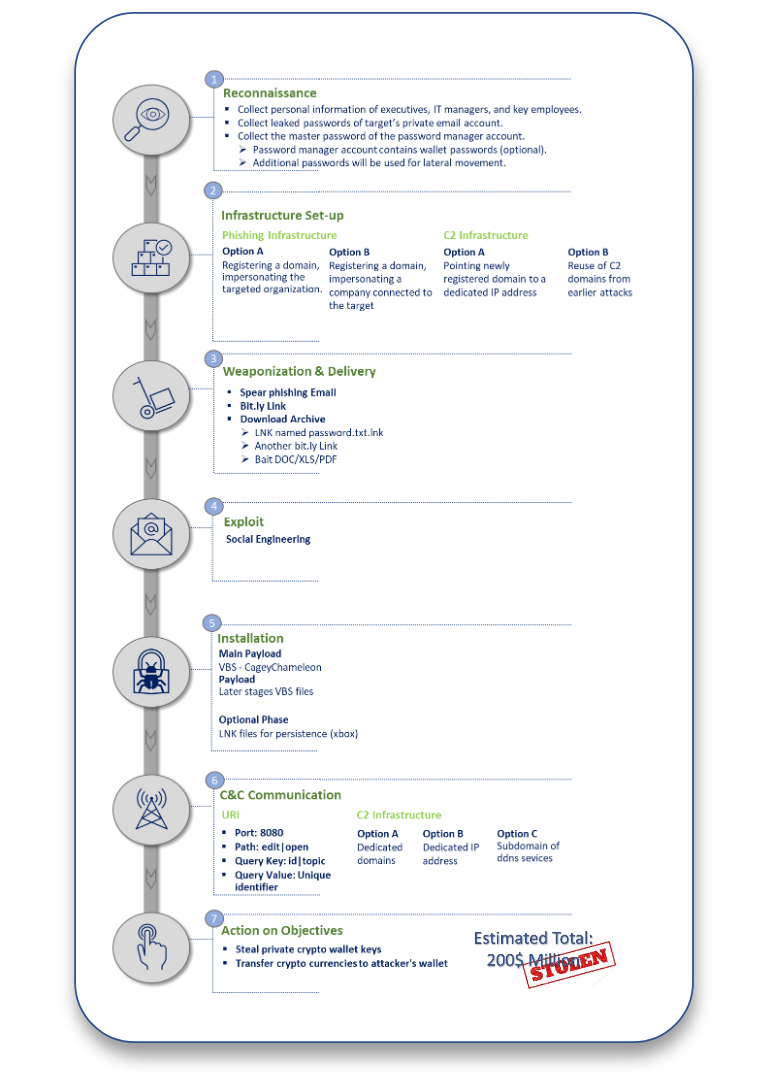
Although ClearSky has been active for two and a half years, the hackers have been using the same tactic all this time with some minor adjustments. Thus, all attacks began with the collection of information: the attackers collected the necessary data on the management of the exchange, its IT staff and other employees.
The group then moved on to phishing attacks, which initially always target personal rather than corporate email addresses. The fact is that personal mailboxes are usually less secure, but there is a good chance that they still contain some kind of work information. And only after some time (from several hours to several weeks), CryptoCore operators nevertheless switched to attacks on victims' work accounts.
The ultimate goal of criminals is to inject malware onto the computer of an exchange employee and gain access to his password manager account (or steal passwords). If the compromise is successful, CryptoCore members use these passwords to access accounts and wallets, to disable the two-factor authentication system and transfer funds from the exchange's "hot wallets" to their accounts.“Spear phishing is usually carried out by impersonating a high-level employee of a target company or other organization (for example, a member of an advisory board) who has a connection with the victim,” the researchers explain.
Attack scheme
All this makes CryptoCore the second hack group to regularly attack cryptocurrencies over the past 3-4 years. However, the main threat to the exchanges is still "government" hackers from North Korea. Let me remind you that, according to the UN, in the period from January 2017 to September 2018 alone, North Korean hackers stole approximately $ 571,000,000 from five Asian cryptocurrency exchanges.
