Student
Professional
- Messages
- 1,662
- Reaction score
- 1,550
- Points
- 113
VoIP (Voice over Internet Protocol) detection has become essential in modern telecommunications for fraud prevention, network optimization, regulatory compliance, quality-of-service (QoS) enforcement, and security monitoring. As of 2026, with rising AI-driven voice scams, deepfake threats, and evolving regulations like tightened STIR/SHAKEN rules, accurate detection is more critical than ever. Detection splits into two primary domains: (1) classifying a phone number as VoIP/virtual versus traditional landline/mobile, and (2) identifying VoIP traffic (signaling and media streams) on networks.
This expanded guide draws on core protocols (SIP, RTP, SDP), real-time telecom databases, deep packet inspection (DPI), statistical analysis, and emerging machine-learning (ML) techniques for encrypted flows. It covers practical tools, implementation details, challenges, global considerations, and future trends.
Core Technique: LRN (Location Routing Number) / LNP Lookups
Every ported number in the North American Numbering Plan (NANP) is mapped to a 10-digit LRN that identifies the current serving switch. Queries to authoritative databases (via SS7 or modern APIs) return the Operating Company Number (OCN), switch type, and routing info.
Commercial Carrier & Line-Type Lookup APIs
Services aggregate global telecom data for instant metadata: line type (VoIP/mobile/landline/toll-free), carrier name, portability status, risk score, and active status. Examples include:
Additional Methods
Use Cases & Fraud Prevention Platforms block high-risk VoIP numbers during registration or SMS campaigns. LRN checks also expose ported/spoofed numbers. In 2026, integration with STIR/SHAKEN (Secure Telephone Identity Revisited / Signature-based Handling of Asserted Information Using toKENs) adds cryptographic caller-ID validation via PASSporT tokens in SIP headers. FCC updates (e.g., Third-Party Authentication Order effective June 2025, Own-Certificate Rule from Sept 2025) require providers to sign calls independently and include Rich Call Data (RCD) for verified names.
Protocol Fundamentals VoIP relies on:
SIP Call Flow Example (simplified): Caller sends INVITE (with SDP offer) → Proxy/Server responds 200 OK (SDP answer) → ACK → RTP media stream.

SIP SDP Protocol: The Complete Guide for VoIP & Multimedia
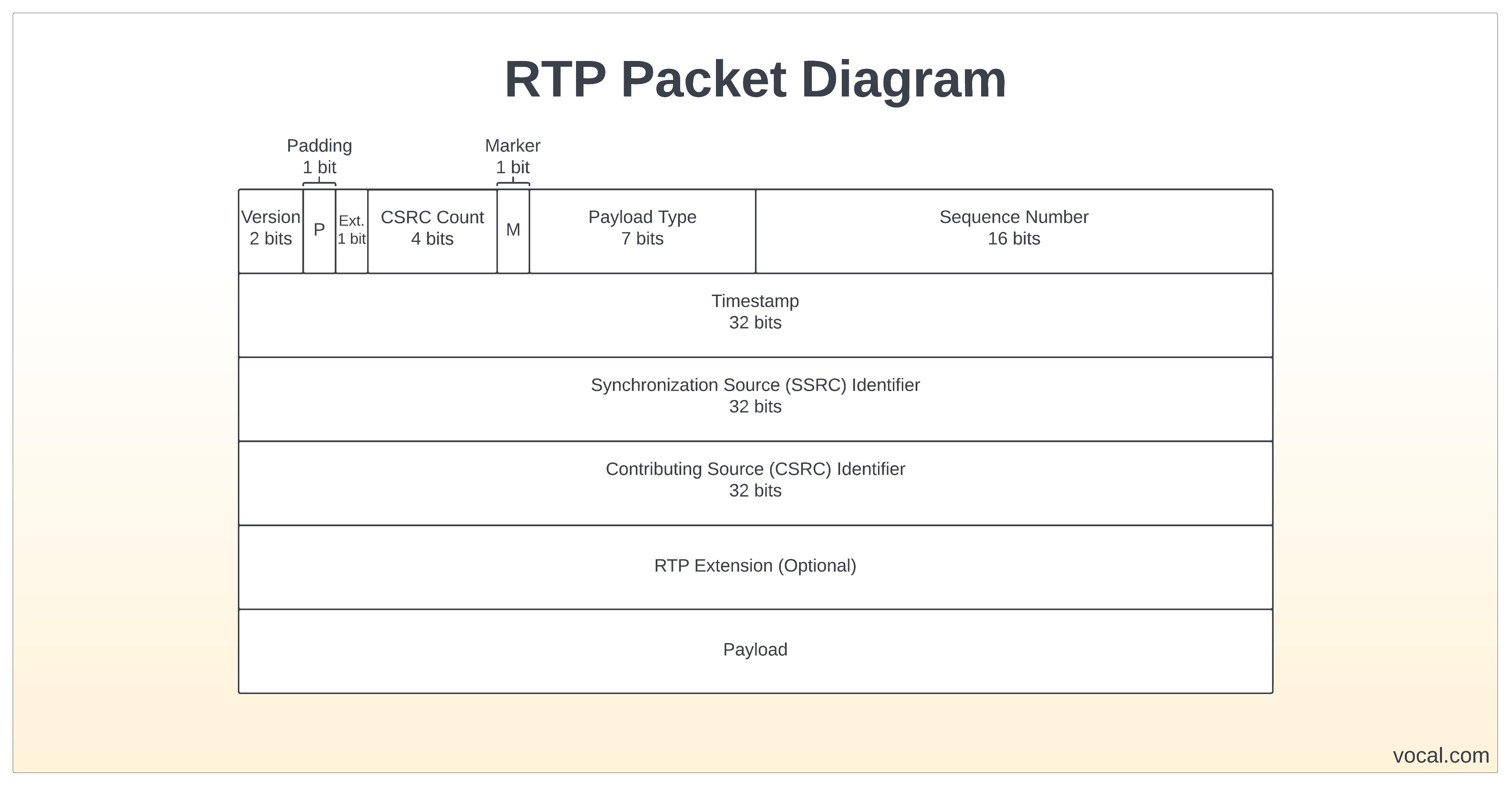
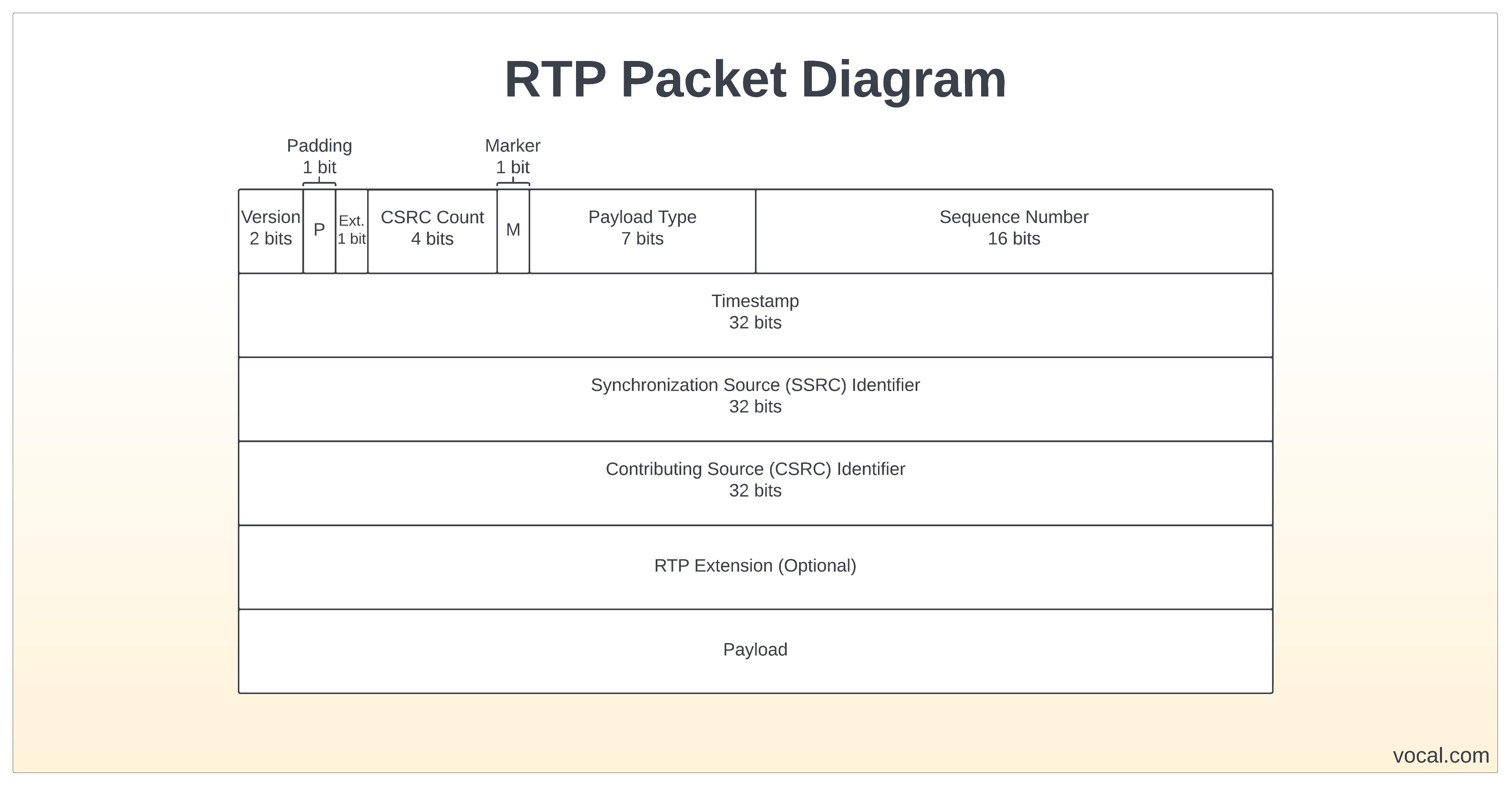
RTP Packet Header Structure (fixed 12-byte base): Ver (2 bits), P (Padding), X (Extension), CSRC Count, M (Marker), Payload Type (7 bits), Sequence Number (16 bits), Timestamp (32 bits), SSRC (32 bits), etc. Payload follows (encrypted in SRTP).
The Real Time Transport Protocol (RTP)
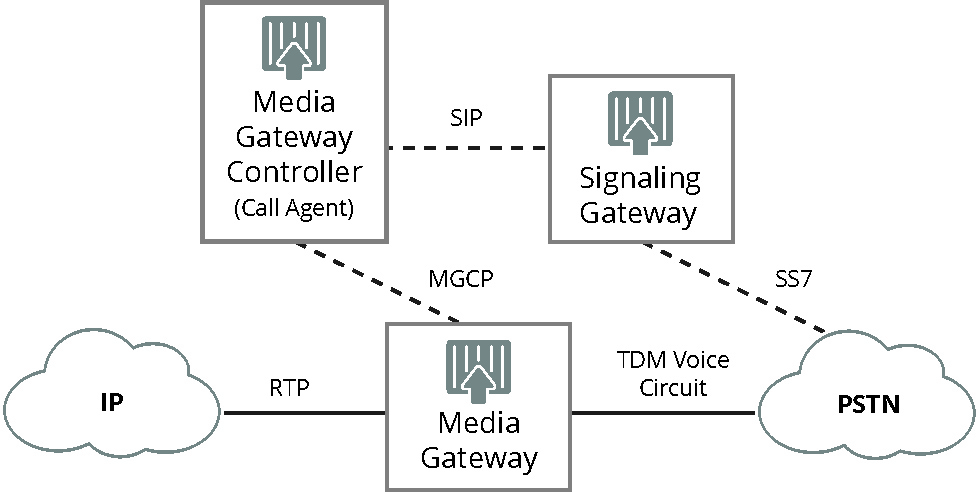
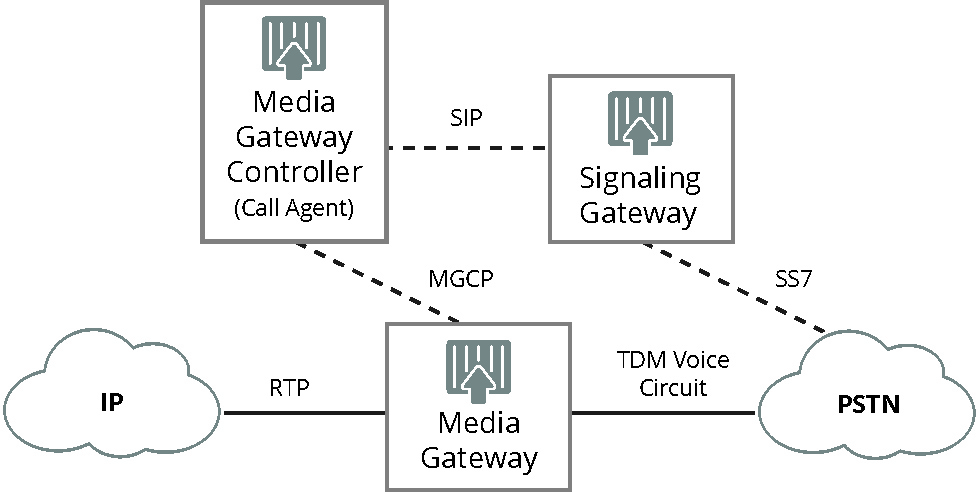
VoIP Network Architecture (Softswitch example): IP endpoints → Softswitch (Media Gateway Controller) → Media Gateway (RTP) ↔ PSTN via SS7/MGCP.
What is a Softswitch?
Detection Techniques
Advanced Methods for Encrypted Traffic (SRTP, WebRTC, DTLS)
Encryption hides payloads, so DPI shifts to flow statistics: packet-size distribution, inter-arrival time (IAT), burstiness, directionality, and duration.
Common Tools (2026 Landscape)
Challenges
Future Trends (2026+)
ML-powered encrypted traffic intelligence, cloud-native SBCs, richer STIR/SHAKEN with RCD, and AI-driven predictive fraud (e.g., behavioral + KYC). Regulatory pressure continues to evolve robocall mitigation.
In practice, start with free tools like Wireshark for traffic or IPQualityScore for numbers, then scale to enterprise APIs/monitors. For custom implementation (e.g., API integration code or Wireshark capture filters), provide your specific environment or use case for tailored examples! This framework equips you for secure, efficient VoIP operations in any context.
This expanded guide draws on core protocols (SIP, RTP, SDP), real-time telecom databases, deep packet inspection (DPI), statistical analysis, and emerging machine-learning (ML) techniques for encrypted flows. It covers practical tools, implementation details, challenges, global considerations, and future trends.
1. Detecting VoIP Phone Numbers (Line Type Classification)
Direct inspection of a number's digits is unreliable due to Local Number Portability (LNP), which allows any number to be moved between carriers. VoIP numbers (e.g., from Twilio, Google Voice, Bandwidth, or Skype) are often flagged as higher-risk for spam, fraud, or disposable accounts in 2FA, SMS verification, sign-ups, and call routing.Core Technique: LRN (Location Routing Number) / LNP Lookups
Every ported number in the North American Numbering Plan (NANP) is mapped to a 10-digit LRN that identifies the current serving switch. Queries to authoritative databases (via SS7 or modern APIs) return the Operating Company Number (OCN), switch type, and routing info.
- If the LRN routes to a softswitch or known VoIP provider (e.g., Bandwidth.com, Level 3, Neutral Tandem) rather than a traditional PSTN Local Exchange Carrier (LEC) like Verizon or AT&T, it is classified as VoIP.
- Softswitches handle IP-based routing, unlike legacy TDM switches.
- Real-time APIs from providers like Alcazar Networks, Bandwidth, MultiTEL, or Teleinx deliver LRN, city/state, OCN, LATA, line type, and Do Not Call status in milliseconds.
Commercial Carrier & Line-Type Lookup APIs
Services aggregate global telecom data for instant metadata: line type (VoIP/mobile/landline/toll-free), carrier name, portability status, risk score, and active status. Examples include:
- ClearoutPhone, IPQualityScore, CarrierLookup.com, SearchBug, and Telesign Phone ID.
- These combine LRN/LNP with HLR (Home Location Register) lookups for mobile/VoIP reachability, CNAM (Caller Name), and signaling analysis.
- Free tiers exist (e.g., IPQualityScore free carrier lookup), while enterprise versions support bulk validation and fraud scoring. Accuracy exceeds 95% in NANP regions when LNP is included; VoIP numbers often route via "landline-like" OCNs leased to providers like Bandwidth.
Additional Methods
- Prefix/Block Analysis: VoIP providers receive dedicated NPA-NXX blocks or recognizable ranges; rulesets flag these.
- Signaling & SMSC Analysis: VoIP routes often use distinct Short Message Service Centers (SMSCs) or IP-based paths.
- Global Extensions: Outside NANP, tools rely on HLR/HSS queries, international carrier databases, or pattern recognition. Services like Sinch or TrestleIQ cover 200+ countries.
Use Cases & Fraud Prevention Platforms block high-risk VoIP numbers during registration or SMS campaigns. LRN checks also expose ported/spoofed numbers. In 2026, integration with STIR/SHAKEN (Secure Telephone Identity Revisited / Signature-based Handling of Asserted Information Using toKENs) adds cryptographic caller-ID validation via PASSporT tokens in SIP headers. FCC updates (e.g., Third-Party Authentication Order effective June 2025, Own-Certificate Rule from Sept 2025) require providers to sign calls independently and include Rich Call Data (RCD) for verified names.
2. Detecting VoIP Traffic on Networks
Network operators, firewalls, IDS/IPS, and monitoring tools identify VoIP to prioritize QoS, troubleshoot jitter/latency, manage bandwidth, or detect attacks (e.g., SIP flooding, toll fraud).Protocol Fundamentals VoIP relies on:
- SIP (Session Initiation Protocol) for signaling (INVITE, REGISTER, BYE, etc.) on UDP/TCP 5060 (unencrypted) or 5061 (TLS). SDP (Session Description Protocol) negotiates media.
- RTP (Real-time Transport Protocol) for media (voice/video) on dynamic UDP ports; includes sequence numbers, timestamps, SSRC, and codecs (G.711, G.729, Opus).
- RTCP for control/quality feedback.
SIP Call Flow Example (simplified): Caller sends INVITE (with SDP offer) → Proxy/Server responds 200 OK (SDP answer) → ACK → RTP media stream.

SIP SDP Protocol: The Complete Guide for VoIP & Multimedia
RTP Packet Header Structure (fixed 12-byte base): Ver (2 bits), P (Padding), X (Extension), CSRC Count, M (Marker), Payload Type (7 bits), Sequence Number (16 bits), Timestamp (32 bits), SSRC (32 bits), etc. Payload follows (encrypted in SRTP).
The Real Time Transport Protocol (RTP)
VoIP Network Architecture (Softswitch example): IP endpoints → Softswitch (Media Gateway Controller) → Media Gateway (RTP) ↔ PSTN via SS7/MGCP.
What is a Softswitch?
Detection Techniques
- Port-Based & Signature Matching: Block/prioritize UDP 5060/5061 + dynamic RTP ports.
- Deep Packet Inspection (DPI): Parse SIP methods/headers and RTP fixed headers/payload types. Correlate SIP dialogs with RTP streams. Tools inspect for consistent packet sizes (~160-200 bytes for G.711 at 20ms) and inter-arrival times.
- Statistical/Behavioral Analysis: VoIP shows low-jitter UDP flows, specific DSCP (EF for Expedited Forwarding), bursty small packets, and predictable MOS (Mean Opinion Score) from jitter/packet loss. NetFlow/IPFIX with AVC reports RTP metrics.
Advanced Methods for Encrypted Traffic (SRTP, WebRTC, DTLS)
Encryption hides payloads, so DPI shifts to flow statistics: packet-size distribution, inter-arrival time (IAT), burstiness, directionality, and duration.
- ML/DL approaches (e.g., C4.5, SVM, or representation-learning models like MAPLE/DATE) classify RTP in middleboxes using embeddings.
- Language identification or speaker detection via packet lengths is possible but privacy-sensitive.
Common Tools (2026 Landscape)
- Wireshark (free): Filters (sip, rtp), Telephony → VoIP Calls, RTP Streams/Graph, audio playback, SRTP decryption (with keys).
- VoIPmonitor (open-source + commercial): Carrier-grade SIP/WebRTC monitoring, live MOS/jitter/packet-loss, call recording, fraud alerts.
- Others: SolarWinds VNQM/NetFlow Analyzer, PRTG, ThousandEyes, Homer Sipcapture, Obkio for synthetic testing.
3. VoIP Fraud, Spam & Advanced Security Detection
Combine number + traffic methods with:- CDR (Call Detail Record) analytics for spikes in international calls or traffic pumping.
- STIR/SHAKEN + RCD for attestation (A/B/C levels) and verified caller names.
- AI/ML: Anomaly detection on CDRs/SIP (e.g., INVITE floods, SIM-box patterns via rapid registration/cycling), voice biometrics, predictive scoring. Platforms like TransNexus or Subex integrate with SBCs for real-time blocking.
Challenges
- Encryption & WebRTC (peer-to-peer, dynamic ports).
- Number portability and international variability.
- False positives in ML; AI voice deepfakes.
- Privacy (e.g., avoiding decryption).
- 5G/IMS integration adds complexity.
Future Trends (2026+)
ML-powered encrypted traffic intelligence, cloud-native SBCs, richer STIR/SHAKEN with RCD, and AI-driven predictive fraud (e.g., behavioral + KYC). Regulatory pressure continues to evolve robocall mitigation.
In practice, start with free tools like Wireshark for traffic or IPQualityScore for numbers, then scale to enterprise APIs/monitors. For custom implementation (e.g., API integration code or Wireshark capture filters), provide your specific environment or use case for tailored examples! This framework equips you for secure, efficient VoIP operations in any context.

